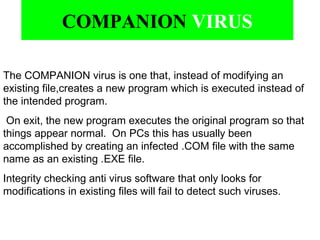
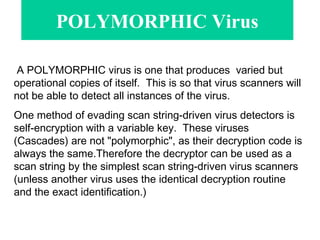
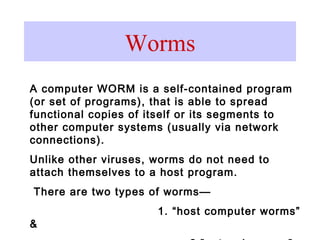
The document provides information on various types of computer viruses, including how they infect systems and replicate. It discusses topics like file infectors, boot sector viruses, polymorphic viruses, and worms. Examples are given of different viruses and recommendations are provided on how to protect against computer viruses.































![What do expert’s believe are in store for
the future of Virus’s?
''Iraq will destroy us by computer,'' the experts screamed
by Rob Rosenburg -- 05/01/03
"IRAQ WILL CRIPPLE the U.S. with cyber-attacks," the fear mongers warned. I tell
you, everyone got into the act -- from Congress to the FBI to former CIA officials to
computer security salesmen.
Even a fire-breathing Muslim cleric living the high life in Britain got into the act. Even
a delusional narcissistic hacker living in the slums of Kuala Lumpur got into the act. I
tell you, everyone screamed about the coming cybergeddon.
I mean, c'mon! How much effort does it take to “open a digital can of whoop-ass” on
the United States? From what I hear, even a 14 year old Iraqi nomad can remotely shut
down our national power grid and remotely pollute our vital toilet water supplies.
In August of last year, an ominous m2g press release quoted CEO D.K. Matai: "it
would seem highly likely that the launch of a physical attack on Iraq will see counter-
attacks from disgruntled Arab, Islamic fundamentalist and anti-American groups."
mi2g warned terrorists might launch remote-controlled “SCADA Attacks” along with
those (equally?) scary "chemical, biological, radiological, [and] nuclear" attacks.](https://image.slidesharecdn.com/virus-101114200338-phpapp02/85/Virus-35-320.jpg)
![CONT. In December 2002, IDC chief research officer John Gantz predicted a major cyber
terrorism event would occur in 2003 -- a cybertastrophe "that will disrupt the economy and bring
the Internet to its knees for at least a day or two," according to News.com scribe Ed Frauenheim.
Gantz specifically warned "the [looming] war with Iraq will galvanize hackers."
A New York Times story in mid-January quoted House Armed Services Committee member
Robert E. Andrews (D-NJ), who warned "a cyber attack really fits Saddam Hussein's paradigm
for attacking us." The same New York Times story quoted ex-FBI flunky Michael Vatis (a well-
documented fear-monger) on the cyber-threat Iraq could pose to U.S. interests should war break
out. ""I would suspect [Iraq's computer warfare program is] at a middling stage ... but even a
middling capability can cause serious harm."
FBI's National Internet Infrastructure Protection Center (now known as DHS NIPC) issued a
pre-war advisory to say Iraq or its sympathizers might cripple the U.S. with Spam.
Meanwhile, Japan's version of NIPC -- the Information Technology Security Center within the
Ministry of Economy -- went on "heightened alert" after their prime minister made comments
supporting the U.S.-led coalition against Iraq. The agency soon upgraded its cyber-threat
assessment and sent a written plea ("written"?) to computer security firms to ask them to "watch
for computer virus attacks and unauthorized changes to Web sites."
According to a Kyodo newswire, Japan's version of NIPC wanted to assure the public "[computer
security firms] will be on alert day and night to be able to act immediately on any abnormal
incidents." No doubt.](https://image.slidesharecdn.com/virus-101114200338-phpapp02/85/Virus-36-320.jpg)

