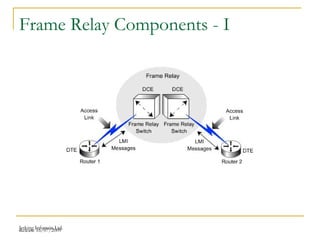
This document discusses Frame Relay components, configuration, and troubleshooting. It describes Frame Relay features, components like DTE, DCE, CIR, and DLCI addressing. It covers virtual circuits, encapsulation types, and LMI configuration. It also provides examples of show commands for verification and troubleshooting Frame Relay networks.
![Release 16/07/2009Jetking Infotrain Ltd.
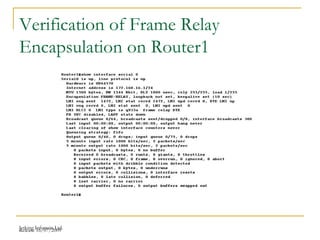
Frame Configuration Command - I
Commands Description
encapsulation frame-relay
[ieft|cisco]
Defines the Frame Relay
encapsulation which is preferred over
HDLC and PPP
frame-relay lmi-type{ansi|
q933a|cisco]
Defines the type of LMI messages that
are sent to the switch
bandwidth num Enables to set the interface speed of
the router
frame-relay map [protocol
protocol-address
dlci}payload-compression
frf9 stac caim [element-
number][broadcast] [ieft|
cisco]
Defines statically the mapping
between the network layer and DLCI](https://image.slidesharecdn.com/chapter11-141217100751-conversion-gate01/85/CCNA-CHAPTER-11-BY-jetarvind-kumar-madhukar-34-320.jpg)
![Release 16/07/2009Jetking Infotrain Ltd.
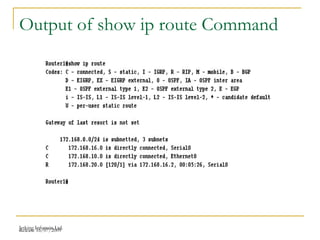
Frame Configuration Command - II
keepalive sec Enables to configure the way and time
interval that the LMI messages are
sent and received
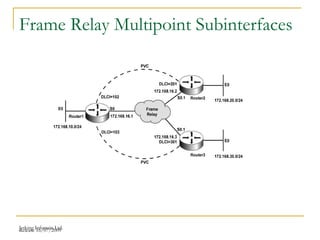
interface serial number.sub
[point-to-point|multipoint]
Enables to create a subinterface or
reference a subinterface that is
already created
frame-relay interface-dlci
dlci [ieft|cisco] [voice-cir
cir] [ppp virtual-template-
name]
Links the DLCI to the subinterface](https://image.slidesharecdn.com/chapter11-141217100751-conversion-gate01/85/CCNA-CHAPTER-11-BY-jetarvind-kumar-madhukar-35-320.jpg)
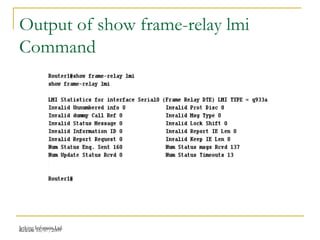
![Release 16/07/2009Jetking Infotrain Ltd.
Frame Configuration Commands in
the Privileged Mode - I
Command Description
show interfaces Displays the status of the physical
interface
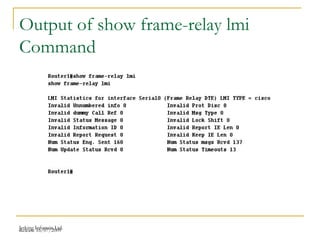
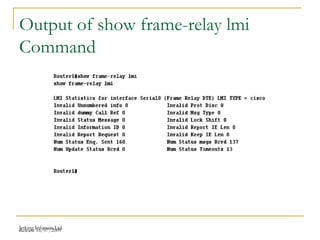
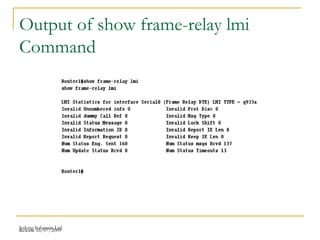
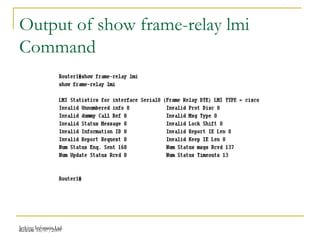
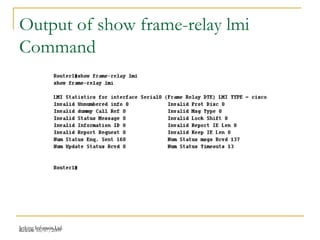
show frame-relay lmi [type
number]
Displays LMI status information
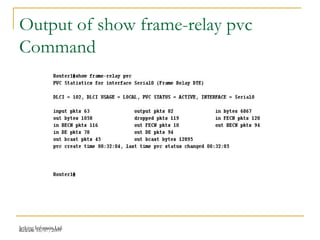
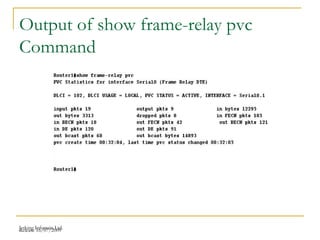
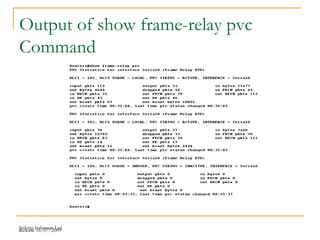
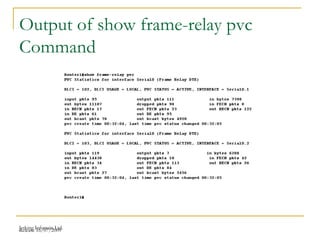
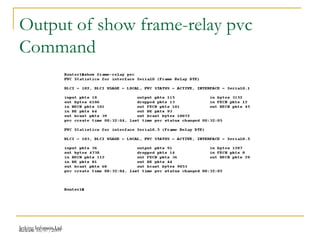
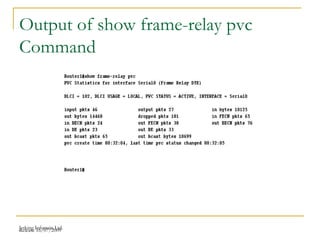
show frame-relay pvc Displays a list of all the configured
PVCs and DLCI numbers
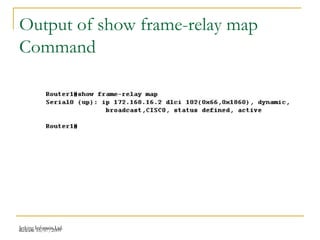
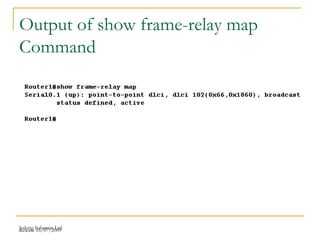
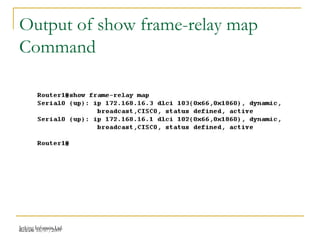
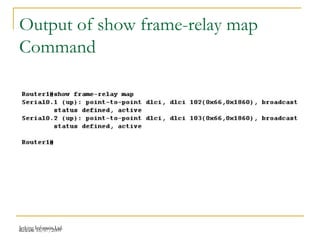
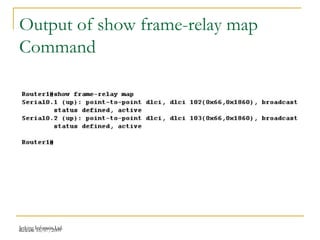
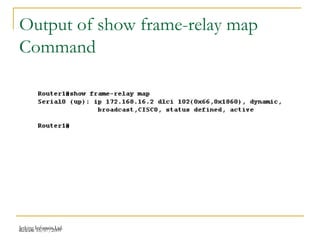
show frame-relay map Provides a list of network layer
addresses mapped to DLCI numbers
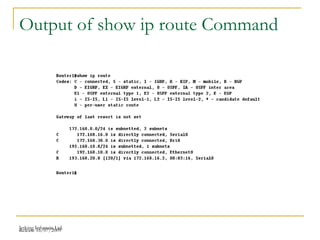
show ip route Displays the available routes for the
packets to travel from one router to
another](https://image.slidesharecdn.com/chapter11-141217100751-conversion-gate01/85/CCNA-CHAPTER-11-BY-jetarvind-kumar-madhukar-36-320.jpg)