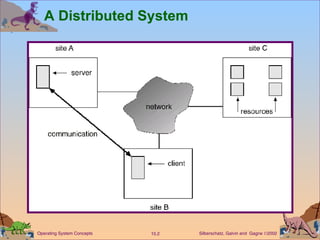
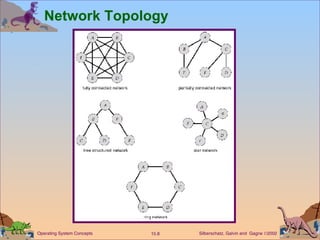
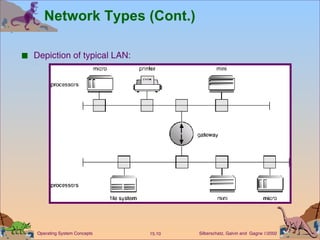
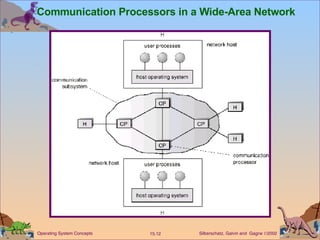
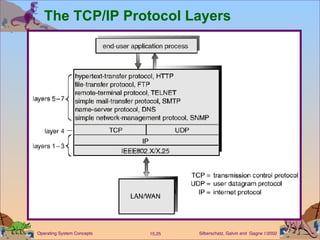
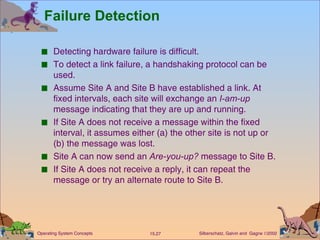
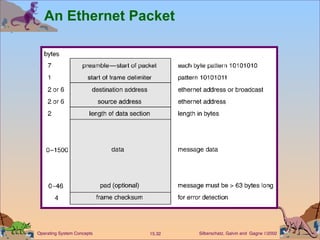
This document discusses distributed systems and network structures. It begins by outlining the motivations for distributed systems like resource sharing and increased reliability. It then discusses different types of network topologies and how sites can be physically connected. The document also covers network types like local area networks and wide area networks. It discusses important aspects of communication over networks like naming, routing, connections, and contention. Design strategies for robustness like failure detection and reconfiguration are also summarized.