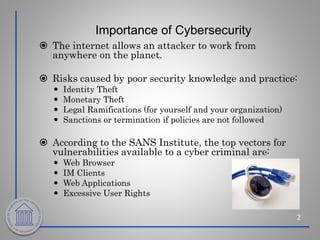
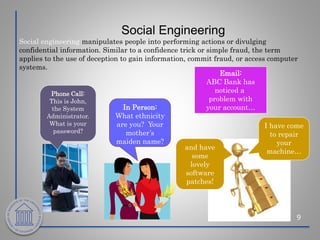
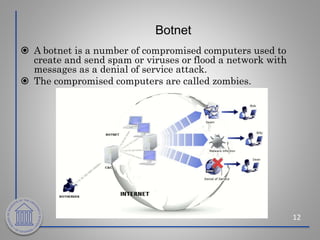
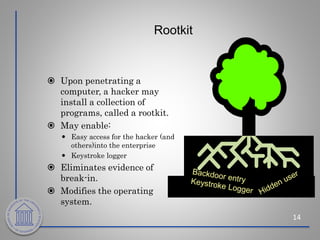
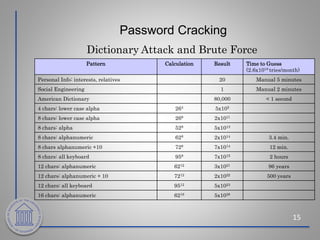
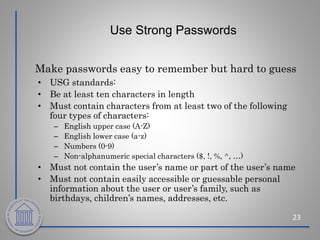
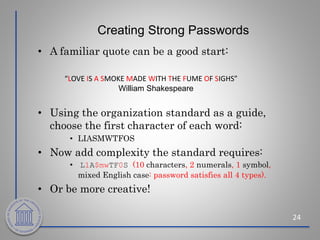
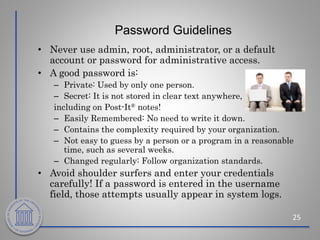
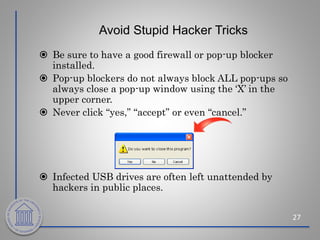
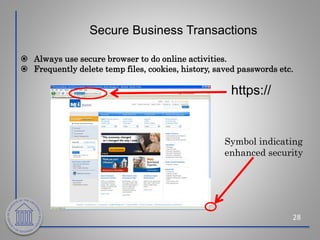
Cybersecurity is important to protect individuals and organizations from threats on the internet. The top threats include viruses, worms, Trojan horses, social engineering, rootkits, and botnets. To avoid these threats, best practices include using strong passwords, keeping systems updated, using firewalls and antivirus software, avoiding suspicious emails and downloads, and practicing cybersecurity awareness. Following guidelines for passwords, software updates, and caution with emails and downloads can help reduce cybersecurity risks.