Cloud computing delivers computing services as utilities over the internet, similar to how electricity or water are provided. There are different types of cloud deployment models including public, private, hybrid, and community clouds. Additionally, there are three main service models - Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). IaaS provides virtual computing resources, PaaS provides development platforms, and SaaS provides complete software solutions delivered over the internet. Cloud computing offers benefits like on-demand provisioning, elastic scaling, pay-per-use billing, workload resilience, and migration flexibility.















![Service
A cloud service includes "products, services and solutions that are delivered and consumed in
real-time over the Internet". For example, Web Services ("software system[s] designed to support
interoperable machine-to-machine interaction over a network") which may be accessed by other
cloud computing components, software, e.g., Software plus service, or end users directly. Specific
examples include:
Identity (OAuth, OpenID)
Integration (Amazon Simple Queue Service)
Payments (Amazon Flexible Payments Service, Google Checkout, PayPal)
Mapping (Google Maps, Yahoo! Maps)
Search (Alexa, Google Custom Search, Yahoo! BOSS)
Others (Amazon Mechanical Turk)
Storage
Cloud storage involves the delivery of data storage as a service, including database-like services,
often billed on a utility computing basis, e.g., per gigabyte per month. For example:
Database (Amazon SimpleDB, Google App Engine's BigTable datastore)
Network attached storage (MobileMe iDisk, Nirvanix CloudNAS) Synchronization (Live
Mesh Live Desktop component, MobileMe push functions)
Web service (Amazon Simple Storage Service, Nirvanix SDN)
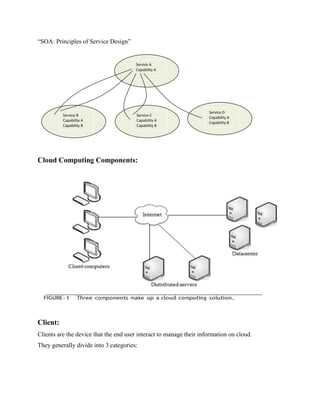
Cloud computing architecture
Cloud computing architecture refers to the components and subcomponents required for cloud
computing. These components typically consist of a front end platform (fat client, thin client,
mobile device), back end platforms (servers, storage), a cloud based delivery, and a network](https://image.slidesharecdn.com/unit5-180608162715/85/cloud-computing-17-320.jpg)


![4. flex tenancy
Of these, flex tenancy is considered the most user adaptive SaaS paradigm in designated multi-
input four way manifold models.[8]
Such systems are based on simplified encryption methods that
target listed data sequences over multiple passes.[9]
The simplicity of this concept makes flex
tenancy SaaS popular among those without informatics processing experience, such as basic
maintenance and custodial staff in franchise businesses.
Development as a service (DaaS)
Development as a service is web based, community shared development tools. This is the
equivalent to locally installed development tools in the traditional (non-cloud computing) delivery
of development tools.
Data as a service (DaaS)
Data as a service is web-based design construct where by cloud data is accessed through some
defined API layer. DaaS services are often considered as a specialized subset of a Software as a
service offering.
Platform as a service (PaaS)
Platform as a service is cloud computing service which provides the users with application
platforms and databases as a service. This is equivalent to middleware in the traditional (non-cloud
computing) delivery of application platforms and databases.
Infrastructure as a service (IaaS)
Infrastructure as a service is taking the physical hardware and going completely virtual (e.g. all
servers, networks, storage, and system management all existing in the cloud). This is the equivalent
to infrastructure and hardware in the traditional (non-cloud computing) method running in the
cloud. In other words, businesses pay a fee (monthly or annually) to run virtual servers, networks,
storage from the cloud. This will mitigate the need for a data center, heating, cooling, and
maintaining hardware at the local level](https://image.slidesharecdn.com/unit5-180608162715/85/cloud-computing-20-320.jpg)

