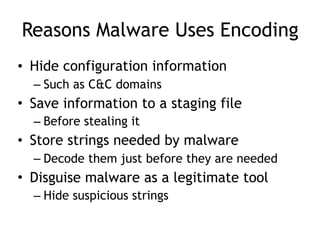
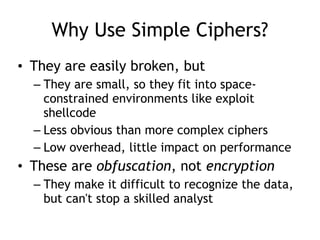
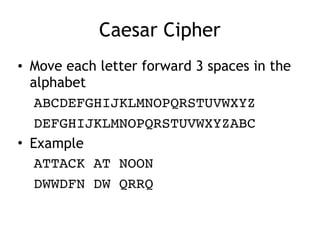
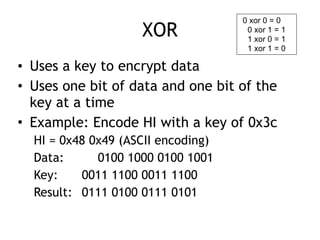
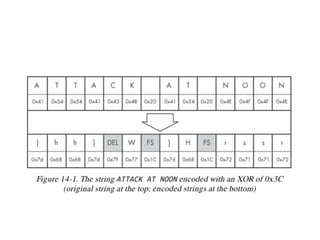
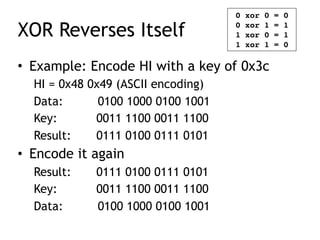
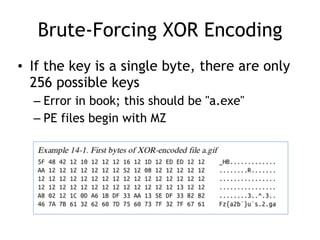
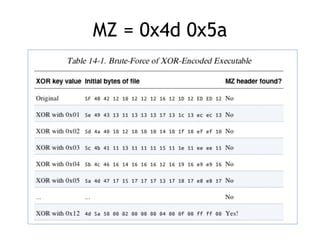
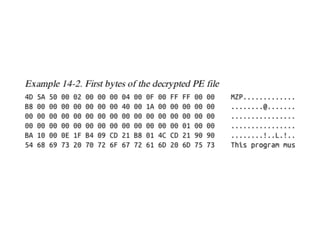
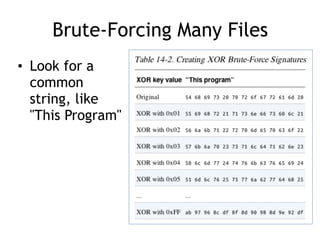
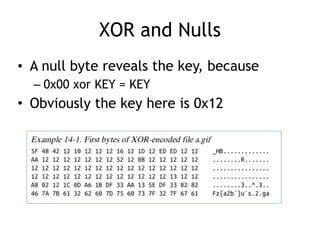
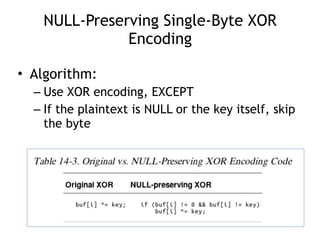
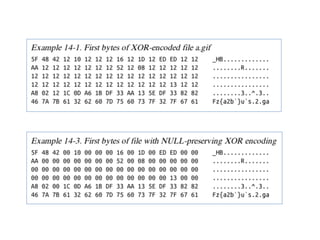
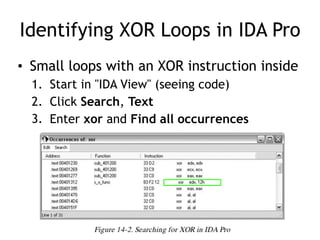
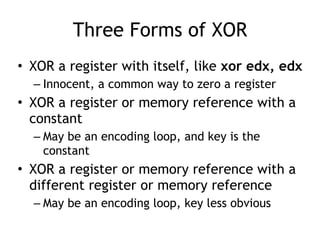
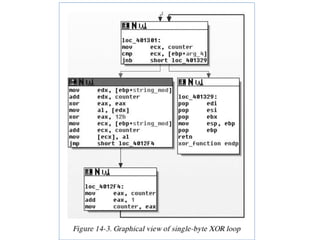
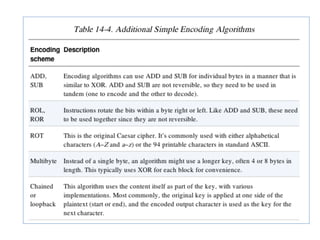
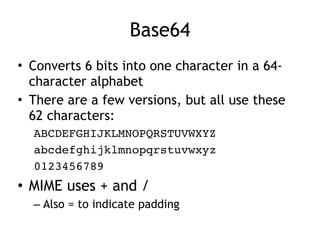
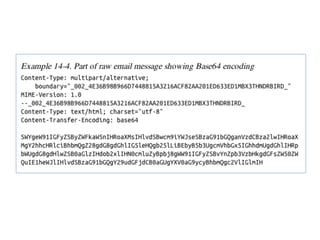
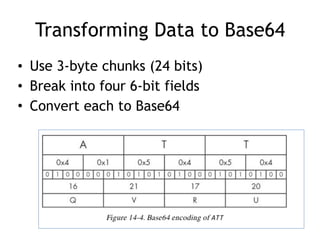
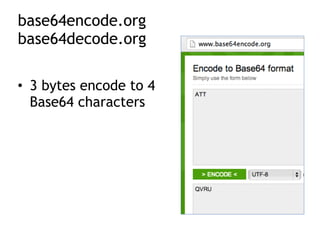
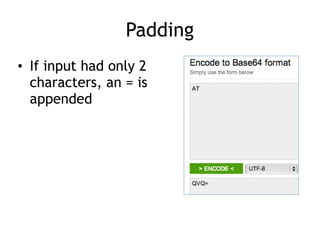
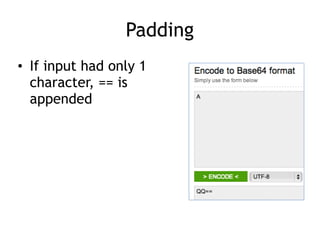
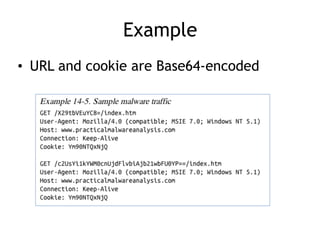
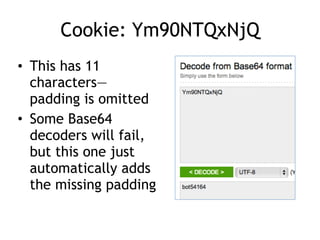
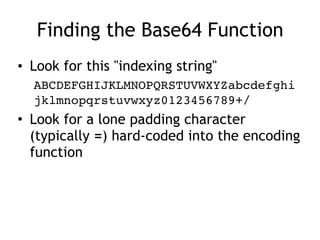
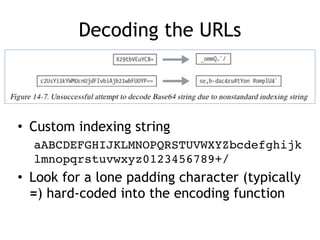
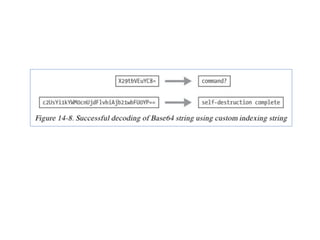
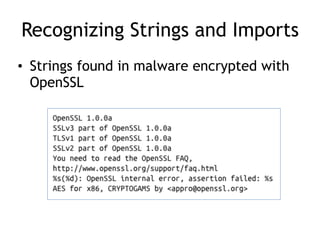
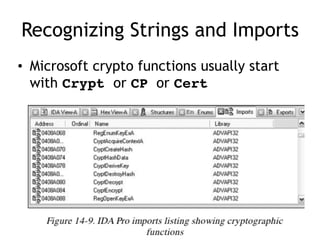
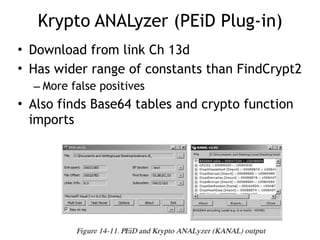
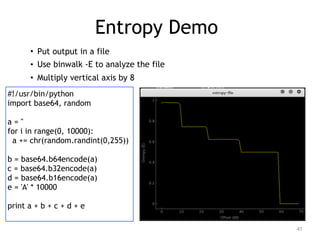
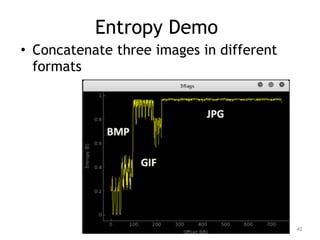
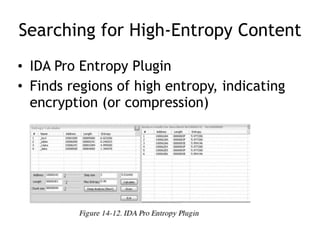
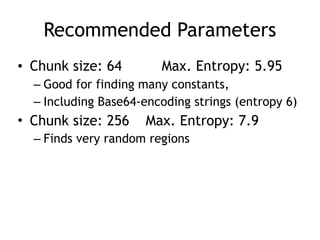
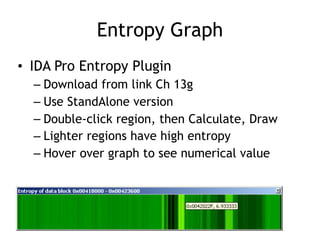
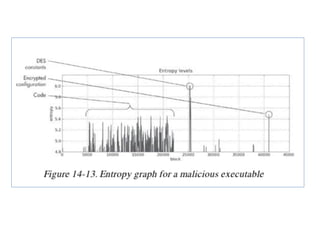
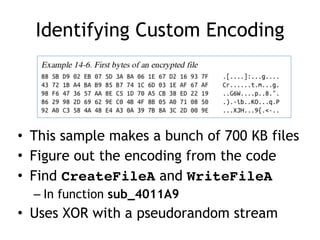
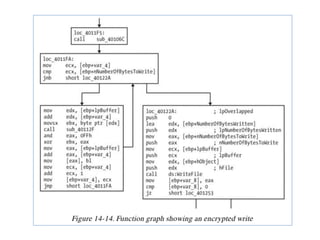
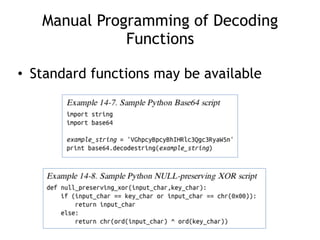
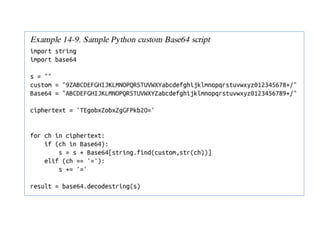
Chapter 13 of the practical malware analysis discusses various data encoding techniques used by malware to obfuscate information and avoid detection. It covers simple ciphers, XOR encoding, base64 encoding, and strong cryptographic algorithms, detailing their implementation and implications for malware analysis. The chapter also explores methods for identifying and reversing these encoding schemes, using tools like IDA Pro and various plugins to analyze entropy and detect malicious patterns.