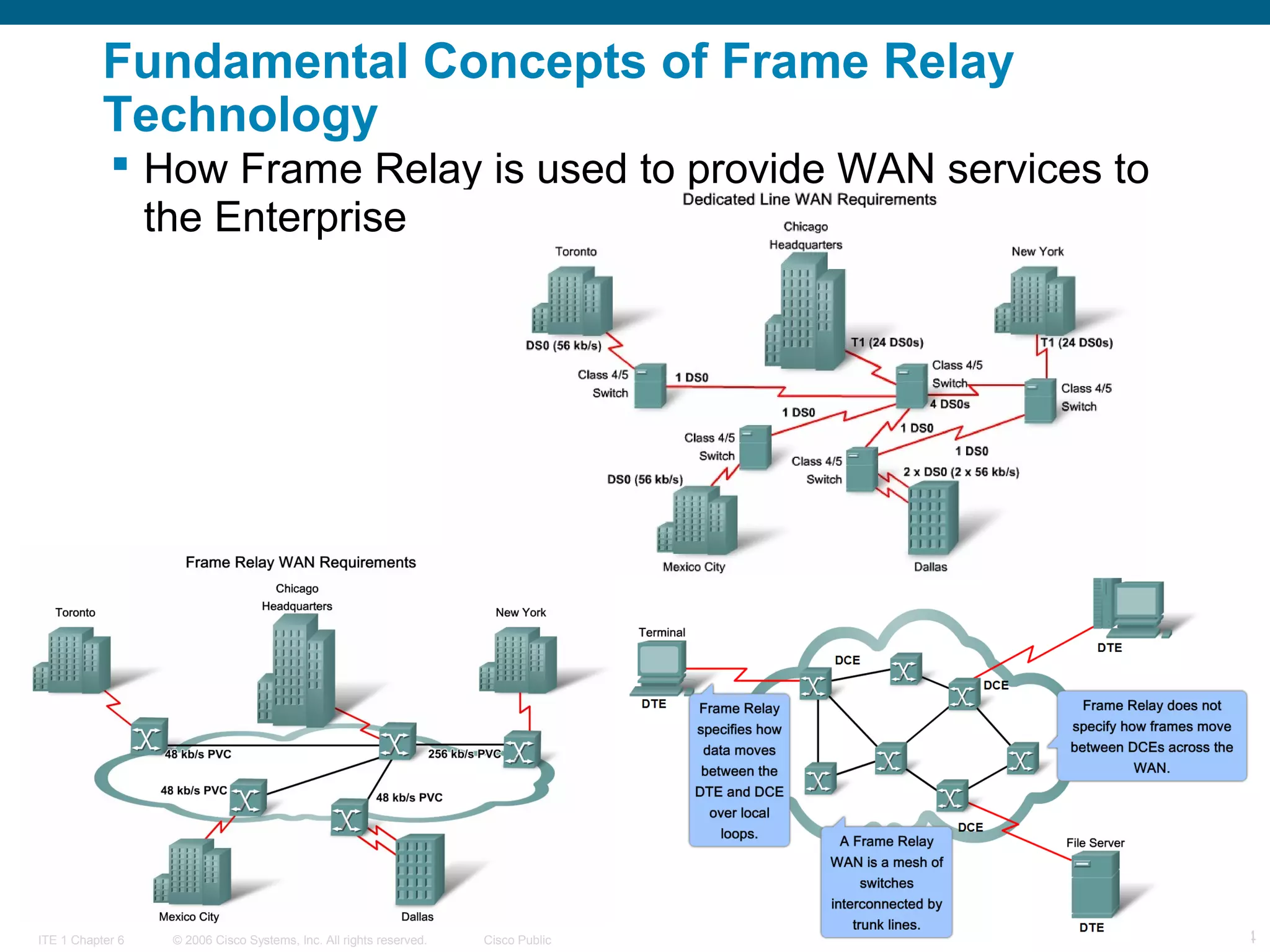
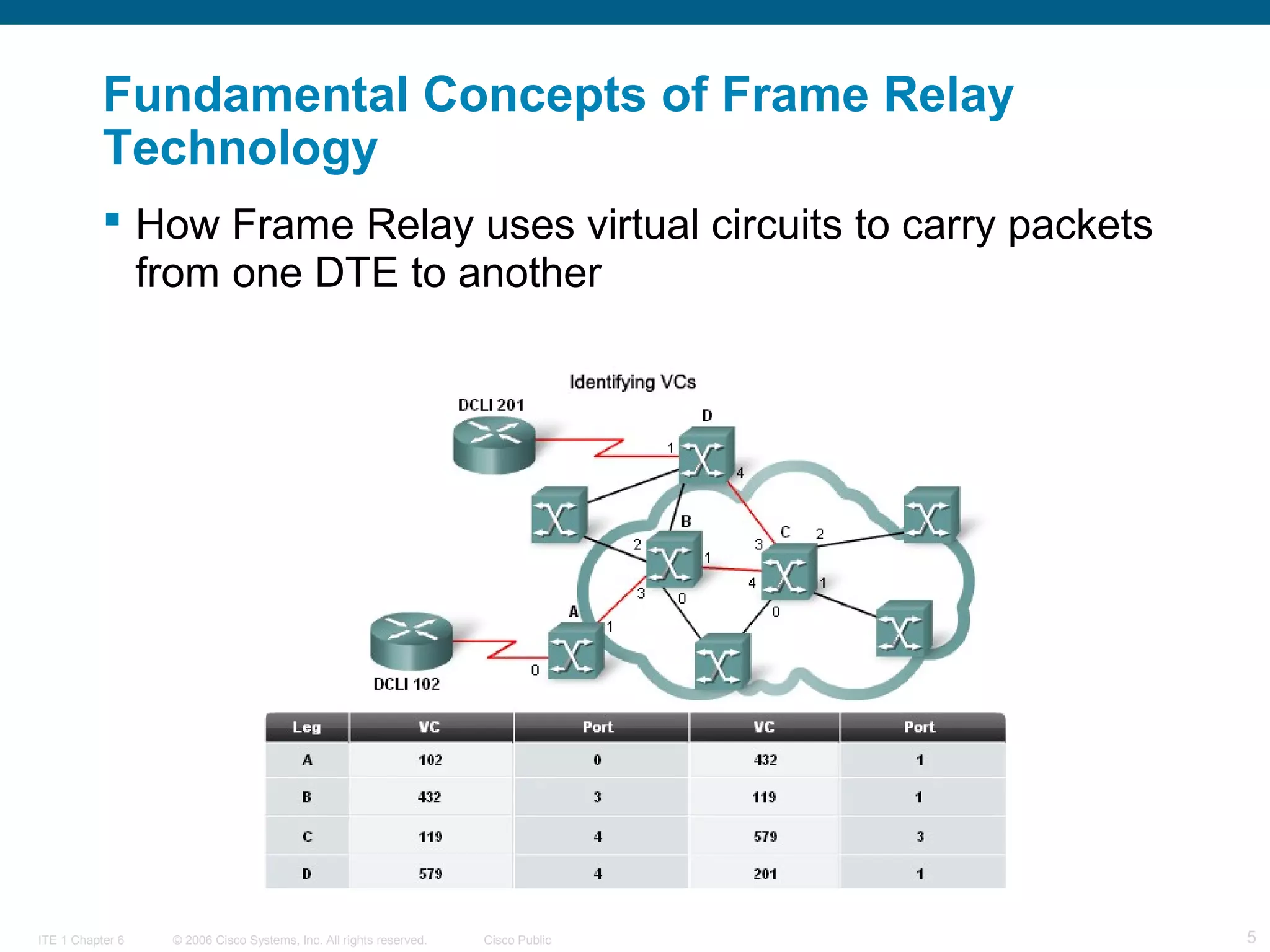
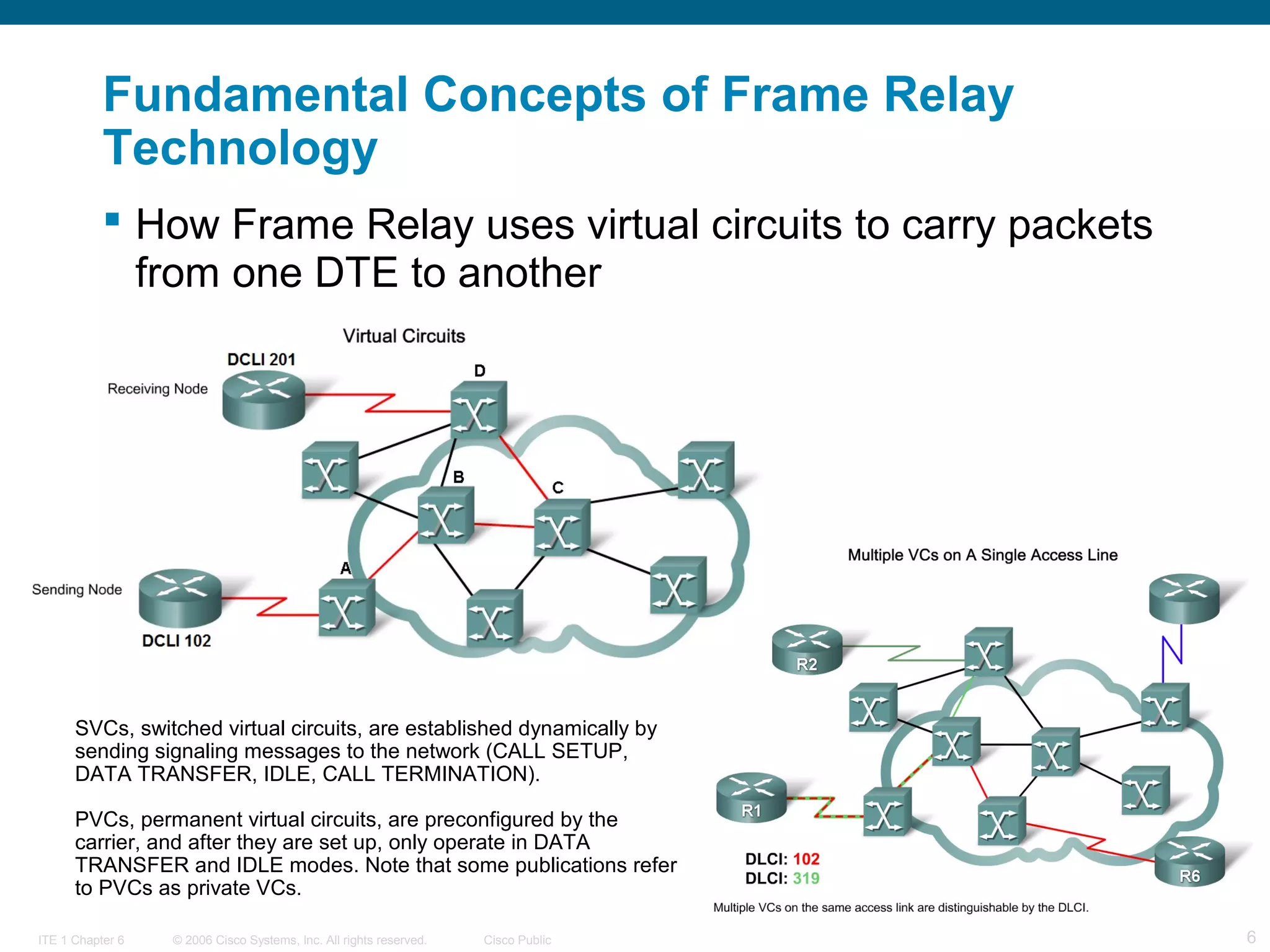
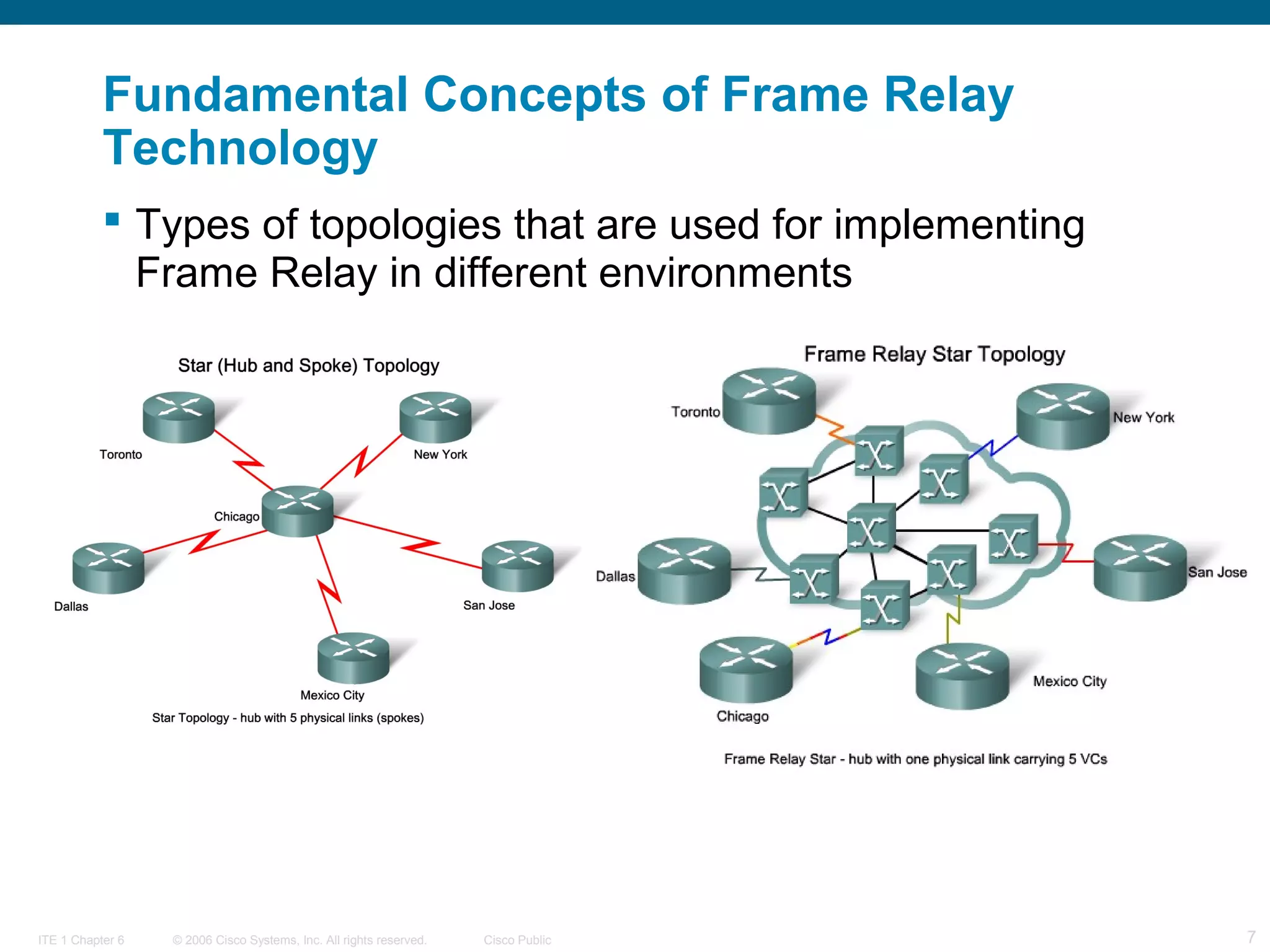
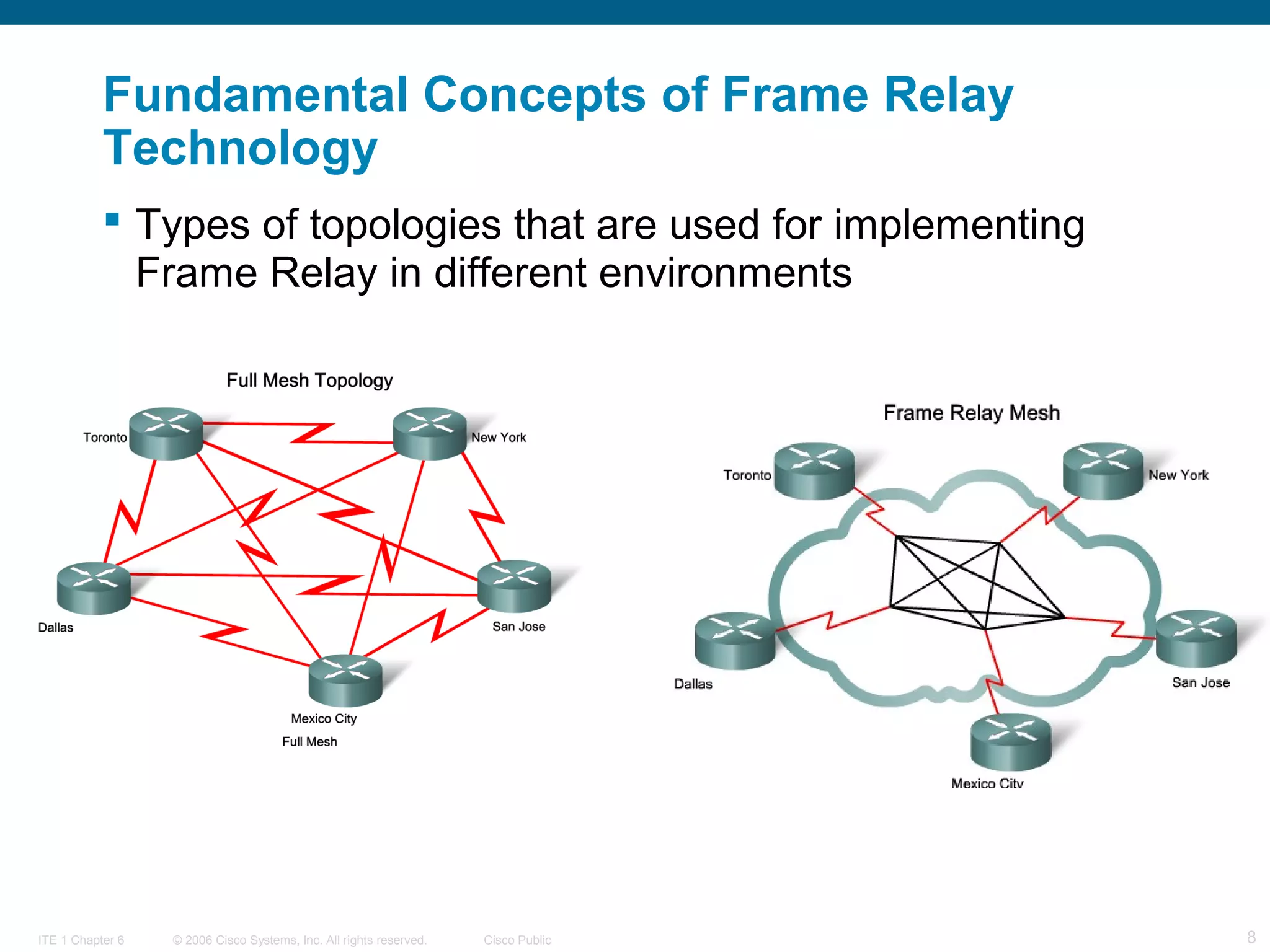
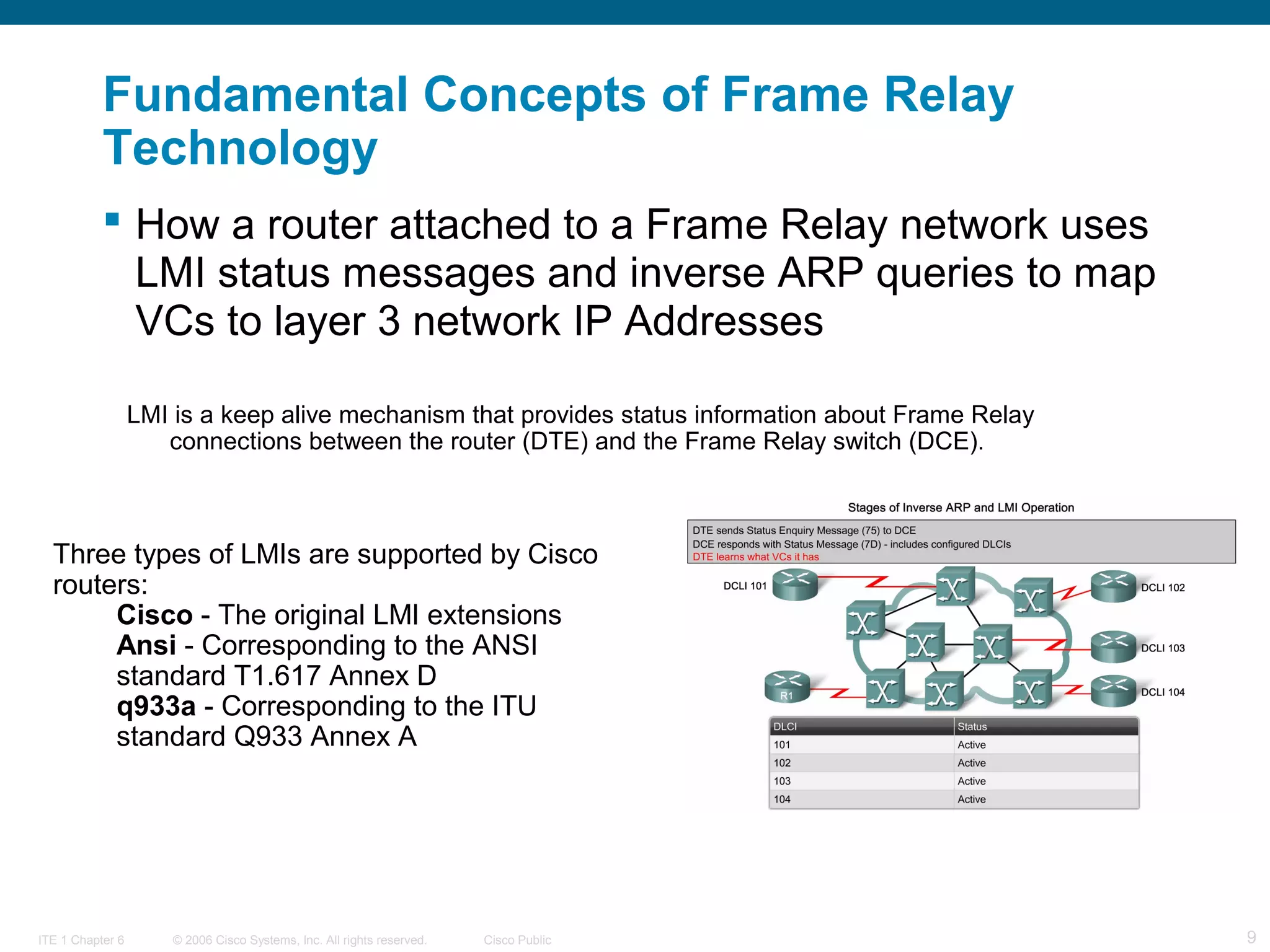
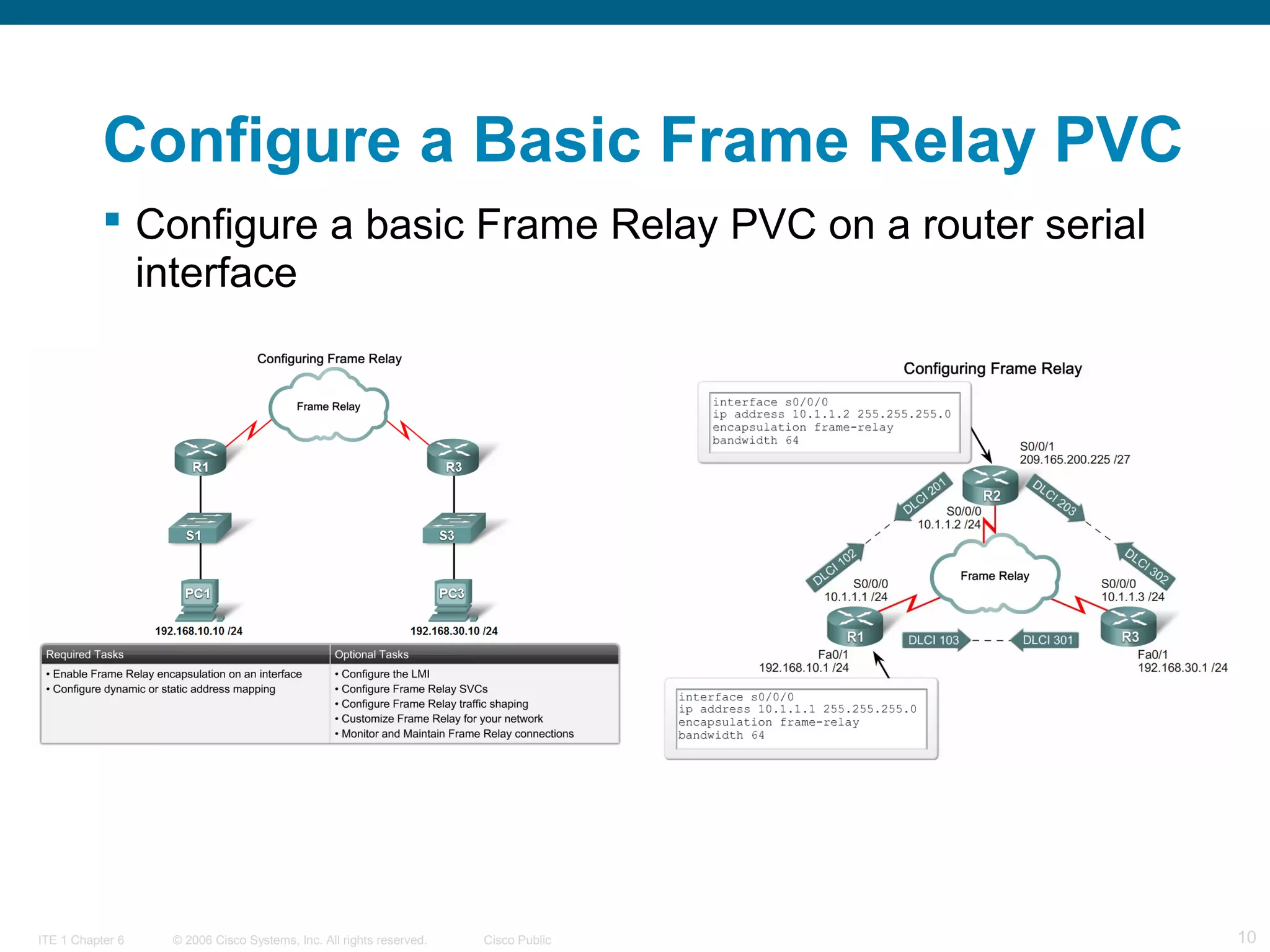
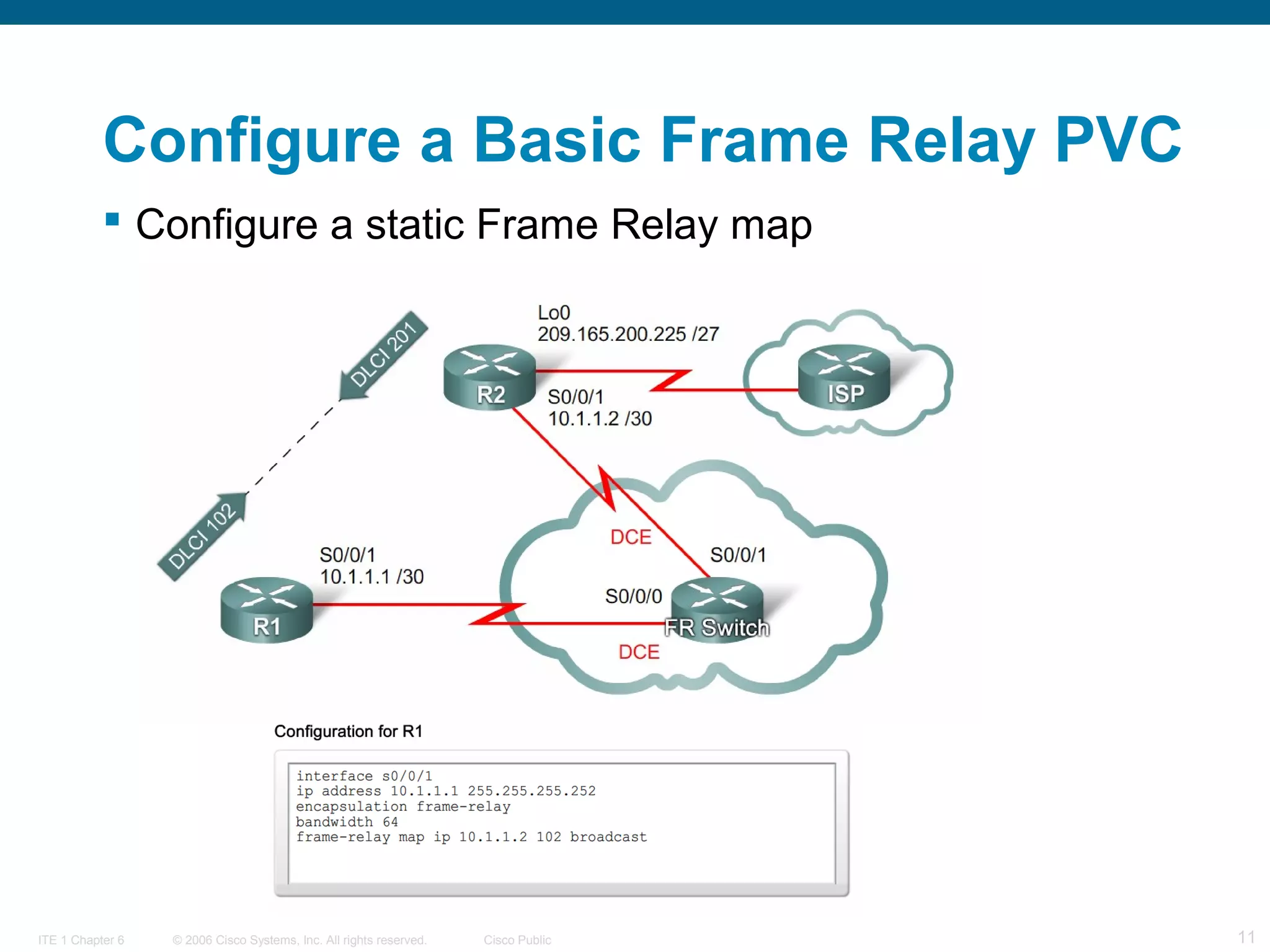
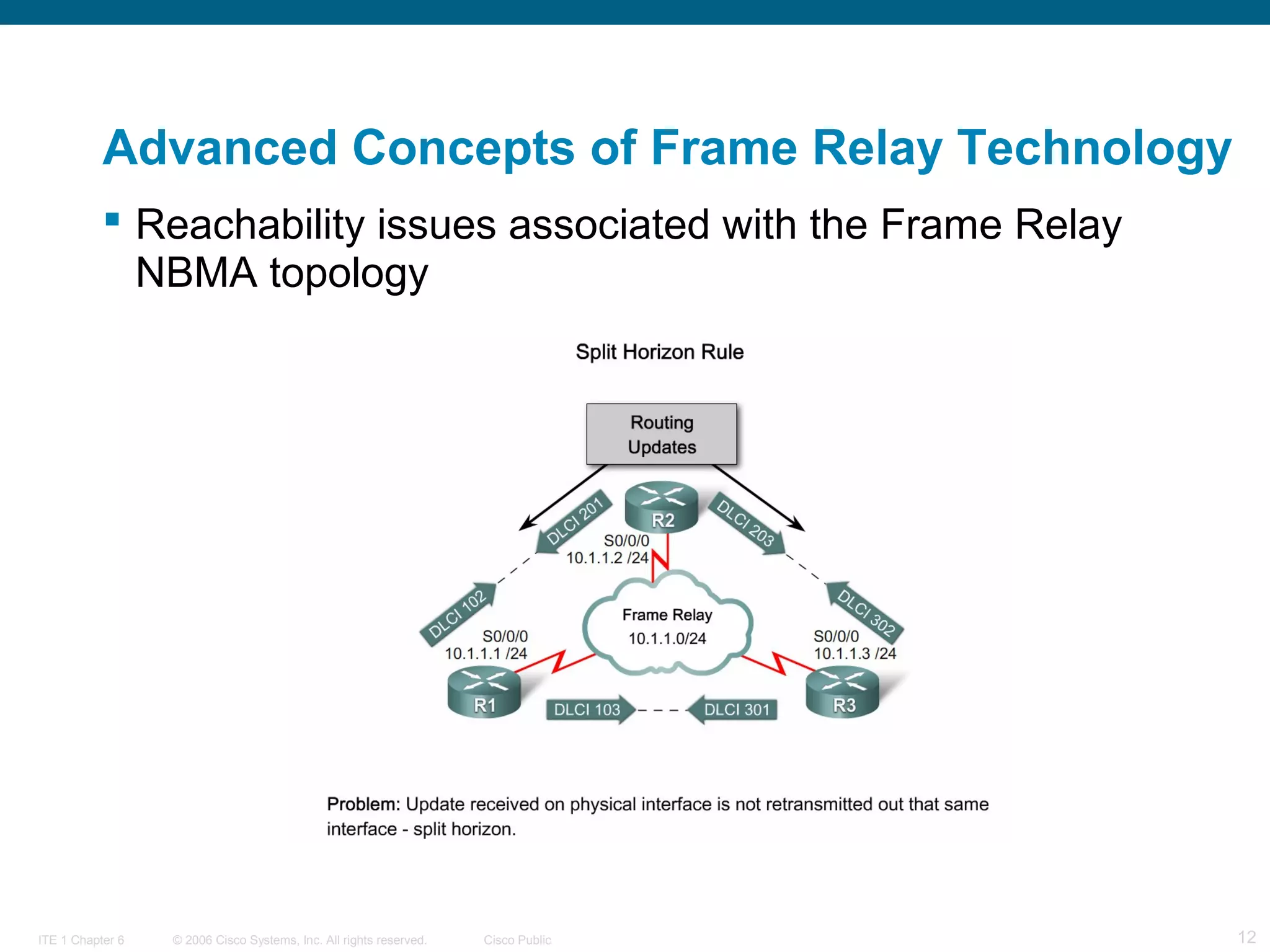
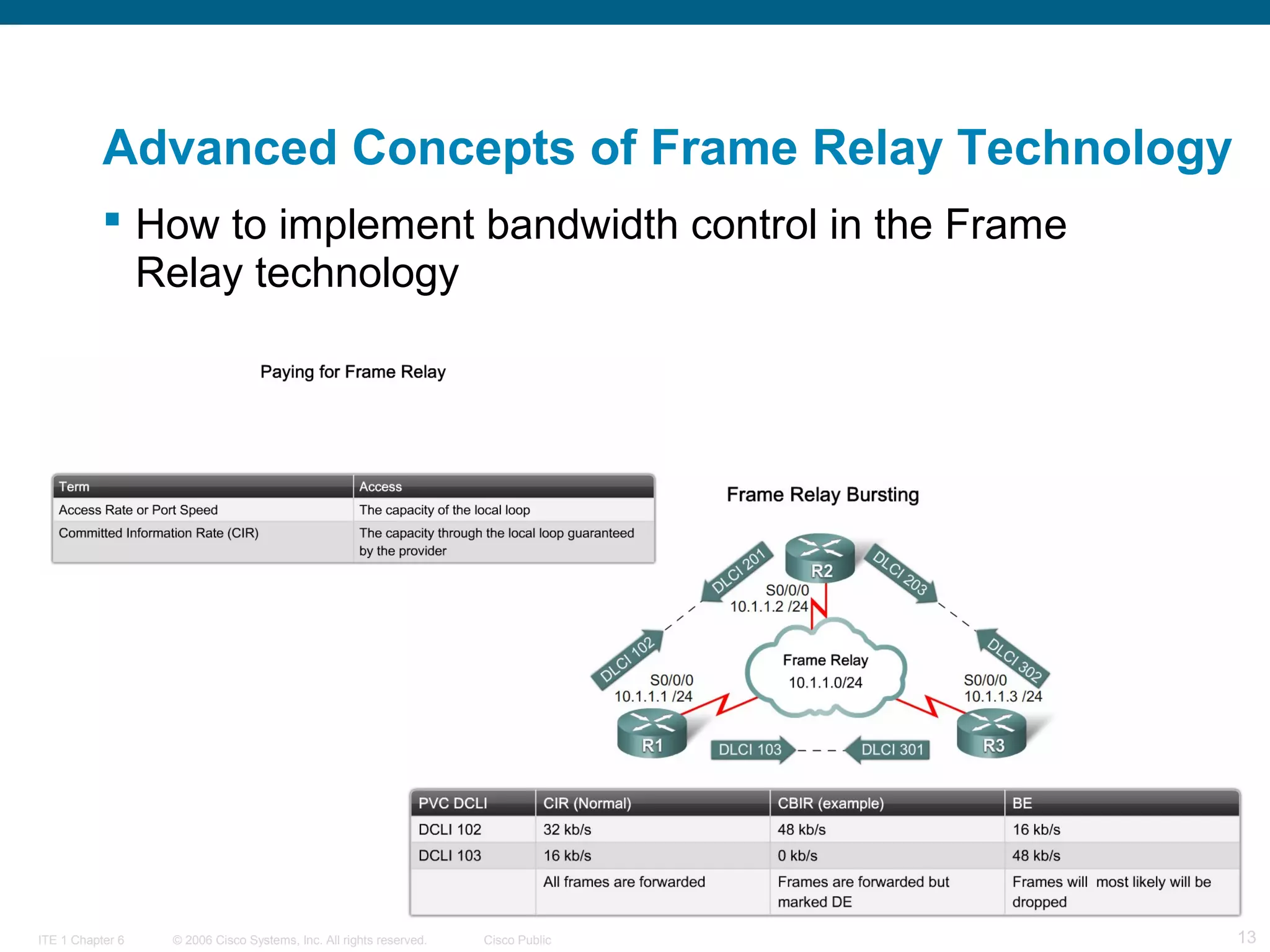
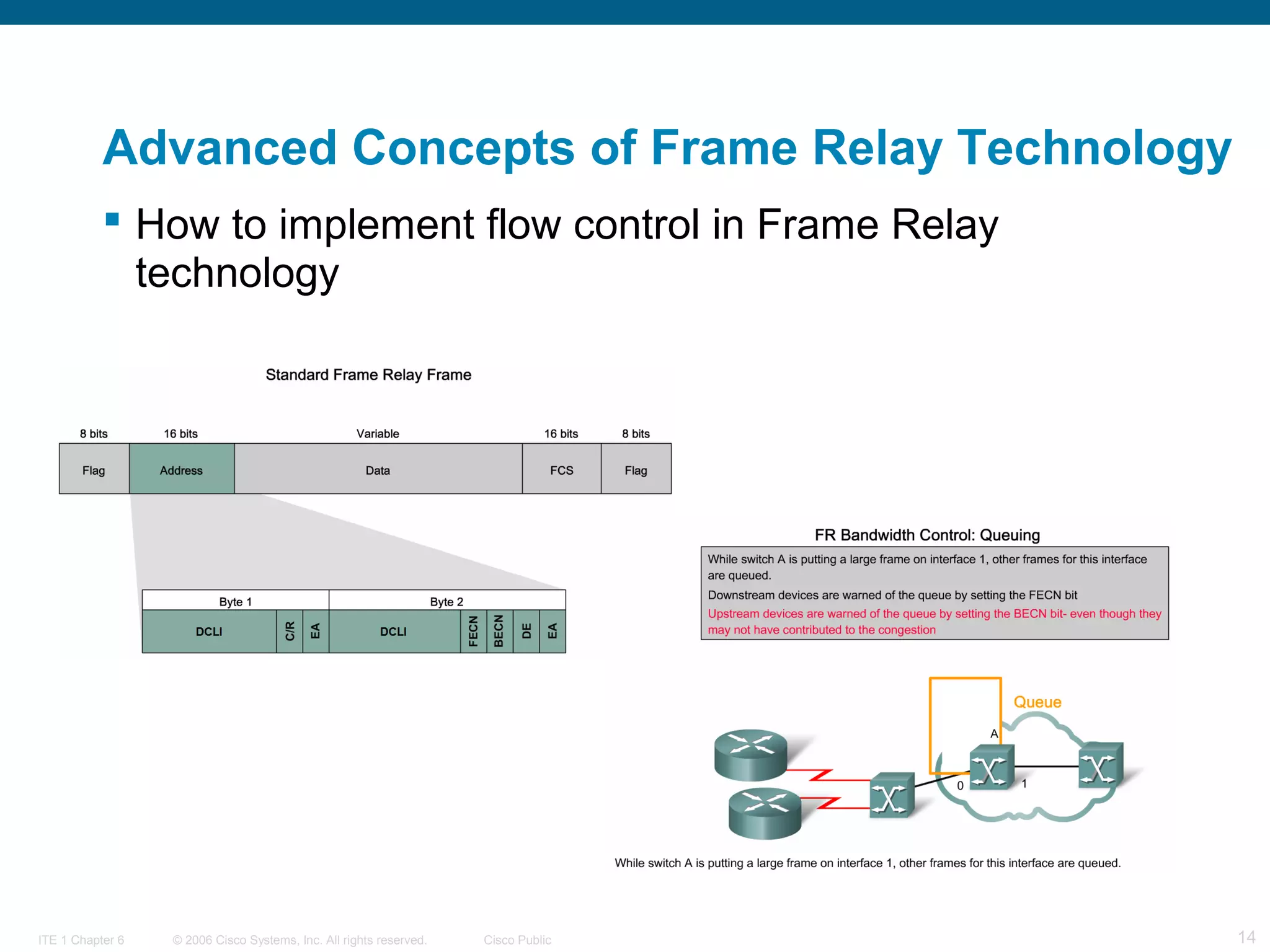
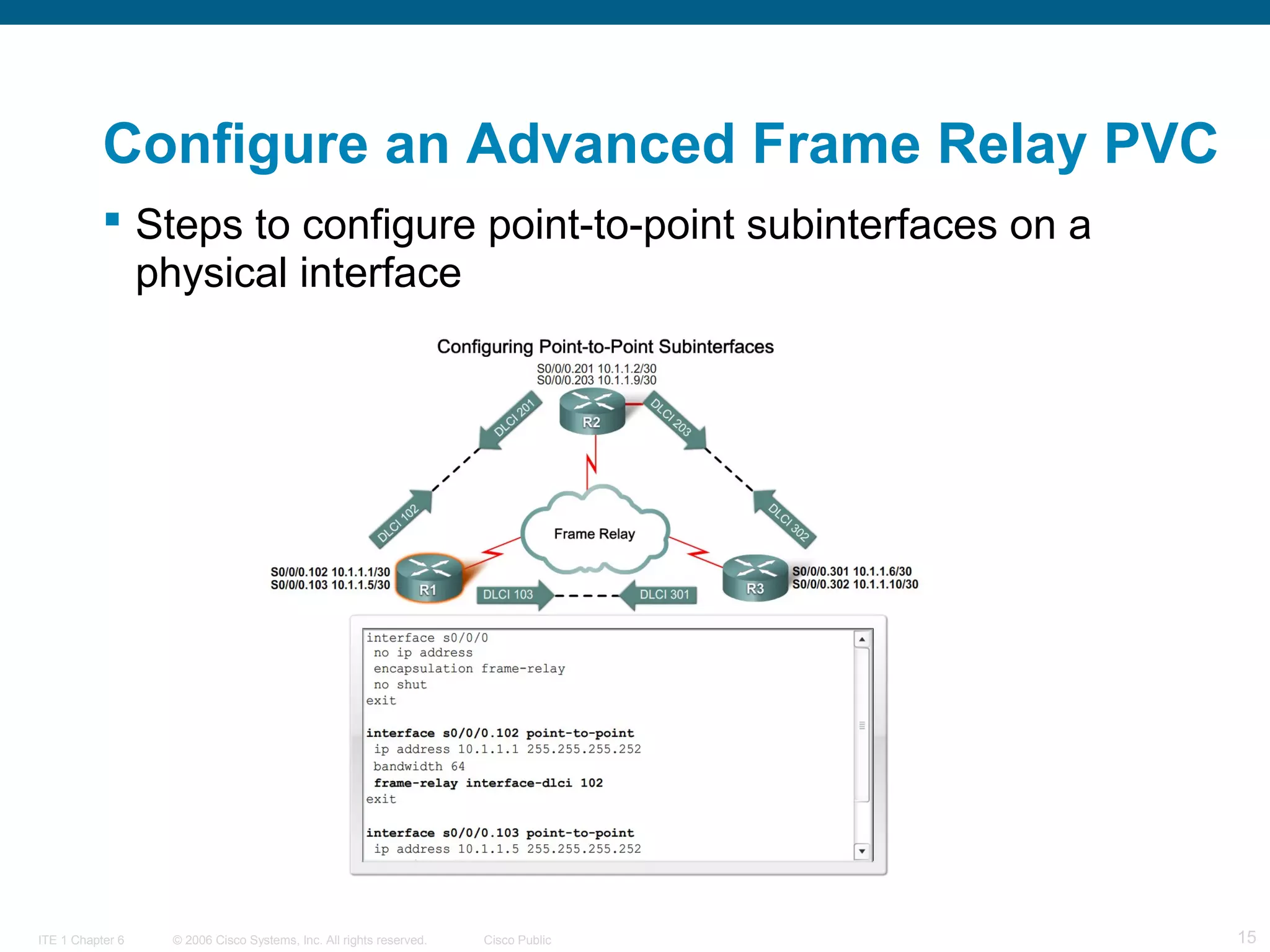
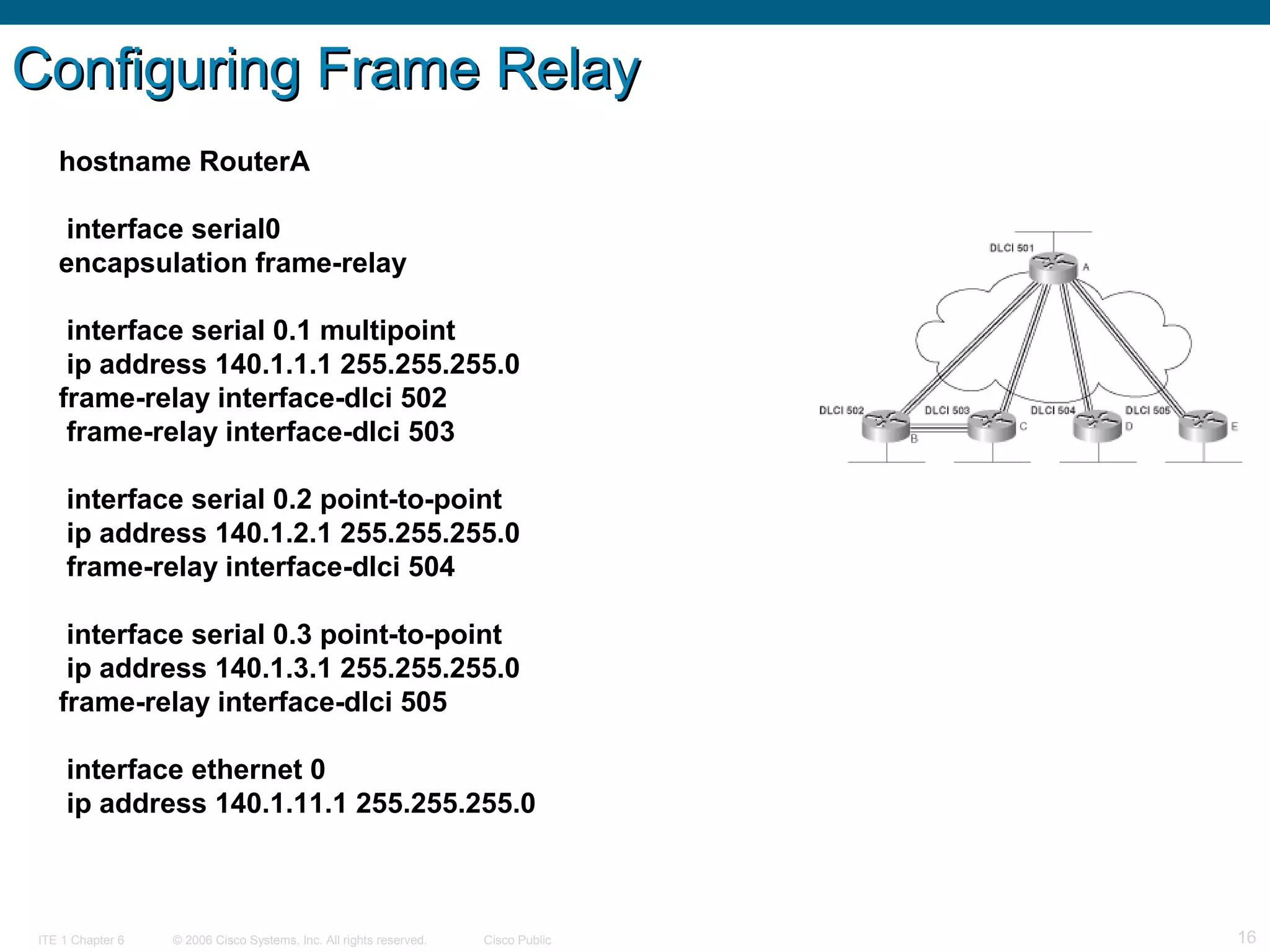
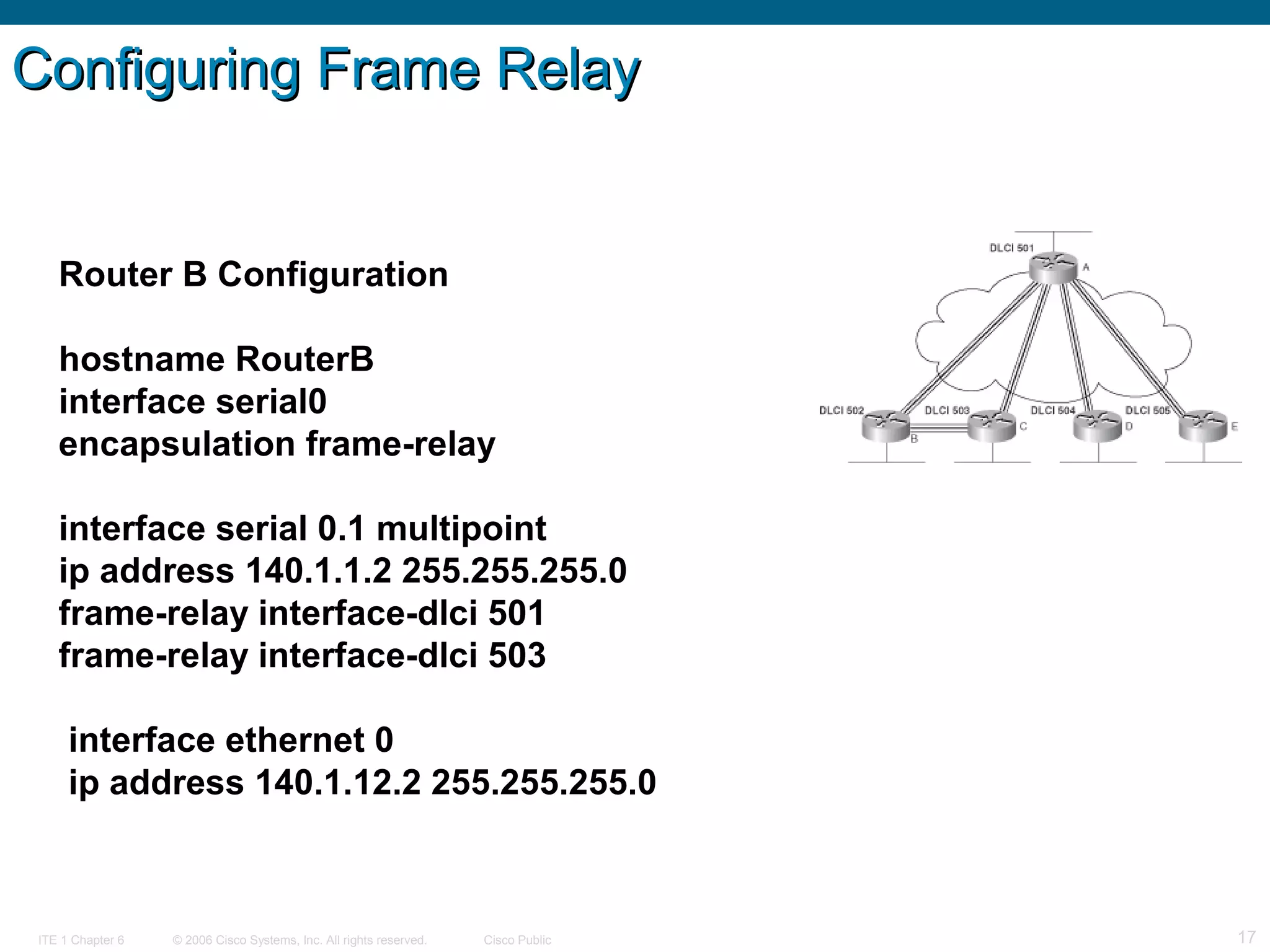
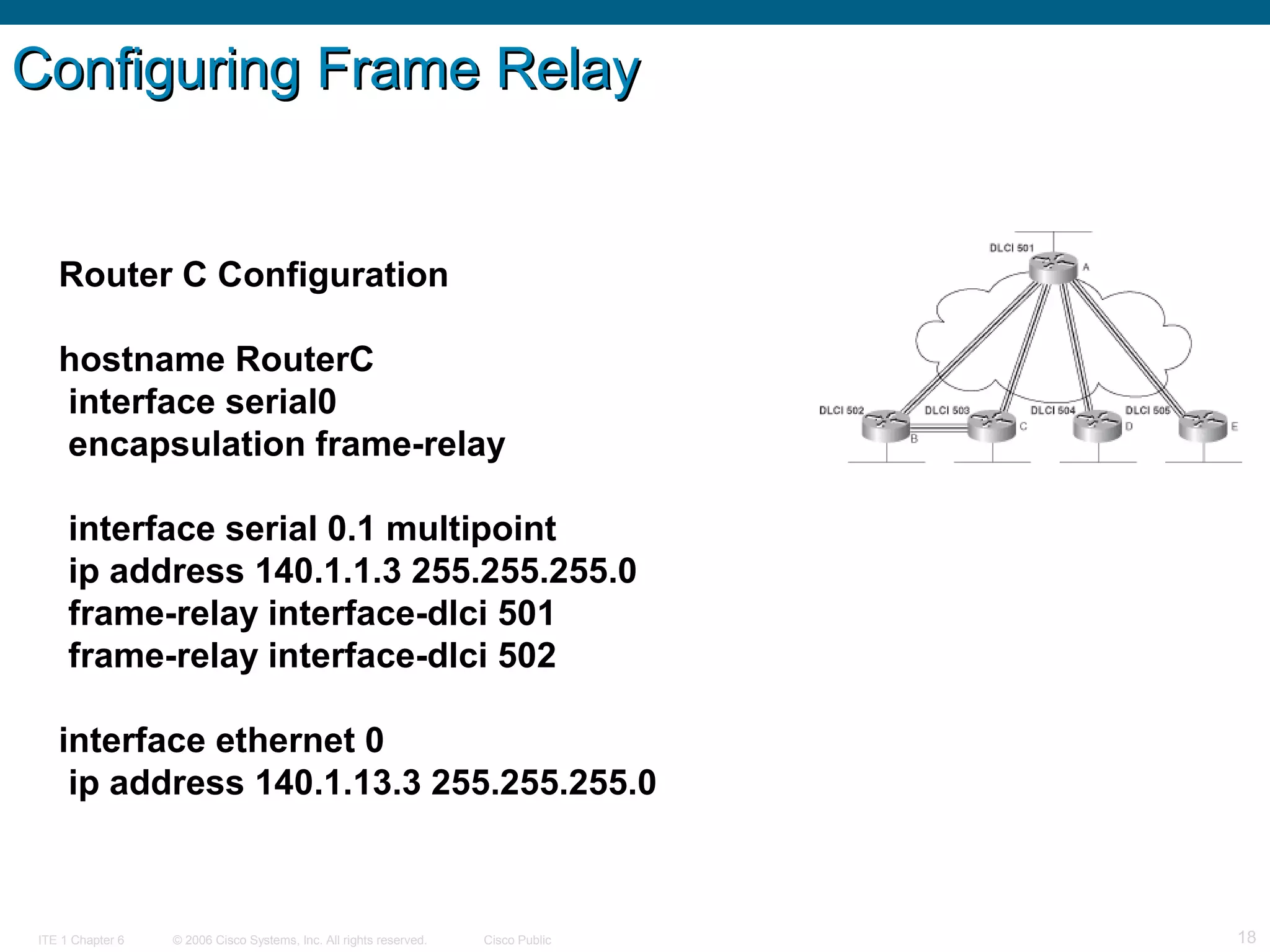
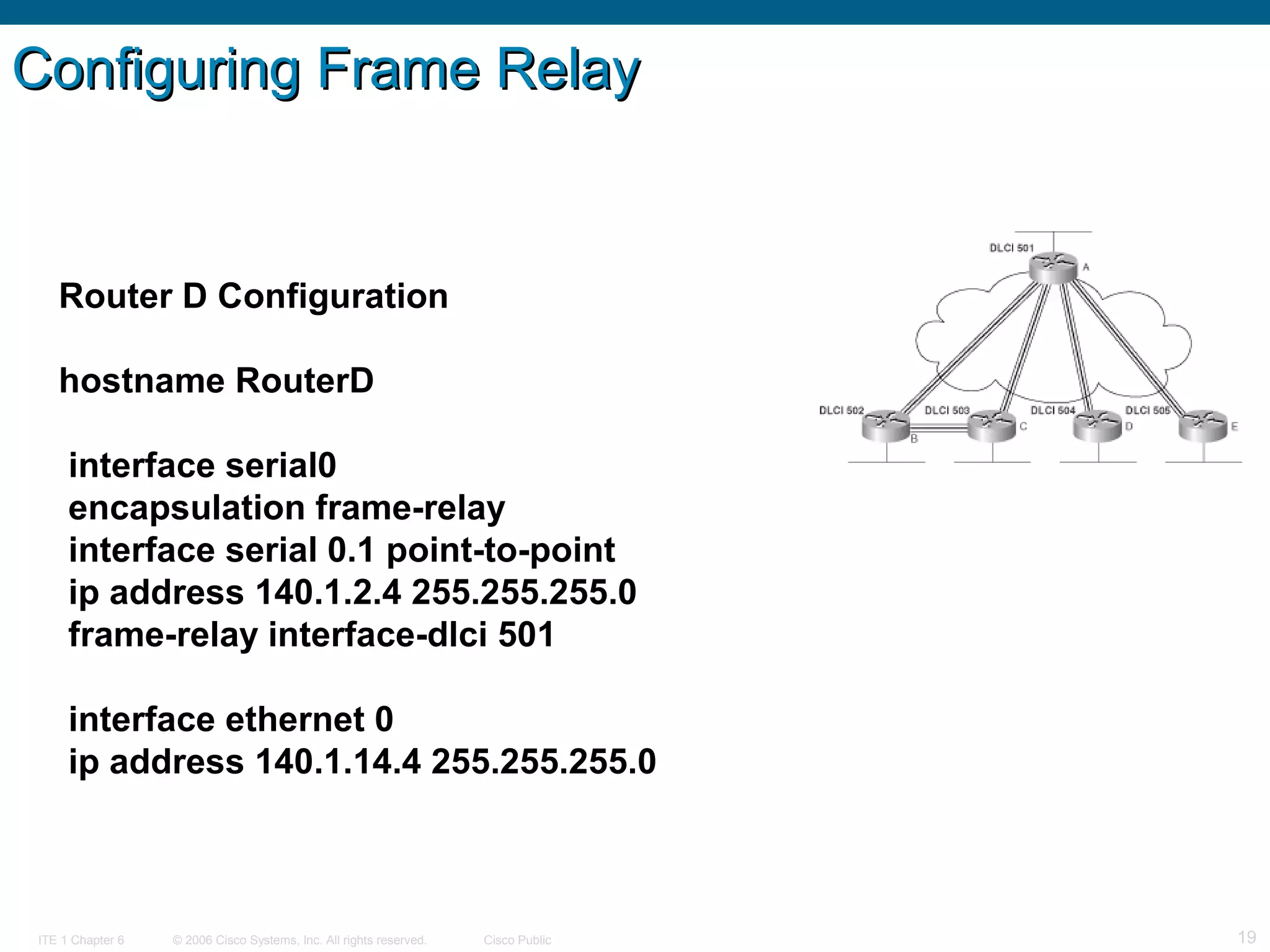
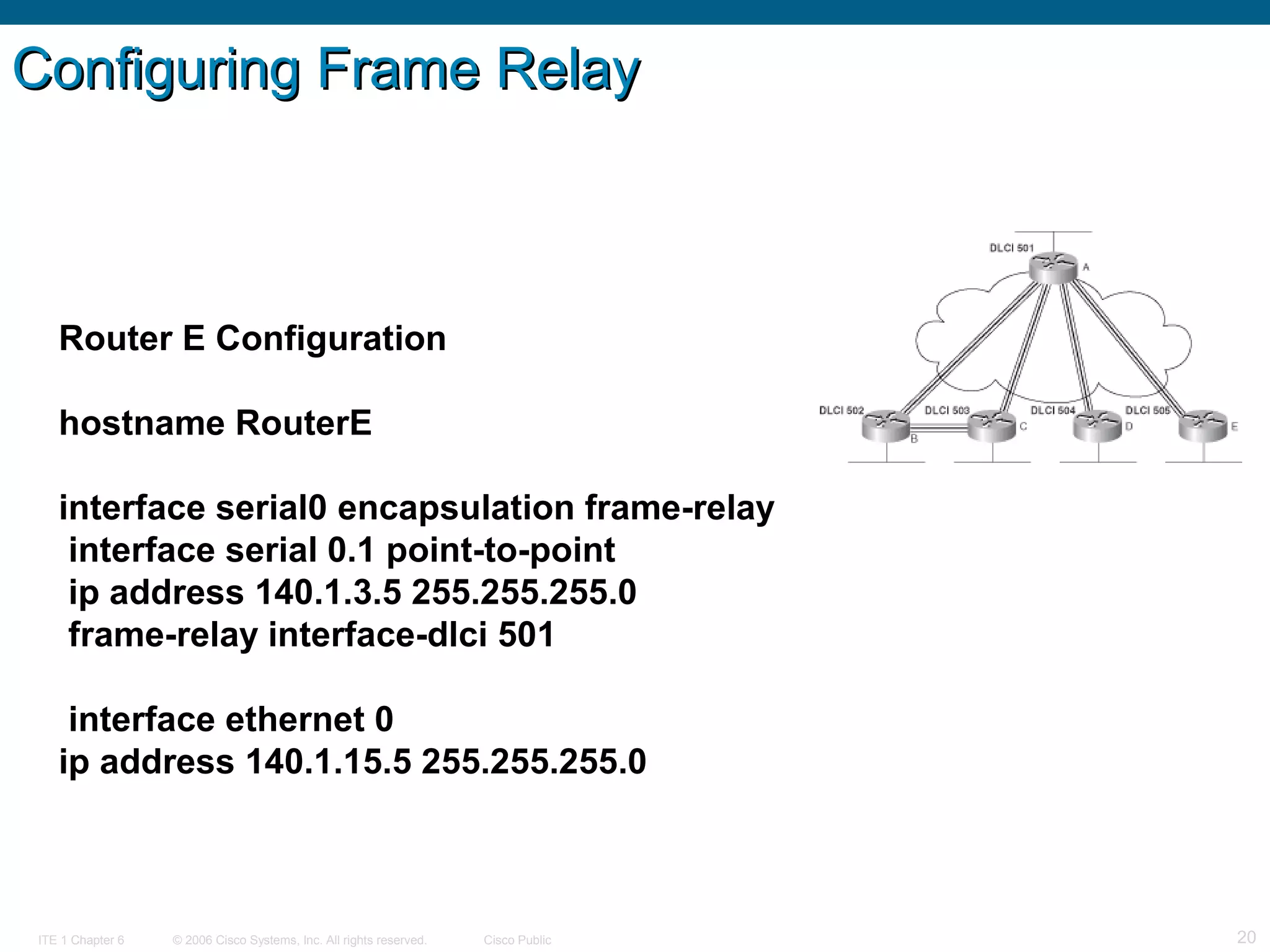
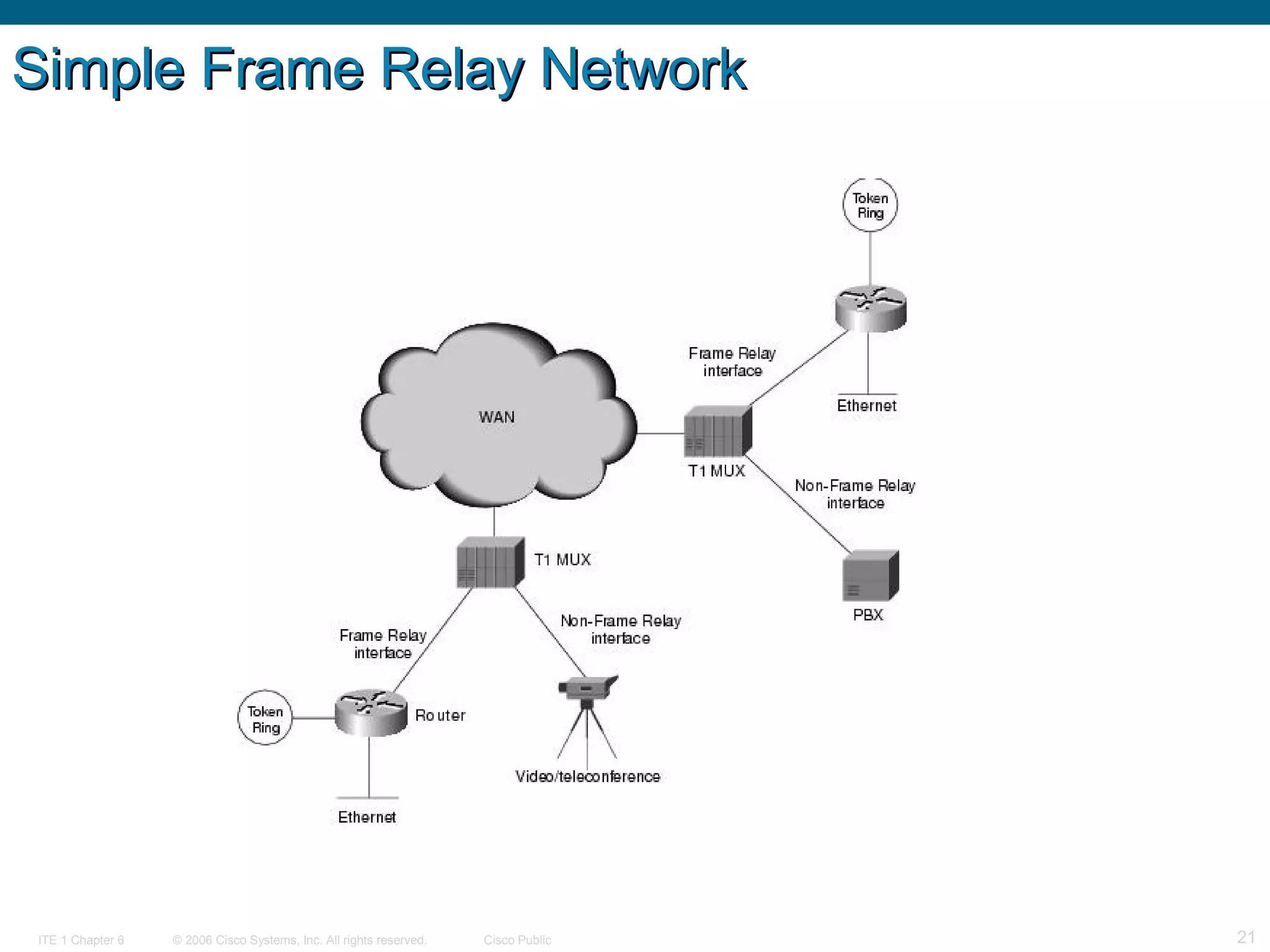
The document provides an overview of frame relay technology, focusing on its fundamental concepts, configuration, and advanced implementation techniques for enterprise WAN services. It outlines basic and advanced PVC configurations, including troubleshooting and utilizing virtual circuits. Additionally, it explains LMI operations, bandwidth control, and flow control within frame relay networks.