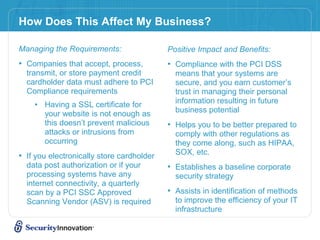
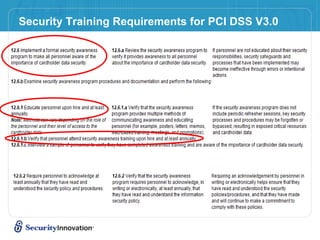
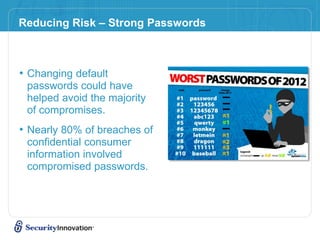
This document discusses navigating PCI compliance and payment security standards. It provides an overview of the PCI Security Standards Council, the development of the PCI Data Security Standard (PCI DSS) and Payment Application Data Security Standard. It outlines requirements for companies that accept credit cards, including adhering to PCI compliance standards, conducting quarterly vulnerability scans, and the consequences of non-compliance such as fines and legal liability. The document stresses the importance of security training to address the human element of data breaches and provides tips to reduce risk such as not storing card data, using validated payment systems, strong passwords, and updating software.