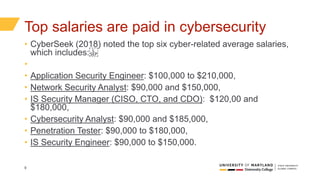
The document outlines the need for enhanced cybersecurity education through resource sharing among regional colleges, driven by increasing cybersecurity threats and a significant shortage of qualified professionals in the field. It discusses various training methodologies and technologies, including virtualization and cloud-based services, to address educational challenges and improve hands-on learning opportunities. The South Central Coast Regional Consortium aims to unify efforts among colleges in California to develop effective cybersecurity programs and create a more skilled workforce.