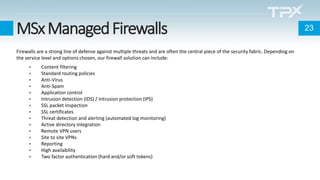
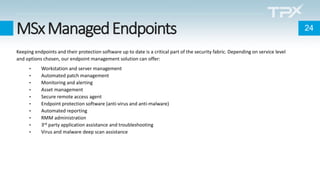
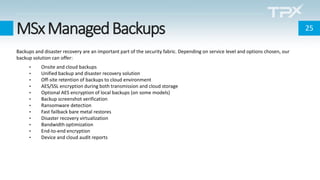
The document addresses the rise in cybersecurity threats due to COVID-19, highlighting an increase in phishing, ransomware, and remote work-related attacks. It emphasizes the importance of firewalls, endpoint security, and maintaining updated software to mitigate risks. Additionally, it discusses backup and disaster recovery as critical components of a comprehensive cybersecurity strategy.