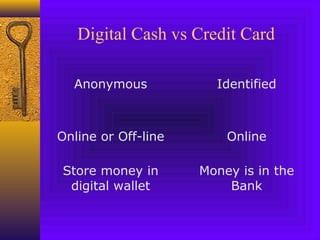
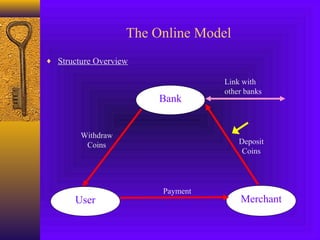
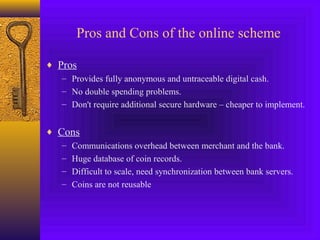
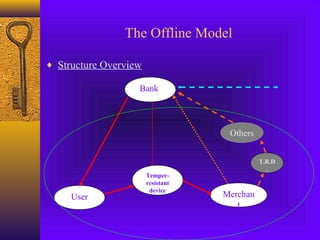
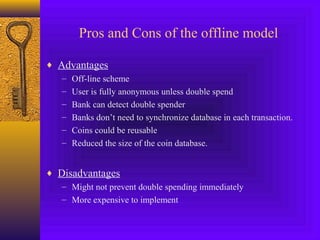
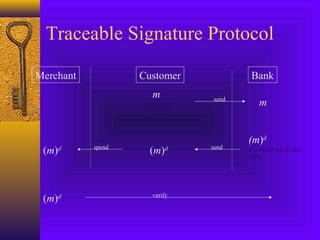
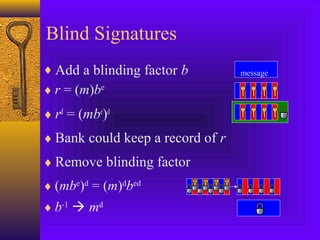
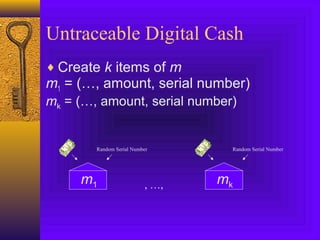
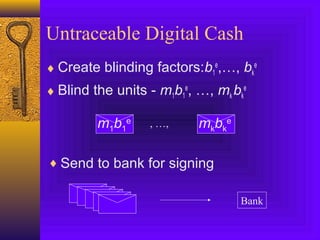
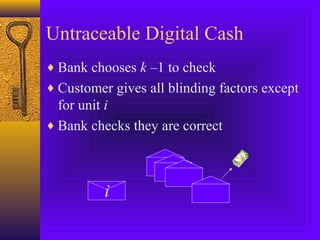
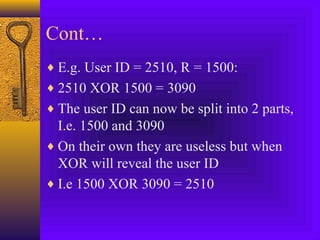
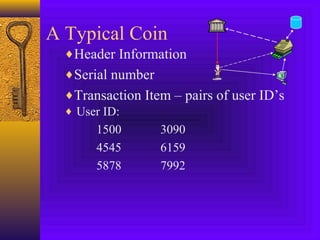
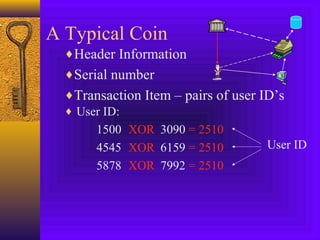
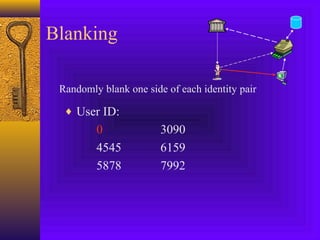
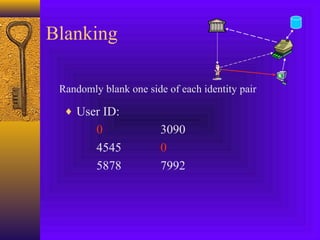
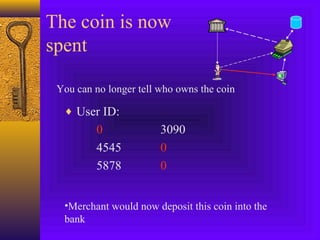
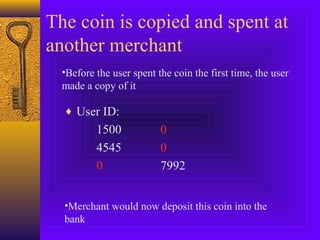
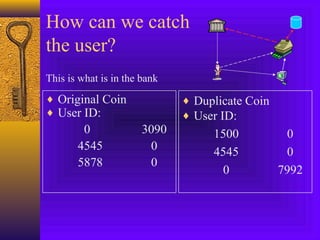
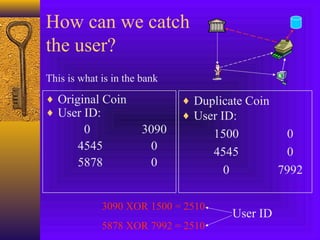
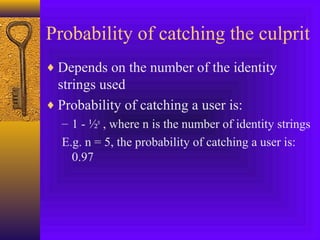
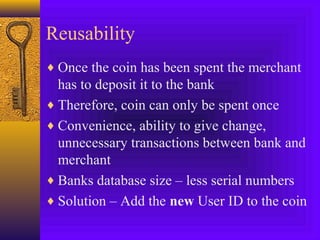
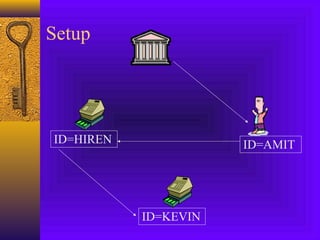
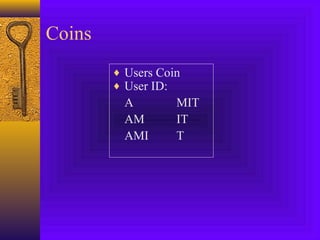
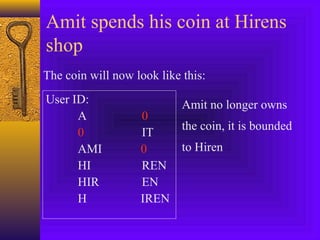
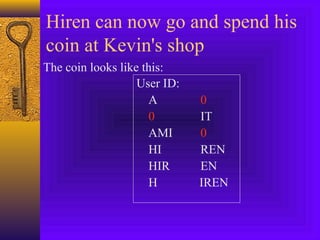
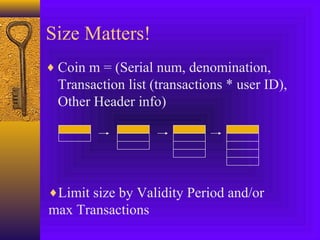
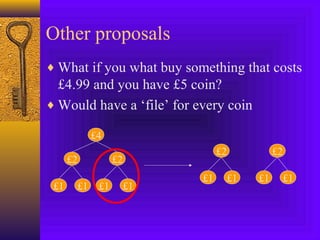
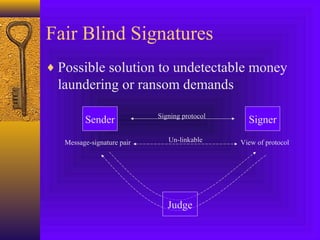
The document presents an overview of digital cash, defining it as a payment method with essential properties including security, anonymity, and portability. It compares online and offline transaction models, discussing their pros and cons, and introduces concepts like traceable signatures and secret splitting to enhance anonymity and prevent double spending. Additionally, it outlines issues of reusability and database management, while emphasizing the convenience and security of digital cash despite potential legal and safety concerns.