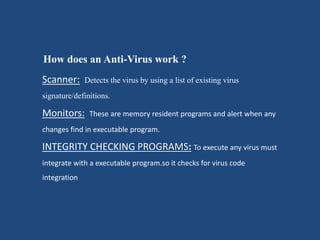
A computer virus is a program that can copy itself and infect a computer without the user's permission or knowledge. Viruses are created by people looking to steal information, make money from antivirus software, or for fun. An infected computer may function slowly, freeze often, restart on its own, and have applications that fail to work correctly. Antivirus software detects viruses using signature files and protects computers and personal information from hackers and viruses.