Cybersafety Talk
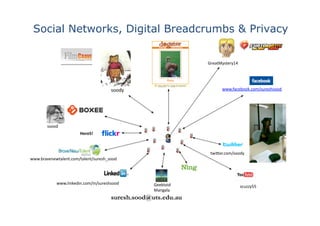
- 1. Social Networks, Digital Breadcrumbs & Privacy GreatMystery14 soody www.facebook.com/sureshsood ssood Hero5! twi7er.com/soody www.bravenewtalent.com/talent/suresh_sood www.linkedin.com/in/sureshsood Geektoid scuzzy55 Mangala suresh.sood@uts.edu.au
- 4. Agenda 0. Inappropriate Content and Contact 1. Online Social Networks 101, “FaceBook to Dogster” 2. TV 3.0 -‐ The Future of Social Networks 3. How should I organise my security seUngs? 4. Where does Twi7er Fit? 5. Digital Breadcrumbs 6. Steps to Avoid Social Engineering A7acks 7. The Australian Government Resources for Safety on the Internet 8. Parents – What Should We Do?
- 6. Linguis`c Inquiry & Word Count : “junk words” in content h7p://www.liwc.net/liwcresearch07.php Cogni`ve complexity = zexcl + ztentat + znegate + zdiscrep zincl Depression = zI + zphyscal + znegemo – zposemo Liar = – zself – zother – zexcl + znegemo or Honesty = zself + zother + zexcl -‐ znegemo -‐ zmo`on Female = zself – zsixltr +z other + znegate – zar`cle – zpreps + zcertain + zsocial + zpresent – zspace – zoccup + zhome – zmoney Aging = zposemo – zI + zsixltr + zcogmech + zexcl + zfuture – zpast – z`me Presiden`al = zsixltr – zwps – zunique – zpronoun – zself – zyou – zother – znegate + zar`cle + zprep Slatcher, R.B., Chung, C.K., Pennebaker, J.W., & Stone, L.D. (2007), Winning words: Individual differences in linguis`c style among U.S. presiden`al and vice presiden`al candidates, Journal of Research in Personality, 41, 63-‐75. 6
- 7. Lurking A Fact of Life Online 0.1 0.003 0 5 0.2 1 95 99.8 99
- 9. Social Media • Blog – reflect, read, write and comment e.g. WordPress, LiveJournal, • Microblogging – brief notes, messages, comments e.g. Twi7er, Tumblr • Social Network – connect, communicate, and sharee.g. Facebook, Ning, MySpace, etc • Generate content – upload content to share with others, comment or tag or reuse the content e.g. YouTube, Vimeo, Flickr, Slideshare
- 10. Social Networking Sites • Parse through friends ac`vi`es forwards & reverse as well as own social gestures • Allow users to: – Create personal profiles inclusive of loca`on informa`on – Write status updates (pos`ngs to friends) c.f. blog entries – Friends specify updates they like – Post photographs, videos, and audio clips – Send and receive private messages – Link to the pages of friends
- 11. TV 3.0 Livesta`on All your channels in one place Surf and email while you watch Instant, live chat with others watching Livesta`on Desktop alerts bring you breaking news and Livesta`on updates Share with friends. Boxee makes it easy for friends to share their favorite movies, TV Shows, and songs with each other, on Boxee or on social networks like Facebook and Twi7er.
- 12. World Map of Social Networks www.incos.it
- 13. Facebook is My Newspaper (Susie Wilkening, h7p://reachadvisors.typepad.com/ OneRiot.com: Search the real`me web
- 15. 16 million people in the UK accessed Internet via mobile phones in December 2009. Total of 6.7 billion pages and 4.8 billion minutes online during the month. Top 10 sites accounted for 70 per cent of both total pages viewed and total `me spent online
- 16. Australia Leads Average Time Spent per Person on Social Media Sites in December 2009
- 17. Facebook • Founded in 2004, primarily catering to students • Over 400M ac`ve members worldwide with 2011 predic`ons for 1 billion users (Gartner) • Facebook has communi`es,users,applica`ons & albums • Over 10 Billion photos in Oct 2008 and adds over 3Billion monthly • Australian 8.1 M users in October2009 had uploaded 80 million pictures and wri7en 32 million "wall posts" and 45 million "status updates". (Nielsen Online) • Australians are spending 29% of all `me browsing the internet on Facebook alone (Nielsen) • Applica`ons run on Facebook platorm • True names encouraged but not guaranteed • Privacy model is highly granular – present different informa`on to different groups or individual users • Messaging includes mail, real-‐`me chat, "wall" • Now used in private background checks
- 20. Inappropriate Contact with Strangers and Bullies Public info: Name, Profile Picture, Current City, Gender, Networks, Friend List and Pages. 20
- 21. Facebook Tips -‐ Privacy • Friends Lists • Facebook Search & Google • Photo Tag Mishaps • Rela`onship Changes • Contact Info • Wall Pos`ngs
- 23. TWITTER • Market leader in "micro-‐blogging" • Began in mid-‐2006 as "status message" service • Ubiquity and ease of upda`ng, but limited space • Breaking news, real-‐`me updates: USAir, Iran • Most mul`media handled by 3d party links • Simplified privacy model: updates public or private • Most Twi7er content is public • Private messages kept un`l user deletes them • Direct messages are private; sender can delete • Short URLs used to serve malicious links and code
- 27. Social Engineering A7acks • Malicious sovware (malware) is installed into a computer fixed or mobile − to collect personal informa`on over `me. • Computers or mobile devices are hacked for personal data. • Phishing – criminals use decep`ve e-‐mails to get users to divulge personal informa`on, includes luring them to fake bank and credit-‐ cards websites. “Pharming”: using decep`ve e-‐mail messages to redirect users from an authen`c website to a fraudulent one, which replicates the original in appearance. – “SMiShing”: sending text messages (“SMS”) to cell phone users that trick them into going to a website operated by the thieves. Messages typically say that unless users go to the website and cancel, they will be charged for services they never actually ordered. – “Spear-‐phishing”: impersona`ng a company employee/employer via e-‐ mail in order to steal colleagues’ passwords/ usernames and gain access the company’s computer system. ID thieves misuse vic`ms’ personal info.
- 30. What to Do – Elements of Strategy
- 31. Cau`on! “Children never put off till tomorrow what will keep them from going to bed tonight” (Anonymous)
