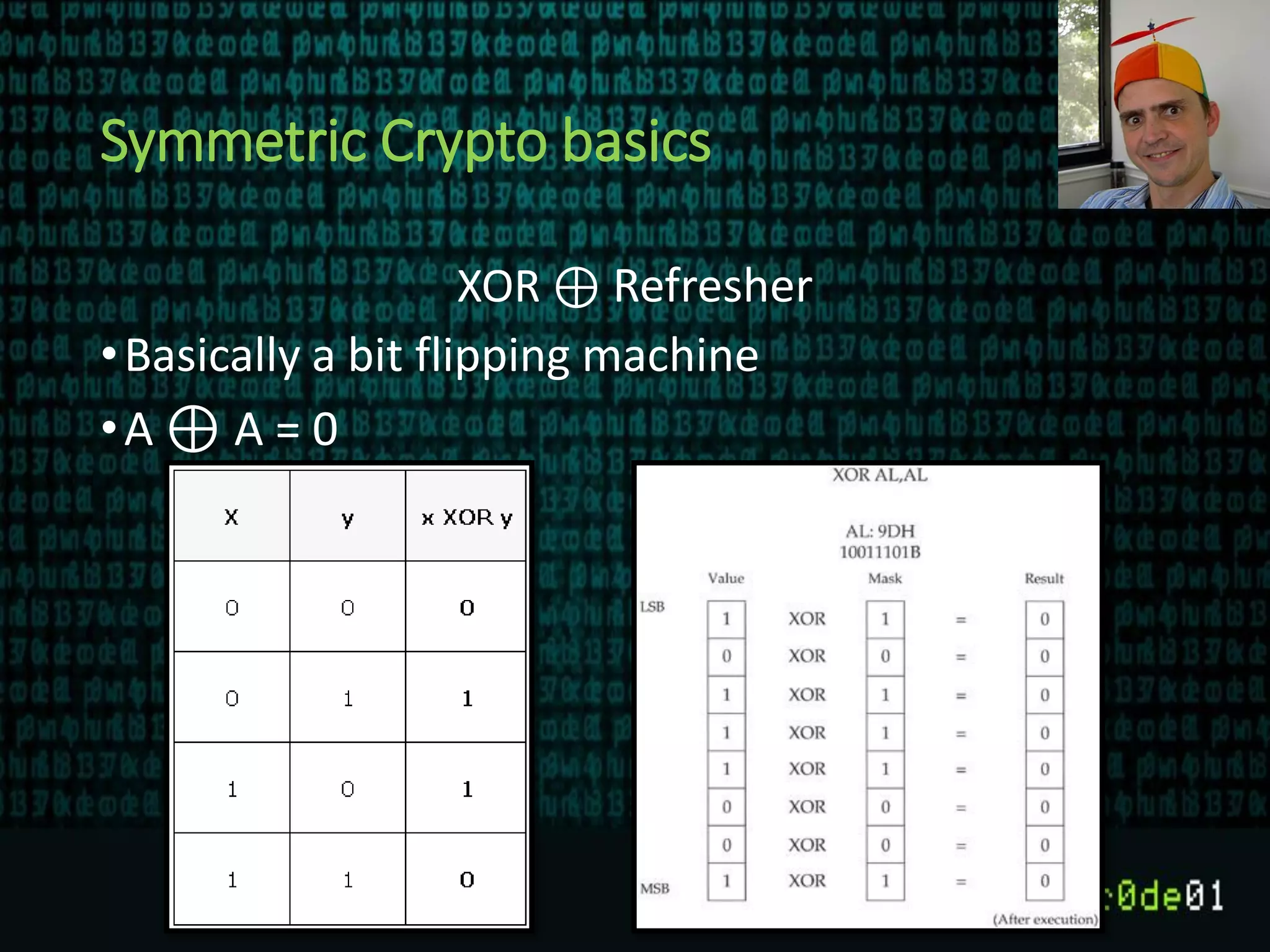
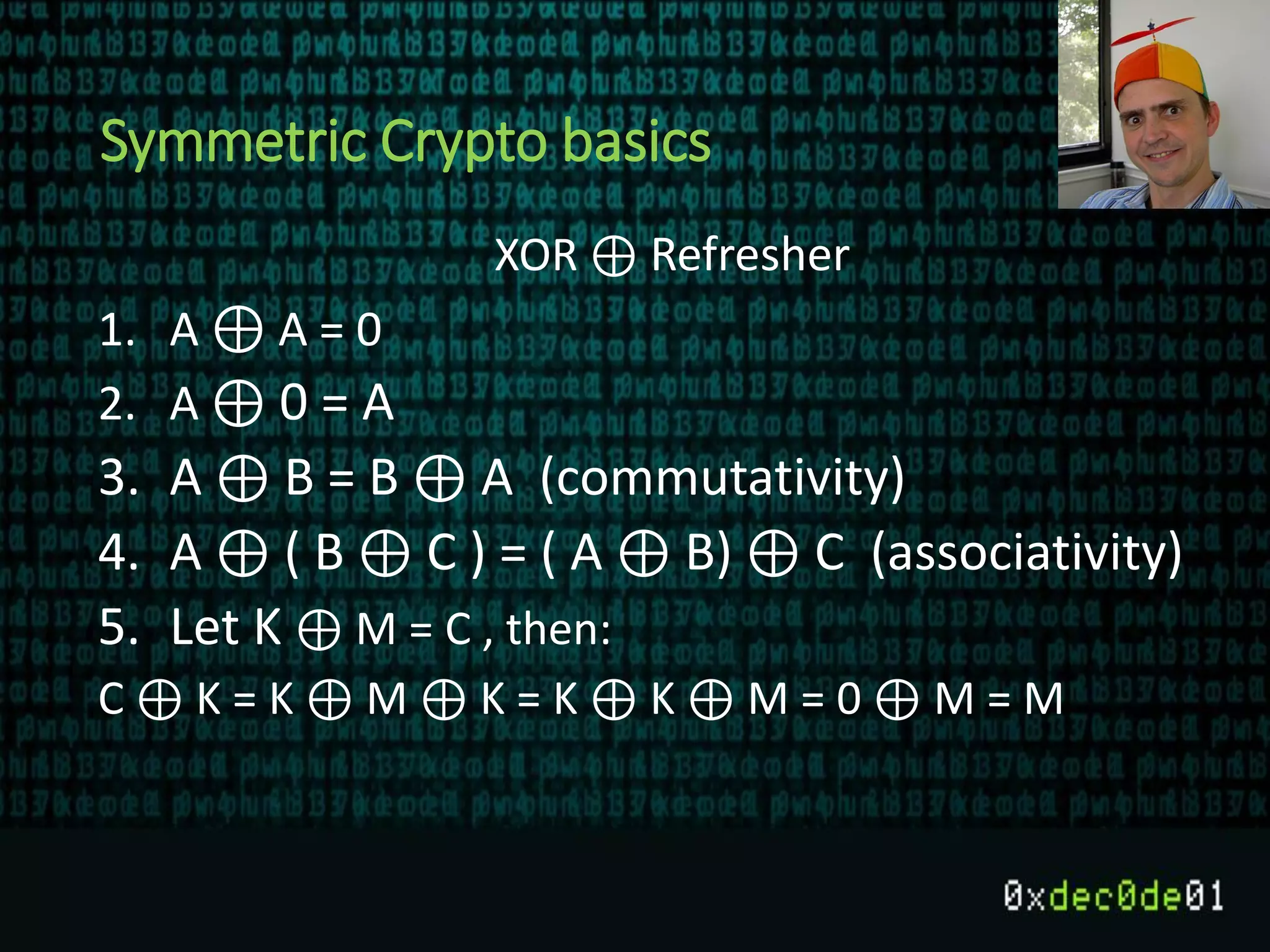
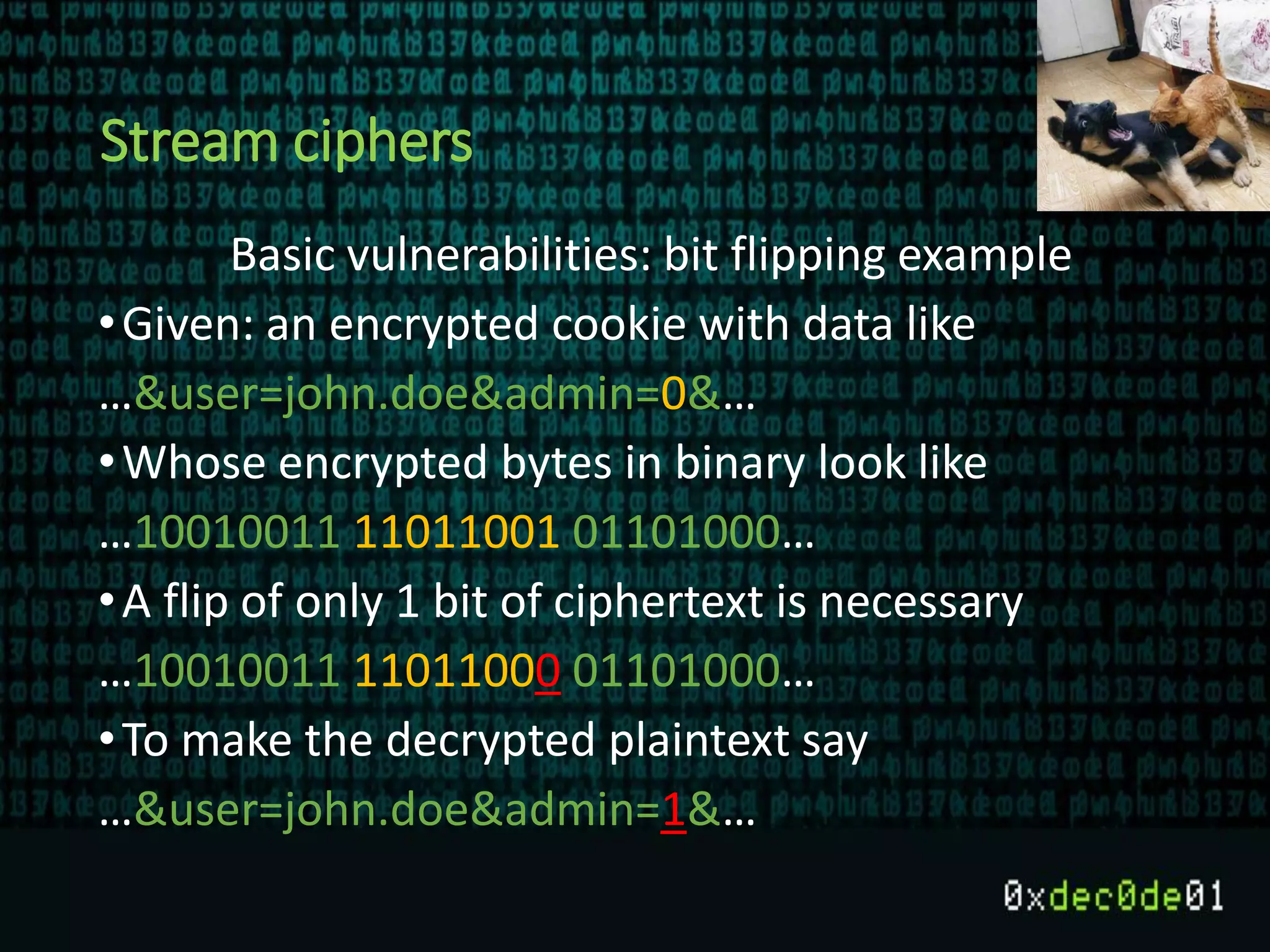
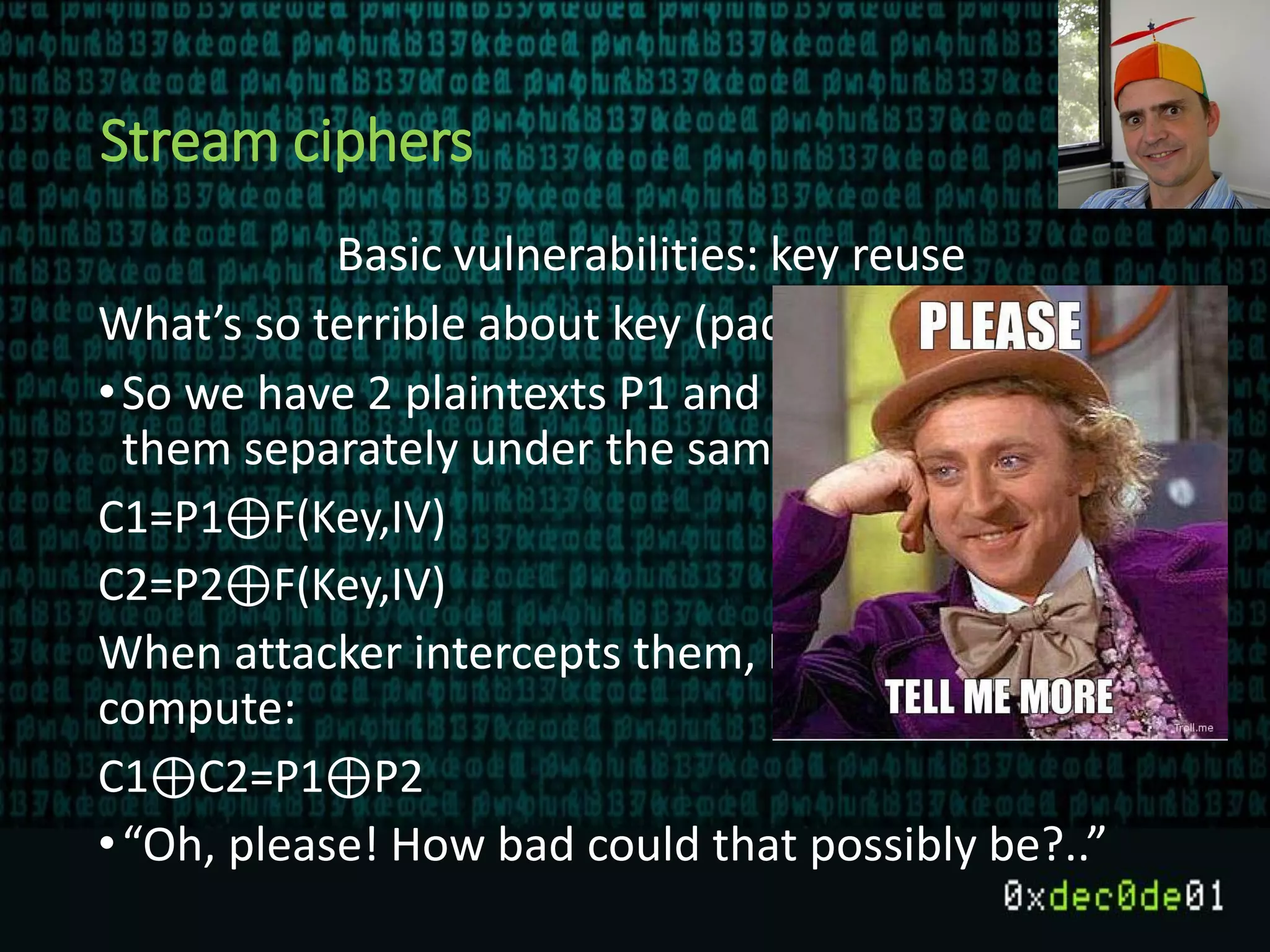
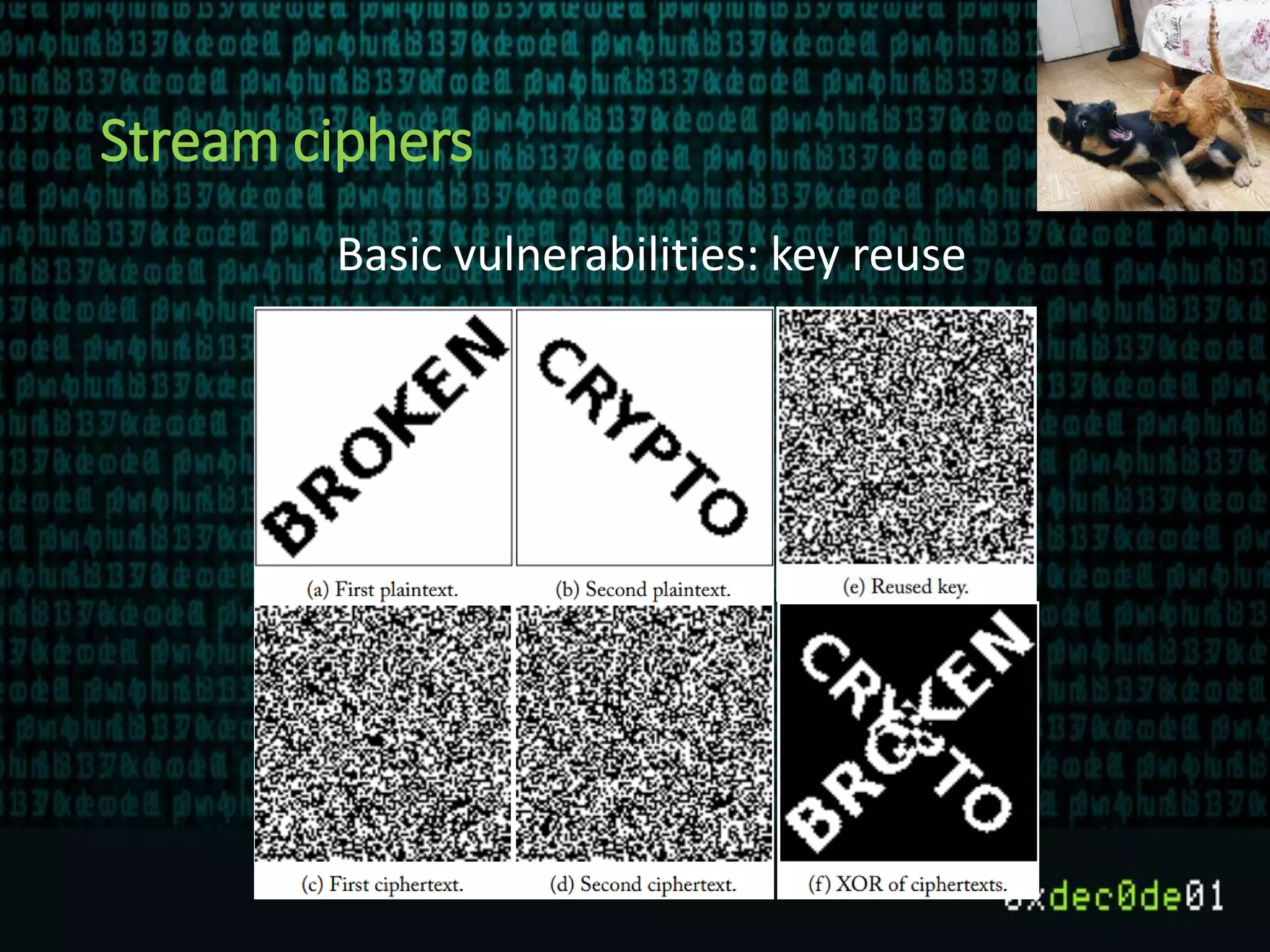
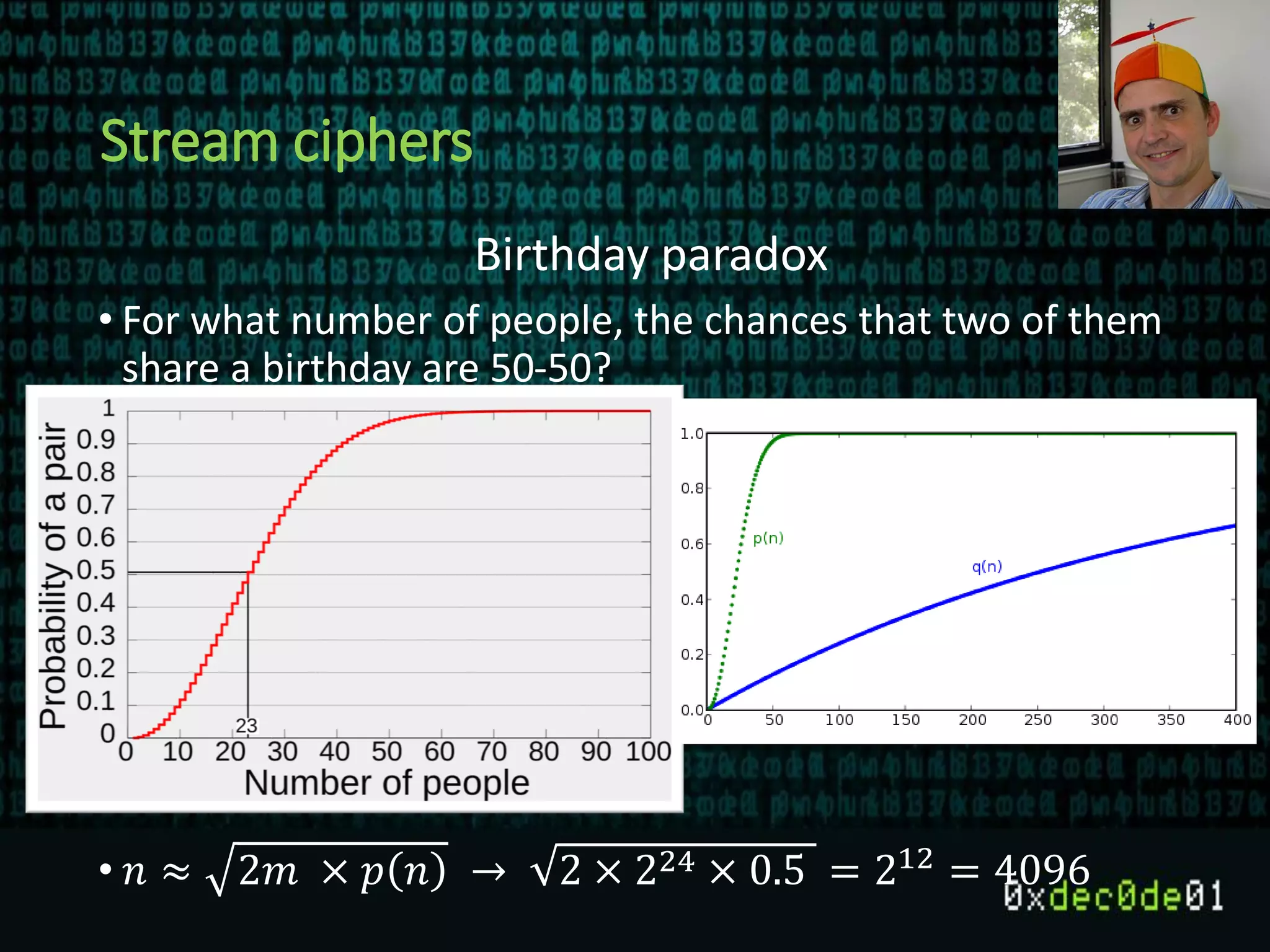
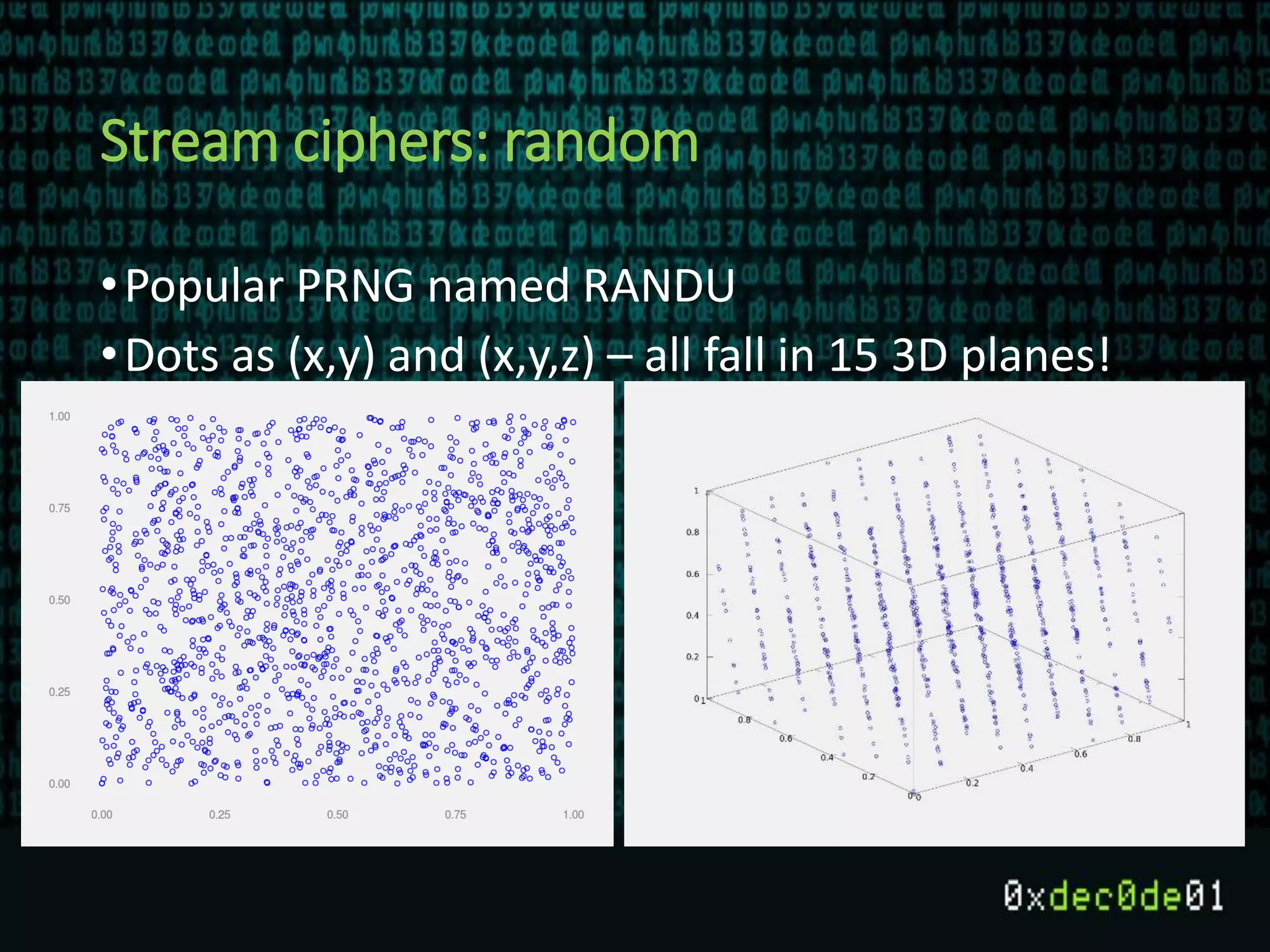
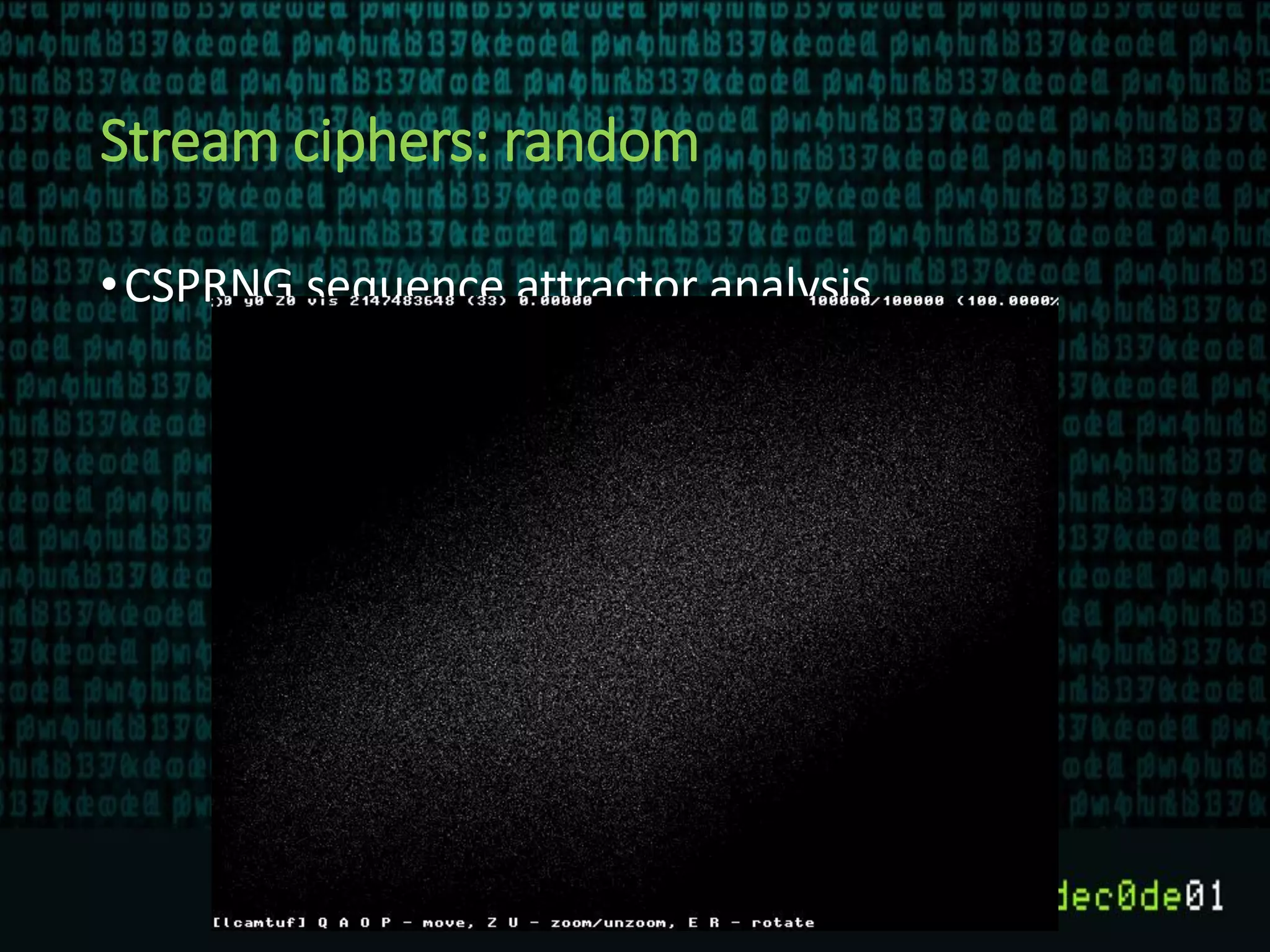
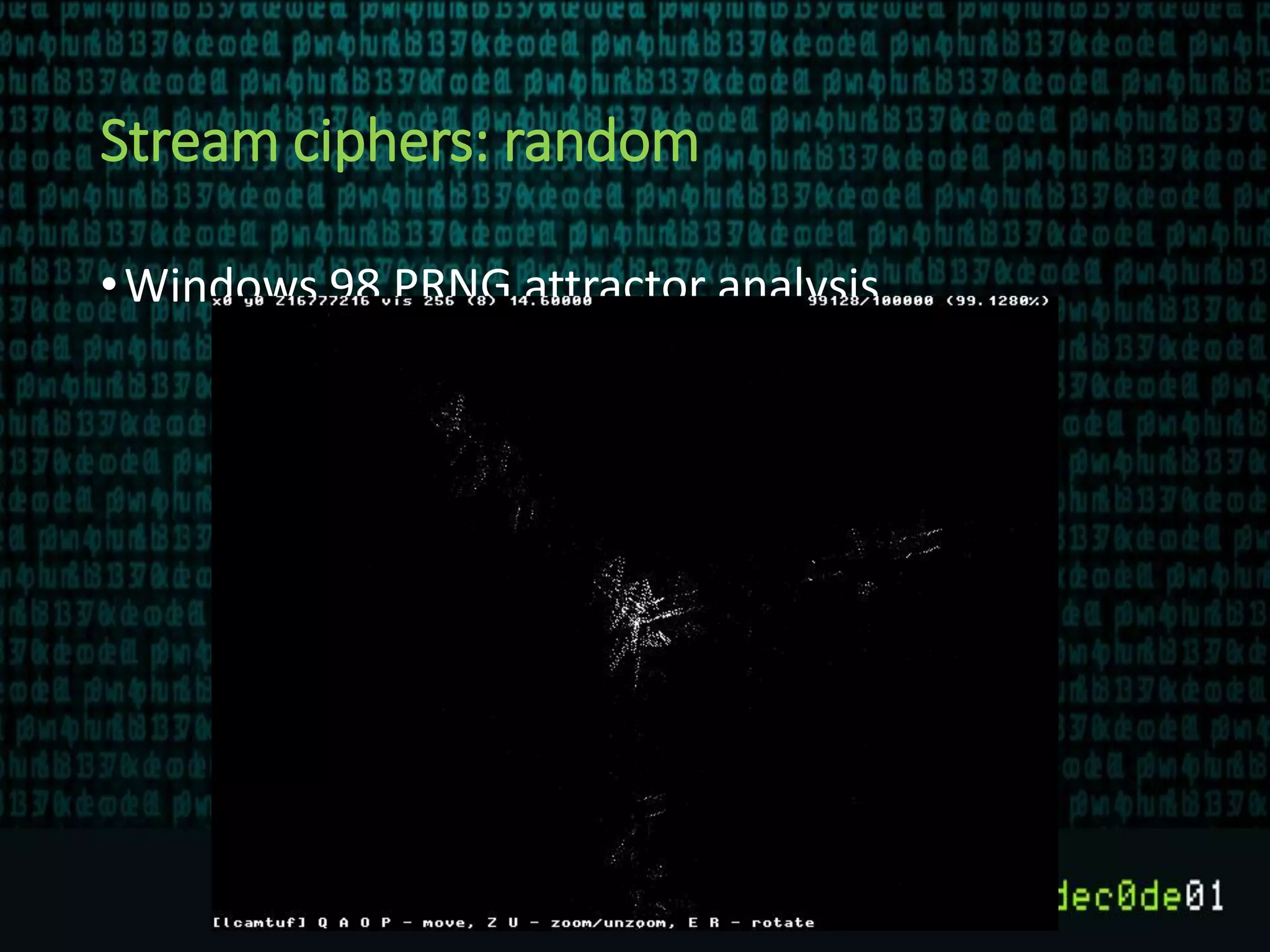
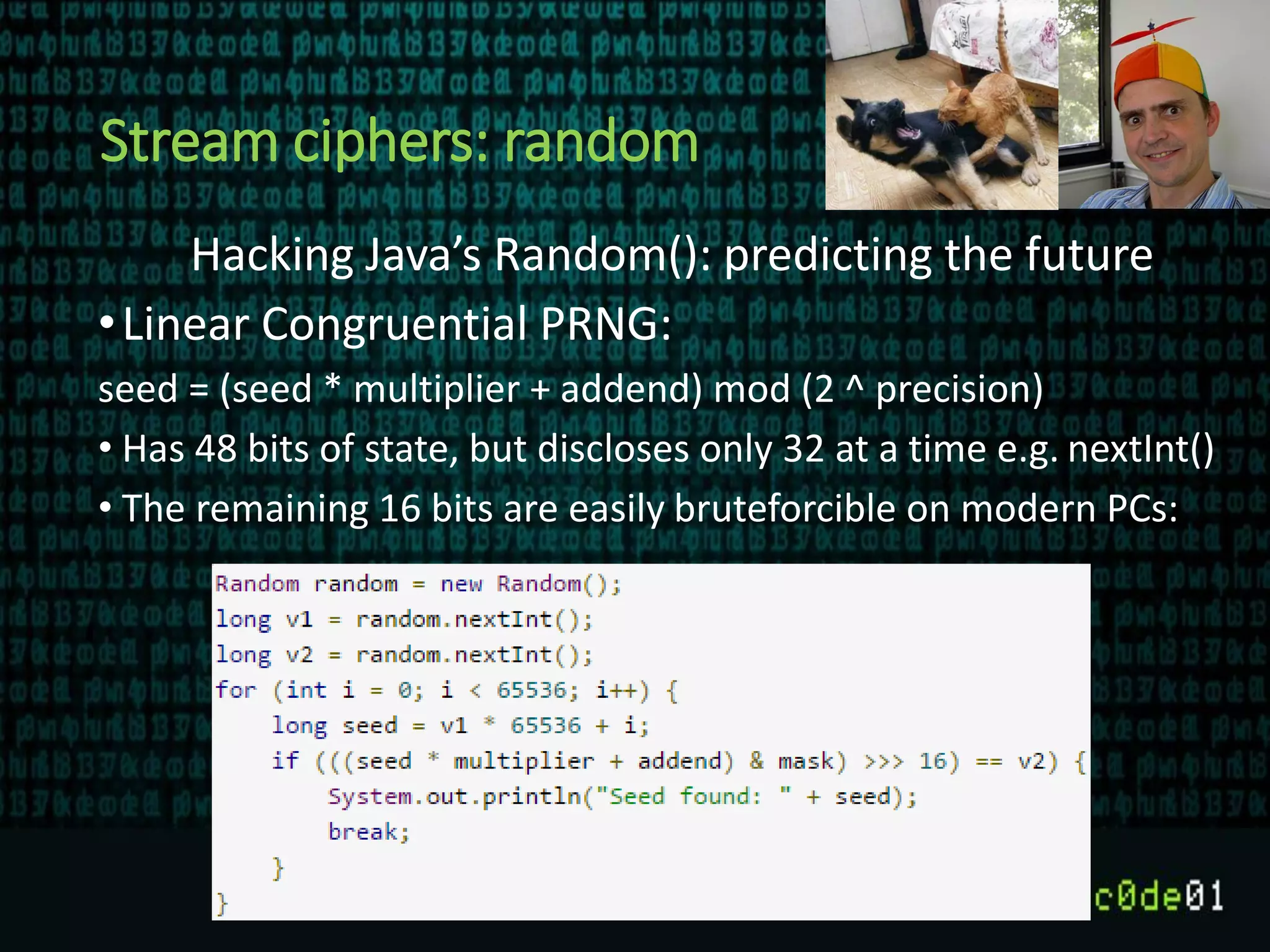
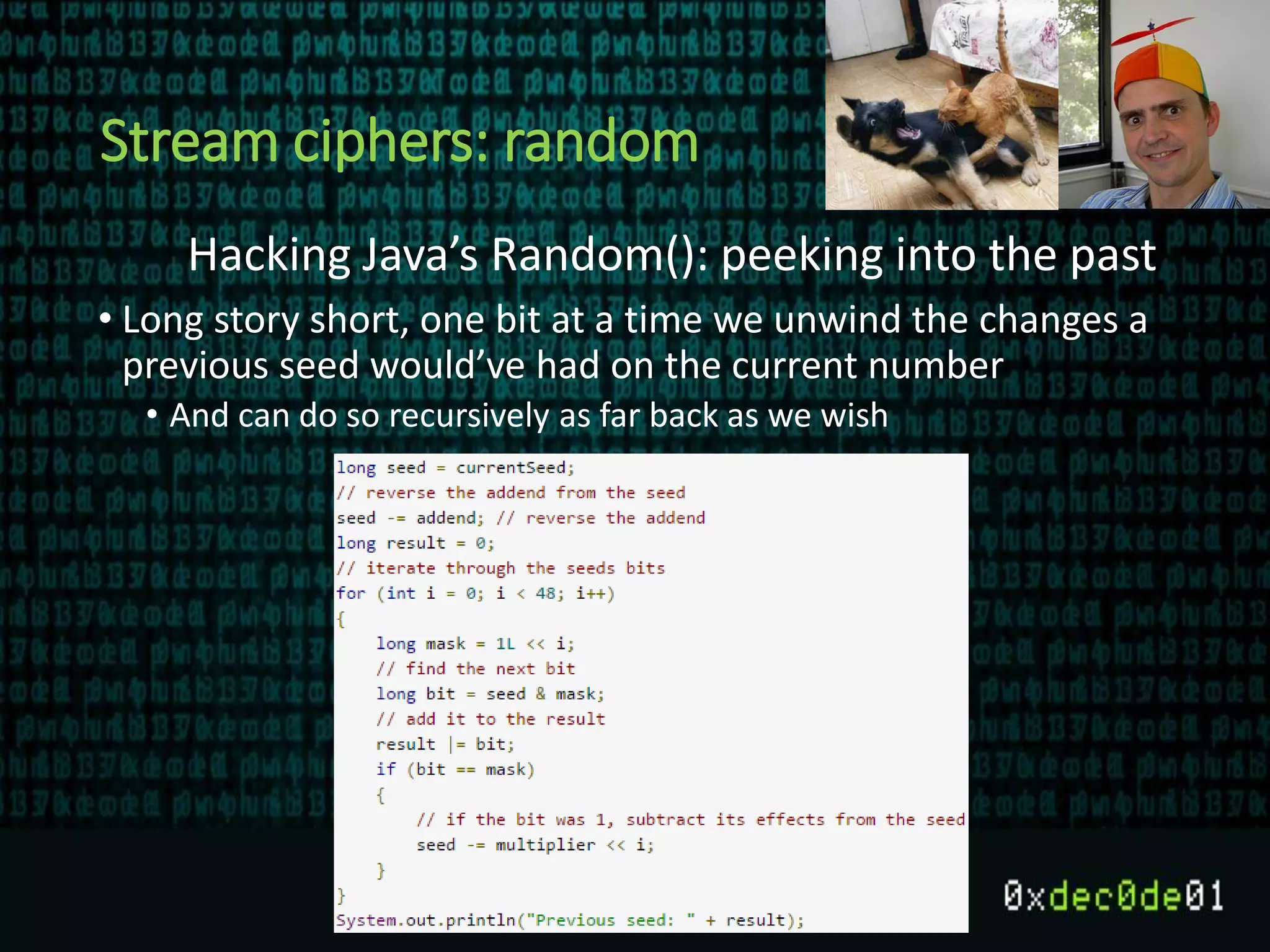
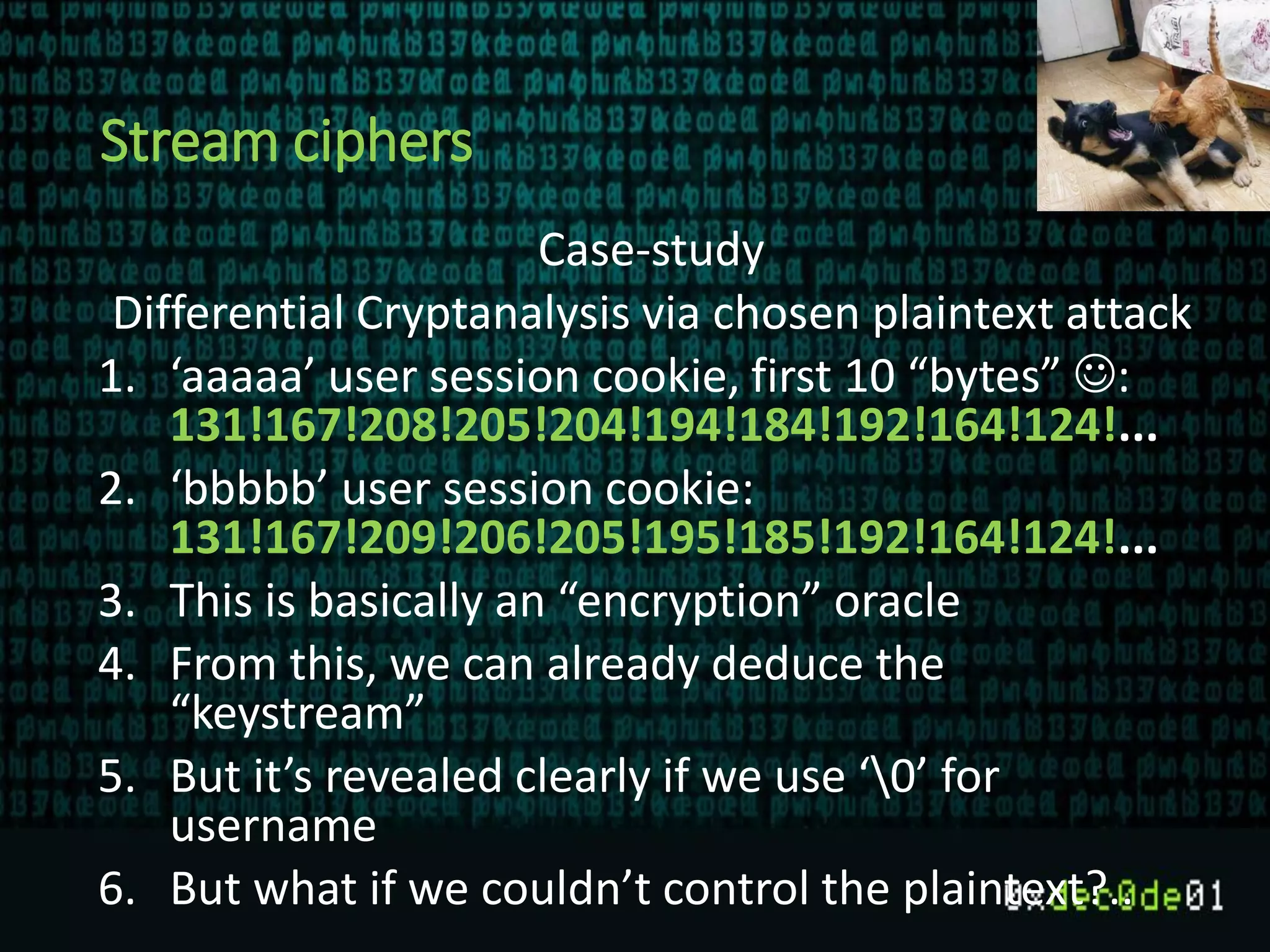
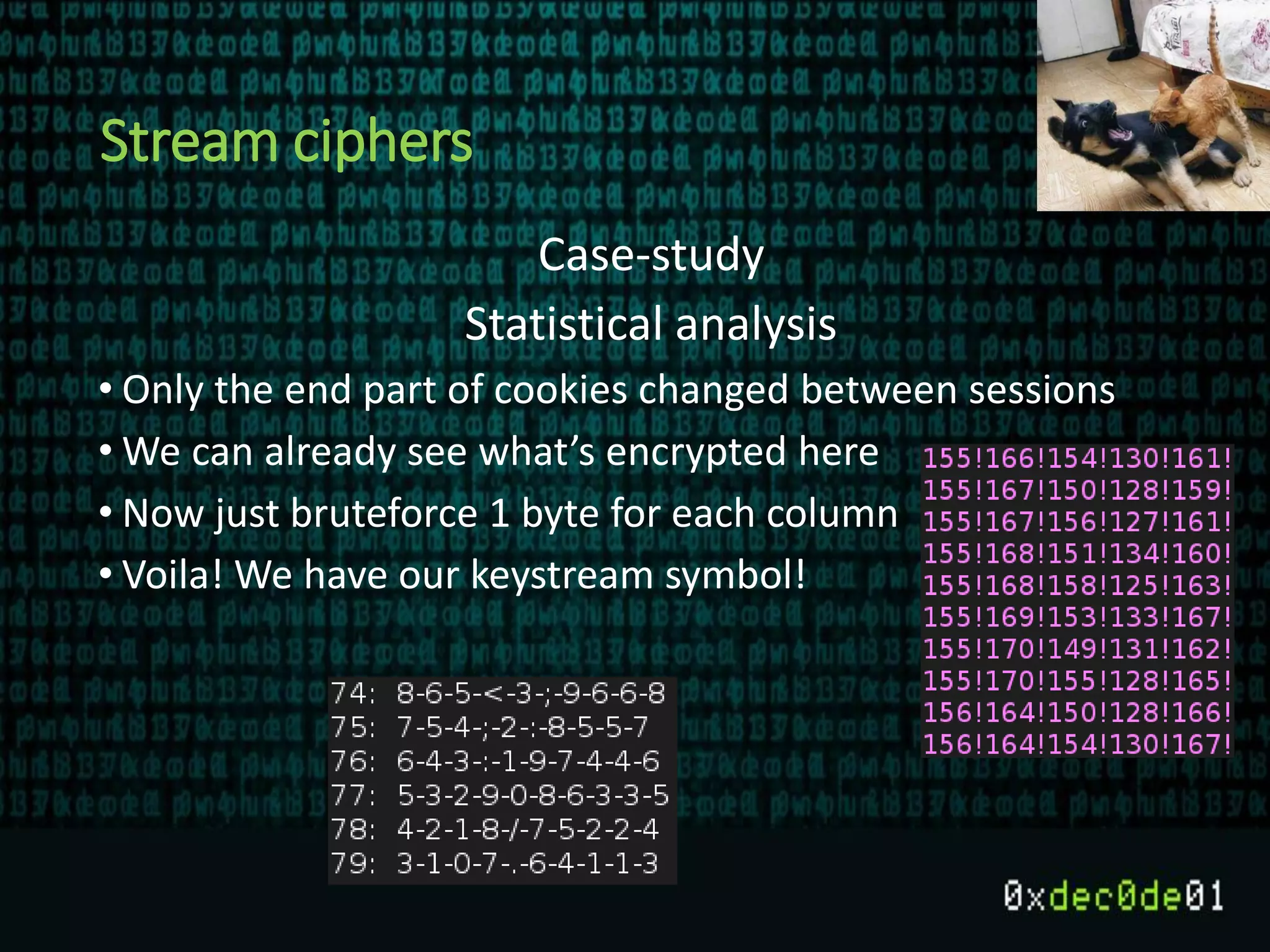
The document discusses the importance of understanding cryptography, particularly symmetric encryption and stream ciphers, detailing the methods of encryption and potential vulnerabilities such as key reuse and bit flipping. It emphasizes the necessity of using well-known cryptographic solutions instead of creating custom methods and highlights the significance of using secure random number generators for initialization vectors. Ultimately, it advocates for following best practices in cryptography to ensure data security.