This document discusses 8 cloud security mechanisms:
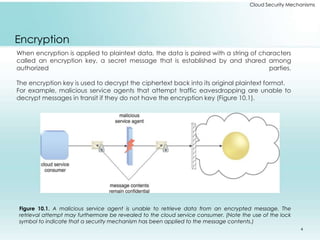
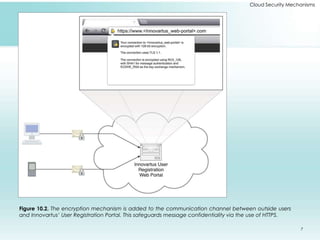
1. Encryption protects data confidentiality during transmission using encryption keys. Symmetric encryption uses one key while asymmetric uses two keys.
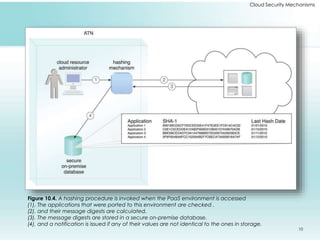
2. Hashing creates a unique code to verify data integrity and detect unauthorized changes using one-way functions.
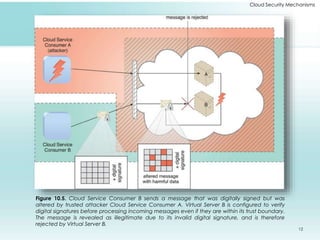
3. Digital signatures provide authentication and non-repudiation by encrypting a hash of a message with a private key.
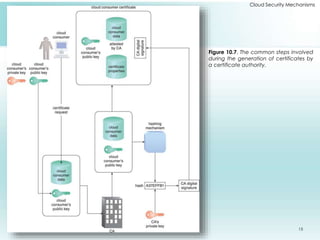
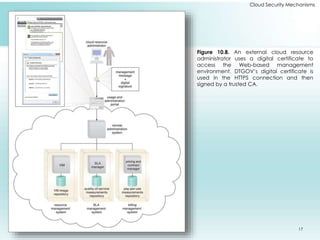
4. PKI uses digital certificates and certificate authorities to securely associate public keys with identities.
5. IAM controls user identities and access privileges using authentication, authorization, user management, and credential management.
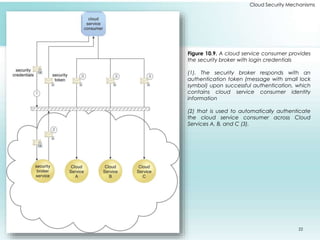
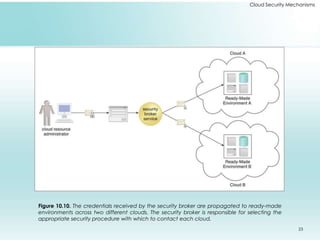
6. SSO allows single authentication across multiple services using tokens from a security broker.