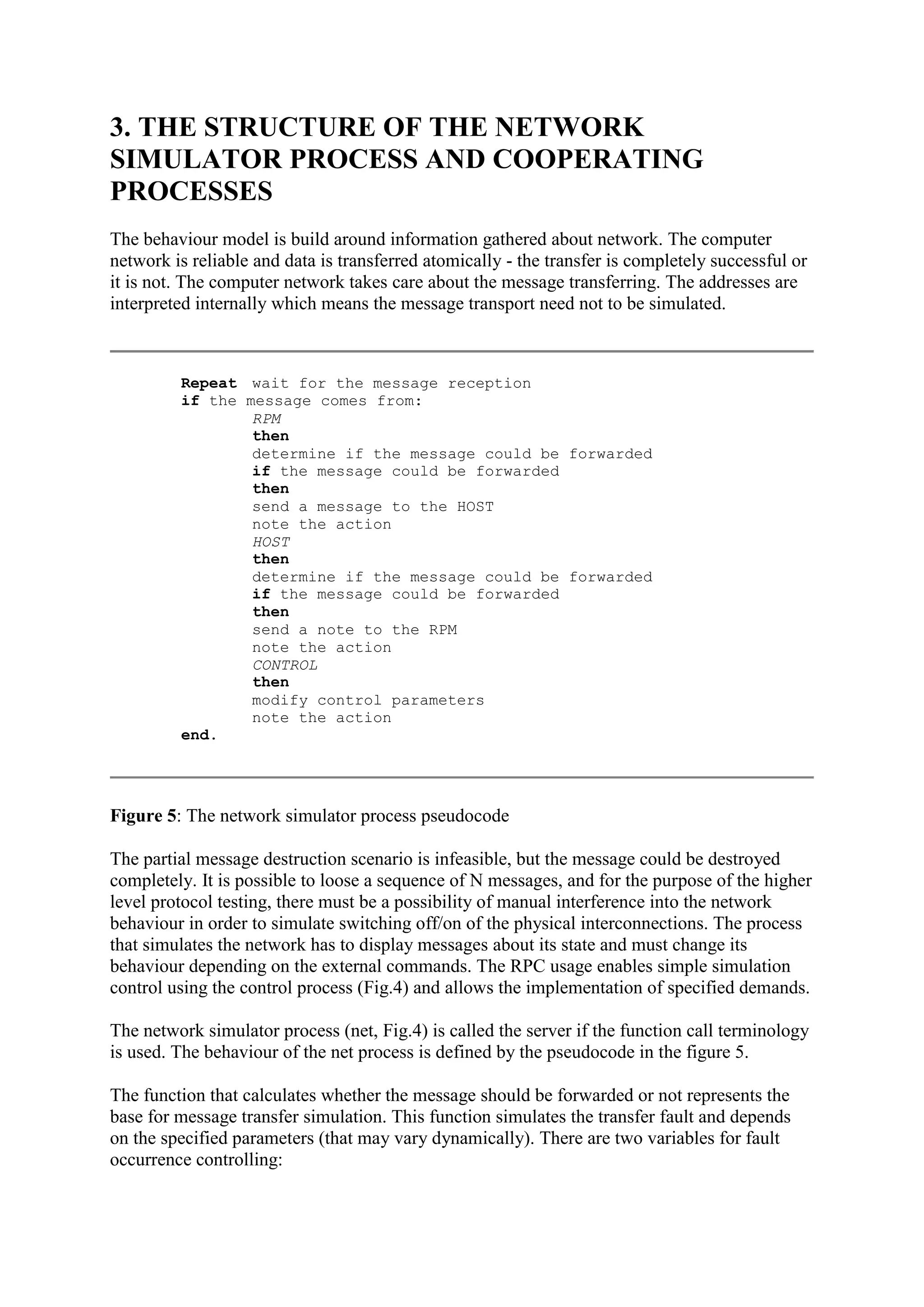
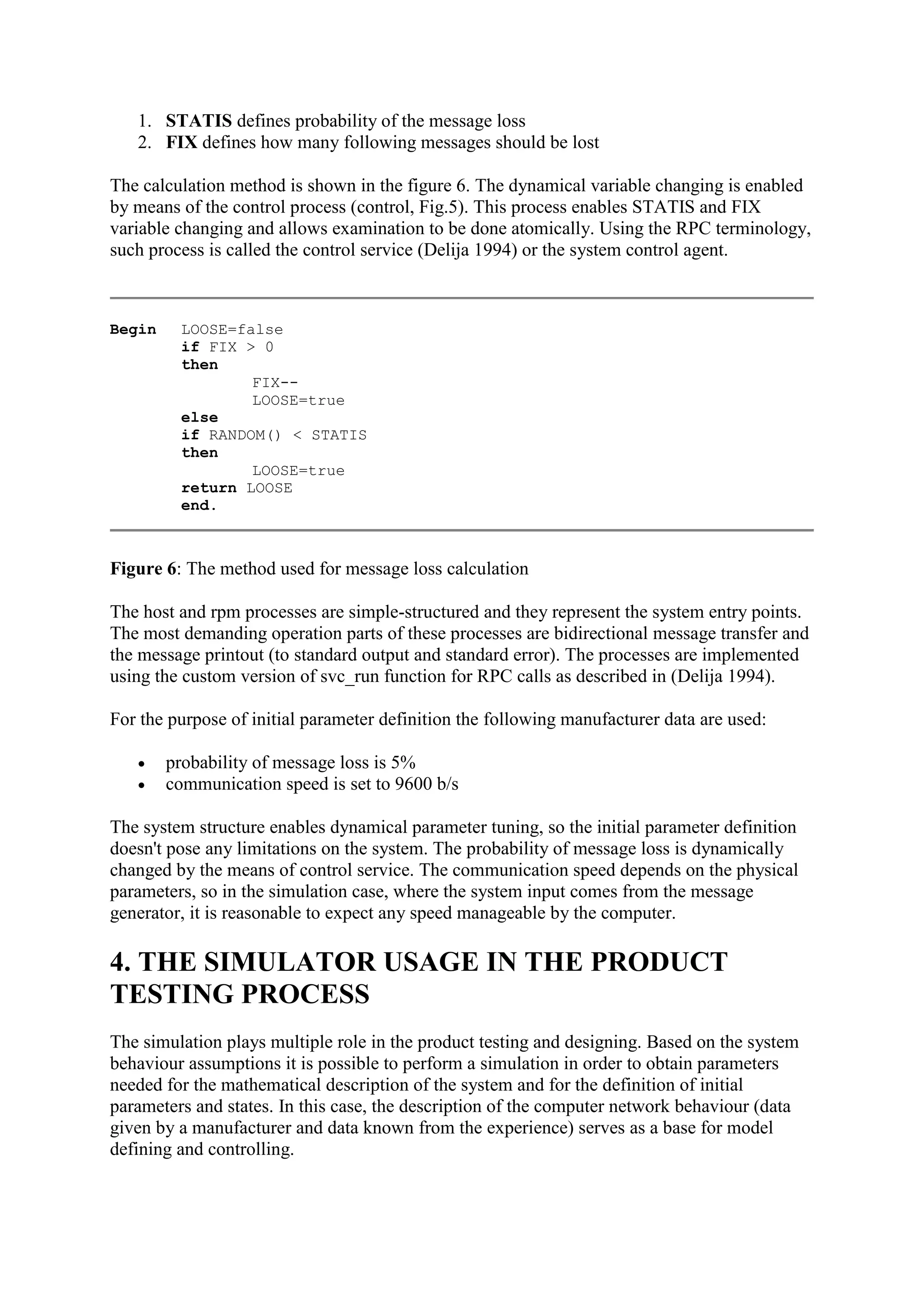
This document describes a simulation of a communication network on UNIX using Remote Procedure Calls (RPCs). The simulation allows testing of network modules and consists of three processes that communicate via RPCs: a network simulator process, a host process, and a remote procedure monitor (RPM) process. The network simulator process pseudocode shows how it simulates message passing between the host and RPM processes and controls message loss based on configurable probability and duration parameters.