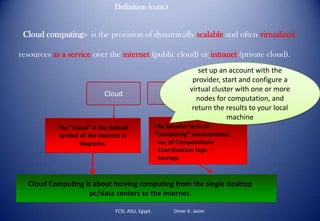
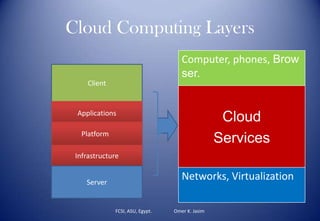
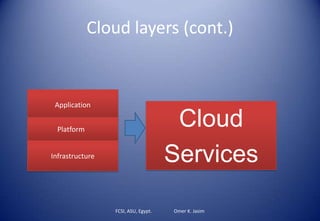
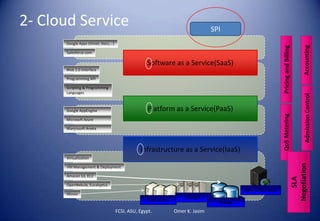
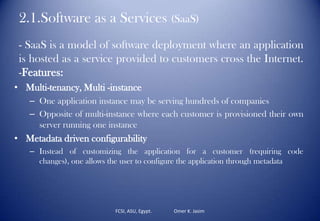
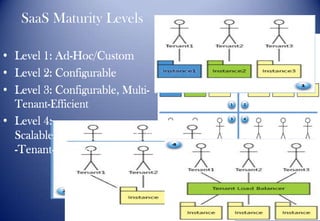
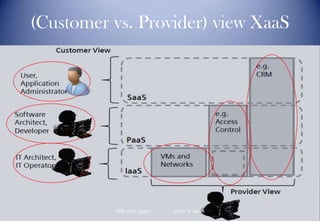
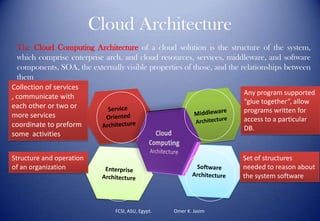
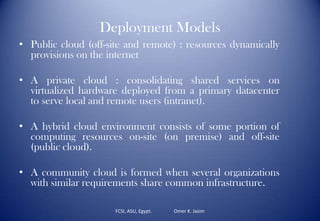
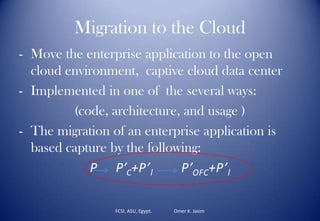
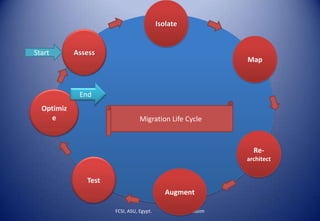
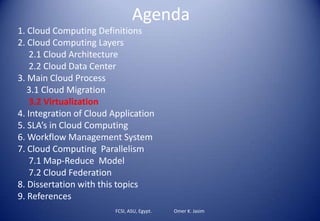
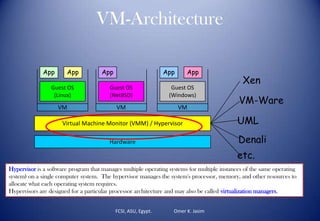
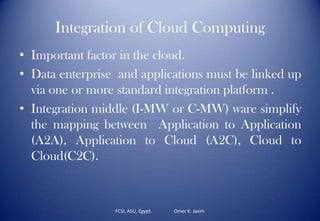
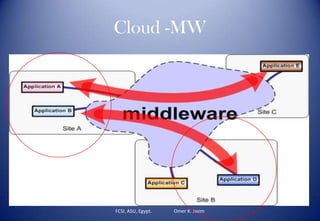
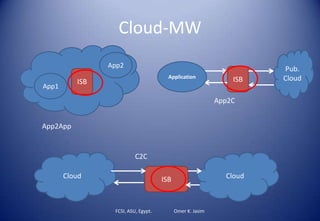
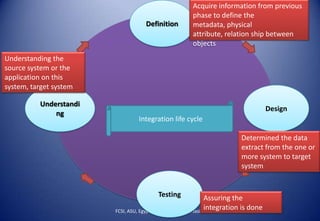
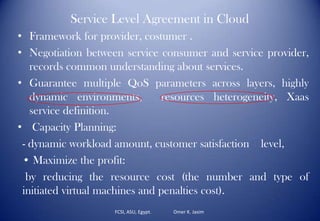
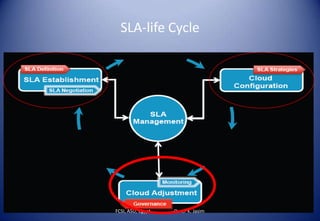
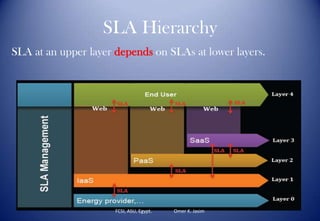
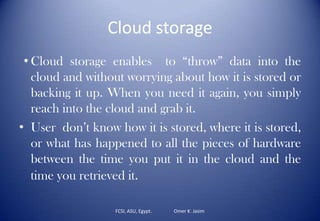
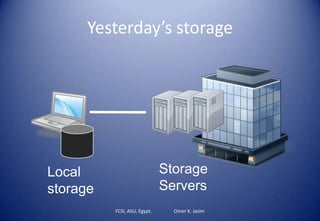
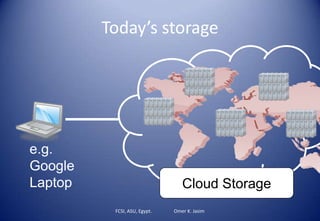
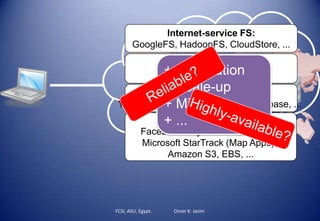
This document discusses cloud computing and provides definitions, layers, architectures, and processes related to cloud computing. It begins with definitions of cloud computing and discusses how it gets its name from the internet symbol of a cloud. It then covers layers of cloud computing including software, platform, and infrastructure as services. Main cloud processes like migration and virtualization are described. The document presents an agenda and table of contents to guide the discussion.