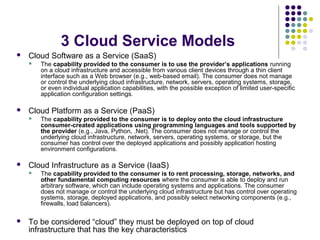
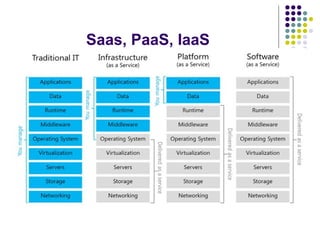
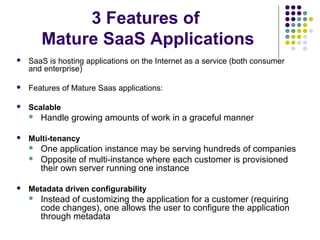
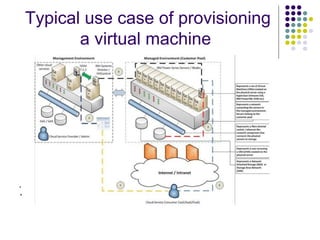
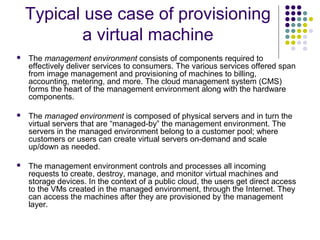
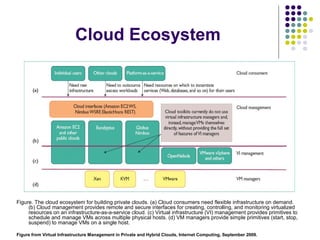
This document provides an overview of cloud computing models and platforms. It defines cloud computing and describes its key characteristics, service models, and deployment models. The objectives of cloud computing are discussed, including elasticity, on-demand usage, and pay-per-use. Common cloud platforms like Amazon EC2, S3, and RDS are introduced along with how they provide infrastructure, platform, and software services. Virtual machine provisioning workflows on cloud platforms are outlined. The cloud ecosystem is depicted showing the relationship between cloud users, management, and virtual infrastructure layers.