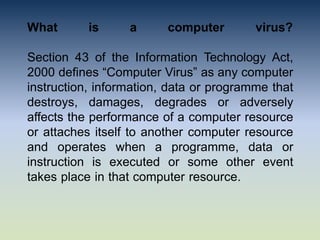
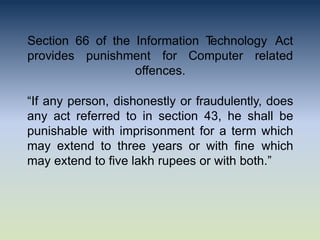
The document discusses computer viruses, defining them as malicious software that spreads and damages data on computers, with legal implications outlined in the Information Technology Act. It details how viruses operate, their symptoms, types, including boot sector and polymorphic viruses, and notable virus outbreaks like MyDoom and ILOVEYOU. The conclusion emphasizes the need for robust cybersecurity measures to combat evolving malware threats.