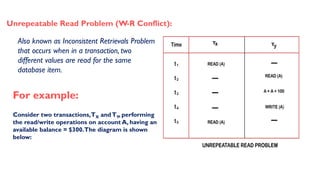
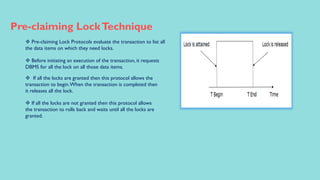
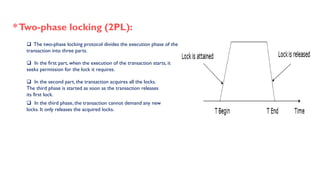
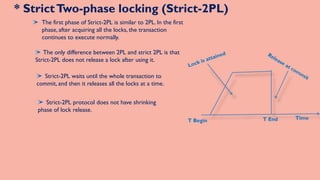
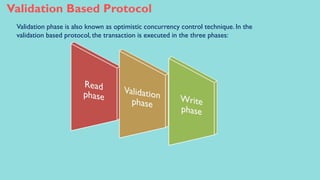
This document discusses concurrency control techniques in database management, essential for ensuring consistency during concurrent operations by multiple users. It outlines problems such as lost updates, dirty reads, and unrepeatable reads, and reviews various protocols like locking mechanisms and timestamp ordering to prevent these issues. Techniques described include simplistic locking, pre-claiming locks, and two-phase locking, detailing their operations and phases.