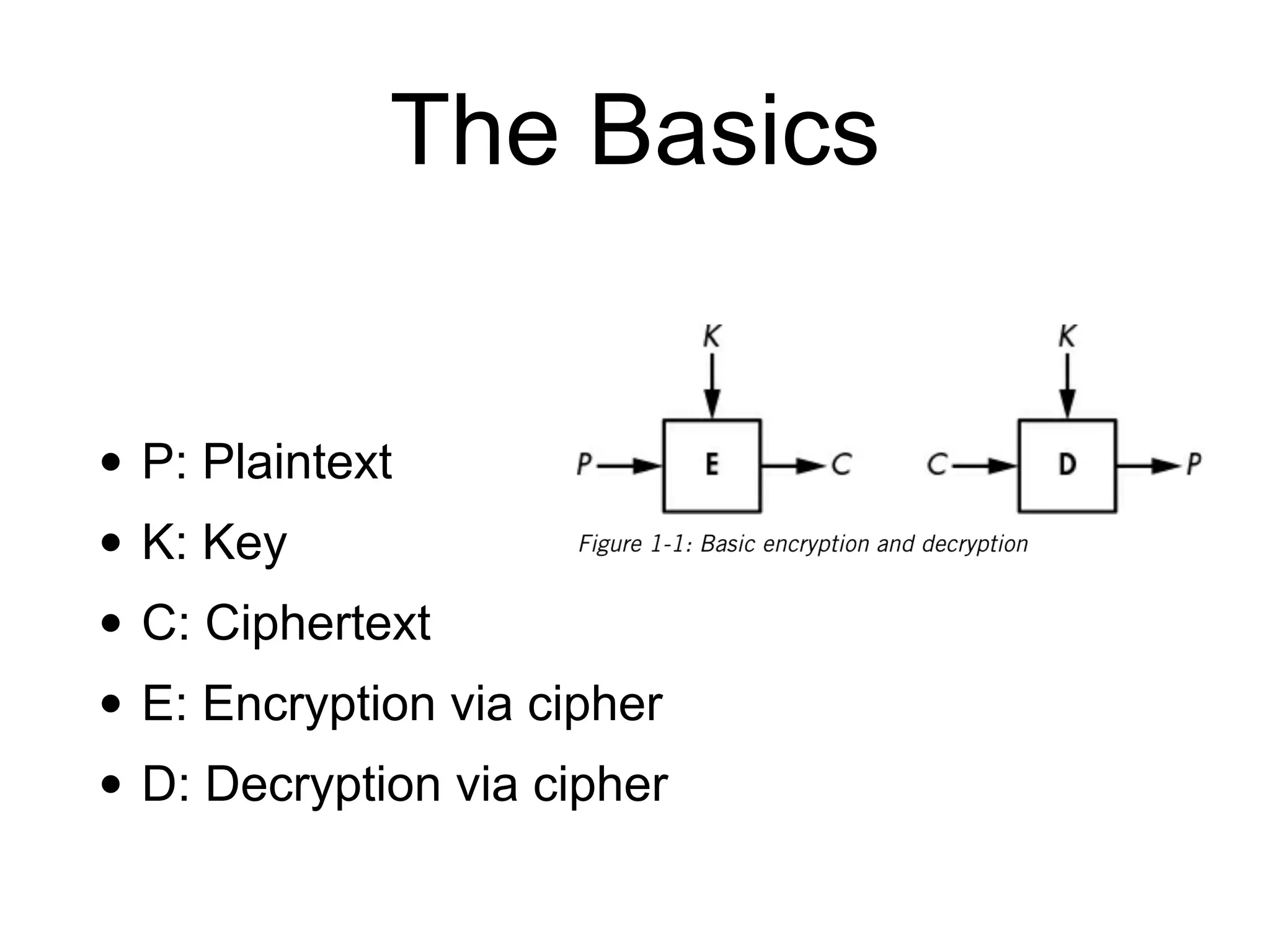
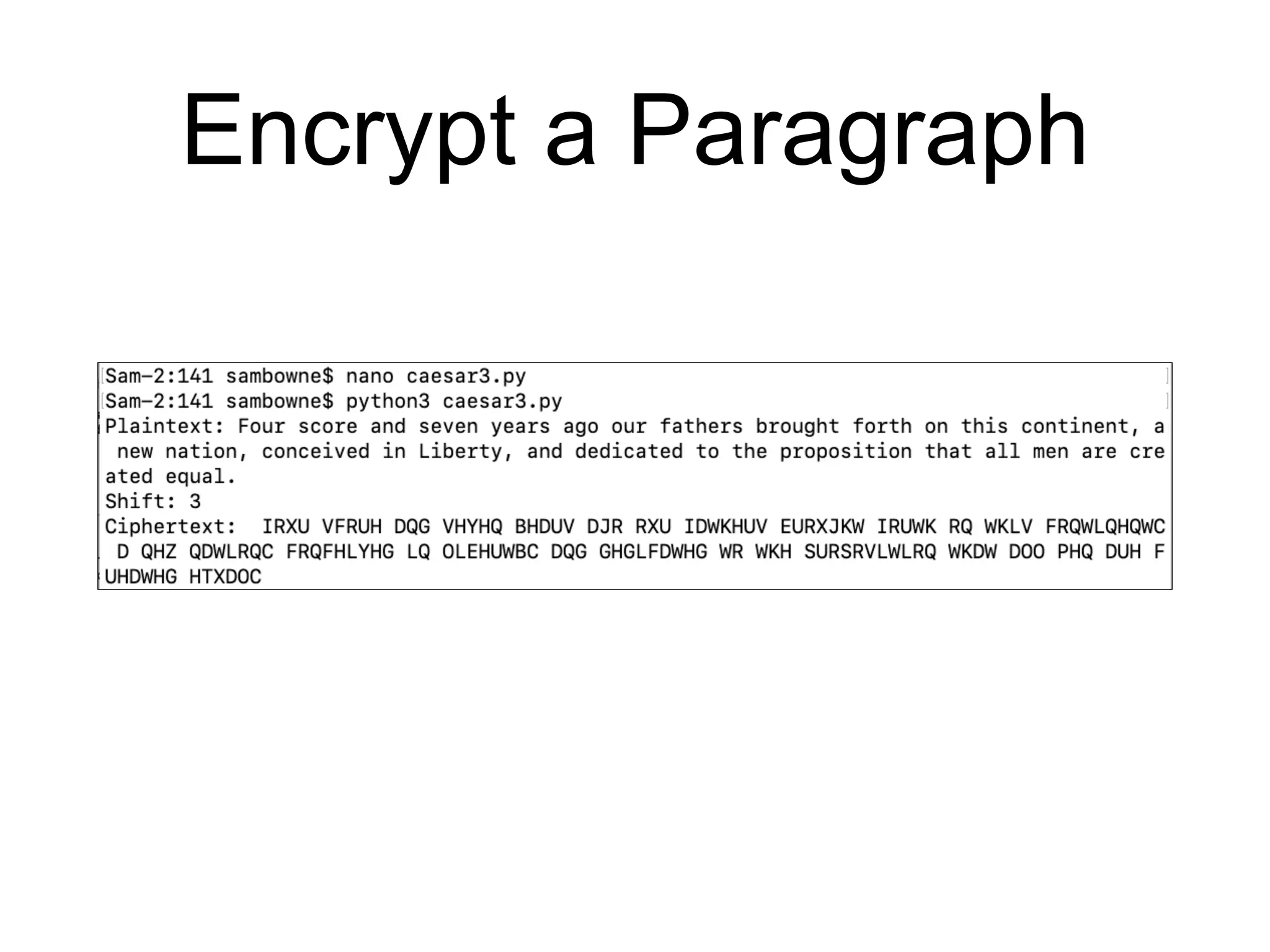
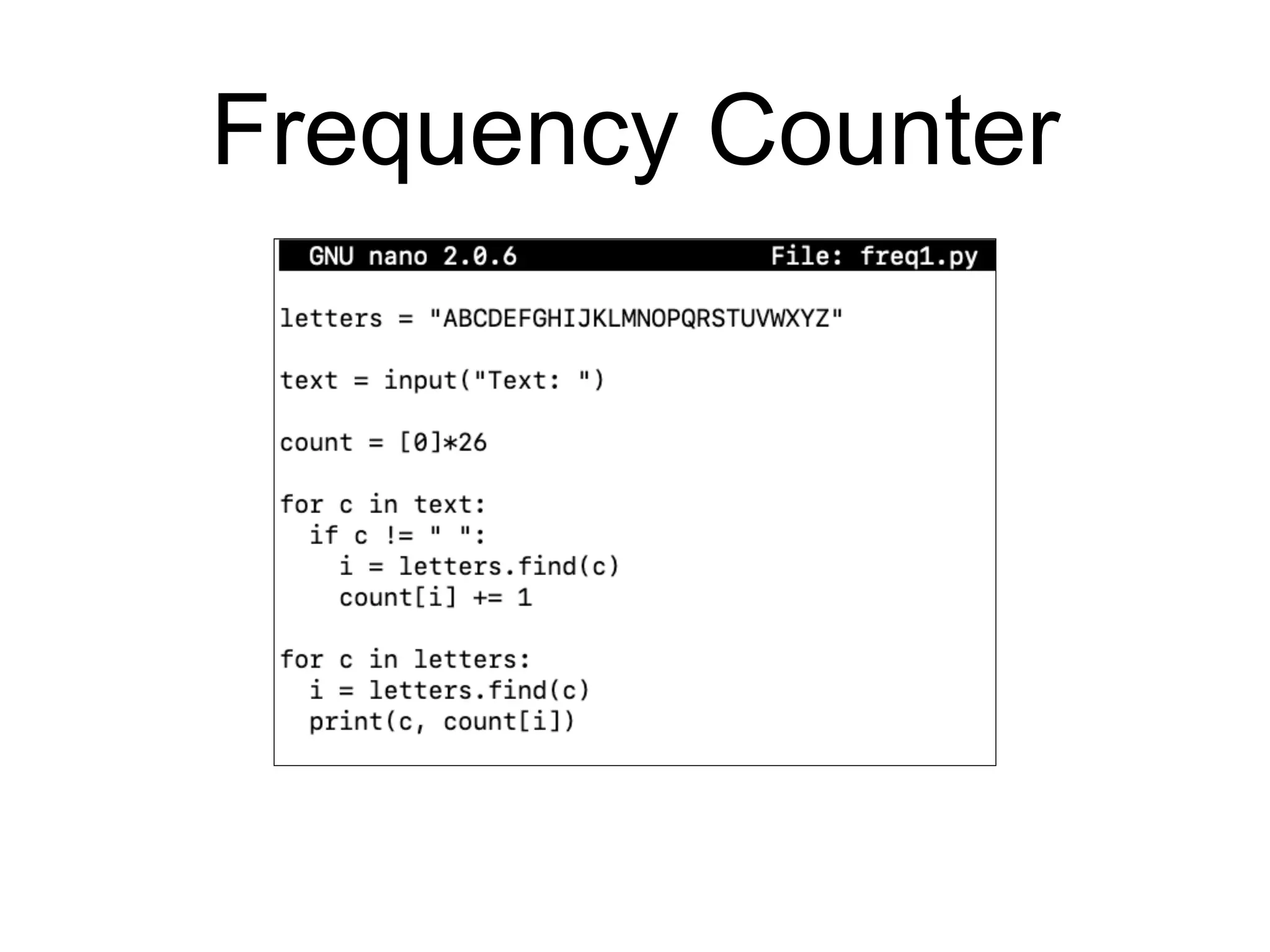
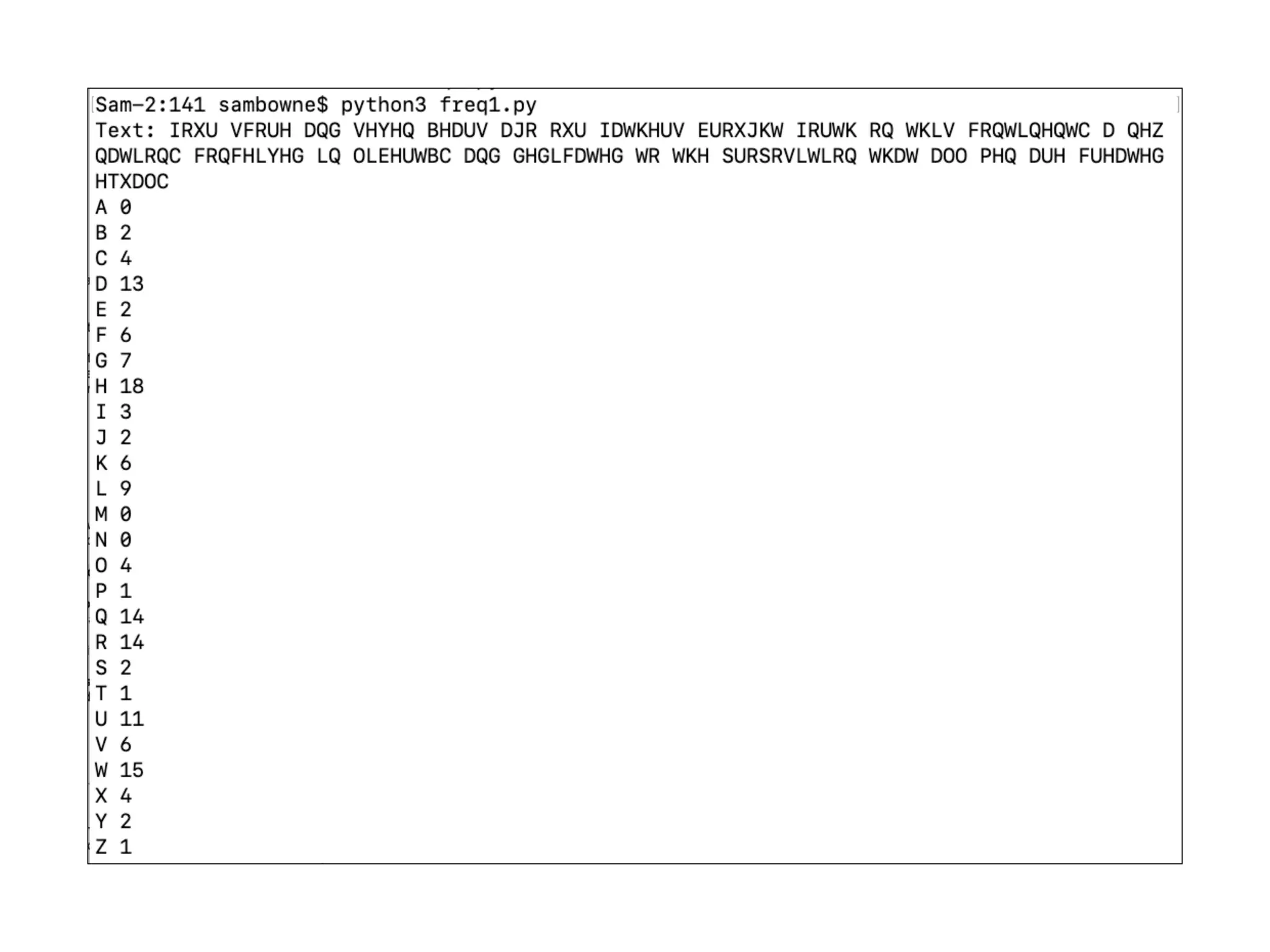
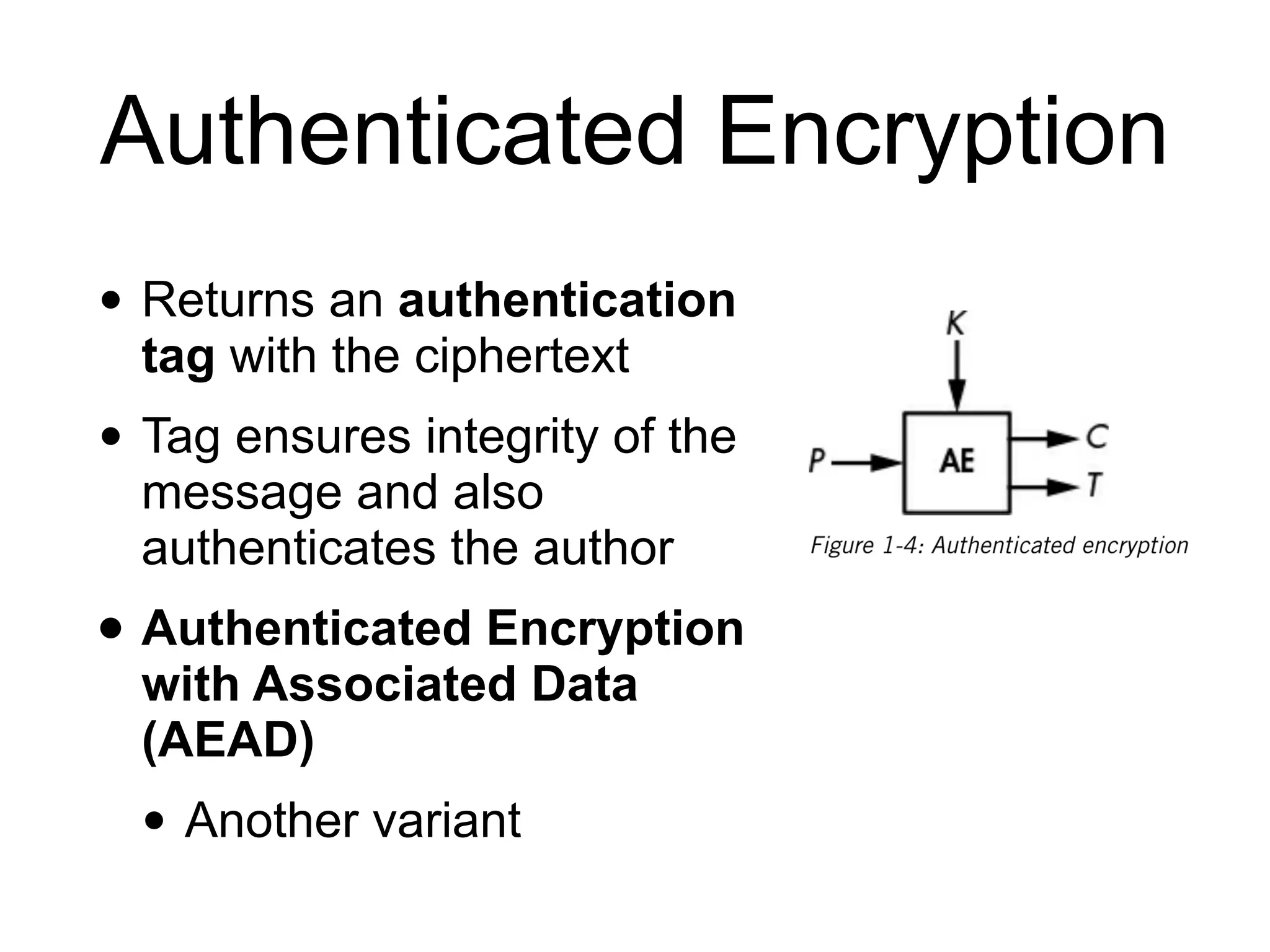
This document provides an overview of cryptography for computer networks. It discusses the basics of encryption including classical ciphers like the Caesar cipher and Vigenere cipher. It also covers perfect encryption using the one-time pad, encryption security models, asymmetric encryption, and how ciphers can be used for more than just encryption like authenticated encryption and format-preserving encryption. It concludes by discussing how implementations can sometimes go wrong if a weak cipher is used or the security model is incorrect.