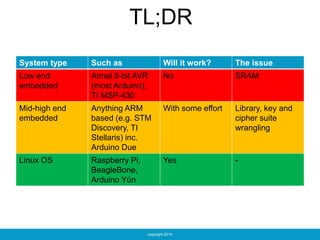
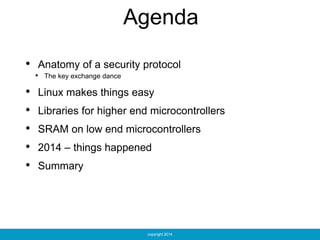
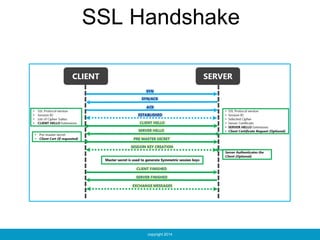
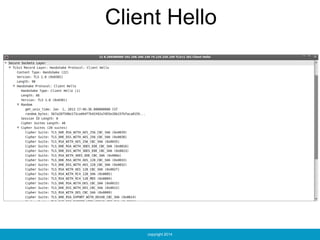
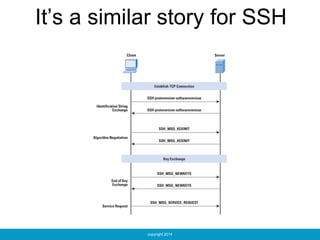
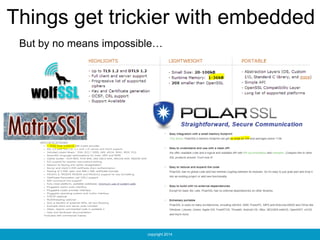
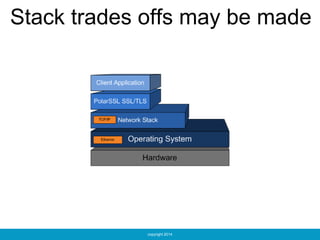
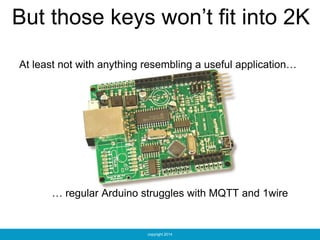
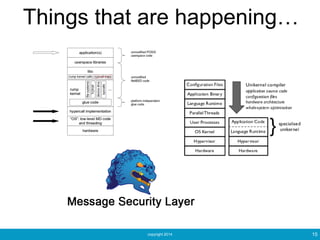
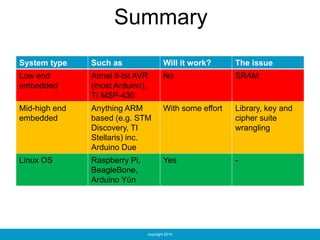
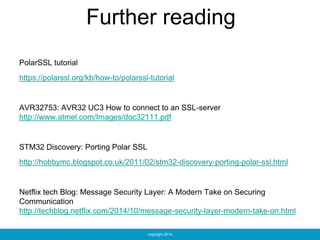
The document discusses security protocols relevant to various embedded systems, focusing on their compatibility with low and mid-high end microcontrollers. It emphasizes the challenges and solutions in implementing protocols like SSL/TLS, SSH, and IPsec, particularly in constrained environments. Additional resources for further reading on securing communications are also provided.