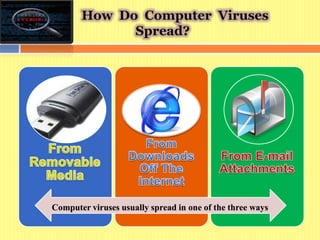
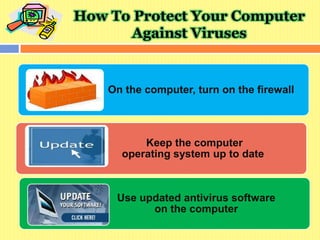
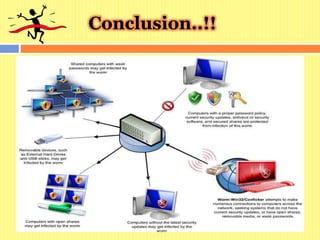
Computer viruses are small programs that spread from one computer to another and interfere with computer operations. They can corrupt or delete data, use email to spread, or delete everything on the hard disk. There are different types of viruses including boot viruses, program viruses, multipartite viruses, macro viruses, and activex viruses. Viruses usually spread via email, removable disks, or networks. To remove viruses, users should install and update antivirus software and scan the computer. They should also install operating system updates and use a firewall to protect the computer from future infections.