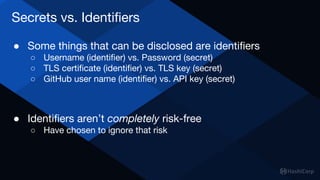
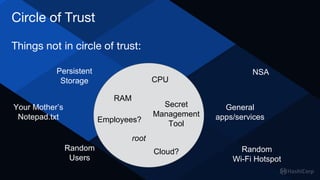
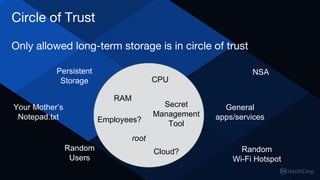
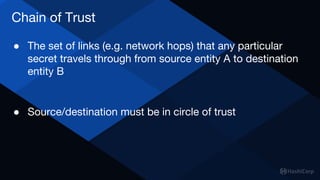
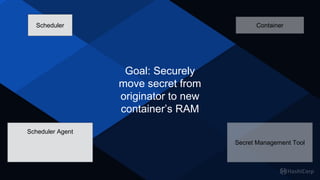
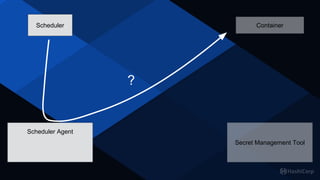
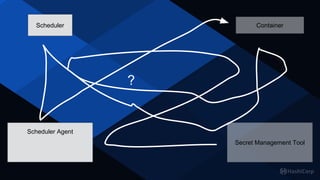
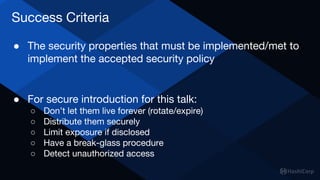
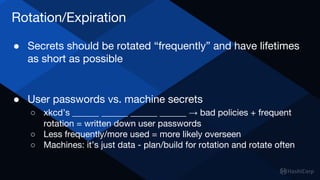
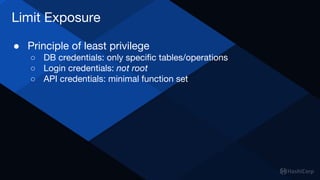
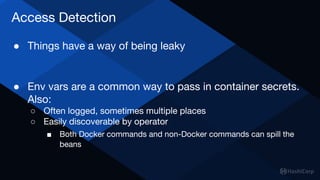
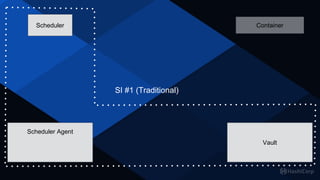
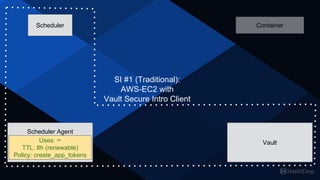
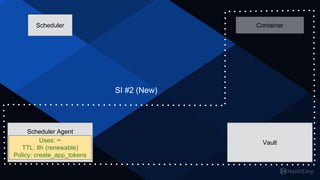
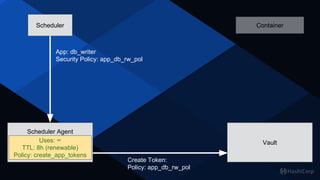
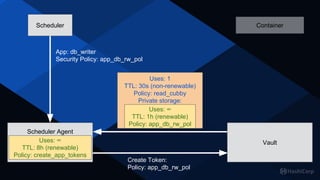
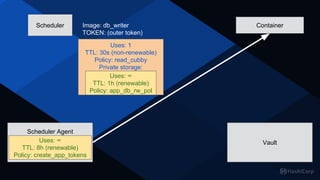
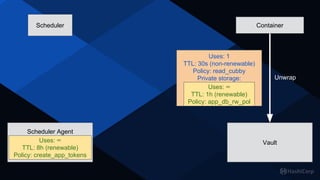
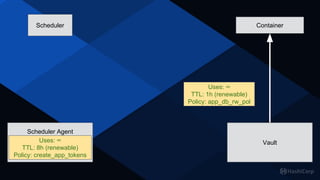
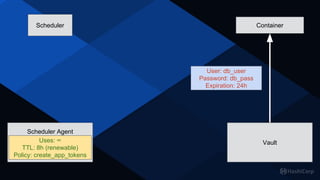
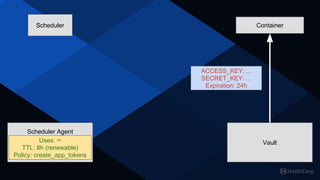
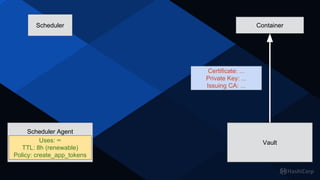
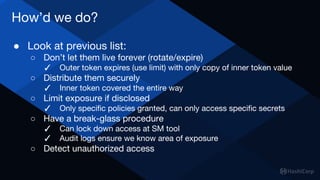
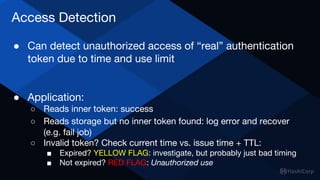
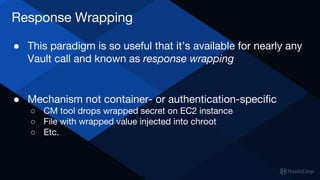
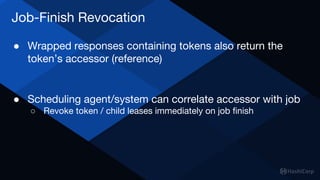
The document discusses key security principles related to secret management, emphasizing the establishment of trust chains and secure introduction within environments utilizing tools like HashiCorp Vault. It outlines essential practices for protecting secrets, including risk minimization, secure distribution, and monitoring unauthorized access. The ultimate goal is to achieve a zero-trust model in secret management, ensuring secrets are securely moved and handled throughout their lifecycle.