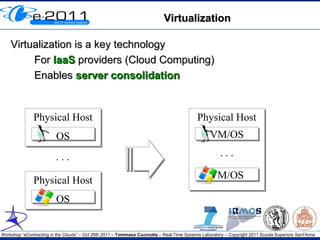
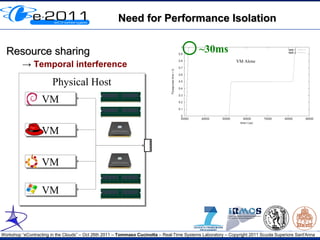
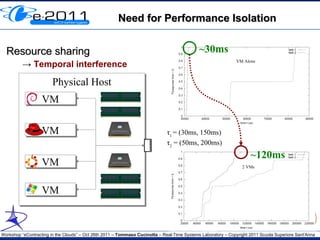
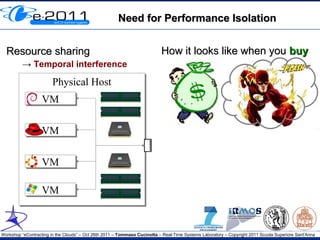
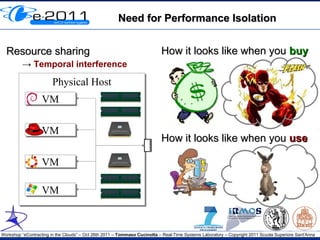
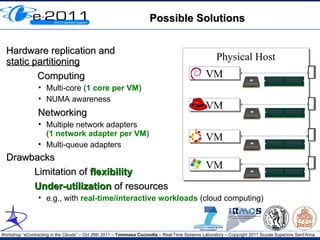
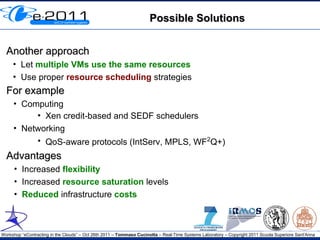
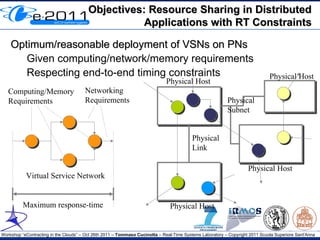
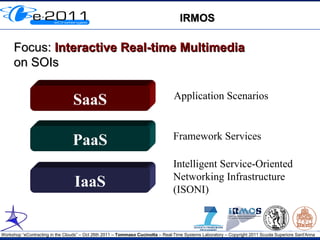
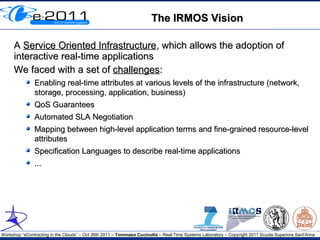
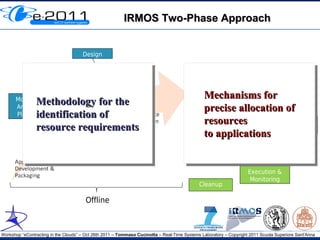
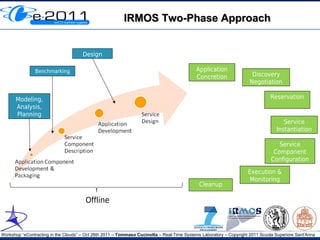
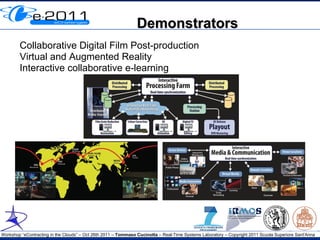
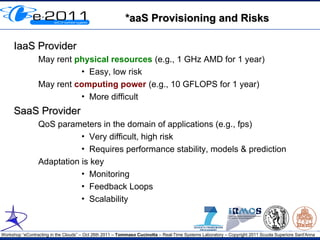
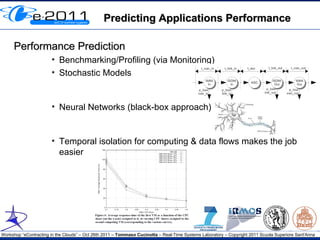
This document discusses the challenges and solutions regarding quality of service (QoS) in virtualized cloud computing infrastructures, particularly focusing on real-time applications. It outlines the need for performance isolation amidst resource sharing, proposes scheduling strategies to improve flexibility and cost efficiency, and introduces the IRMOS approach to ensure real-time multimedia interactions. Future research directions include specifying verifiable QoS requirements in service level agreements (SLAs) and exploring business models addressing imprecise QoS guarantees.