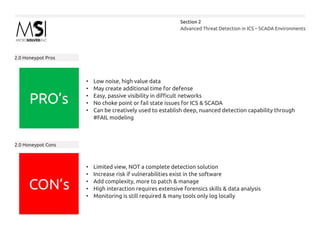
The document discusses the use of honeypots for advanced threat detection in ICS and SCADA environments, detailing different types of honeypots and their functionalities, such as production, research, and high versus low interaction. It also outlines the advantages and challenges of implementing honeypots, emphasizing their role in enhancing visibility, intelligence gathering, and decision-making in cybersecurity. Lastly, it presents a maturity model for honeypot deployment and includes case studies illustrating their effectiveness in identifying unauthorized access and vulnerabilities.