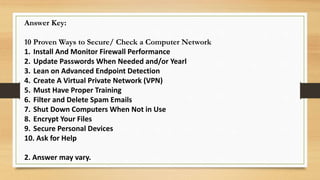
This document outlines 10 proven ways to secure and check a computer network. It discusses installing and monitoring firewalls, updating passwords regularly, using advanced endpoint detection technology, creating a virtual private network, providing proper training to users, filtering spam emails, shutting down computers when not in use, encrypting files, securing personal devices, and asking for help from technology management providers. Regularly inspecting and testing configured computer networks is important to ensure their safe operation and prevent costly security breaches and data loss from hackers and viruses.