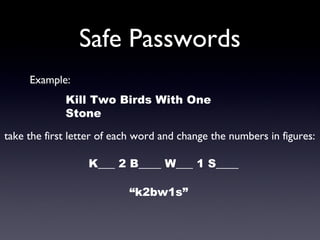
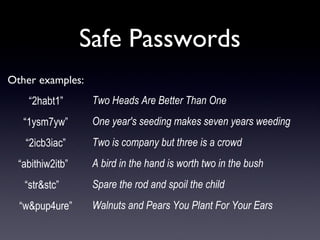
The document discusses computer security, defining it as a branch of technology focused on protecting information and property from risks like theft and malware. It explains various types of malware (viruses, trojans, bots, spyware) and social engineering tactics (spam, hoaxes, phishing) used to compromise security. Recommended defenses include being cautious with information sharing, using strong, memorable passwords, and regularly updating them.