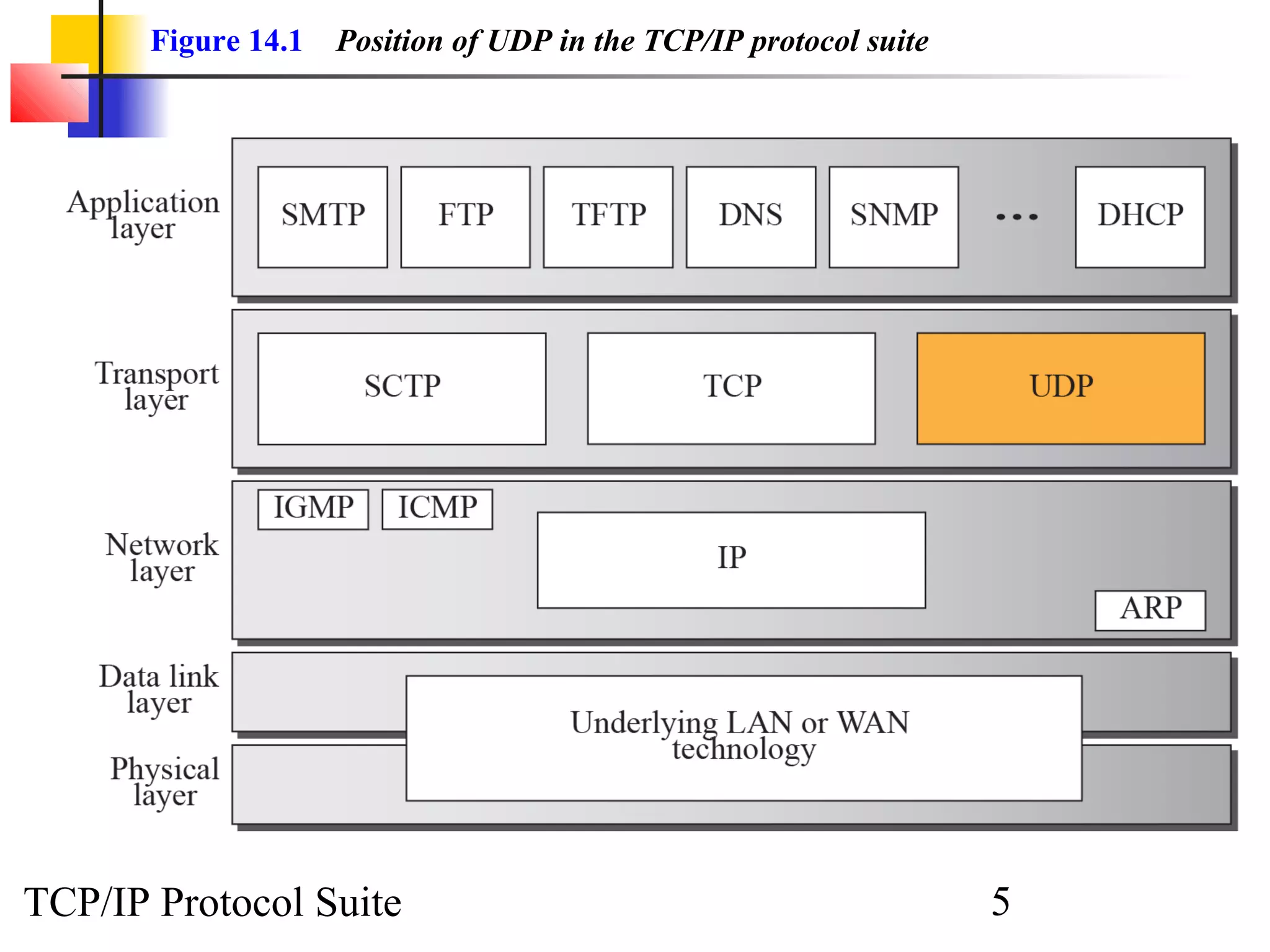
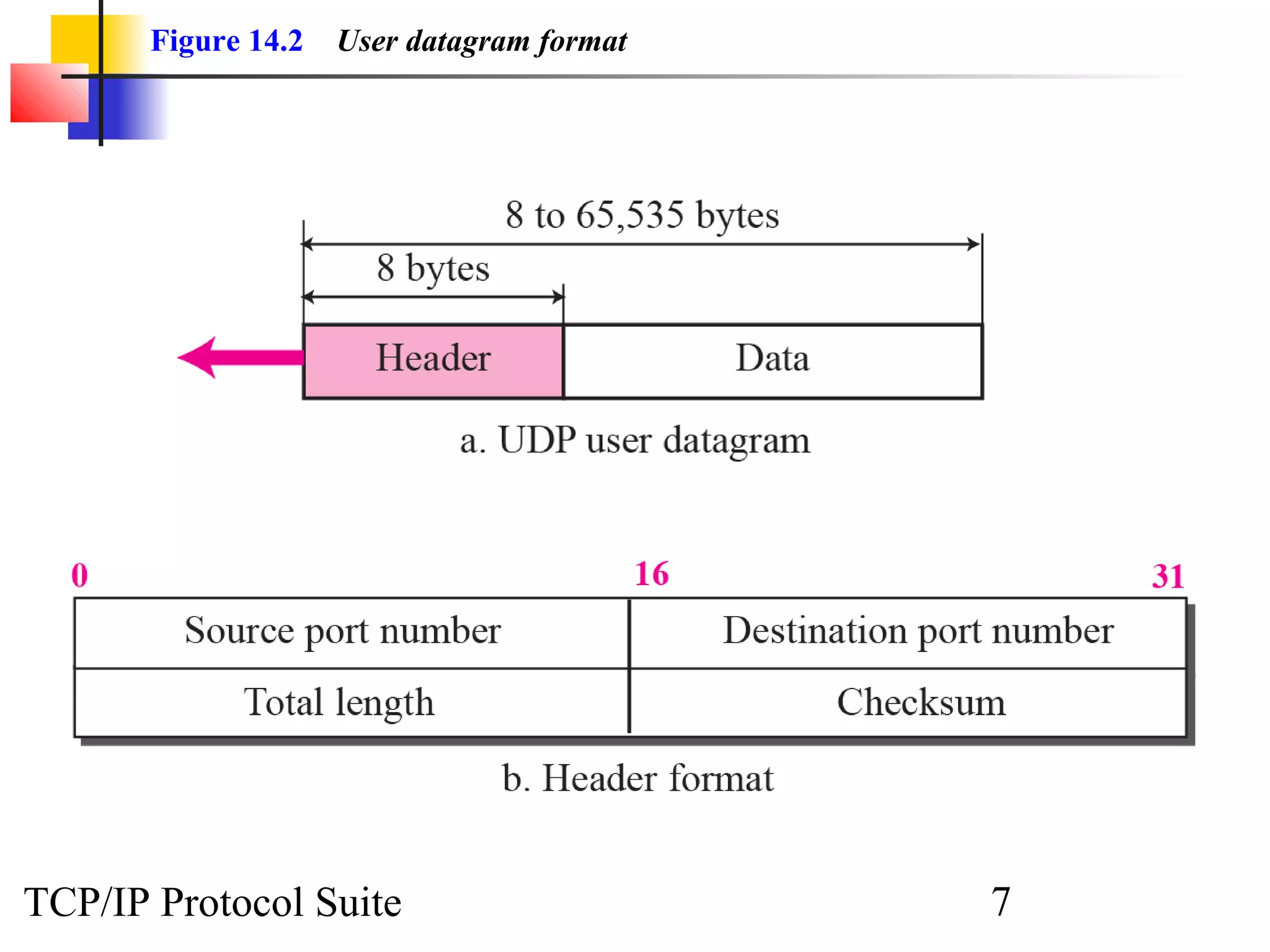
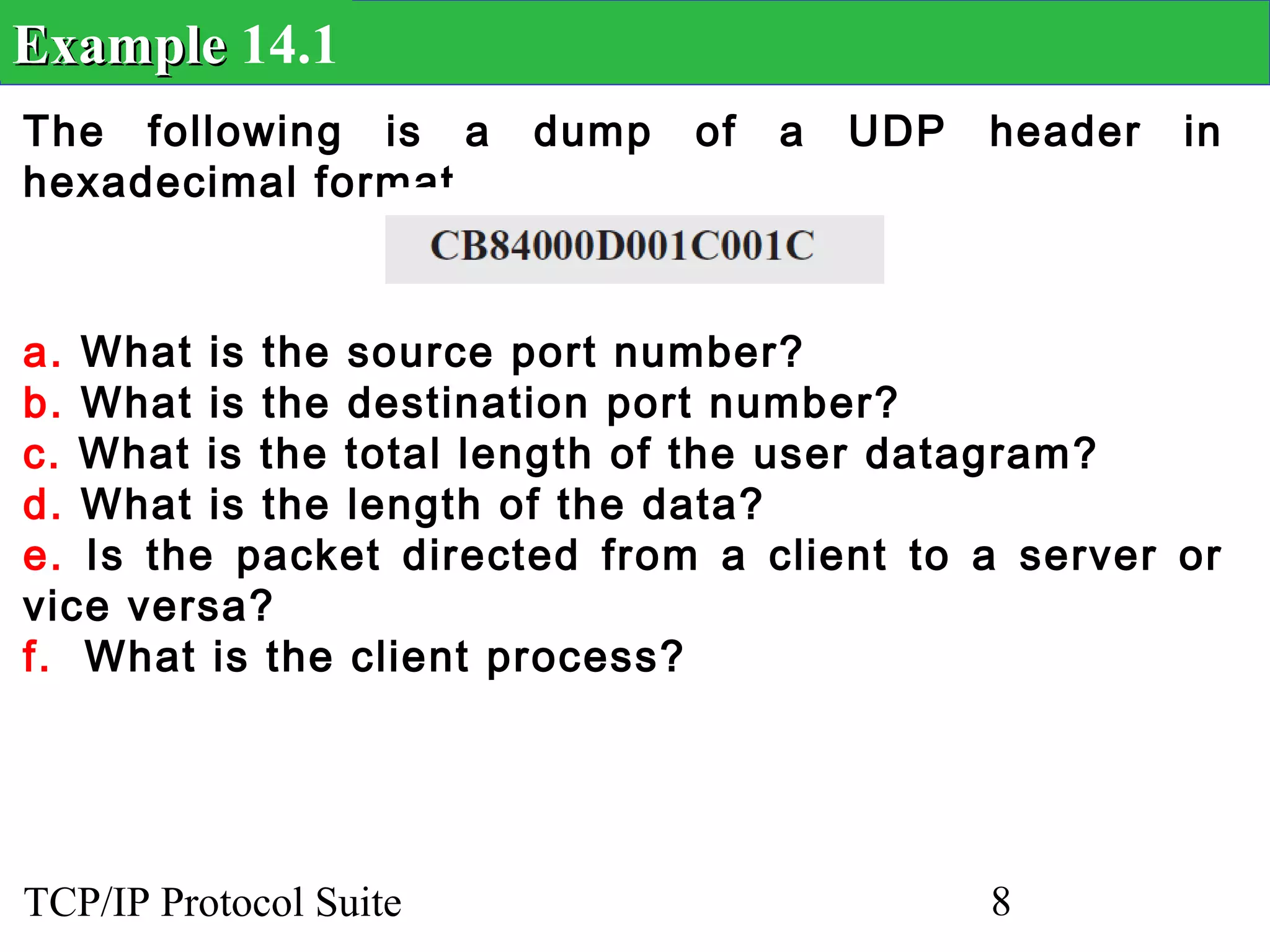
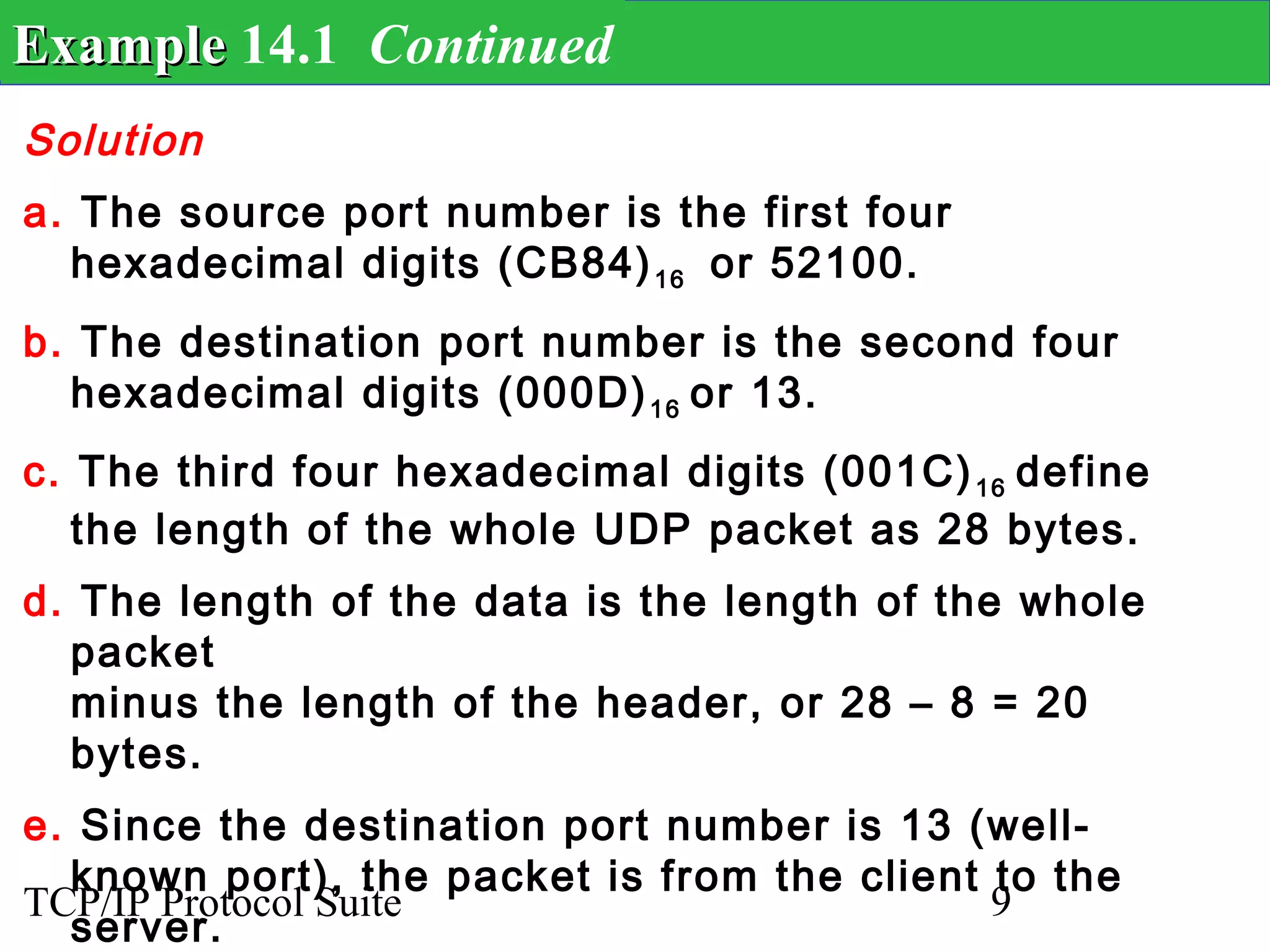
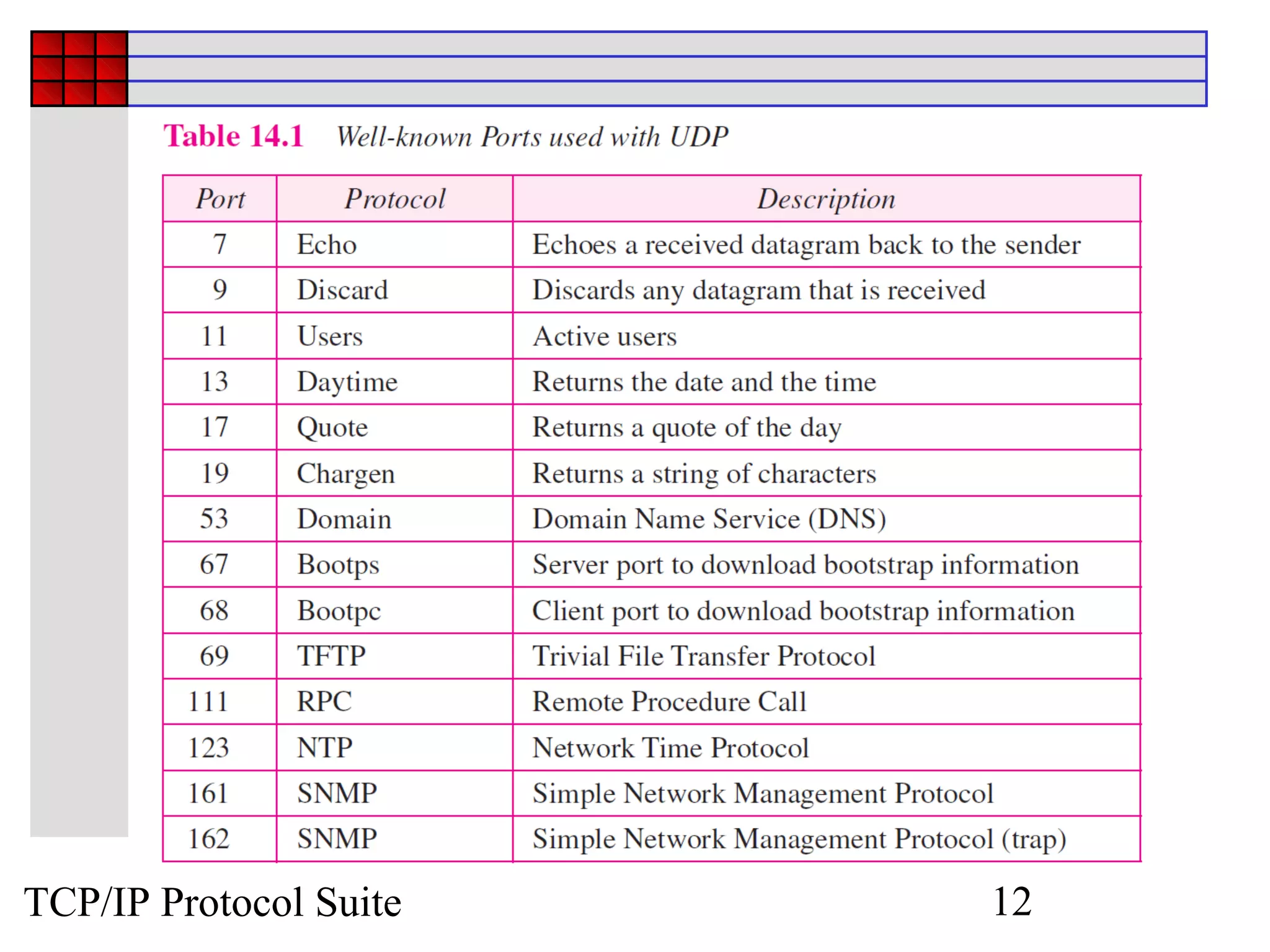
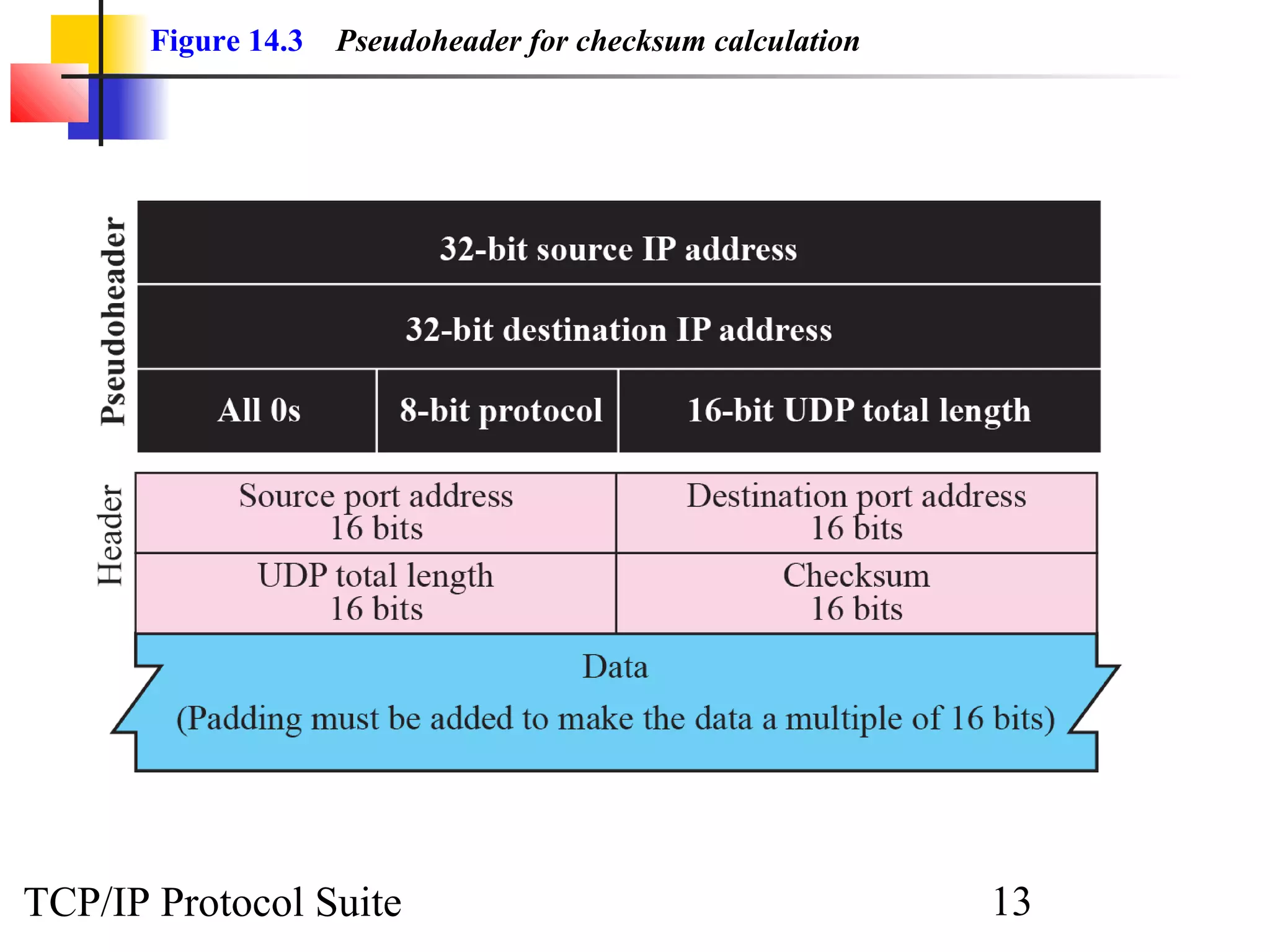
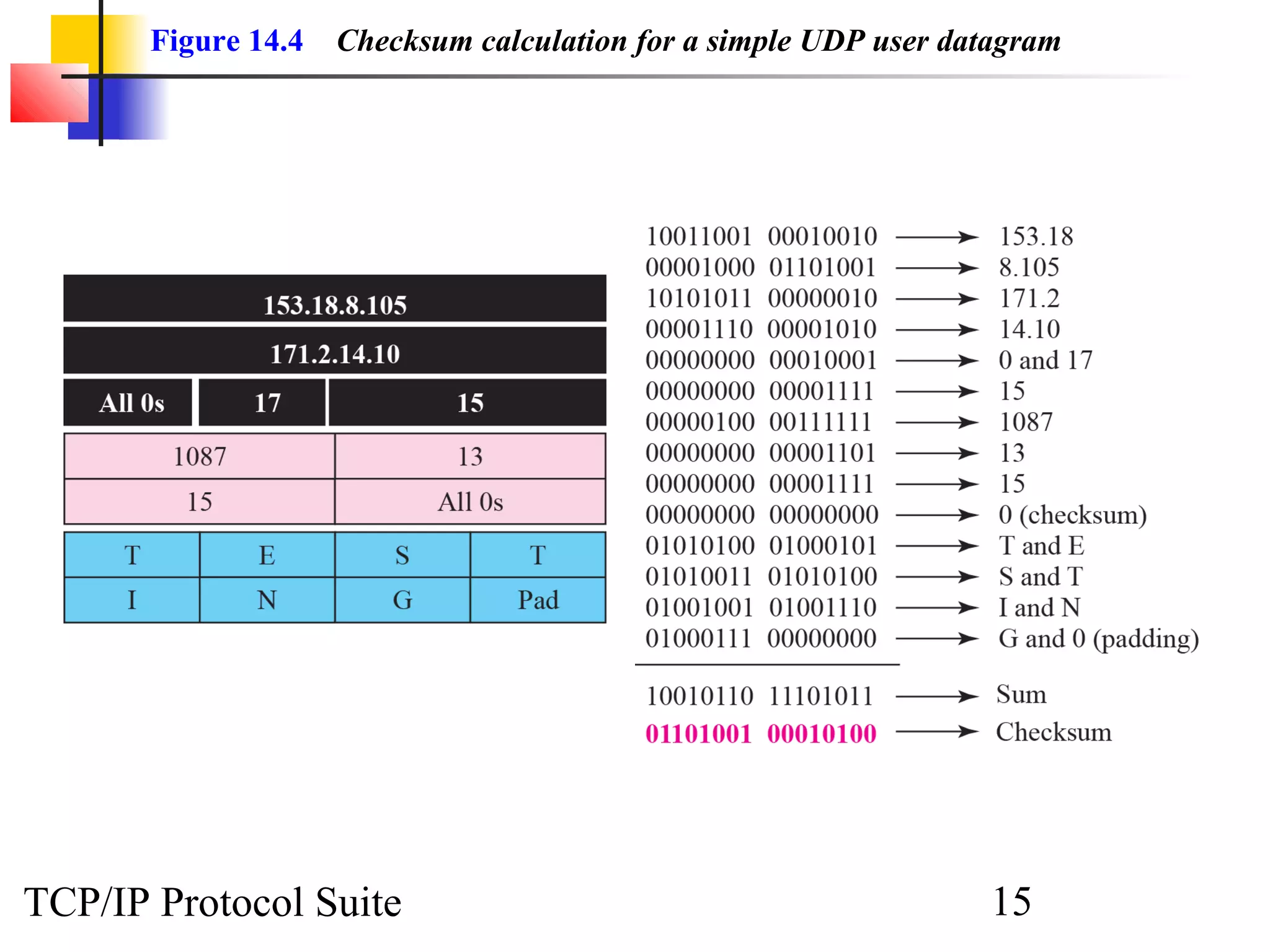
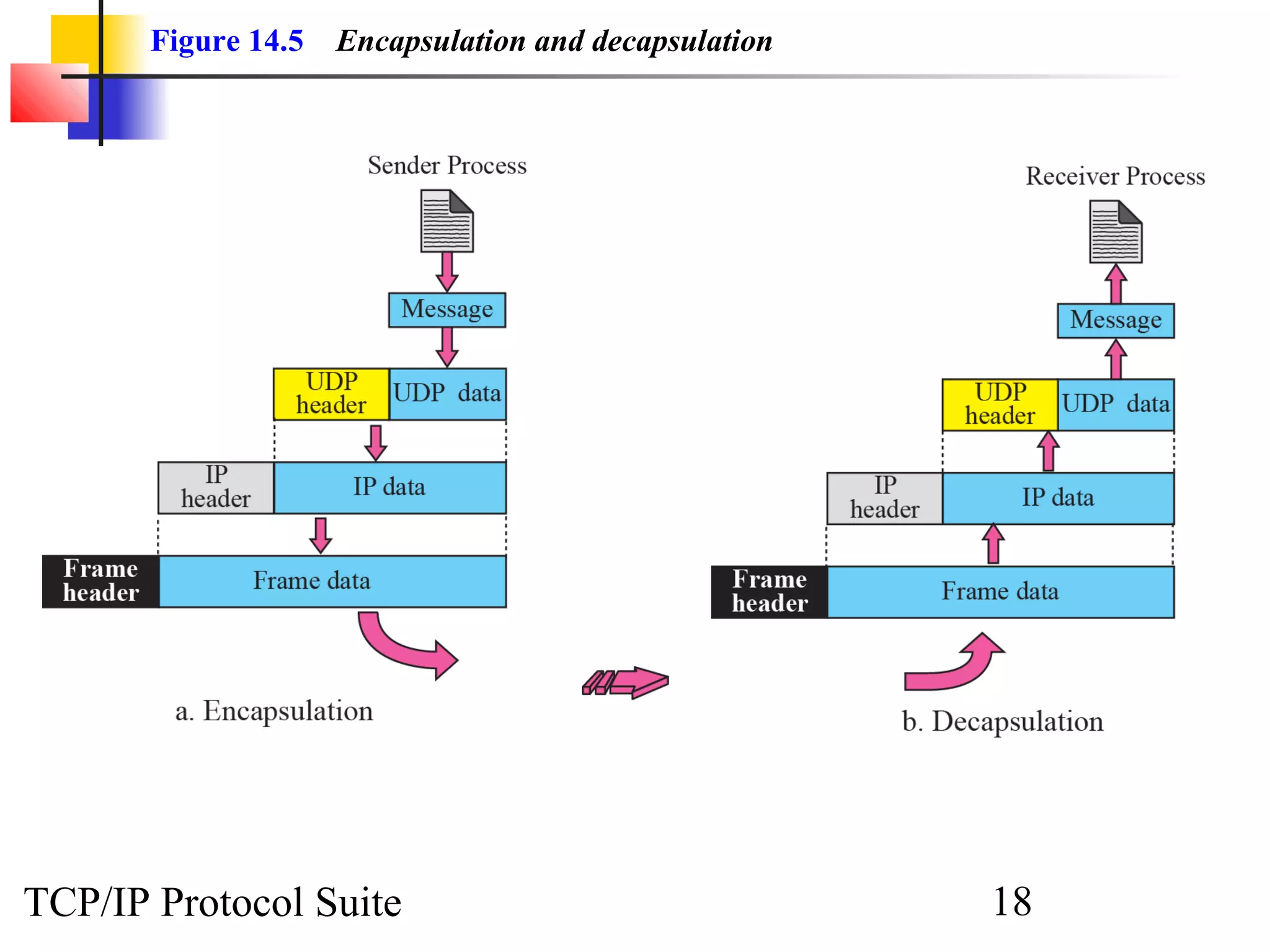
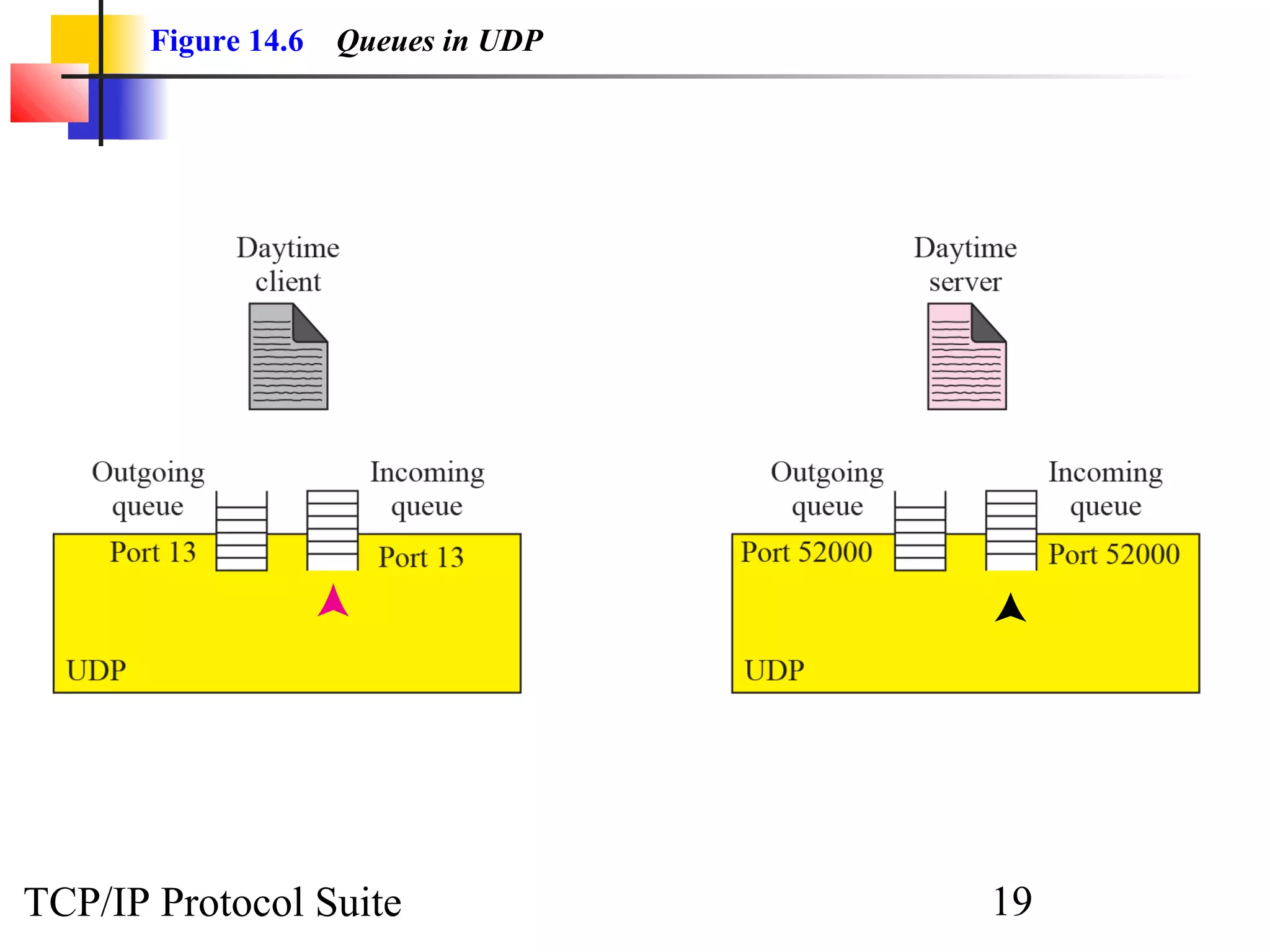
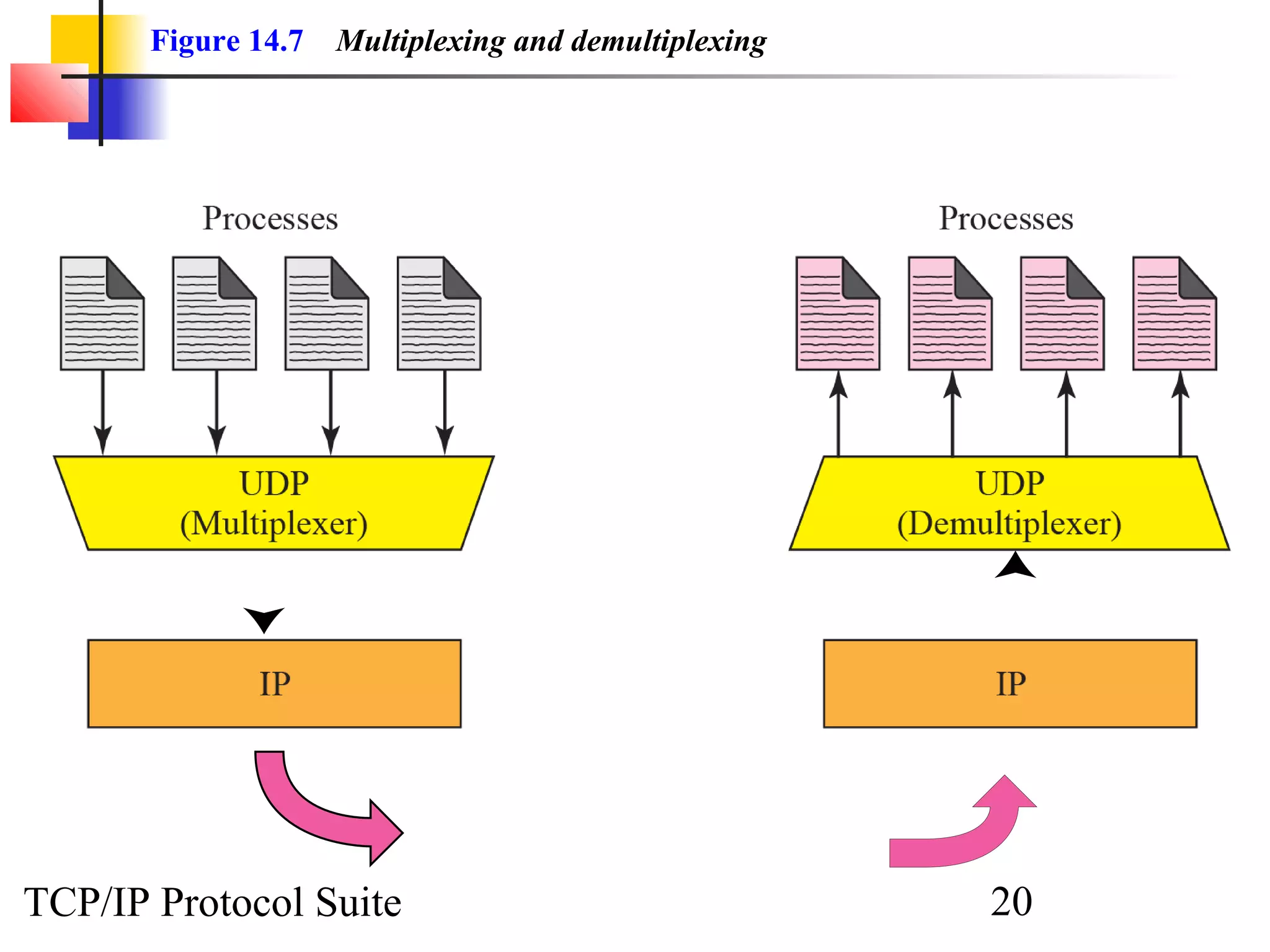
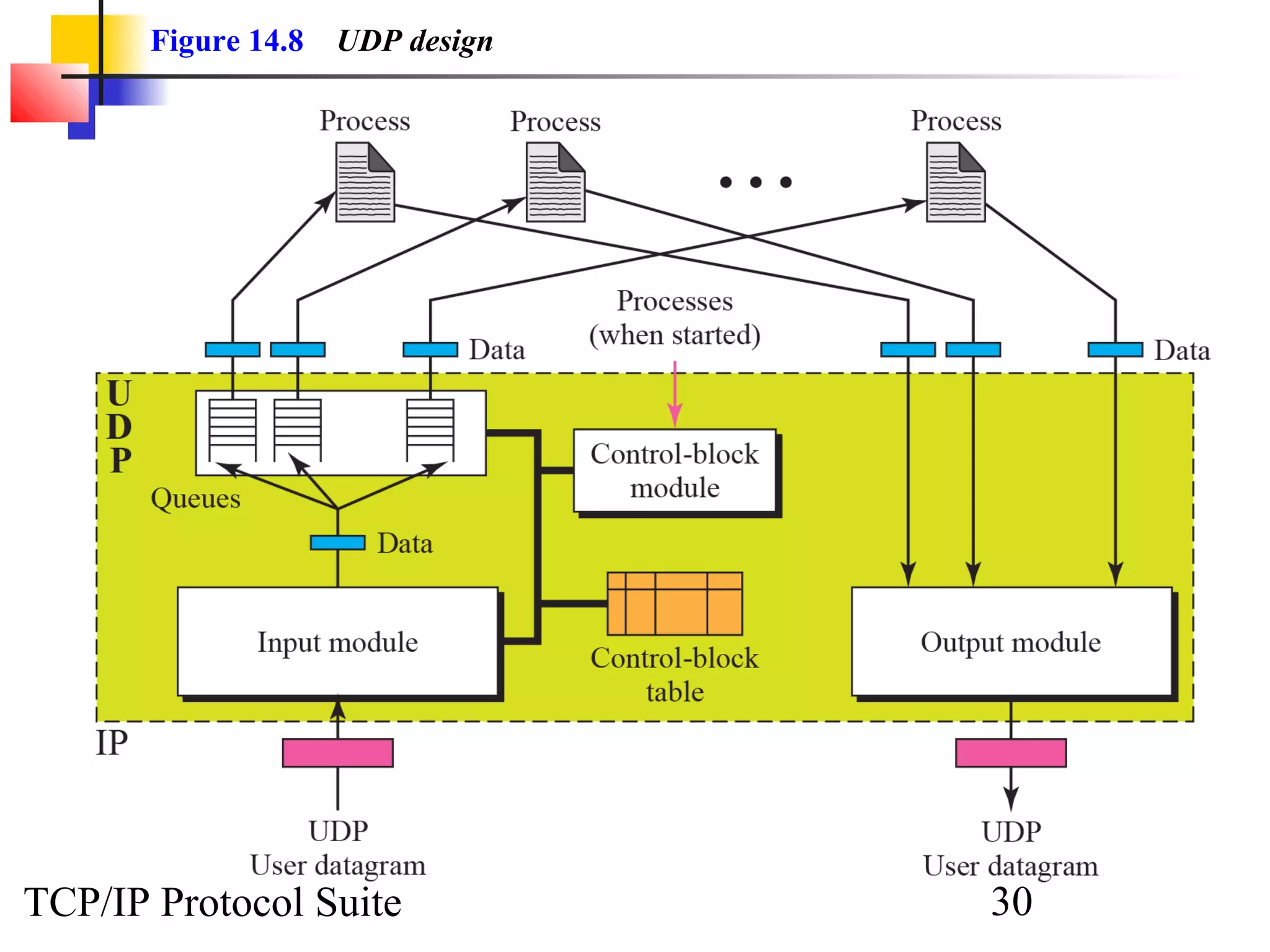
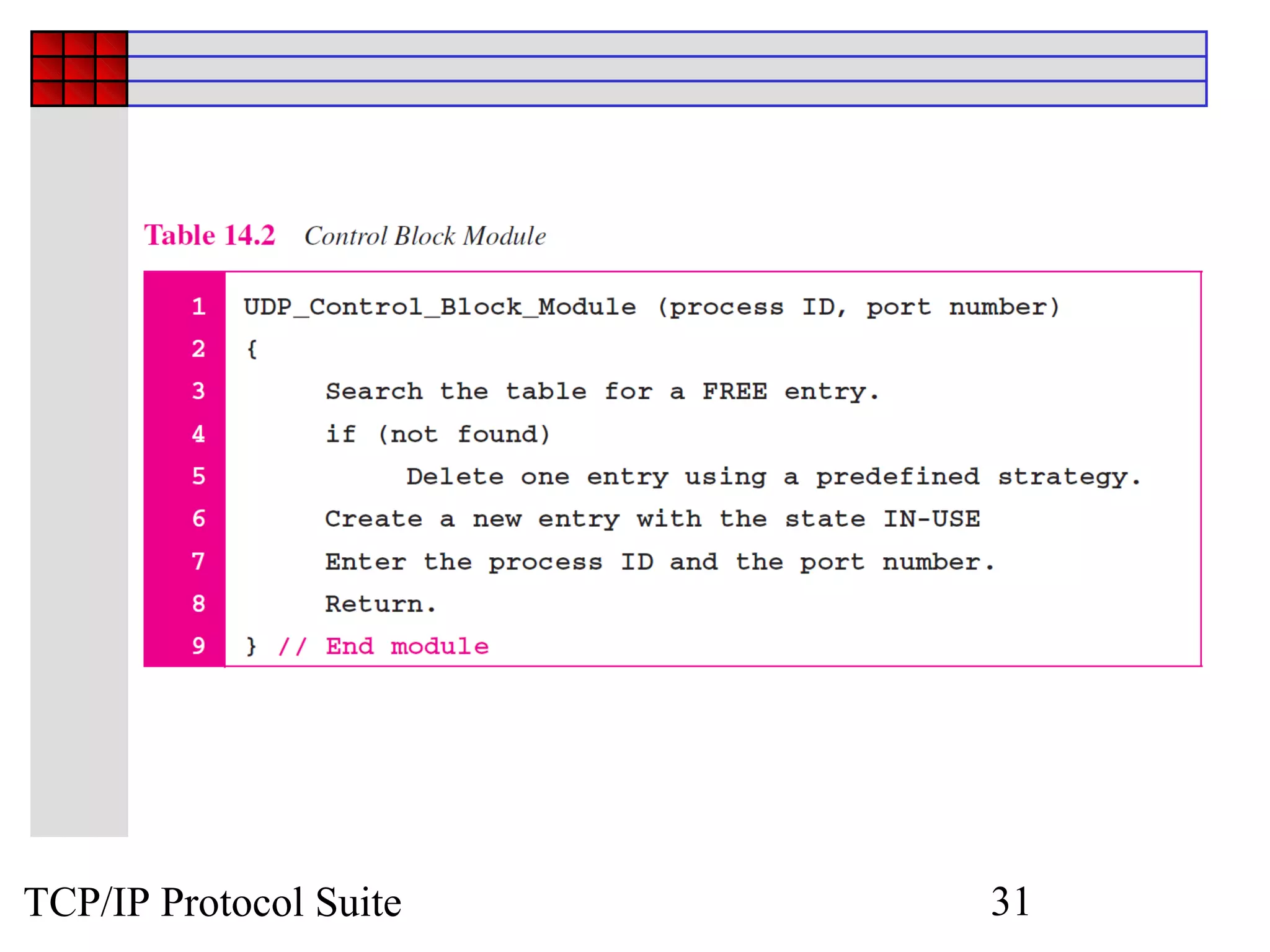
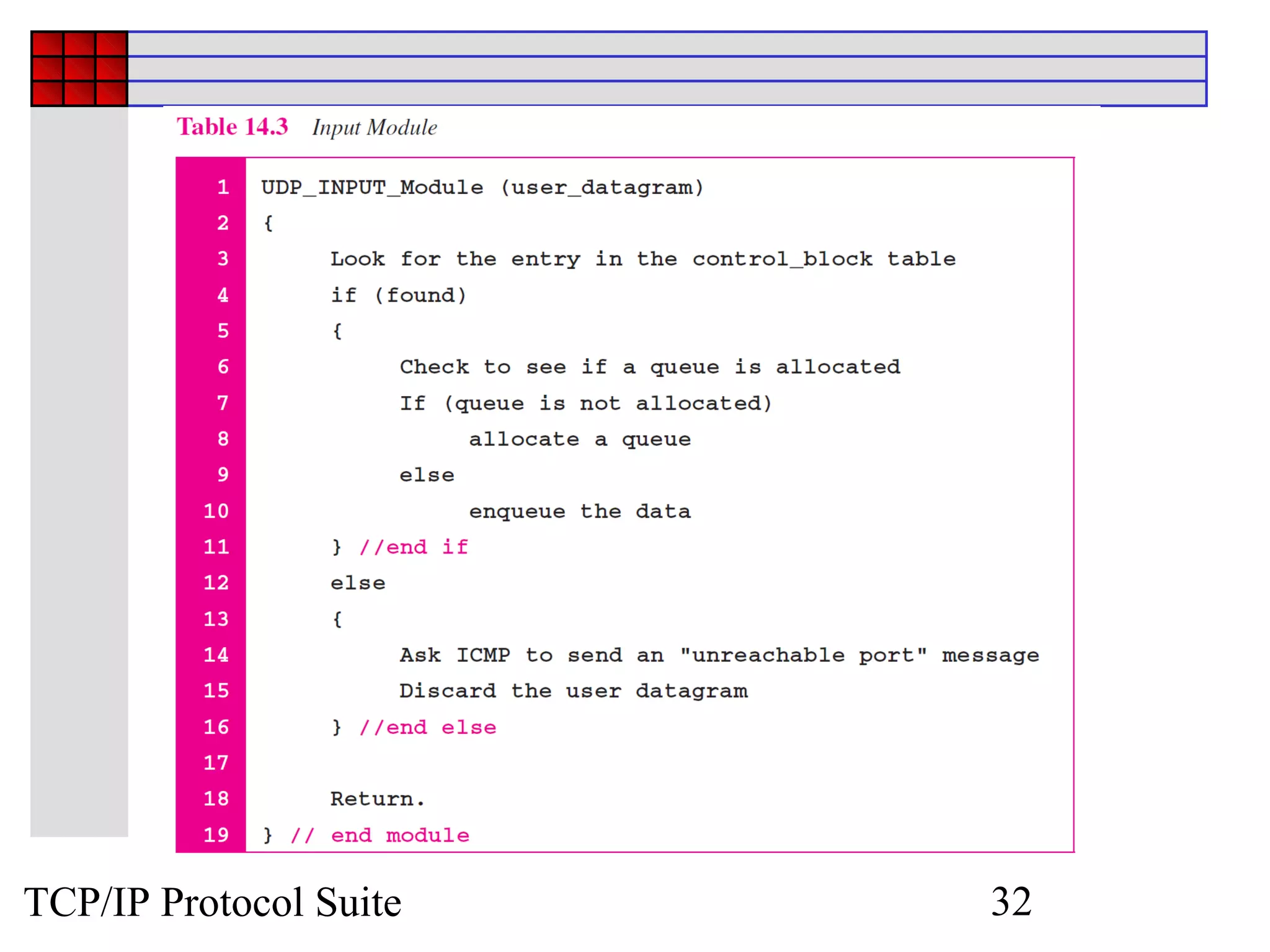
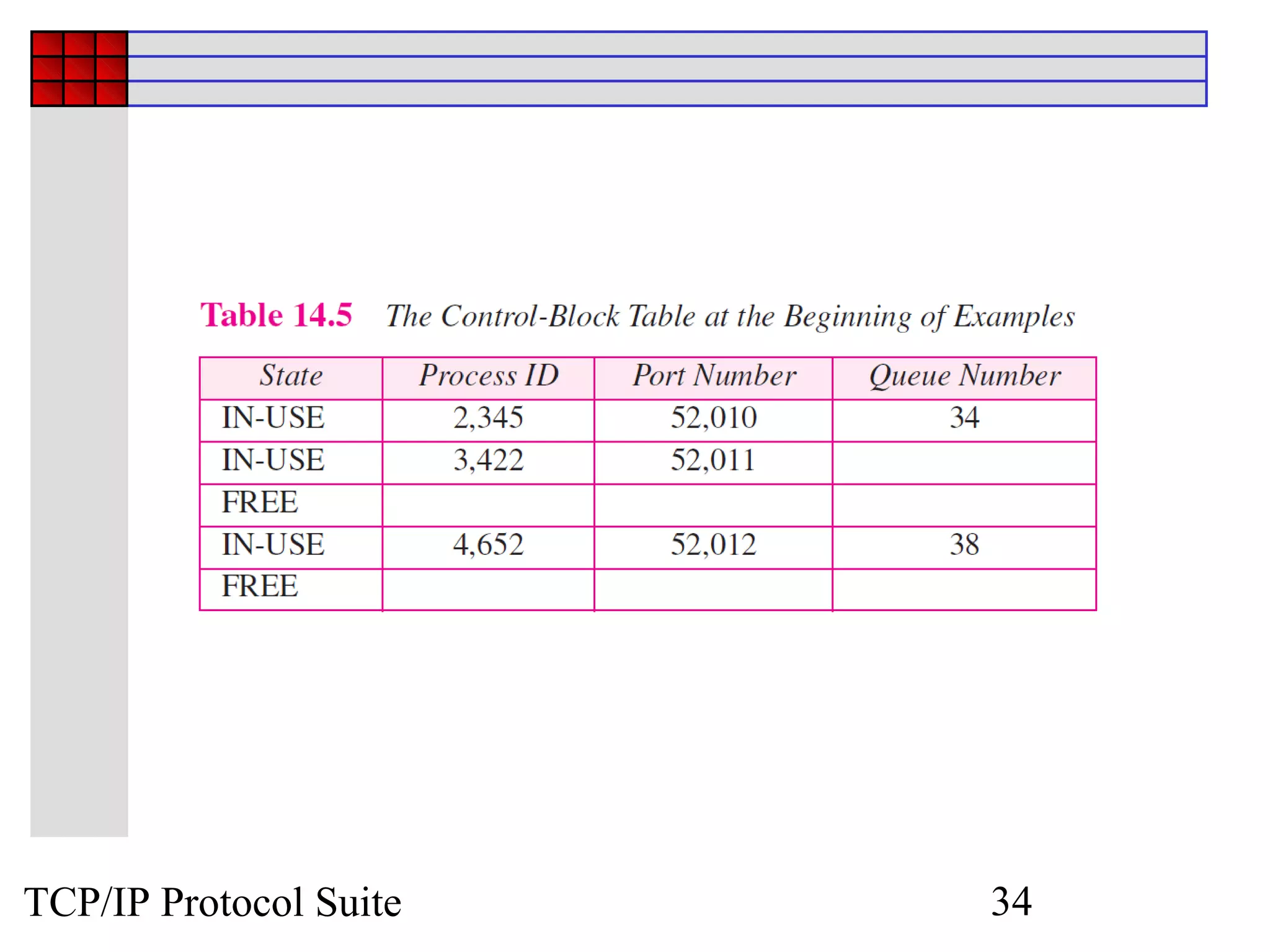
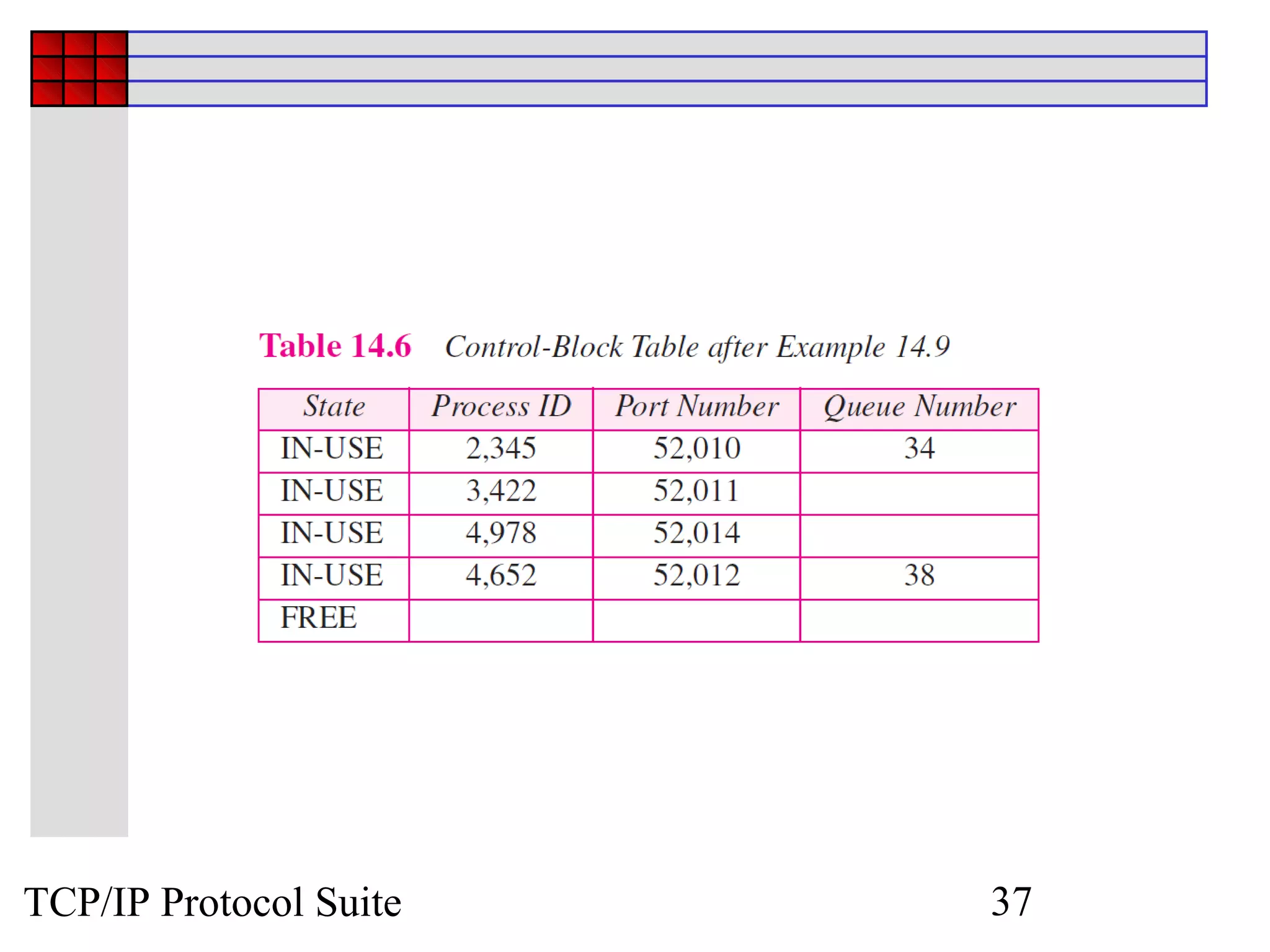
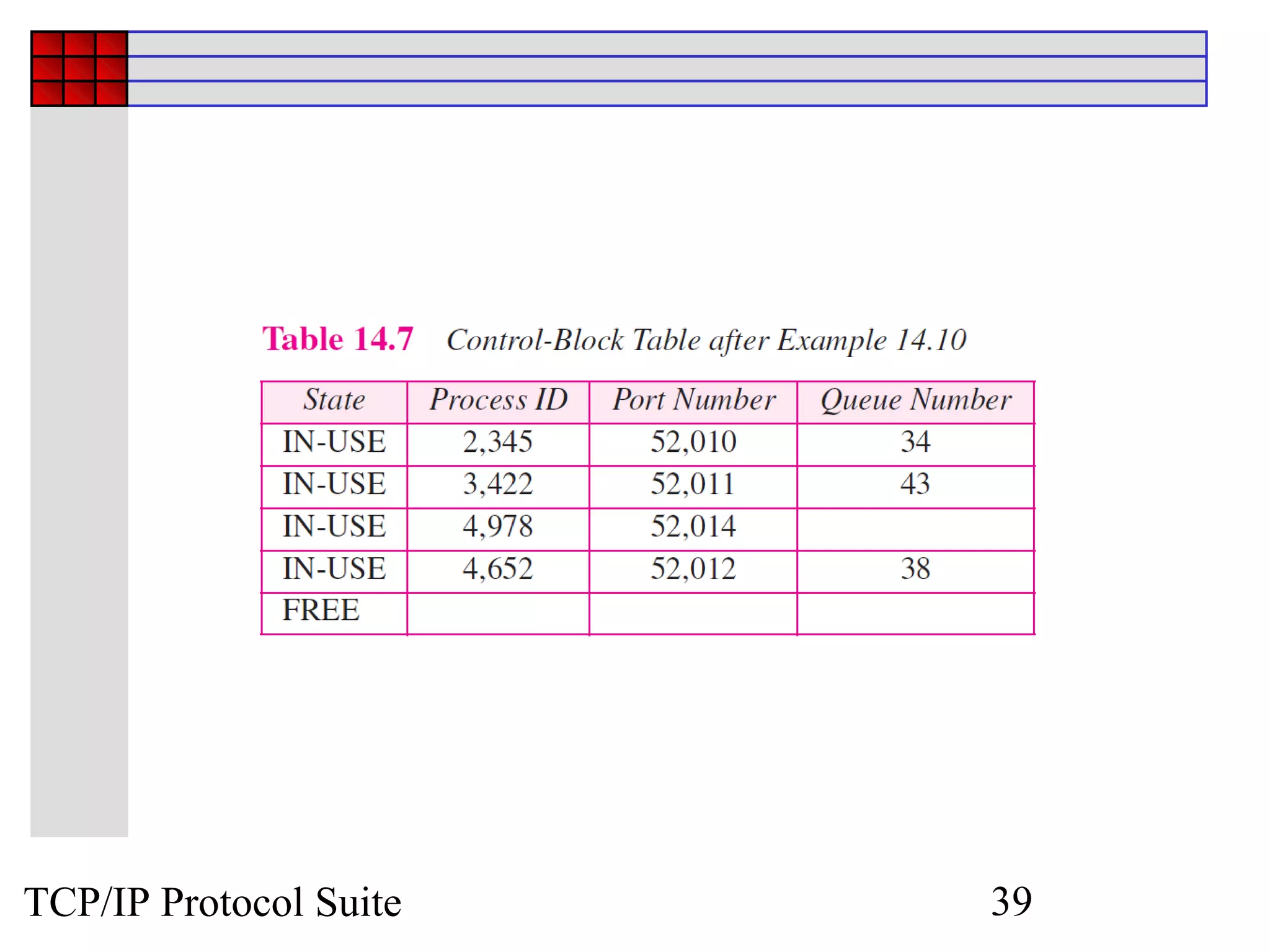
The document discusses the User Datagram Protocol (UDP) which is part of the TCP/IP protocol suite. UDP is located between the application layer and the IP layer and serves as an intermediary between application programs and network operations. UDP provides connectionless and unreliable data transfer through the use of datagrams which have a fixed header format containing source and destination port numbers as well as length fields. While UDP does not provide many typical transport layer services like flow control or error correction, it is useful for applications requiring low-latency or real-time data delivery. The document outlines UDP's position, packet format, services, applications, and basic internal package structure.