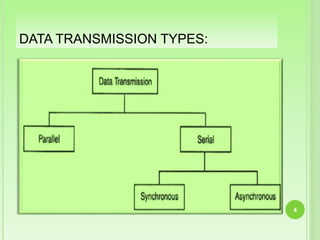
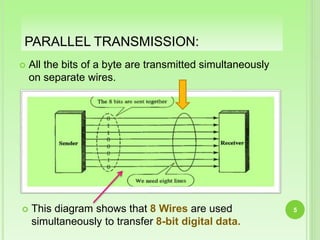
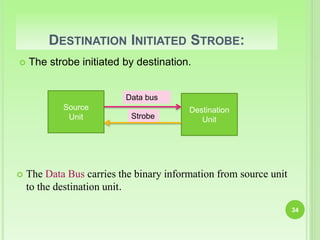
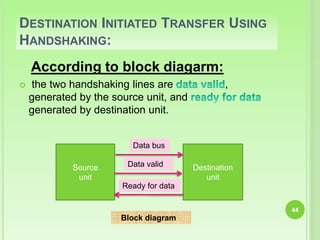
The document discusses different methods of data transmission between digital devices. It describes parallel transmission where all bits are transmitted simultaneously on separate wires, allowing for faster transmission but requiring more wires. Serial transmission transmits bits one after the other on a single wire, requiring fewer wires but slower transmission. Synchronous transmission uses a common clock while asynchronous transmission uses start and stop bits between bytes. The document also discusses transmission modes like simplex, half-duplex, and full-duplex, and methods for asynchronous transmission including strobe control and handshaking.