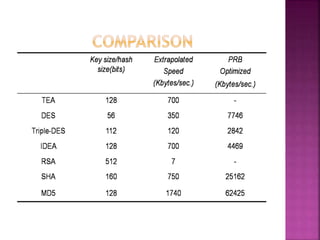
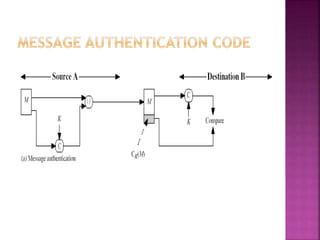
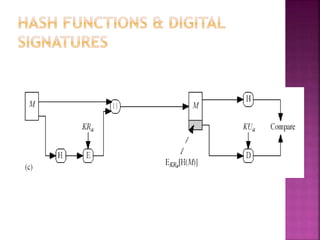
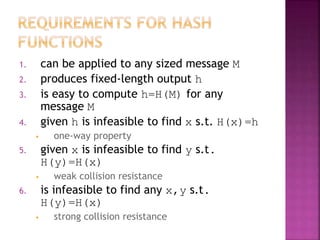
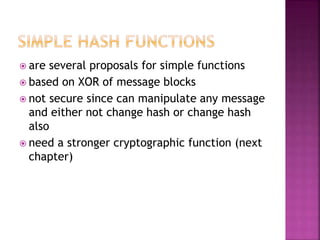
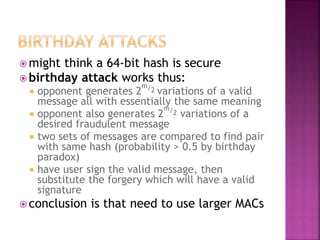
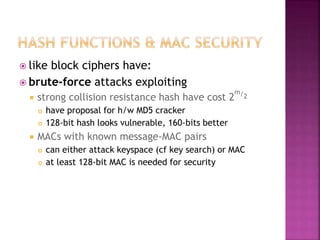
This document discusses message authentication and encryption. It explains that message authentication aims to protect integrity, validate originator identity, and enable non-repudiation. Message encryption provides authentication if symmetric encryption is used, while public-key encryption requires signing. Message authentication codes (MACs) and hash functions are also examined. The MD5 algorithm is summarized, which takes an input of arbitrary length and produces a 128-bit fingerprint.

![ can use block ciphers as hash functions
using H0=0 and zero-pad of final block
compute: Hi = EMi
[Hi-1]
and use final block as the hash value
similar to CBC but without a key
resulting hash is too small (64-bit)
both due to direct birthday attack
and to “meet-in-the-middle” attack
other variants also susceptible to attack](https://image.slidesharecdn.com/cryptographyandnetworksecurity-190408182012/85/Cryptography-and-network_security-19-320.jpg)
![ cryptanalytic attacks exploit structure
like block ciphers want brute-force attacks to be
the best alternative
have a number of analytic attacks on
iterated hash functions
CVi = f[CVi-1, Mi]; H(M)=CVN
typically focus on collisions in function f
like block ciphers is often composed of rounds
attacks exploit properties of round functions](https://image.slidesharecdn.com/cryptographyandnetworksecurity-190408182012/85/Cryptography-and-network_security-21-320.jpg)
![Round 1.
[abcd k s i] denote the operation a = b + ((a + F
(b, c, d) + X [k] + T [i]) <<< s).
Do the following 16 operations.
[ABCD 0 7 1] [DABC 1 12 2] [CDAB 2 17 3]
[BCDA 3 22 4]
[ABCD 4 7 5] [DABC 5 12 6] [CDAB 6 17 7]
[BCDA 7 22 8]
[ABCD 8 7 9] [DABC 9 12 10] [CDAB 10 17 11]
[BCDA 11 22 12]
[ABCD 12 7 13] [DABC 13 12 14] [CDAB 14 17 15]
[BCDA 15 22 16]](https://image.slidesharecdn.com/cryptographyandnetworksecurity-190408182012/85/Cryptography-and-network_security-28-320.jpg)