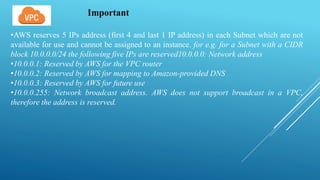
VPC allows users to create a virtual network in AWS that is logically isolated from other networks. It includes IP addresses, subnets, route tables, internet gateways, and security features. VPC supports private IP addresses that can only communicate within the VPC, public IP addresses reachable from the internet, and elastic IP addresses that can be attached and detached from instances. Subnets divide the VPC into distinct regions and cannot span availability zones. They can be configured as public or private depending on internet access. Route tables and security groups control network traffic flow. Network ACLs provide optional subnet level firewalls.