The document discusses several network security protocols:
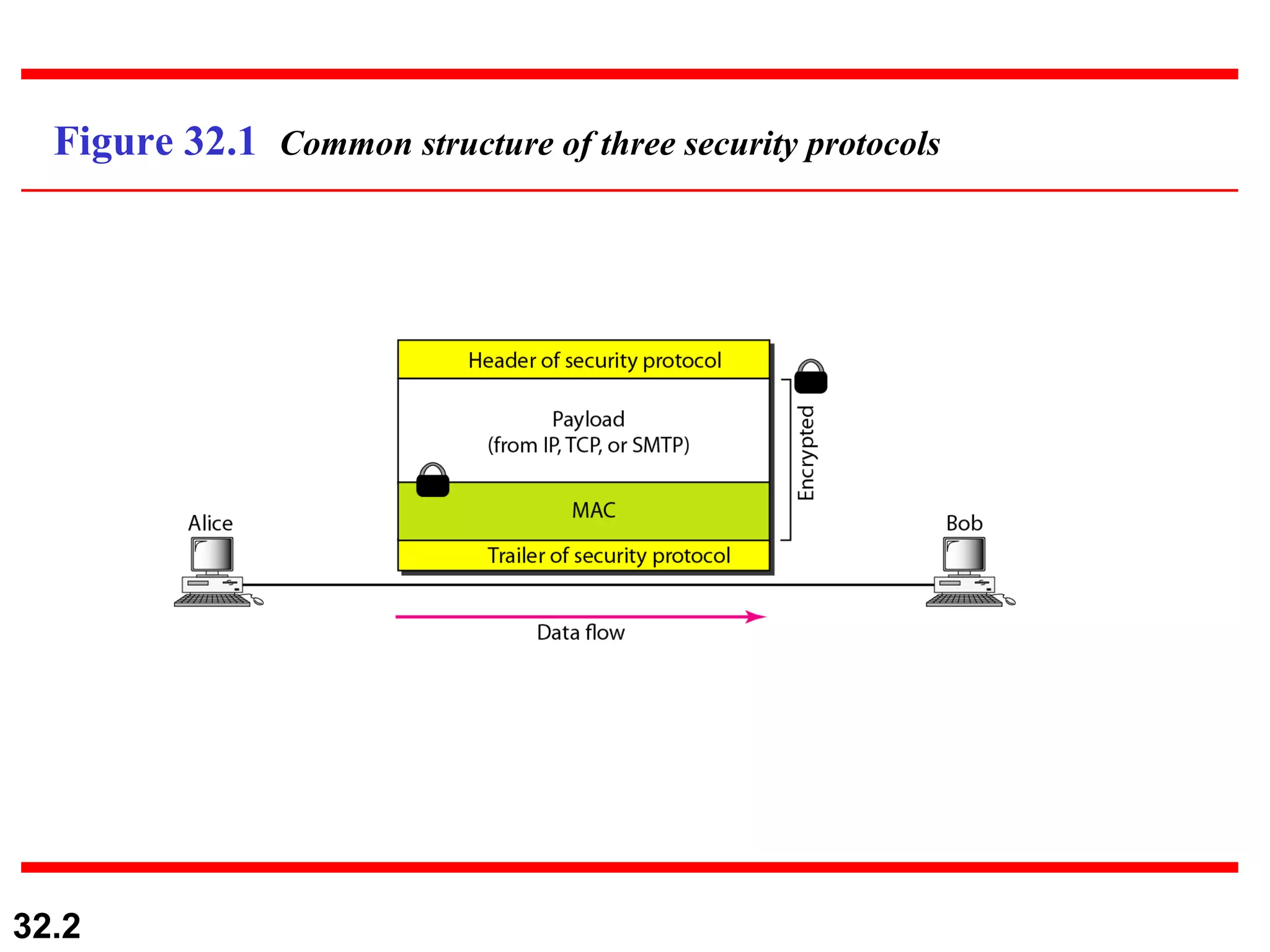
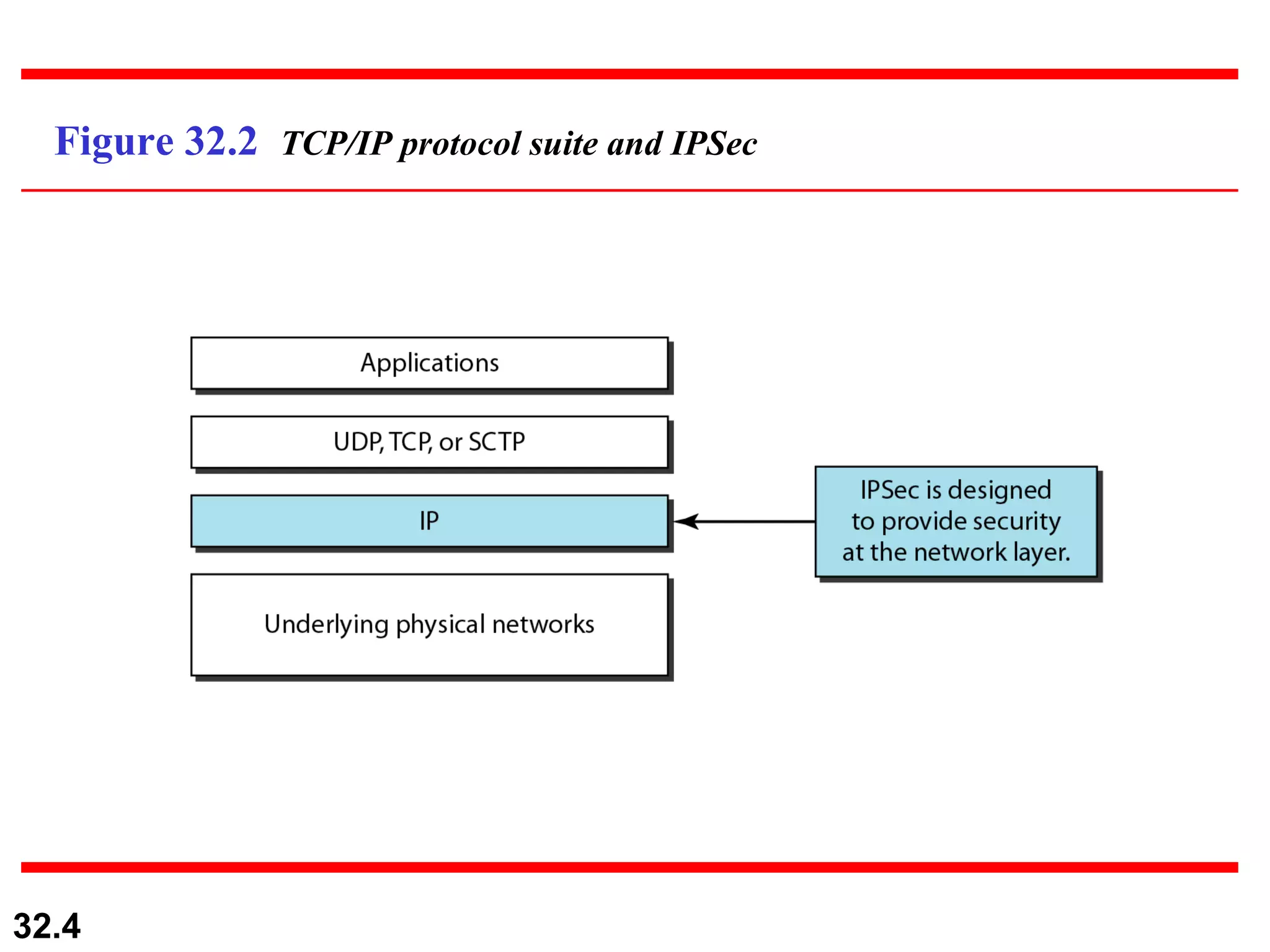
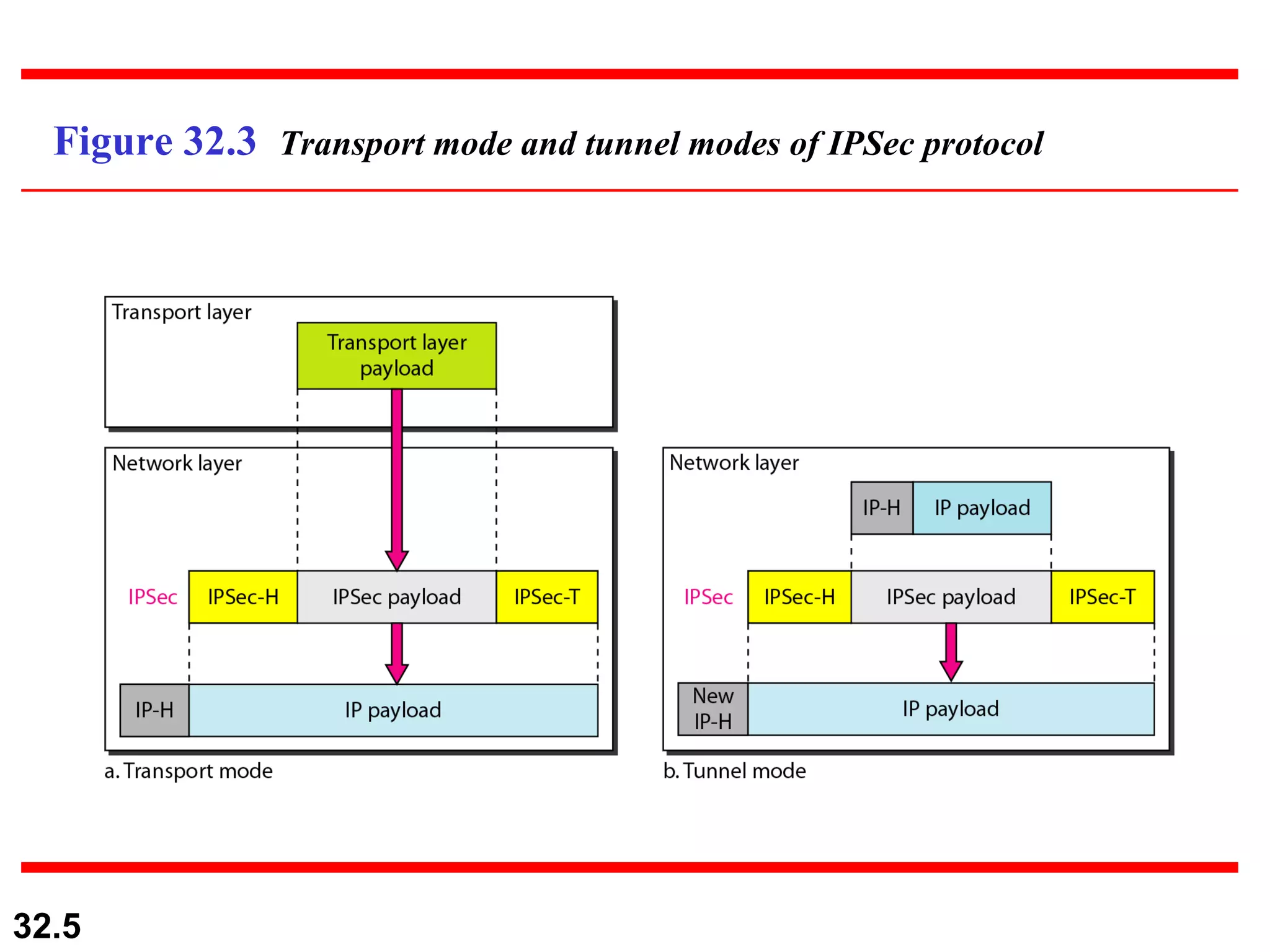
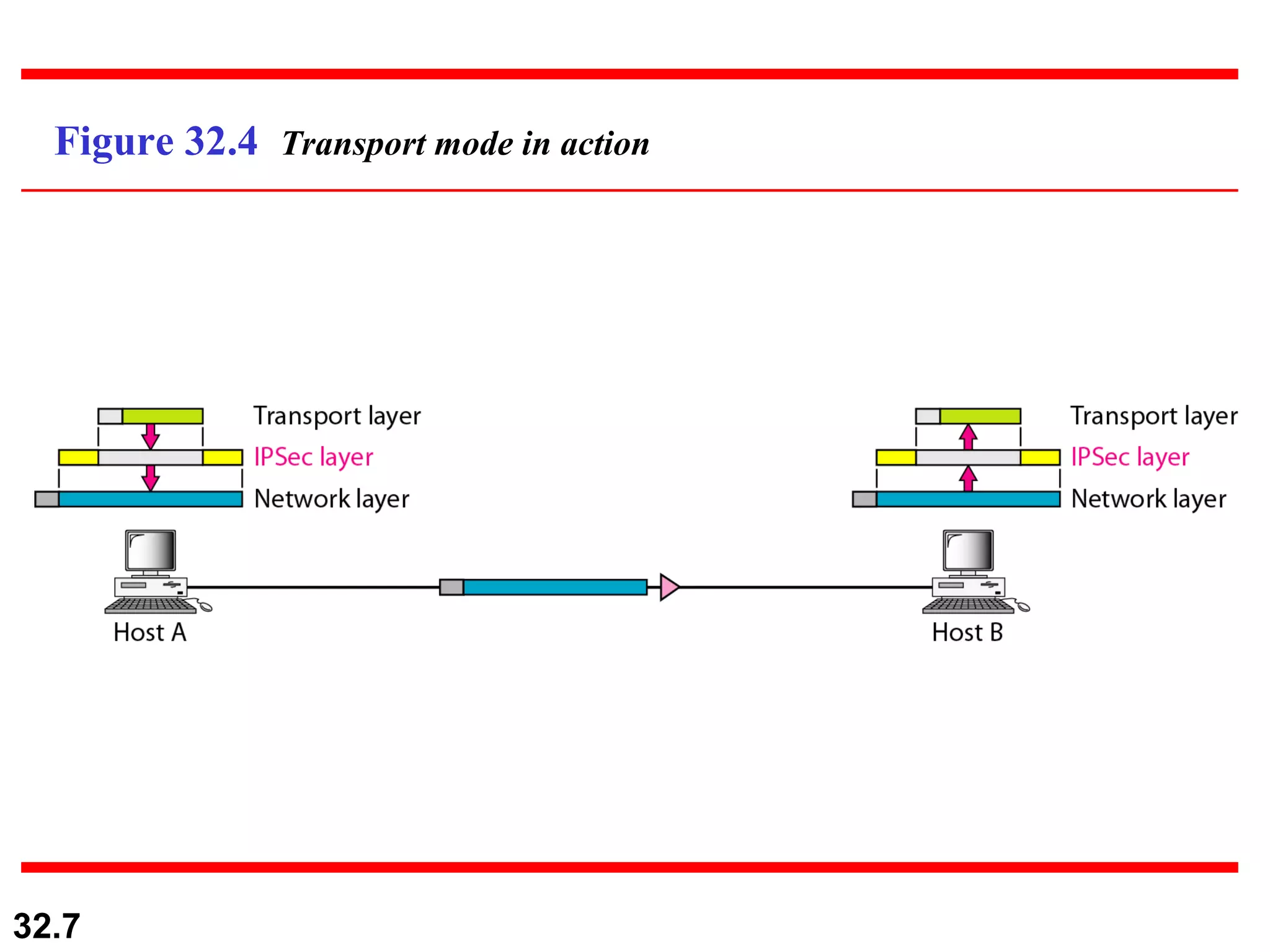
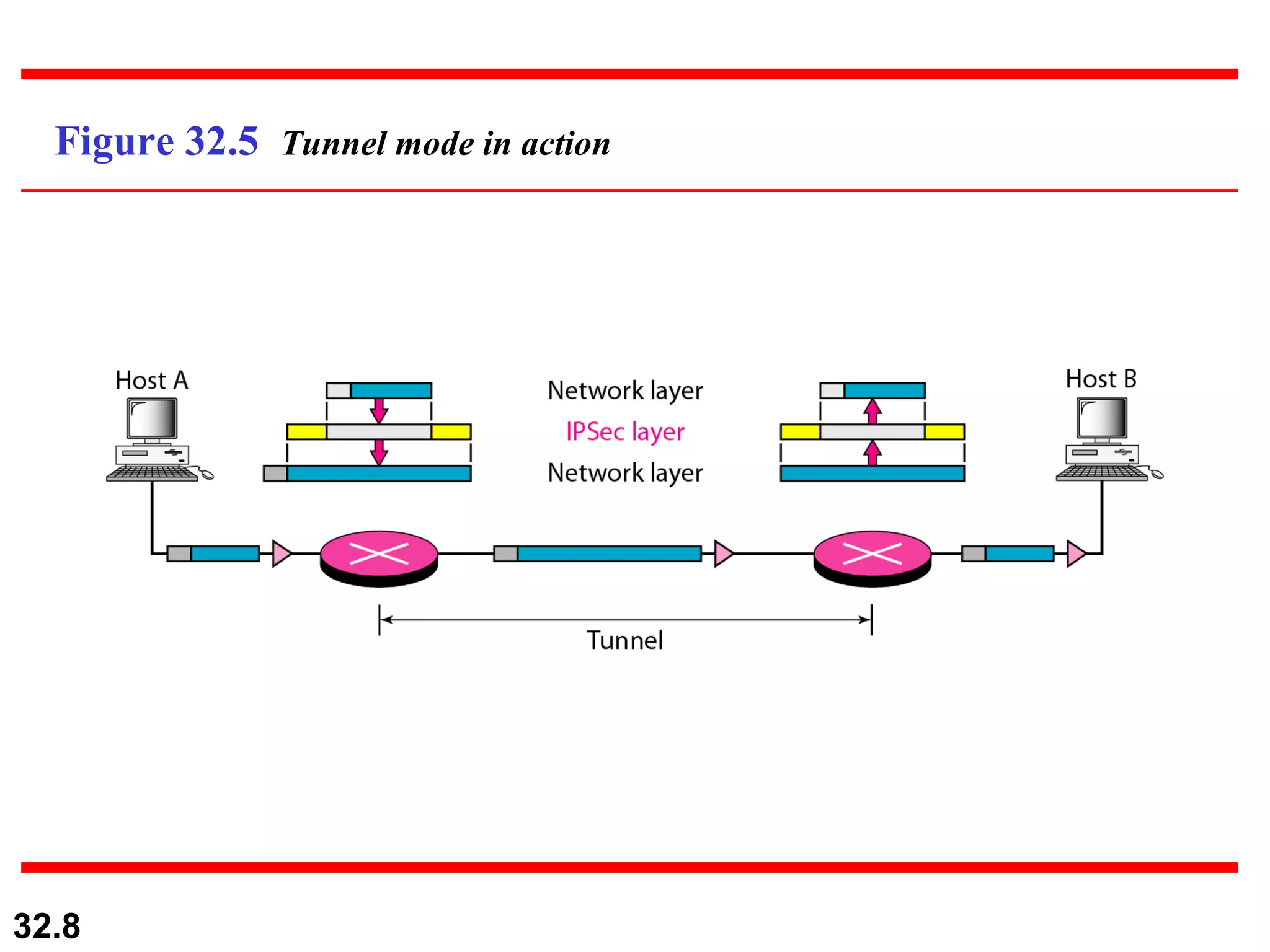
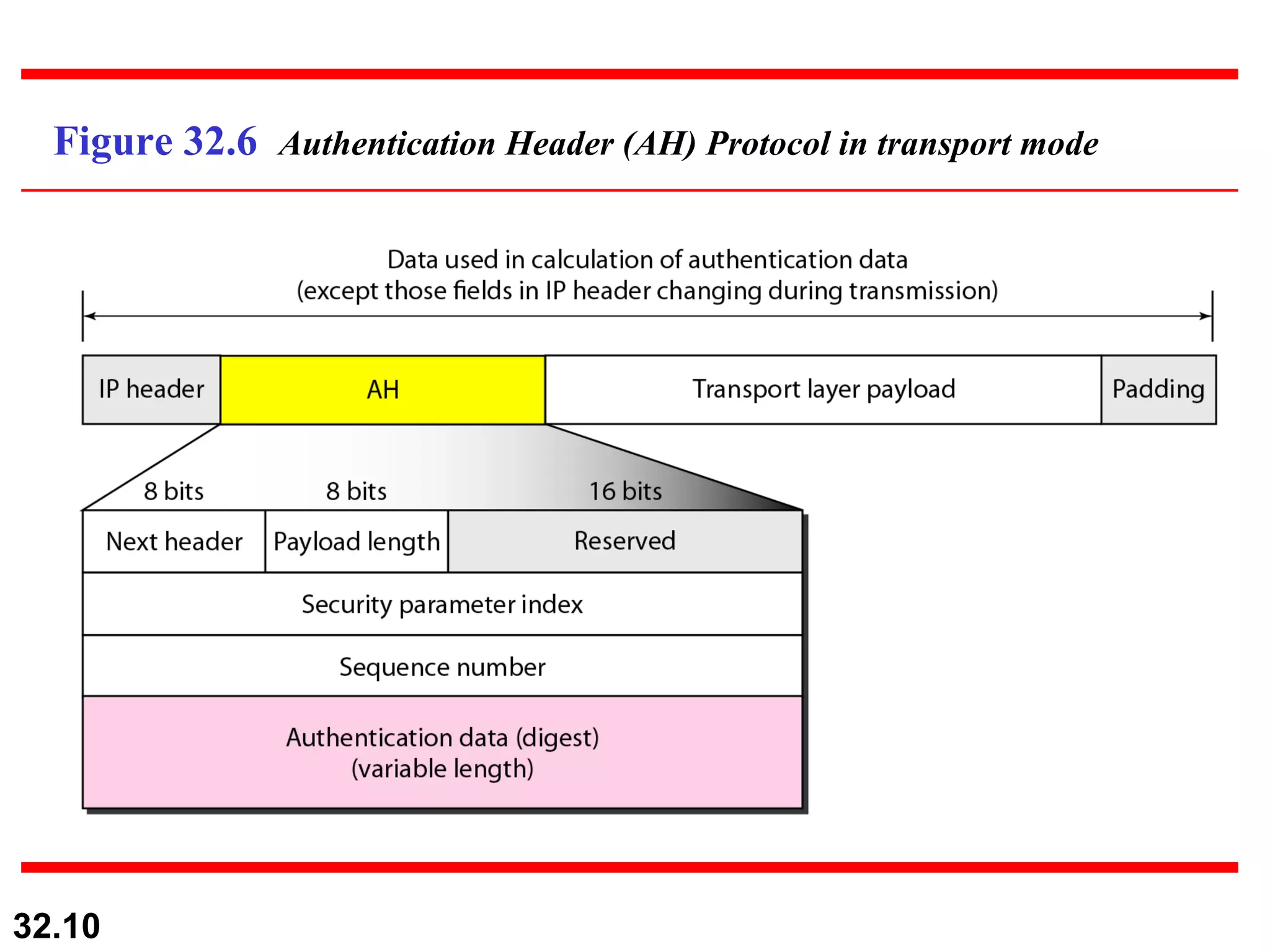
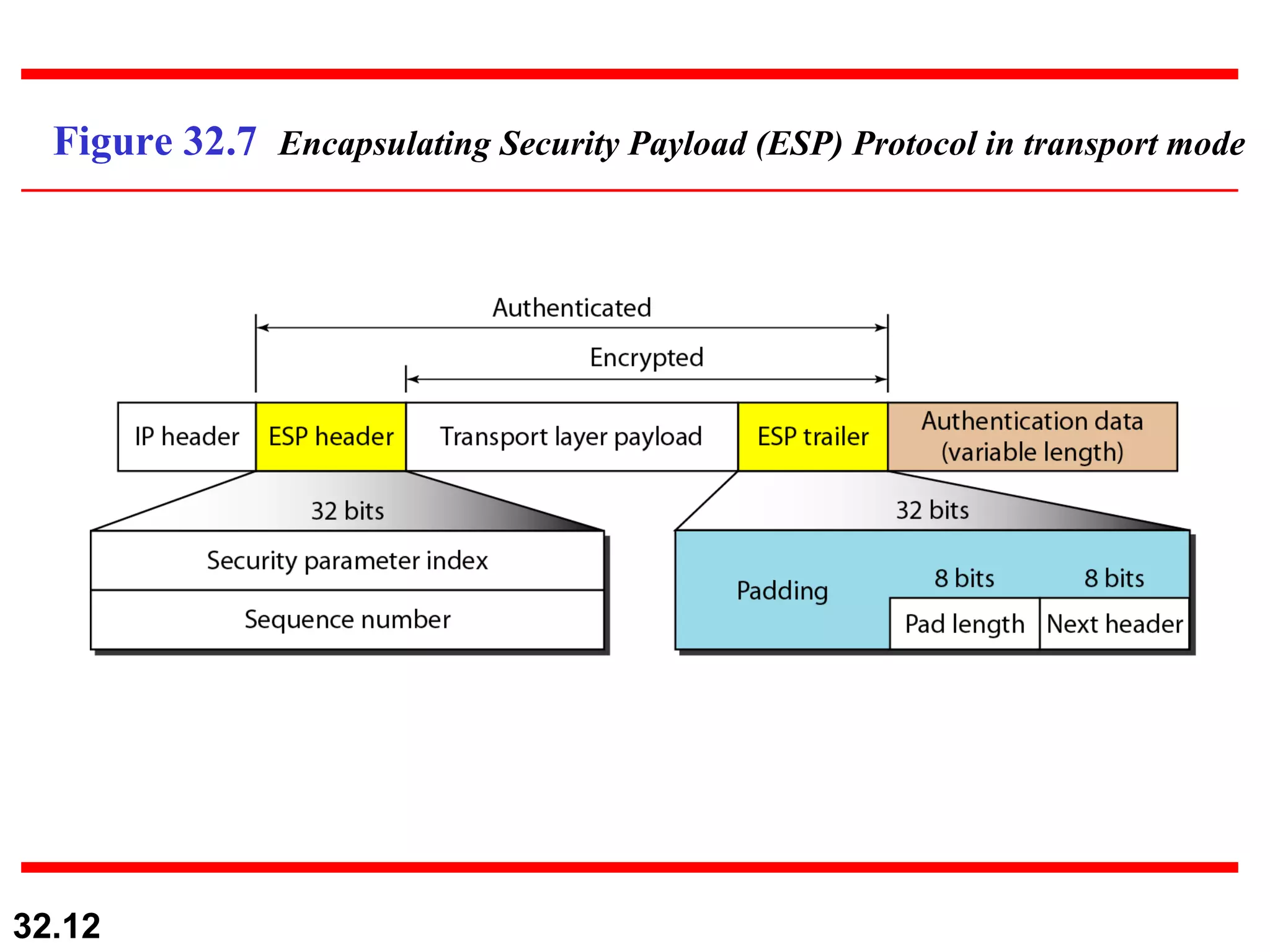
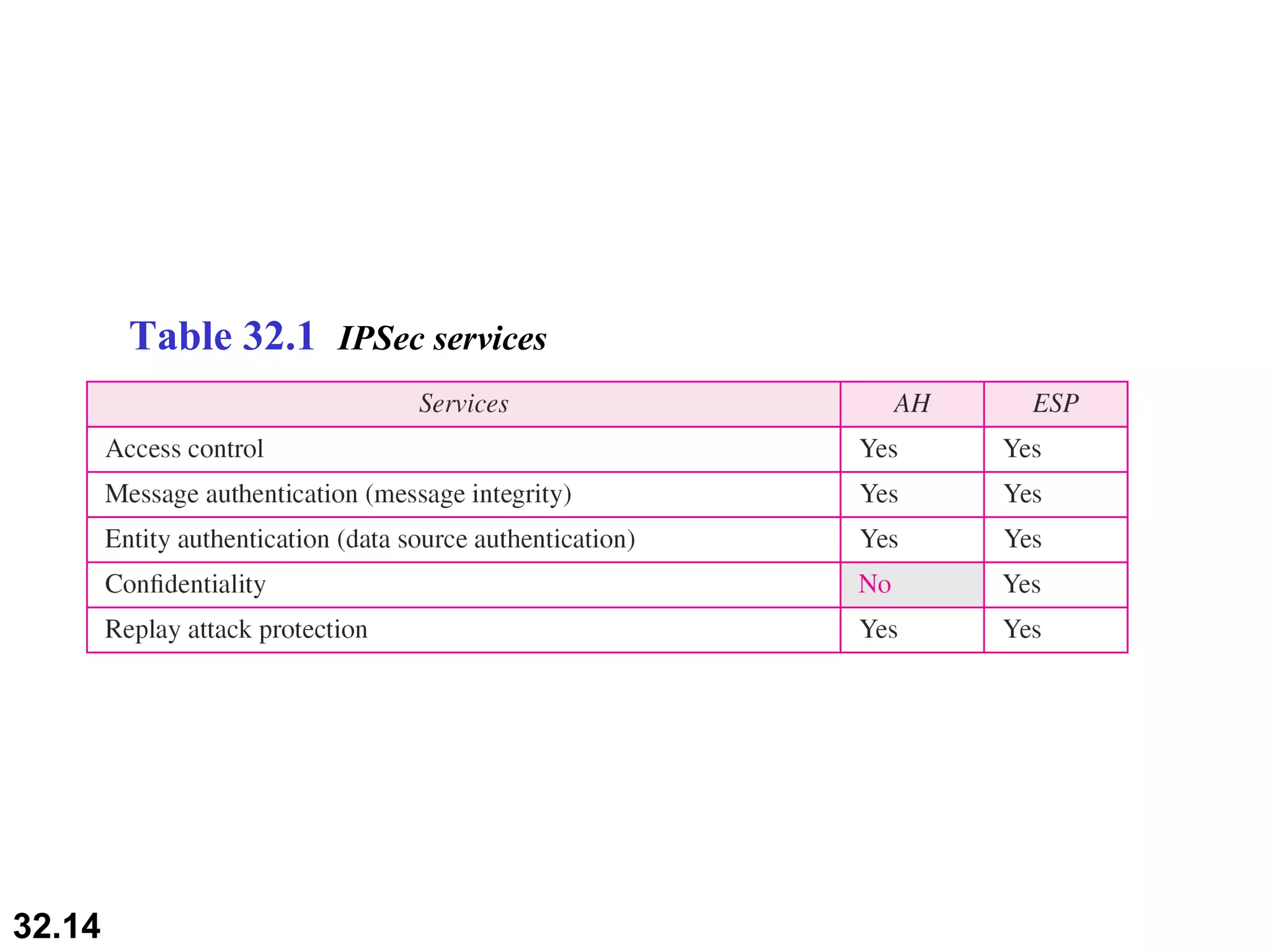
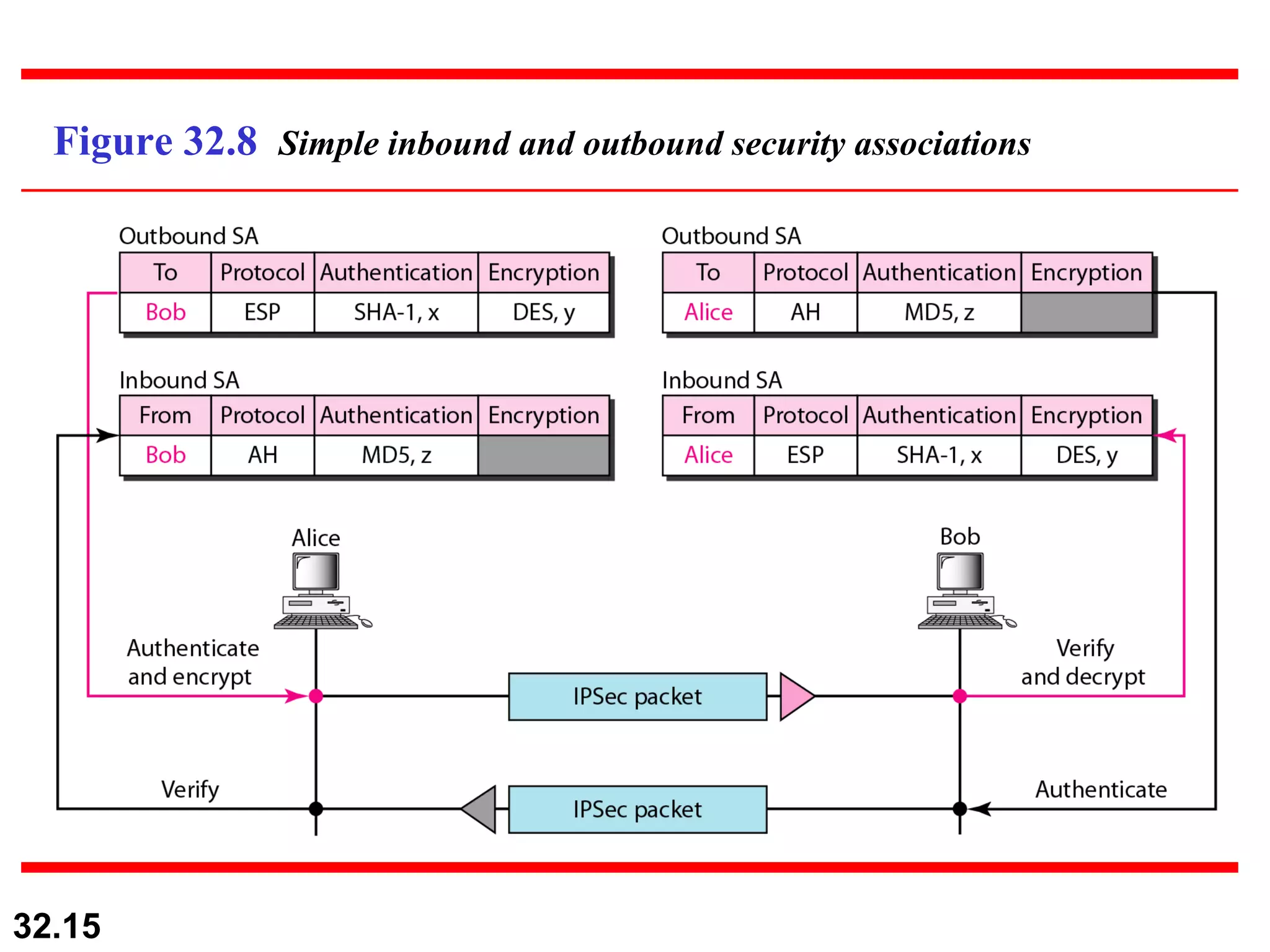
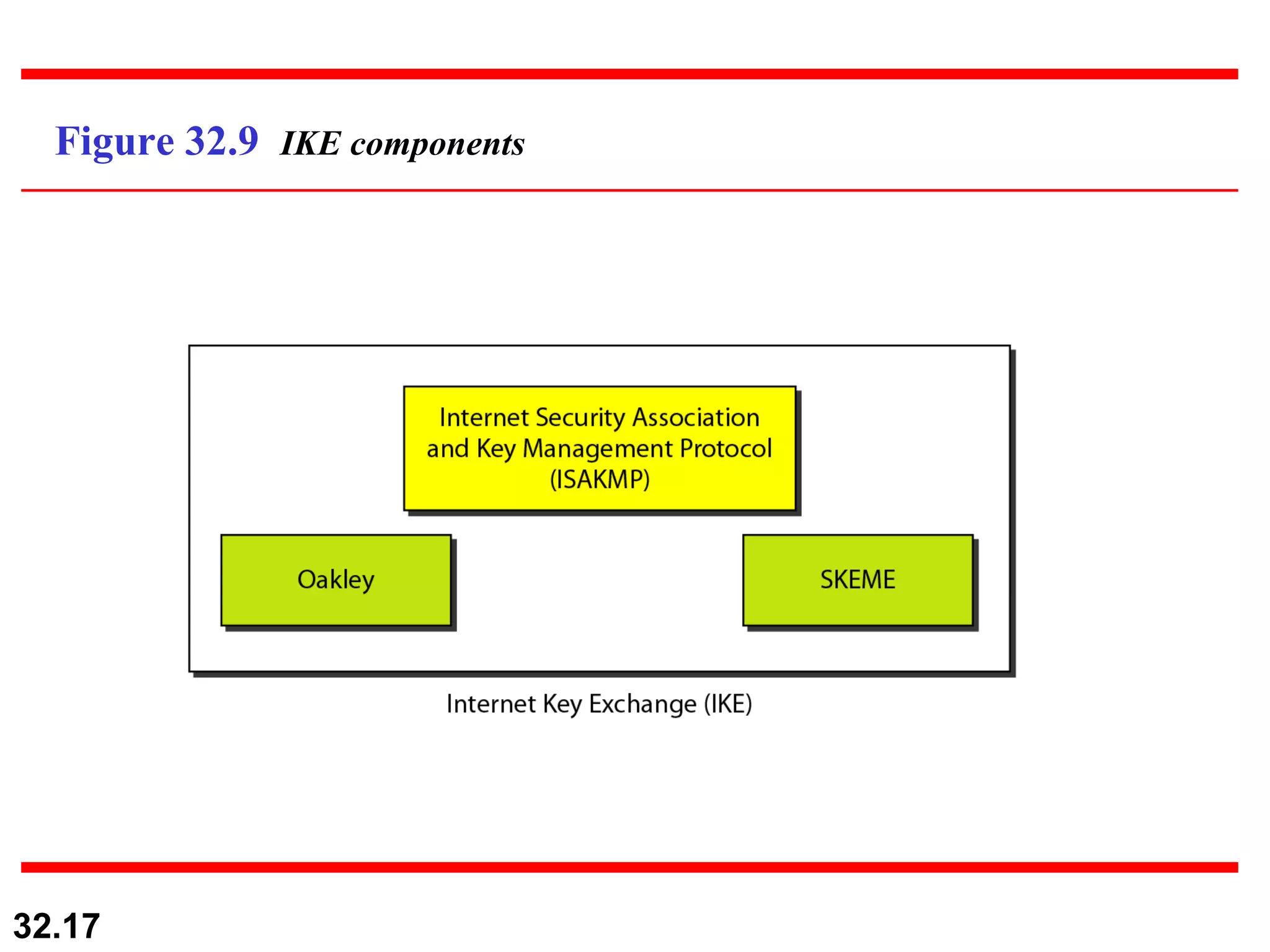
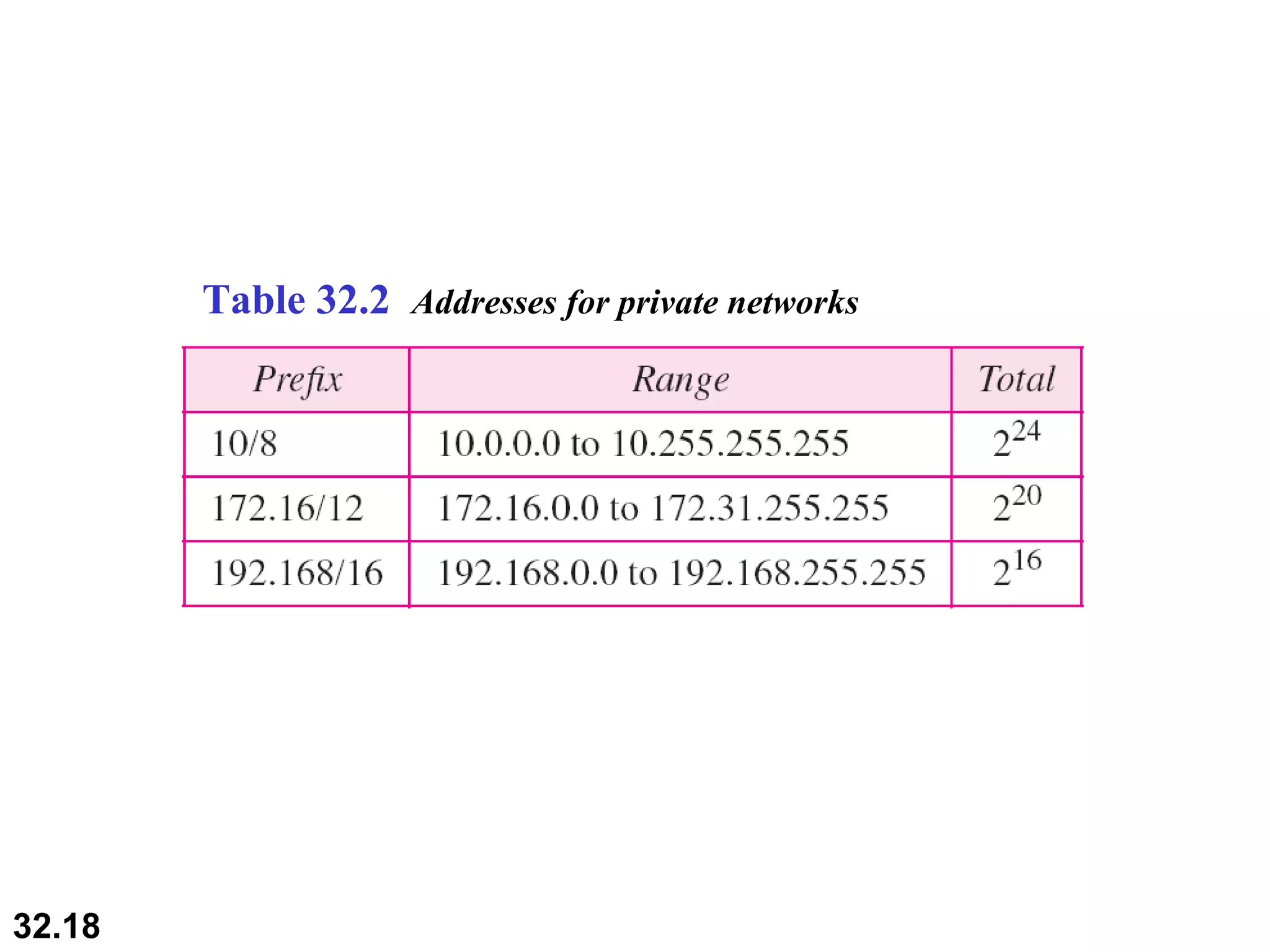
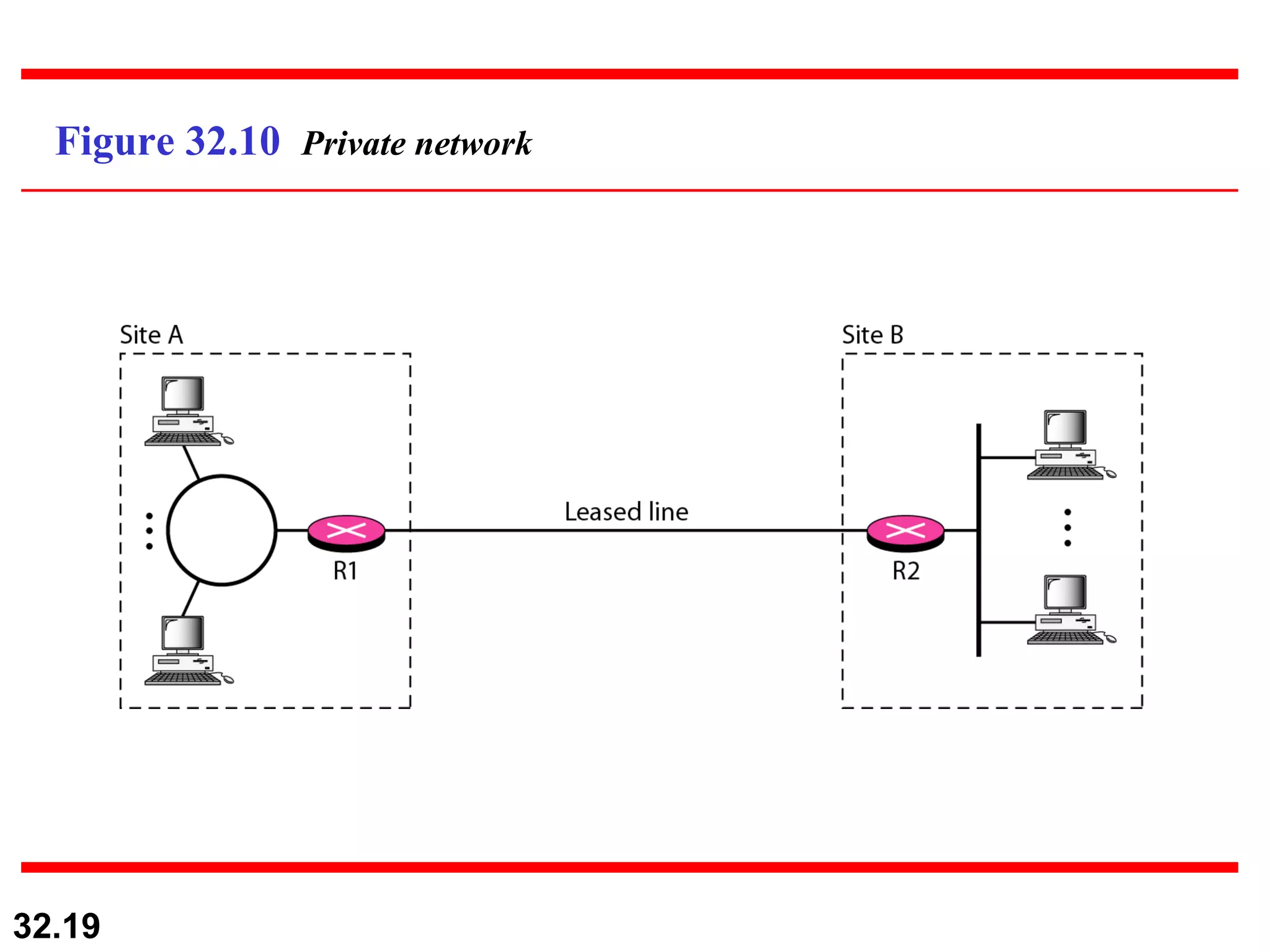
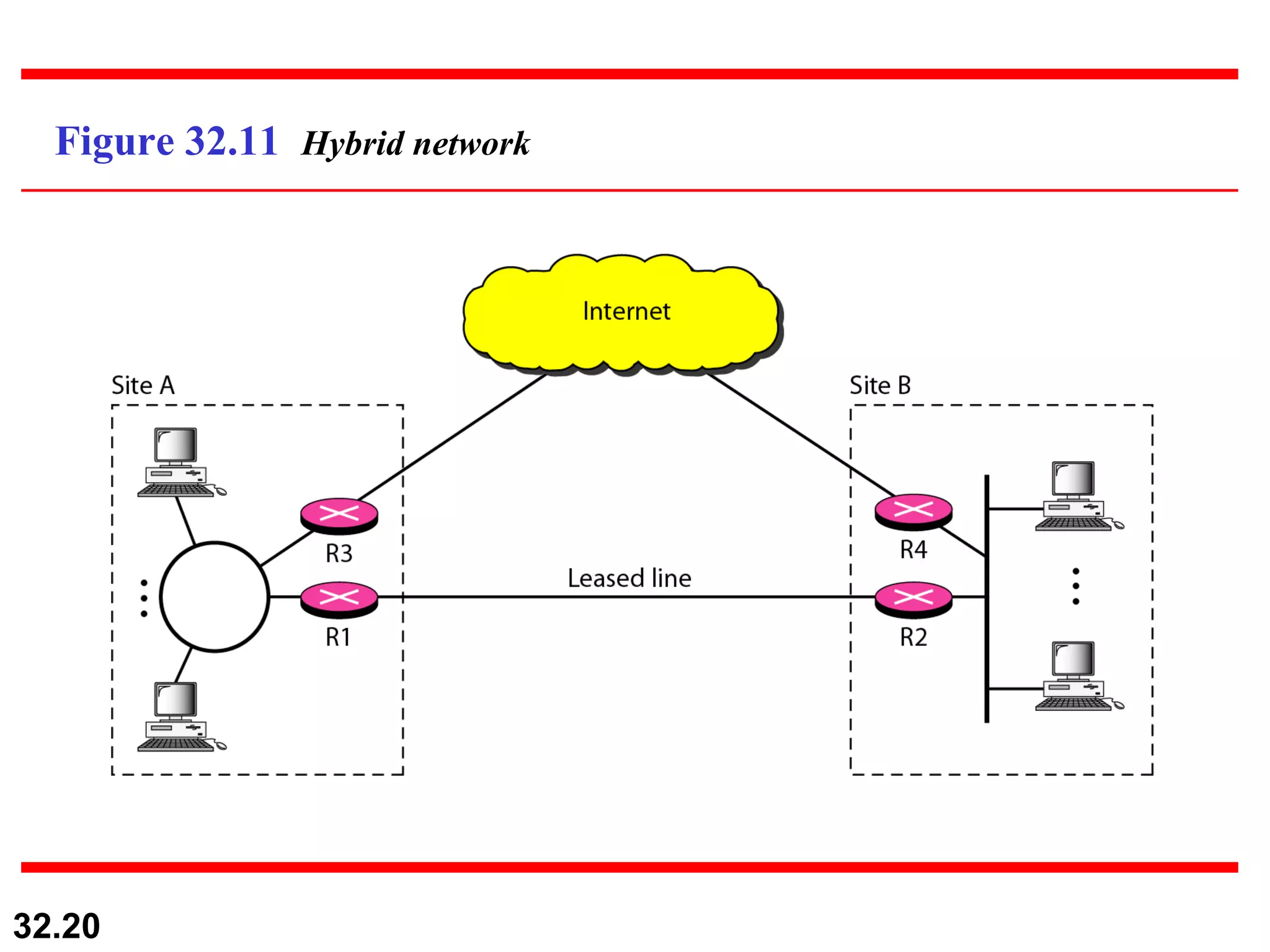
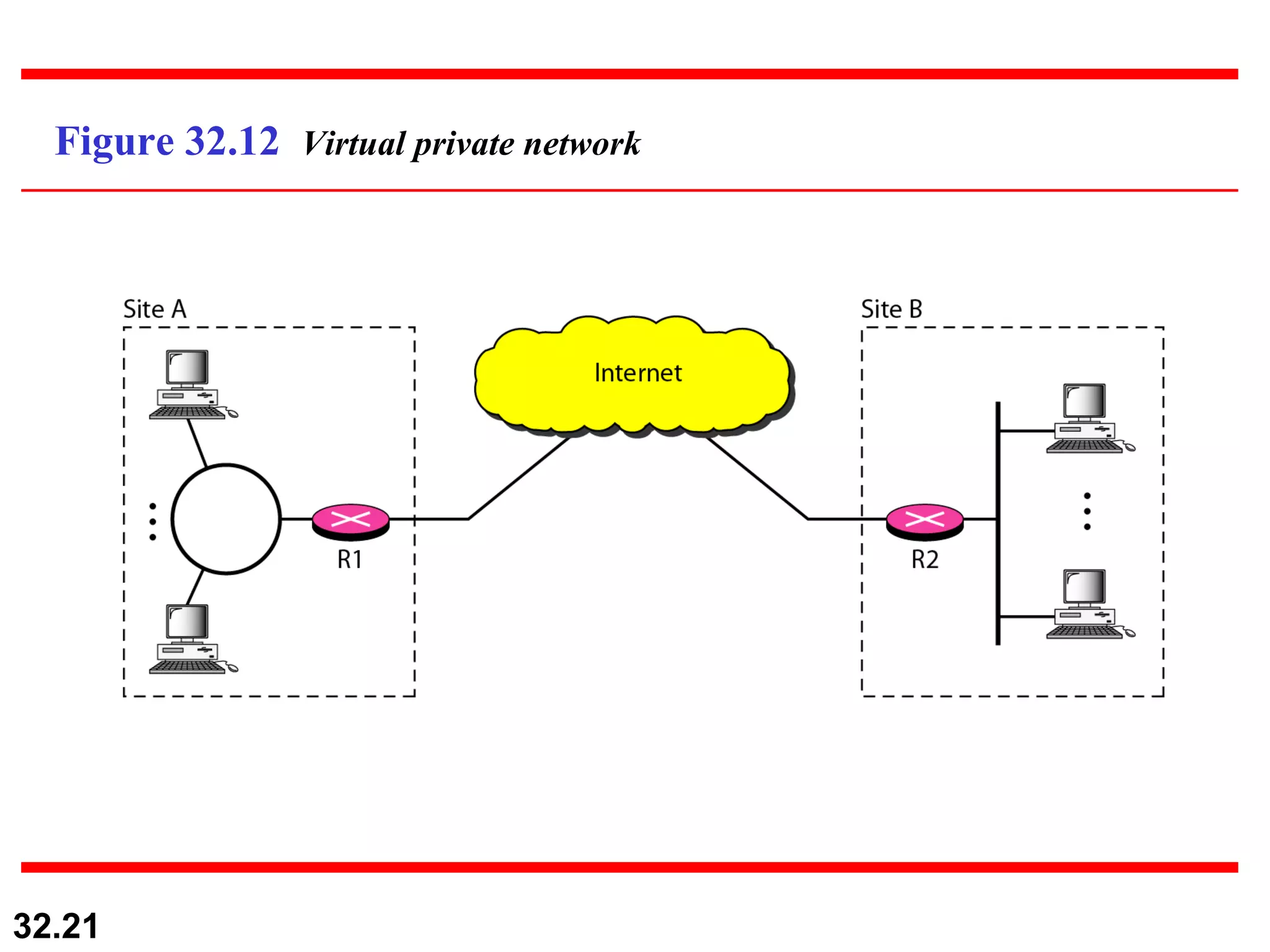
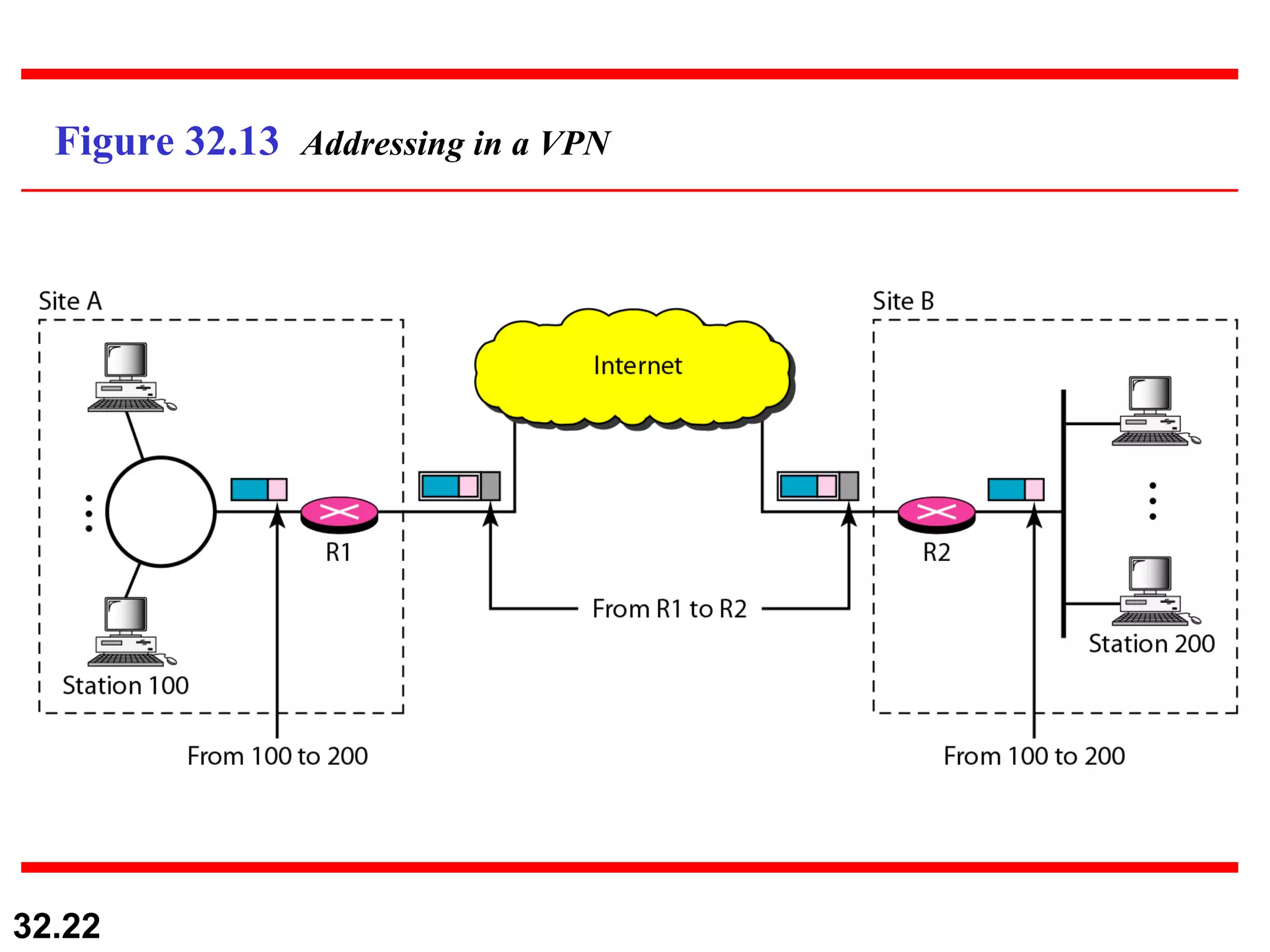
1) IPSec provides security at the network layer and has two modes - transport and tunnel. It uses IKE to establish security associations.
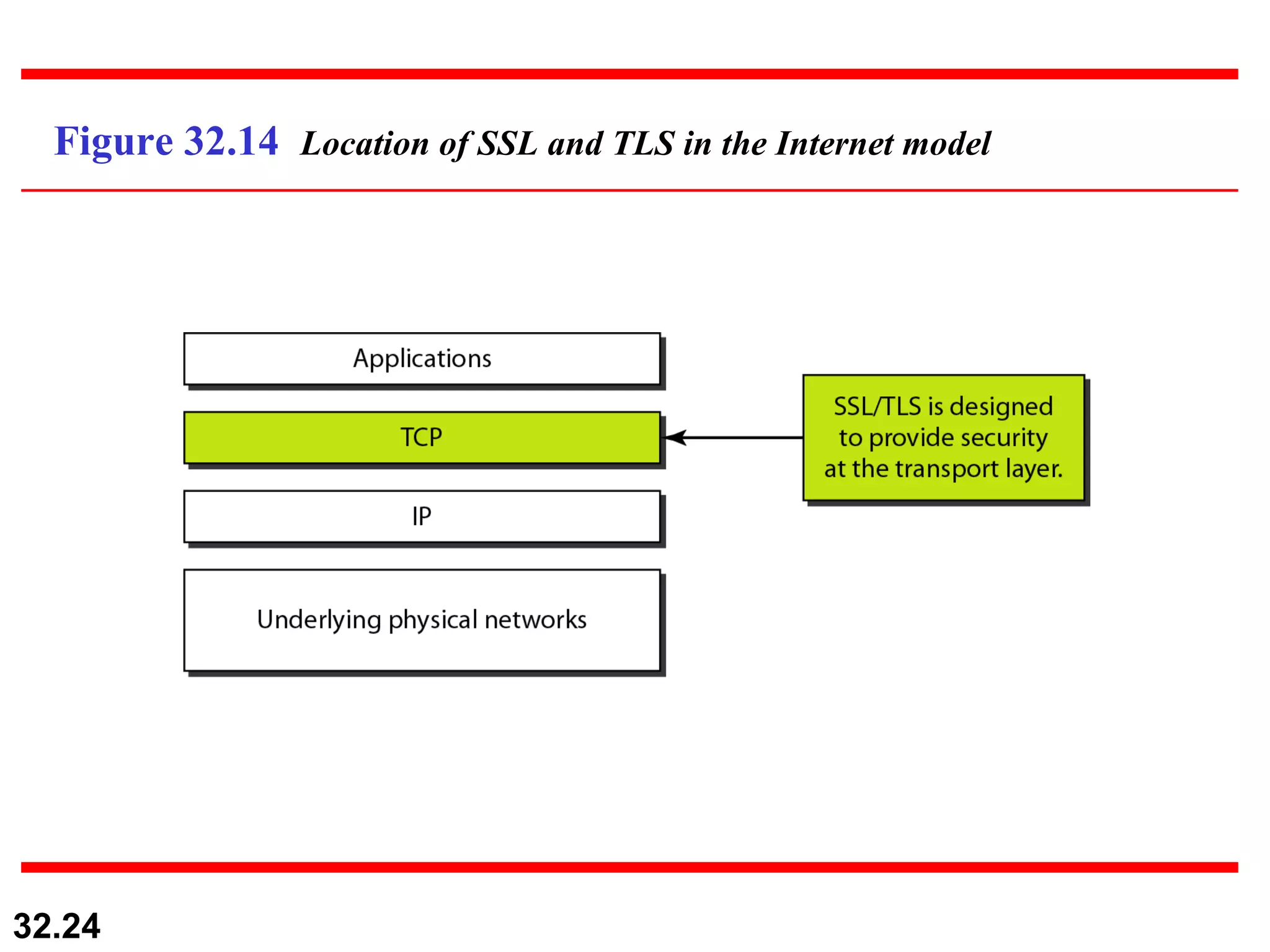
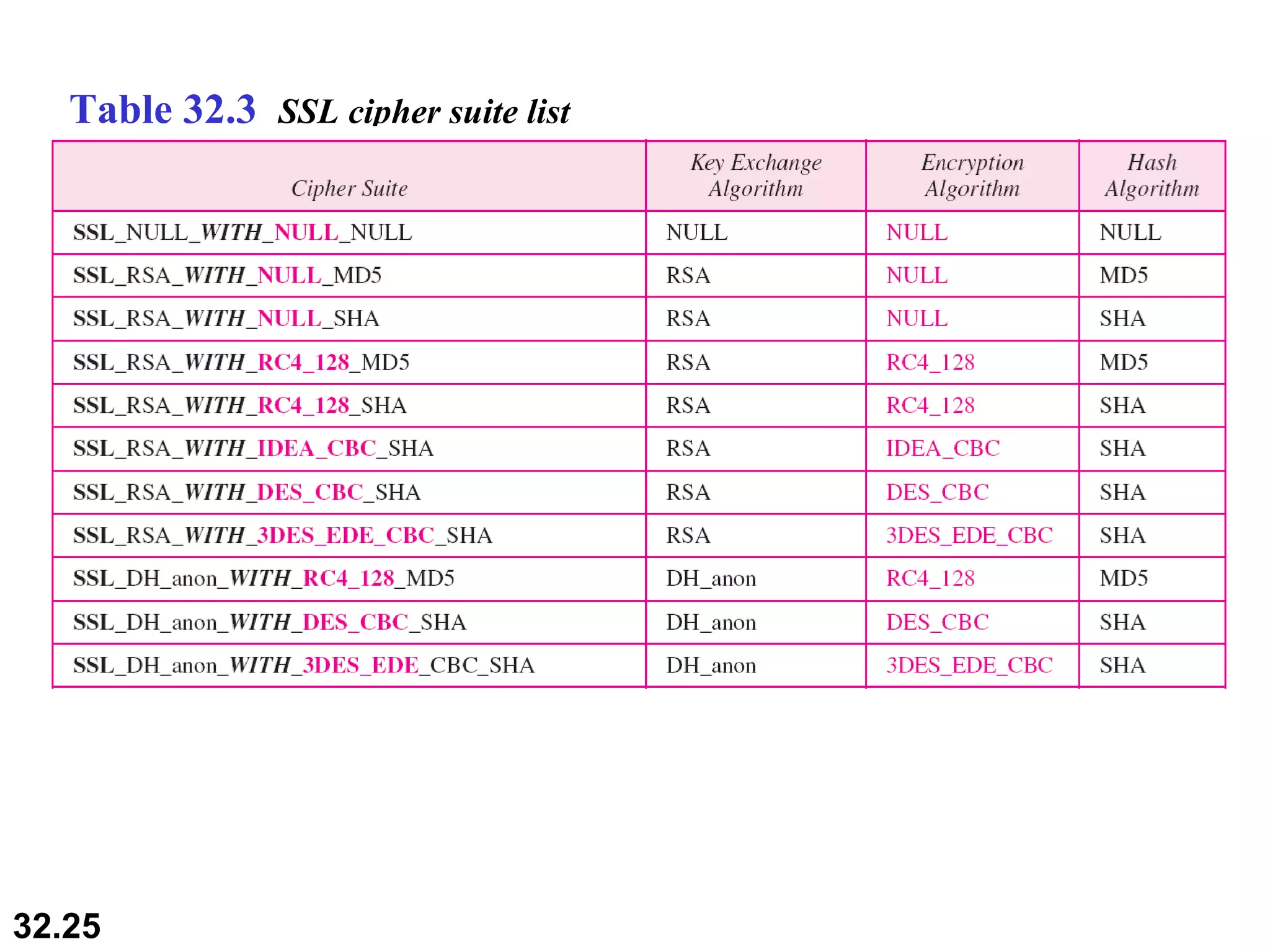
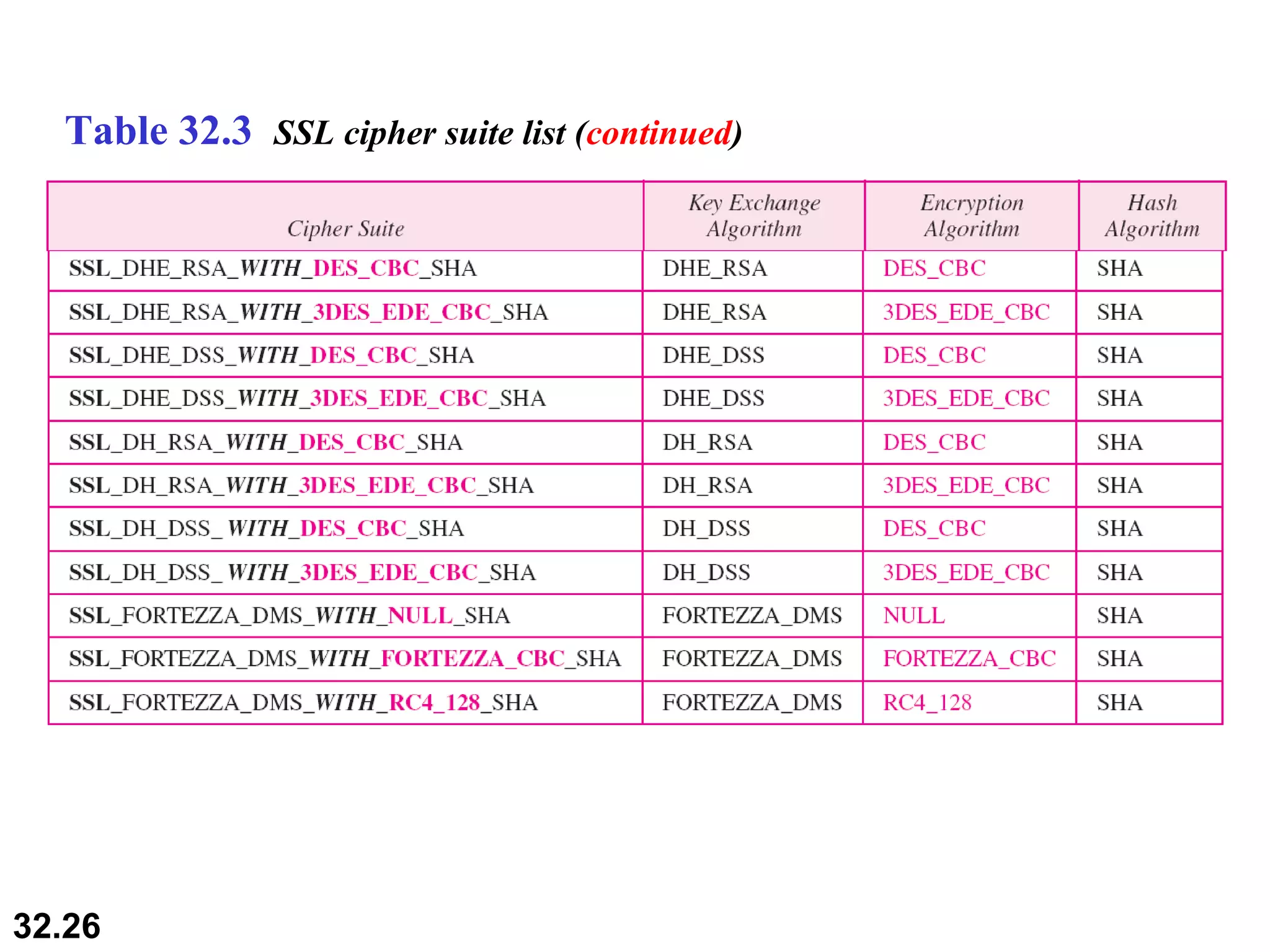
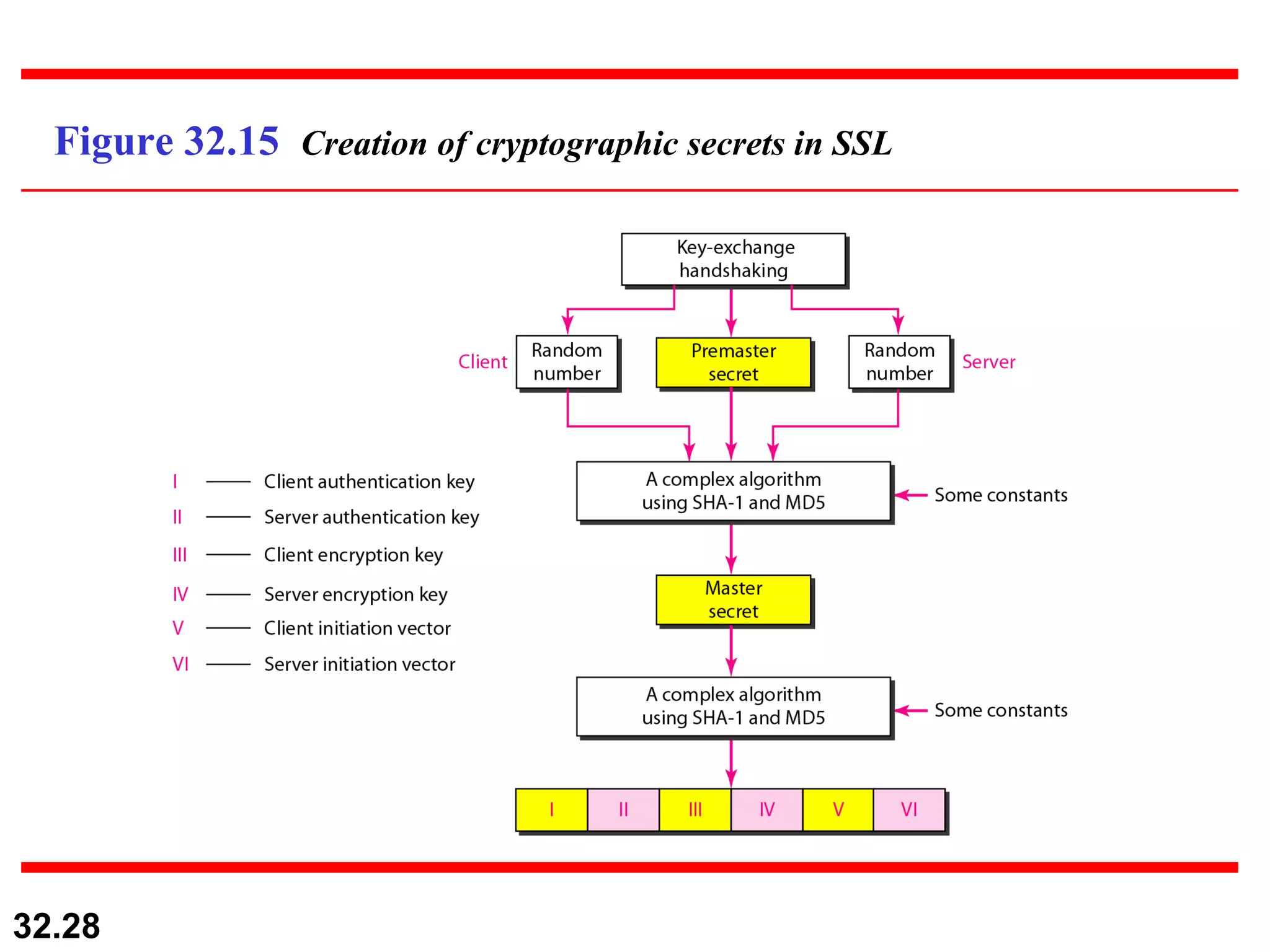
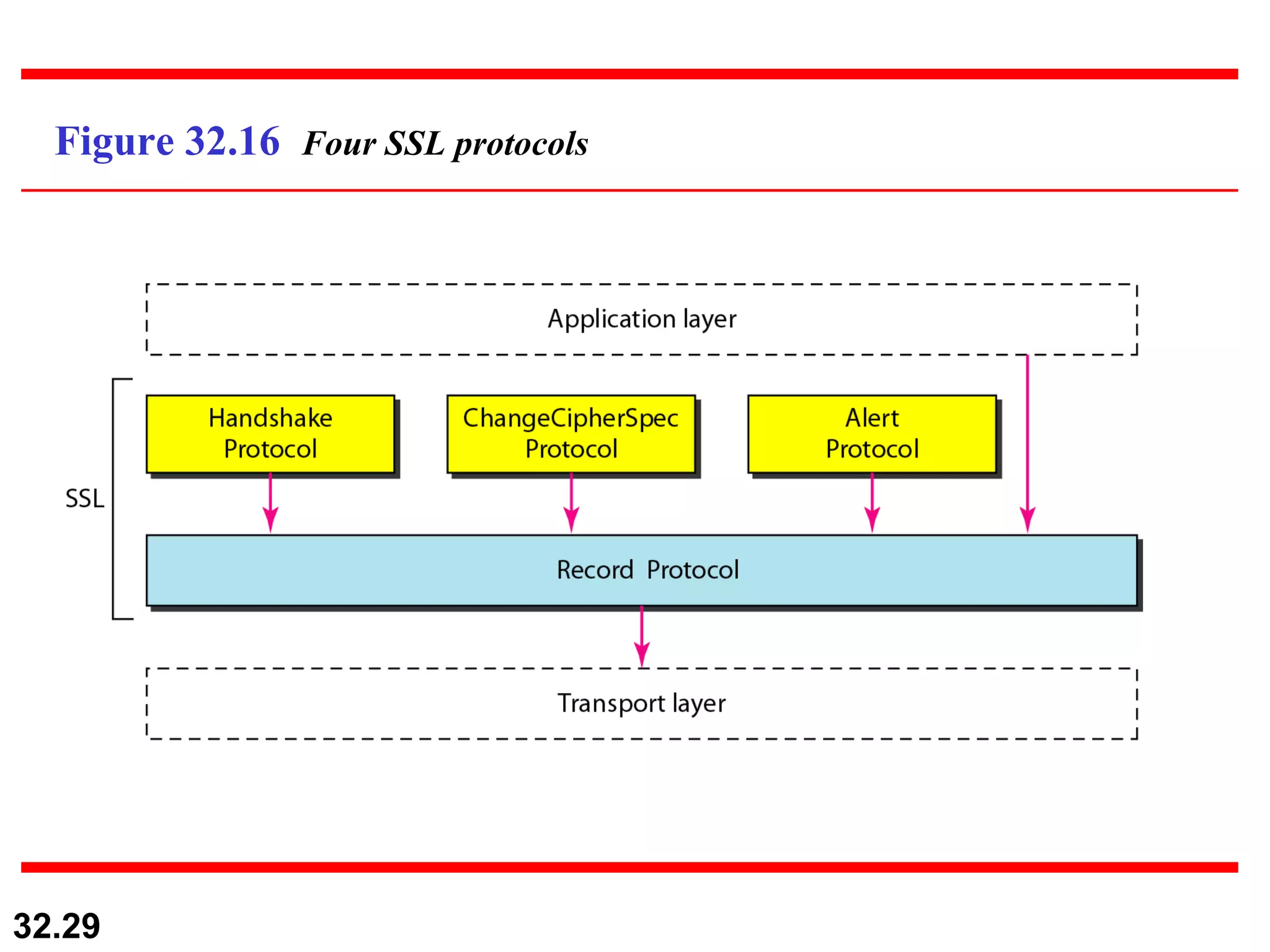
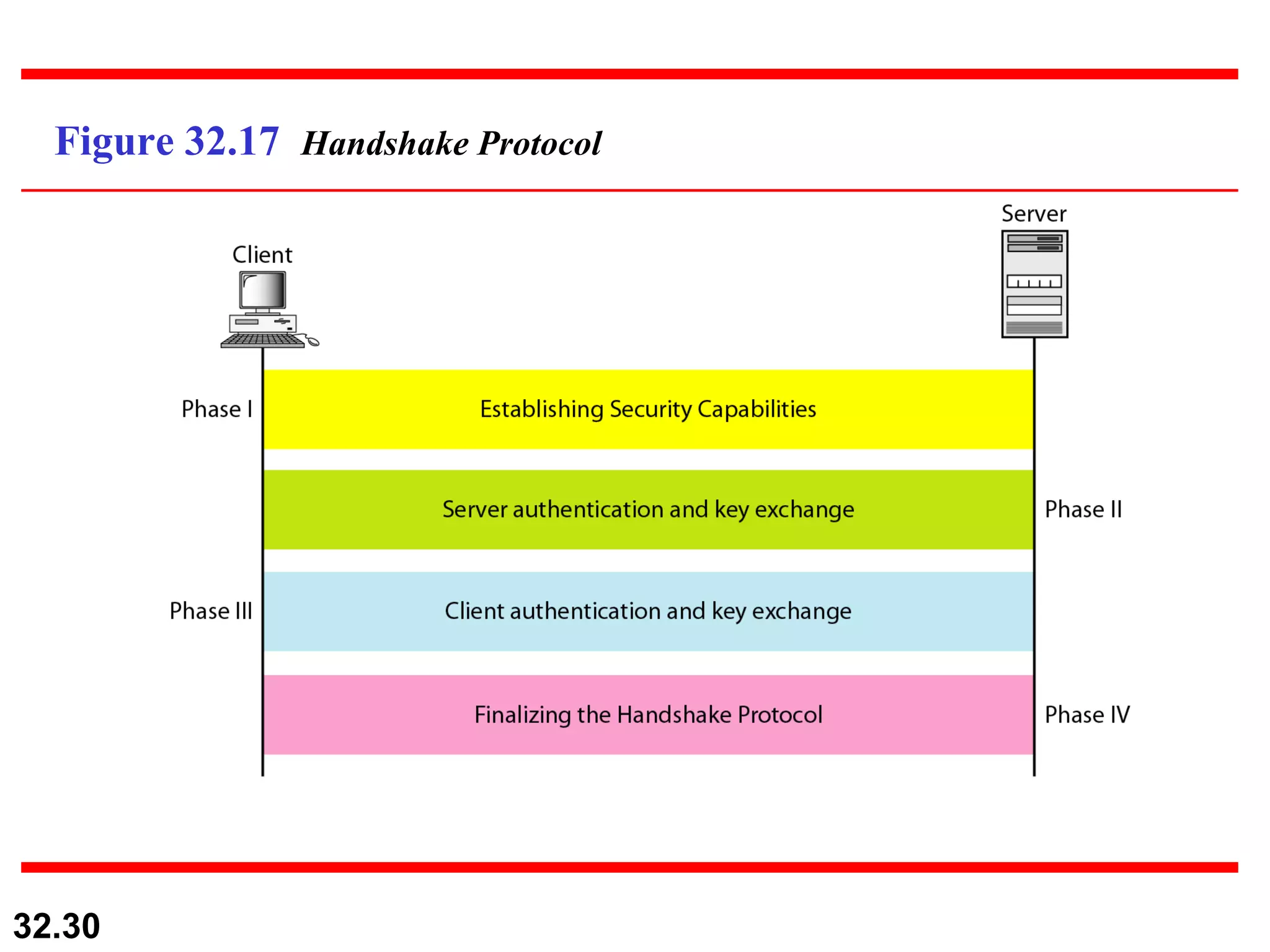
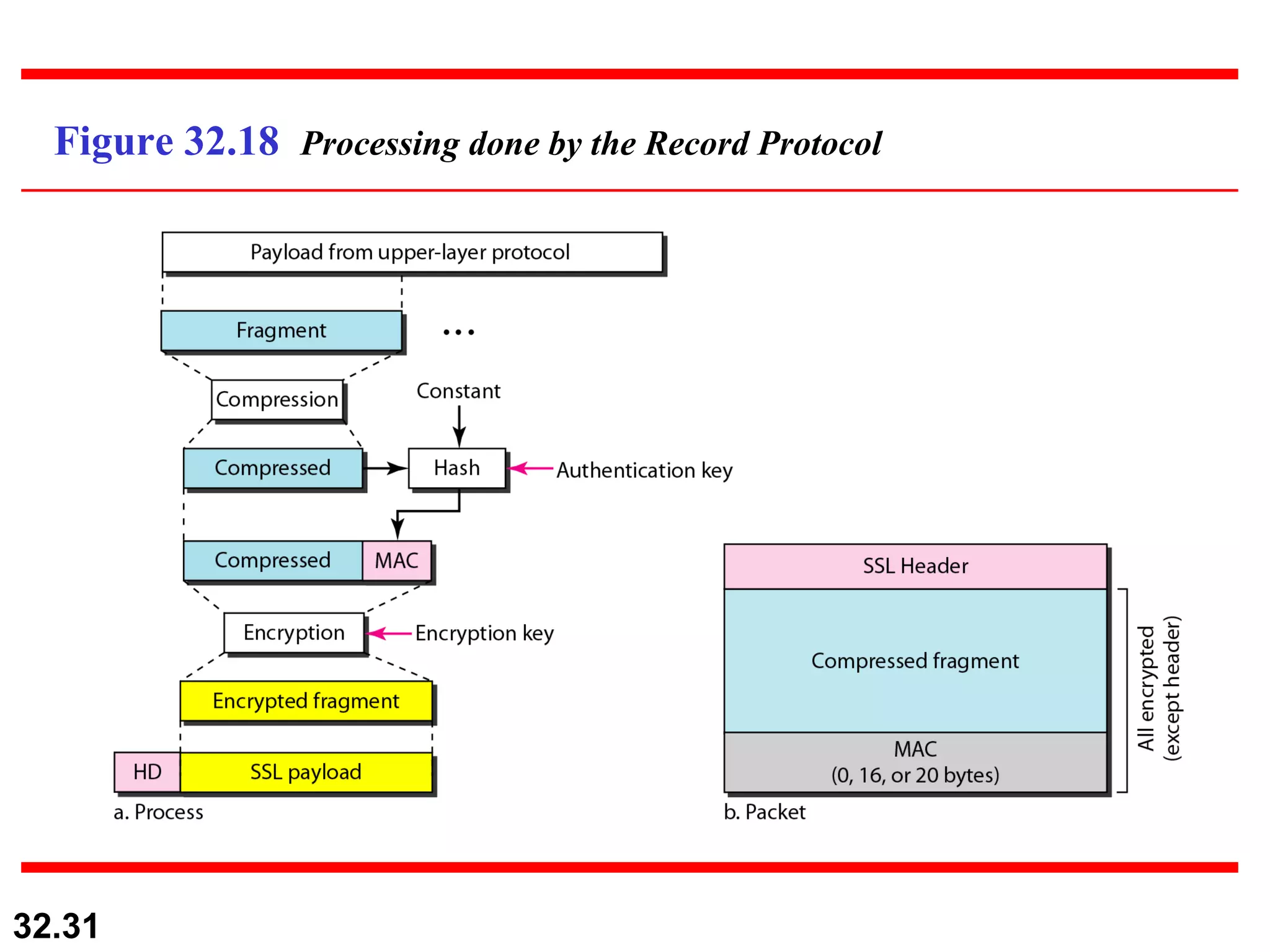
2) SSL/TLS provides security at the transport layer for network communications. It uses cryptography to provide authentication, integrity, and privacy.
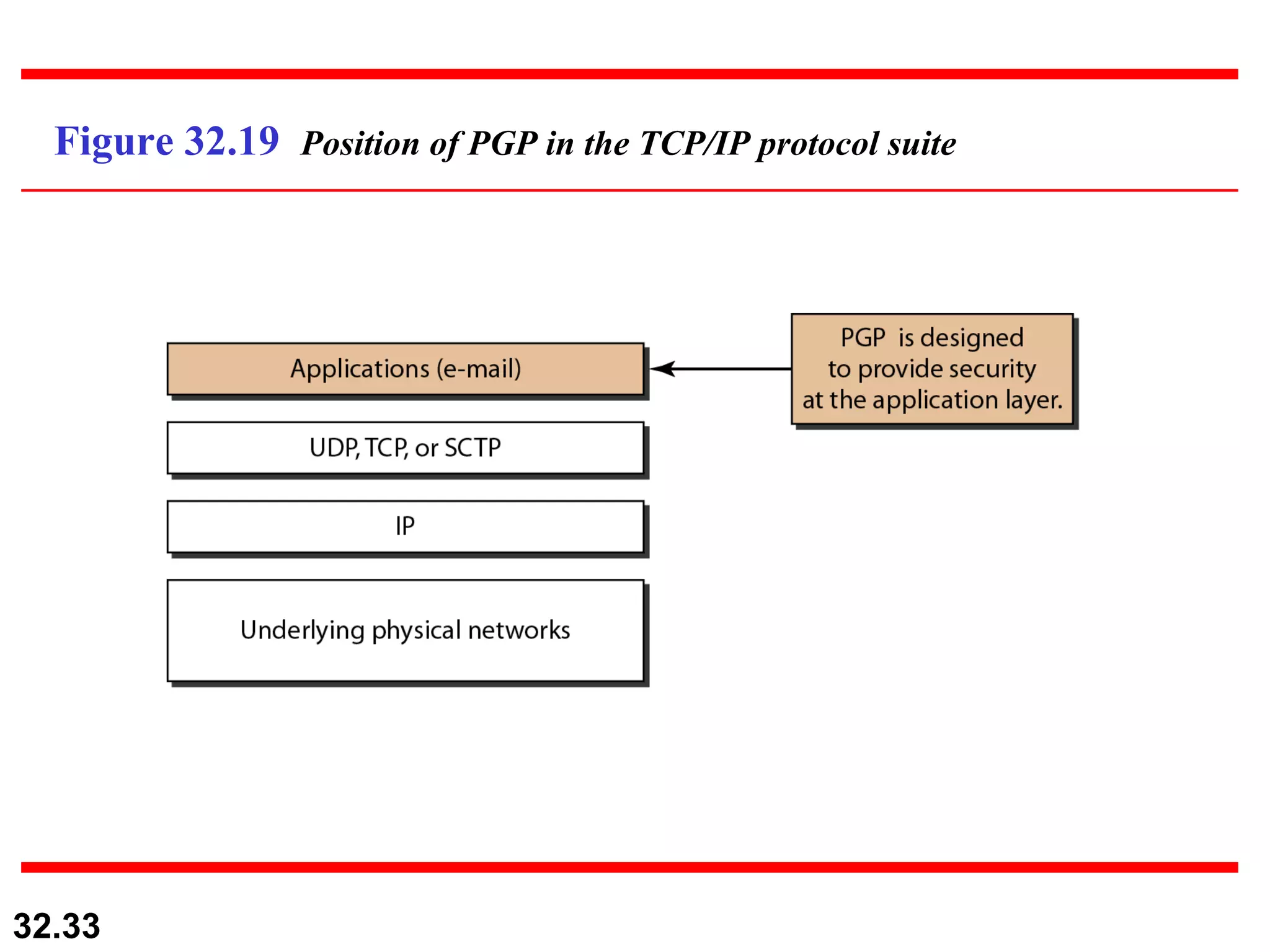
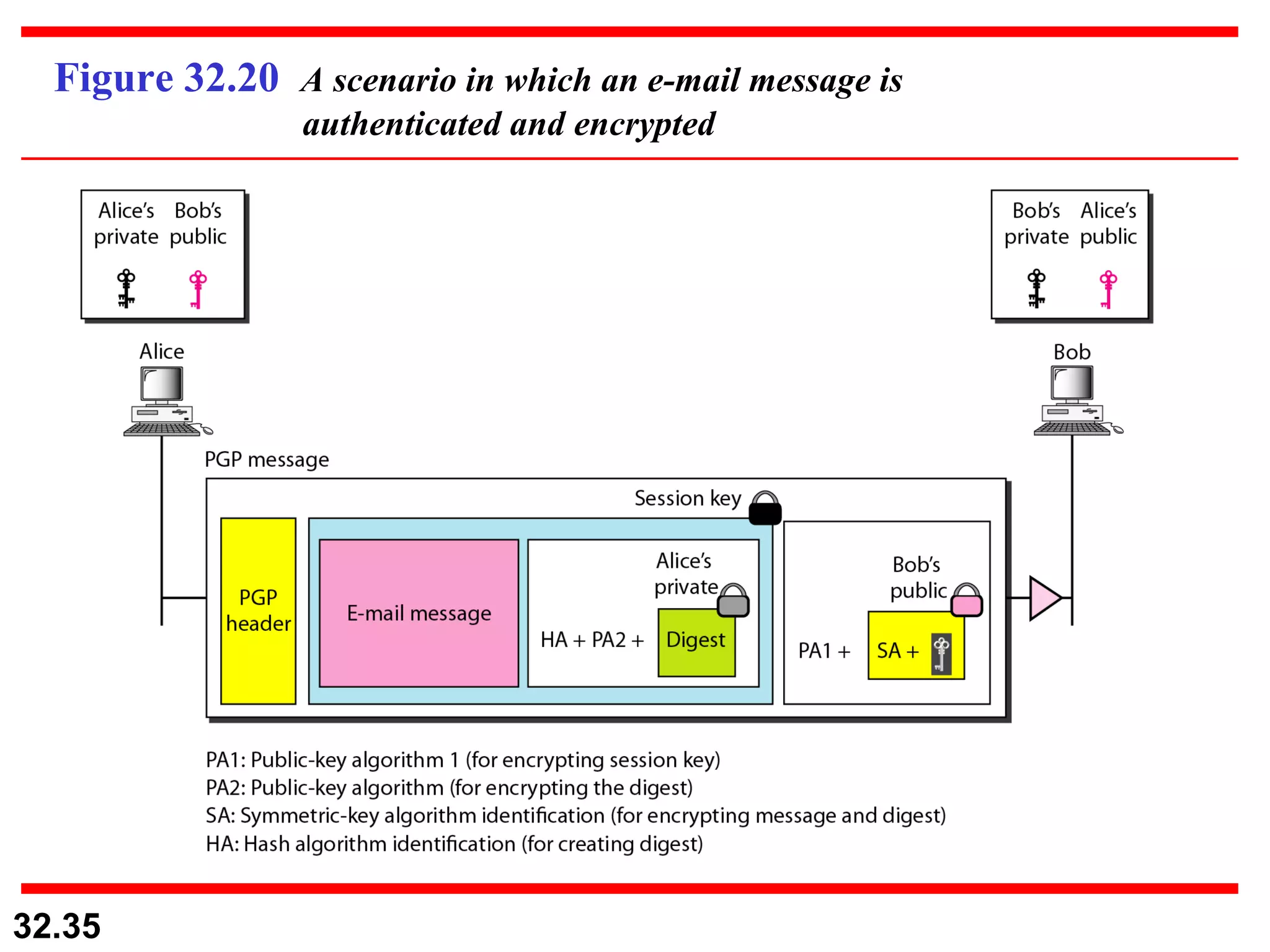
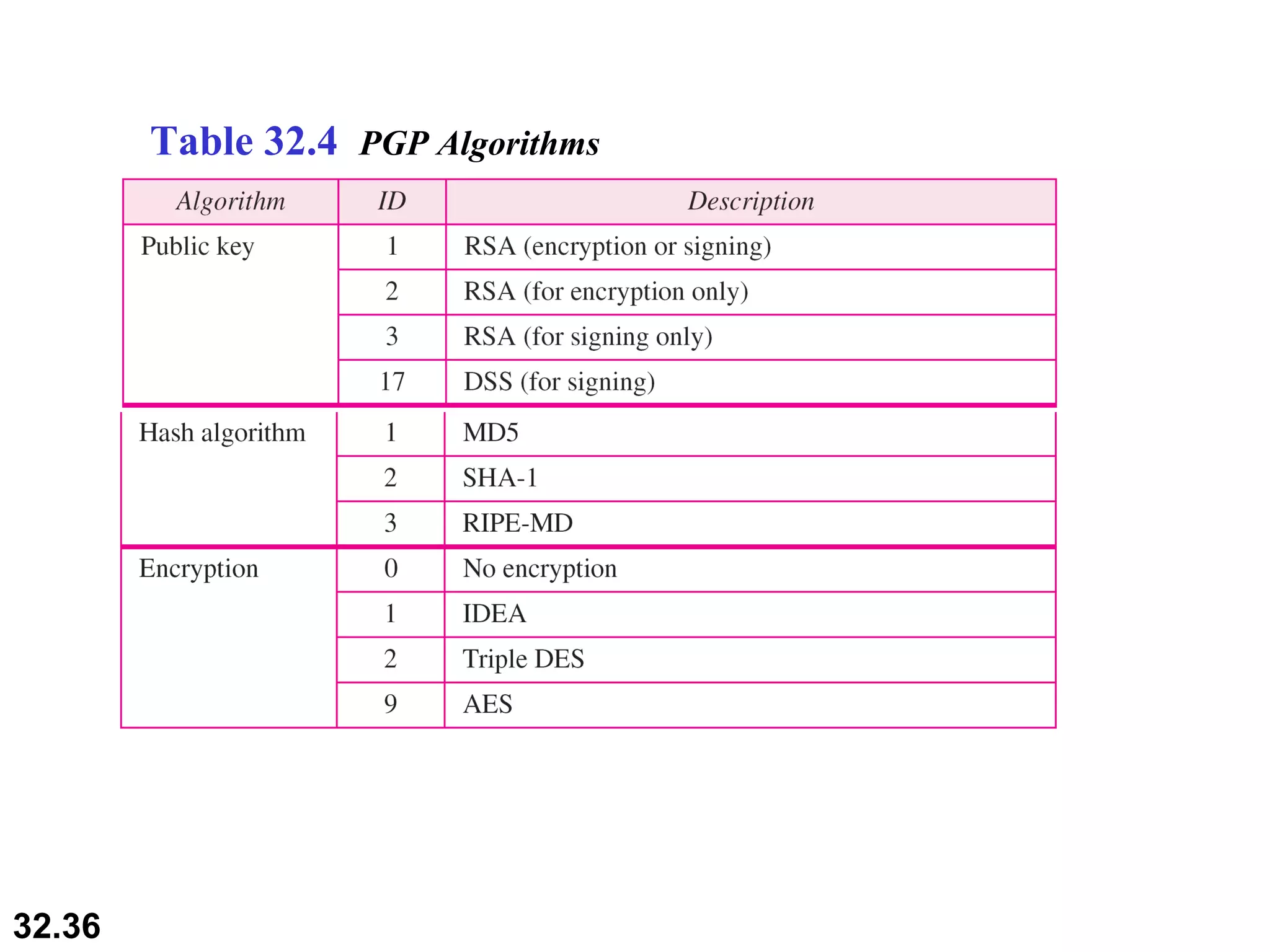
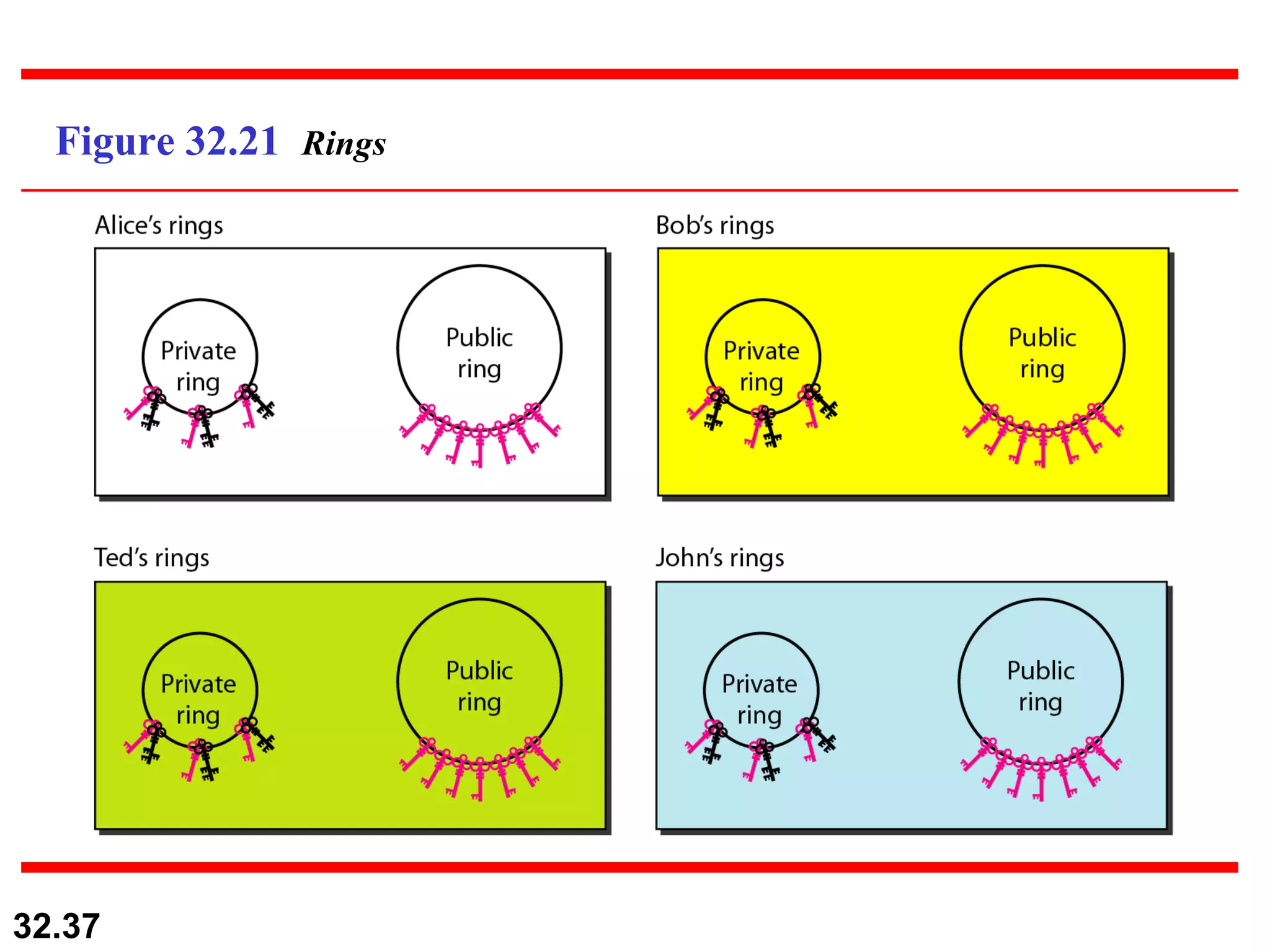
3) PGP provides security at the application layer for encrypting and authenticating emails. It uses public key cryptography and has key rings for managing keys.
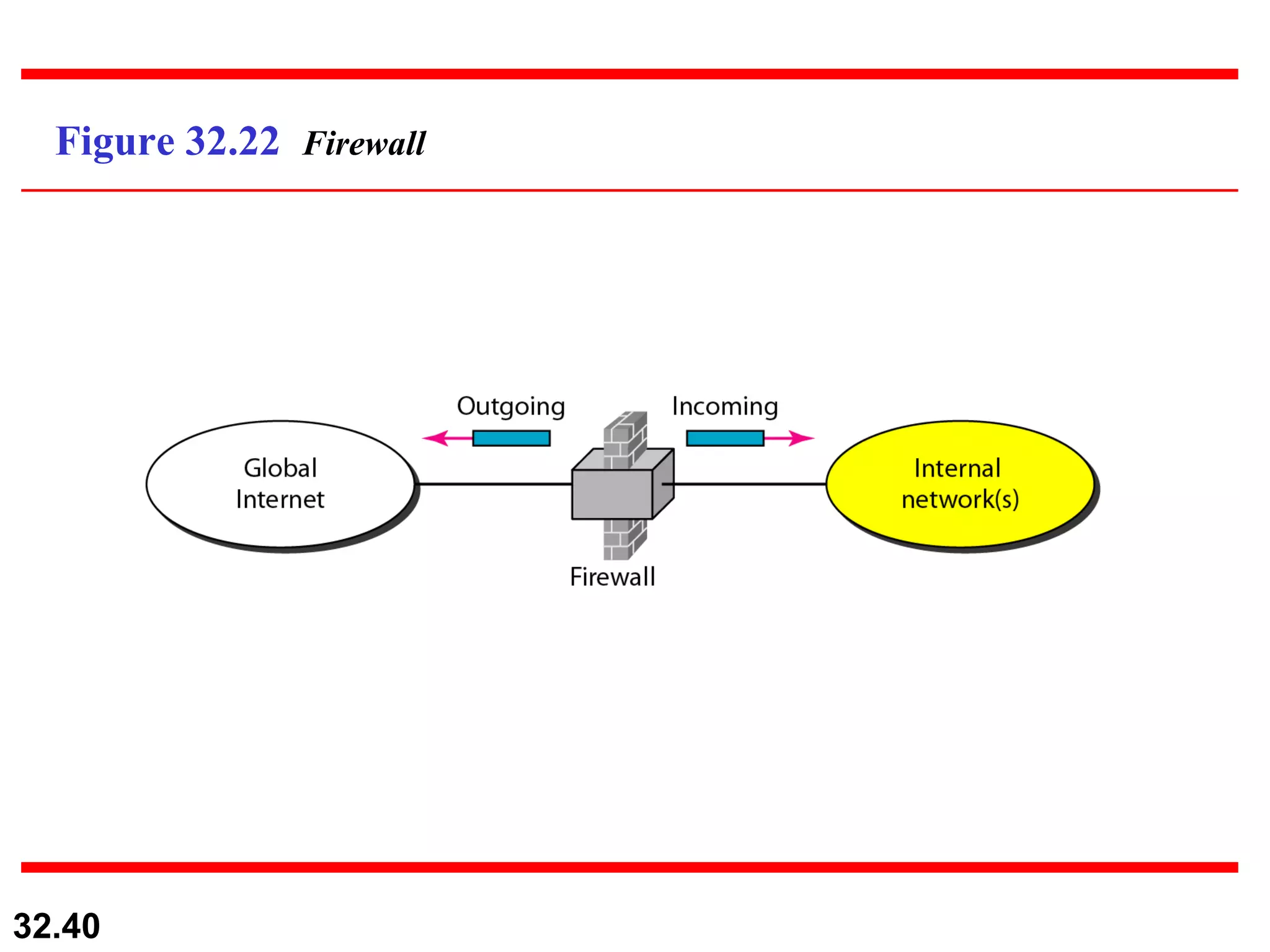
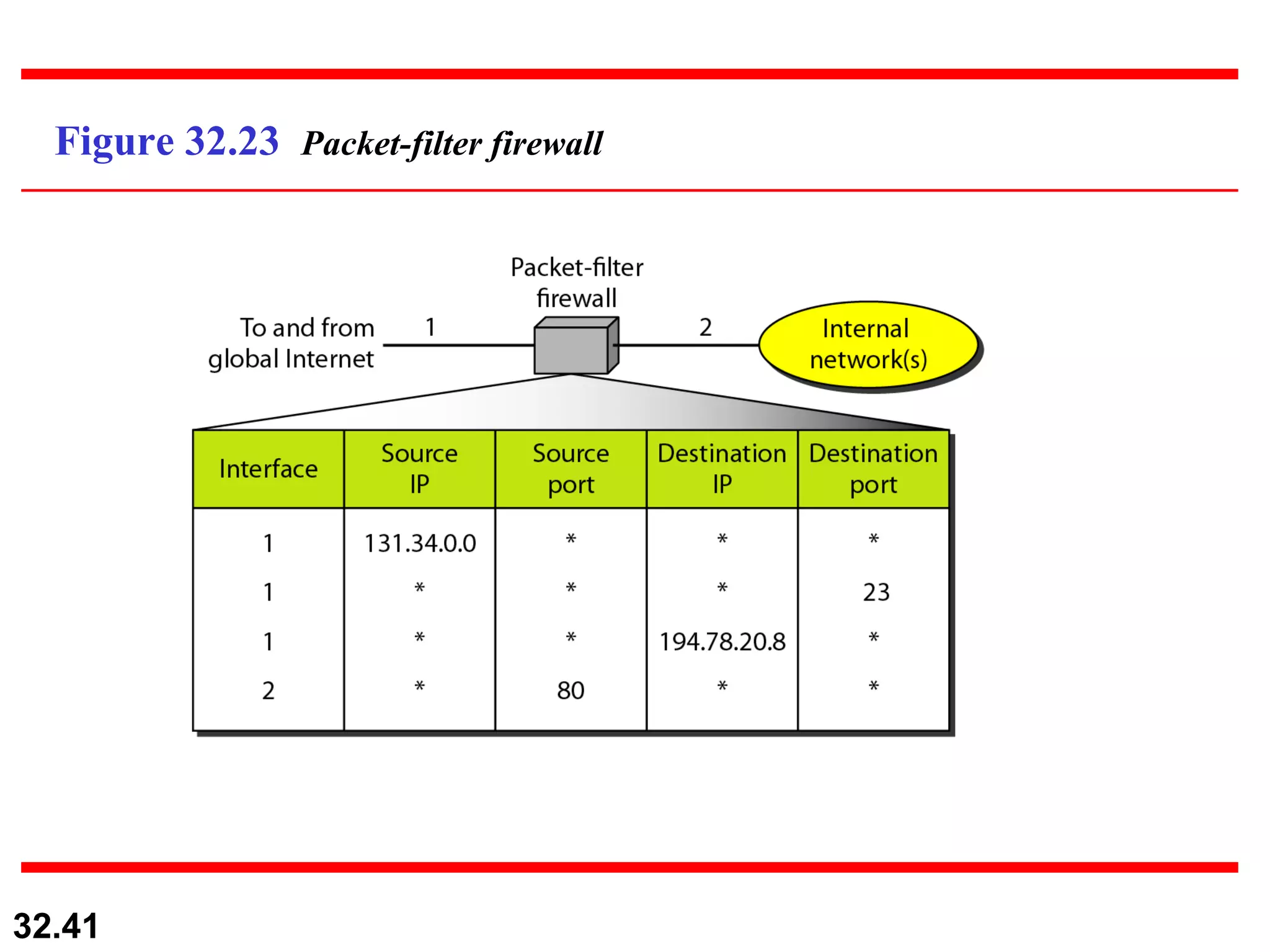
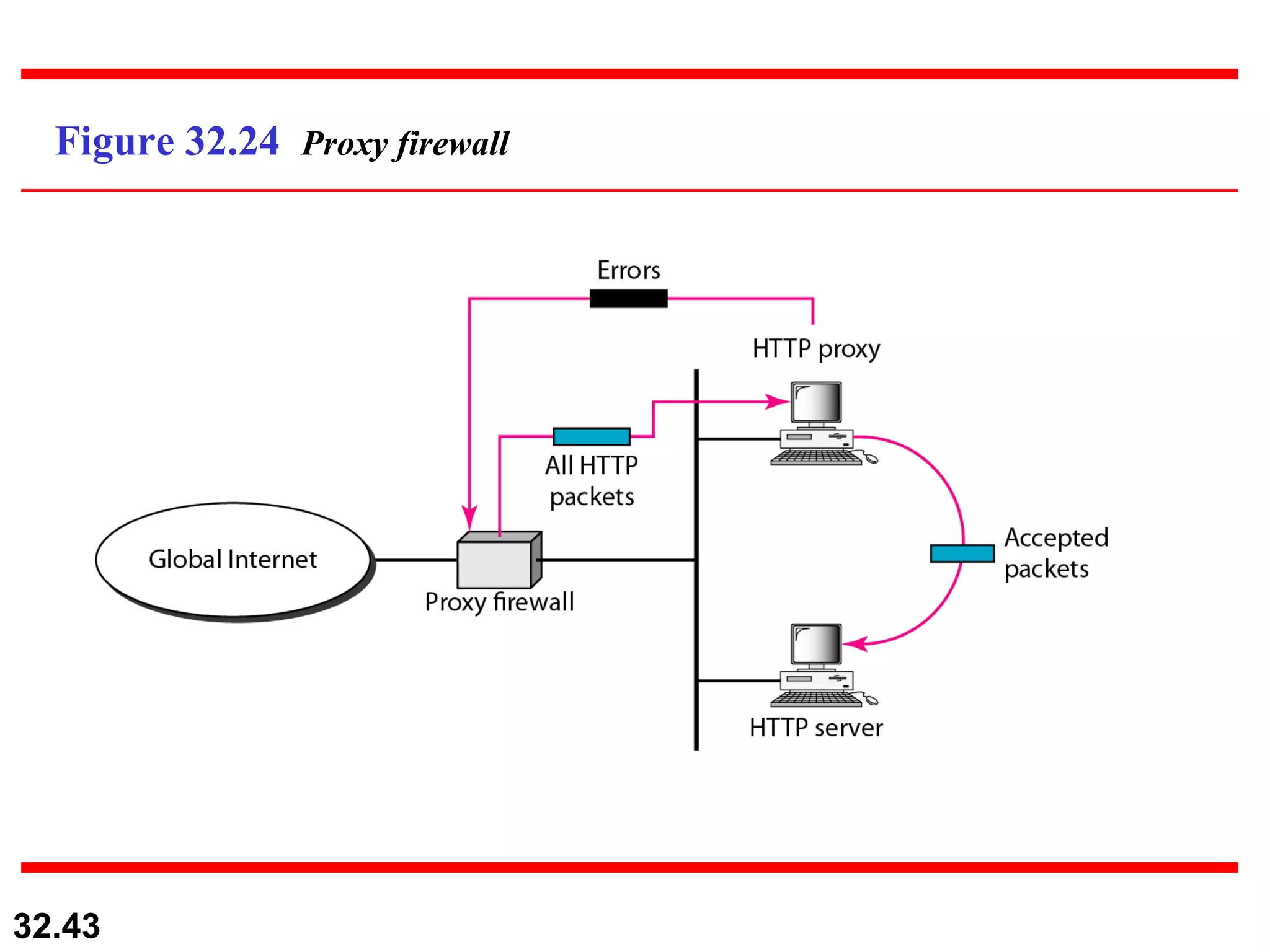
4) Firewalls control access between internal and external networks. Packet-filter firewalls filter at the network/transport layer while proxy firewalls filter at the application layer.