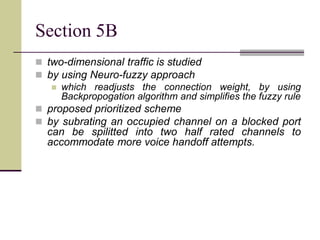
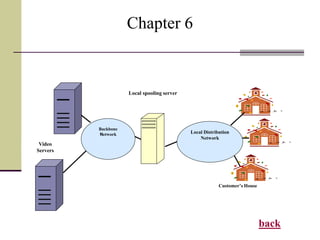
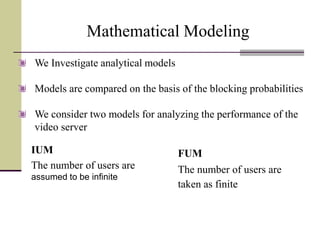
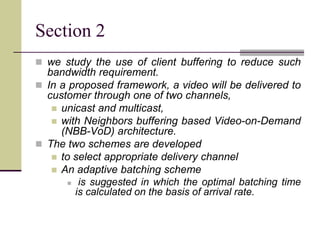
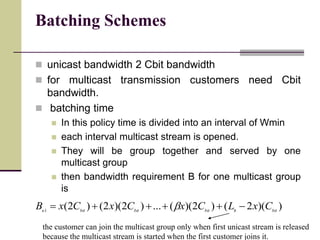
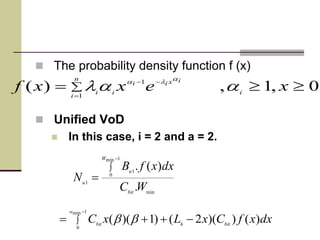
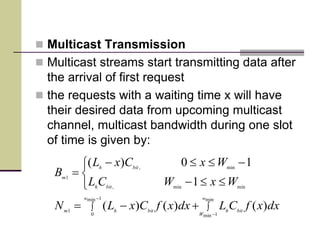
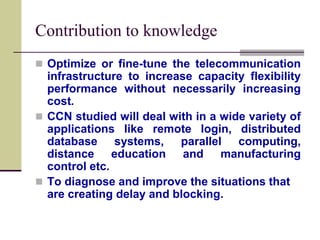
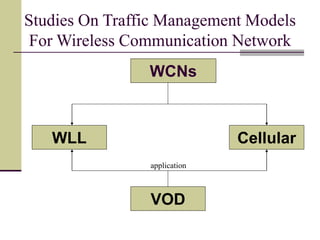
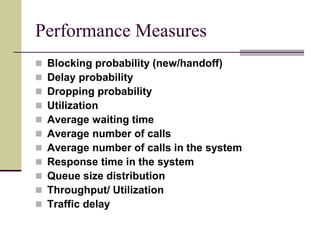
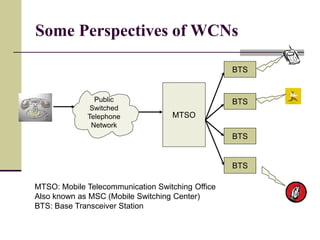
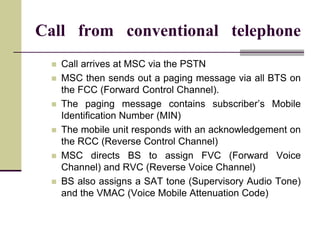
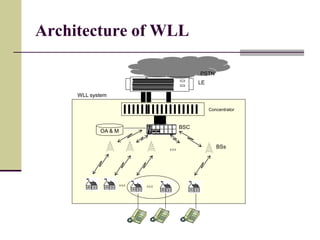
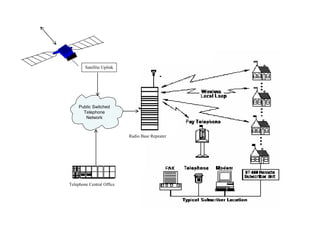
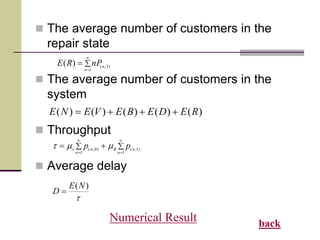
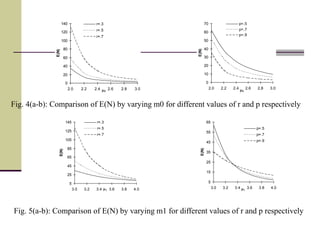
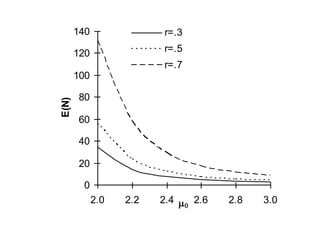
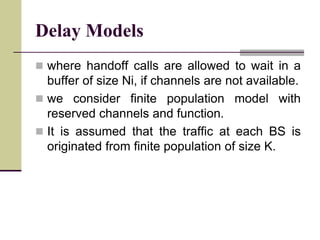
This document presents a study on traffic management models for wireless communication networks. It contains 7 chapters that analyze performance of different aspects of wireless networks like wireless local loop systems, cellular networks, and video on demand applications. The introduction chapter discusses motivation, performance modeling, traffic management techniques, and performance measures for wireless communication networks. It aims to ensure information exchange with optimal quality of service anywhere and anytime.
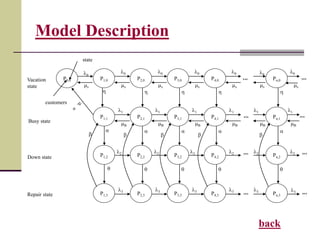
![IDMS
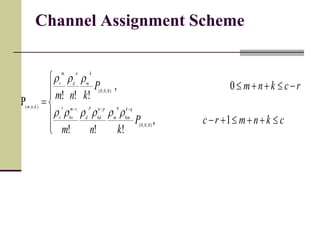
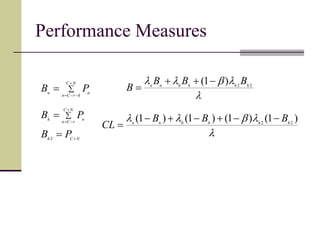
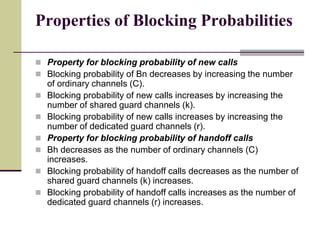
iiiiicn
j
Di
ic
i
icn
cehandoffvoii
ic
isj
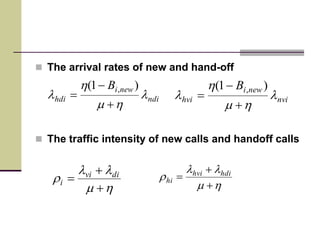
newiihandoffi
is
iiin
n
isj
newiihandoffi
is
iin
n
i
ni
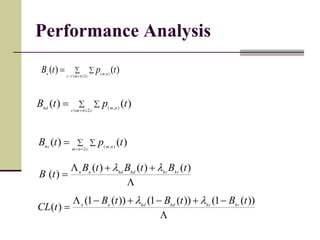
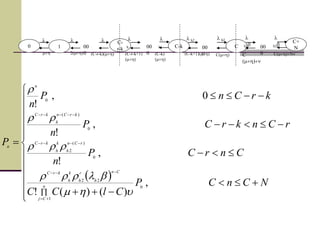
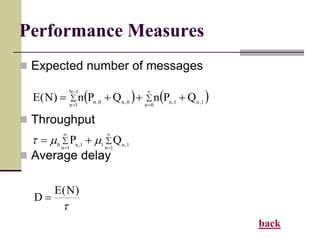
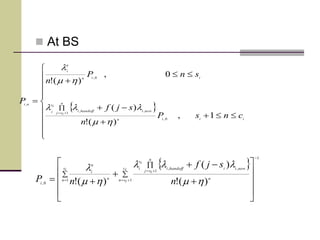
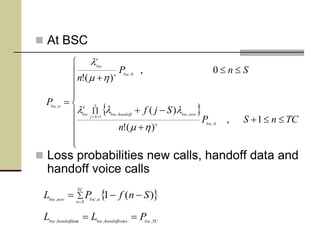
NcncP
jcc
sjf
cnsP
n
sjf
snP
n
P
1
)]()([)(!
)(
1,
)(!
)(
0,
)(!
,0,
0
,
1
,,
0,
1
,,
0,
,
hmhmhm
llll
hm
lll
hm
l
iNic
icn
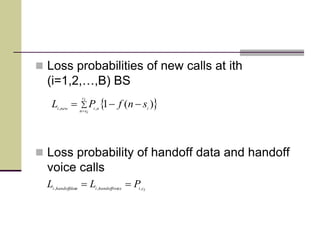
ni
ic
isn
ininewi
PsnfPD 1
,,,
)(1
iiNic
icn
niahandoffdati
PD ,, iNicicehandoffvoii
PD
,,
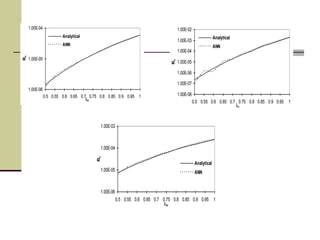
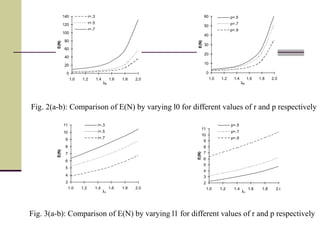
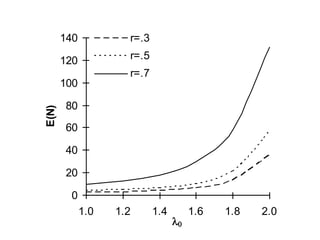
Numerical Result](https://image.slidesharecdn.com/thesis-191021052304/85/Studies-On-Traffic-Management-Models-for-Wireless-Communication-Network-53-320.jpg)