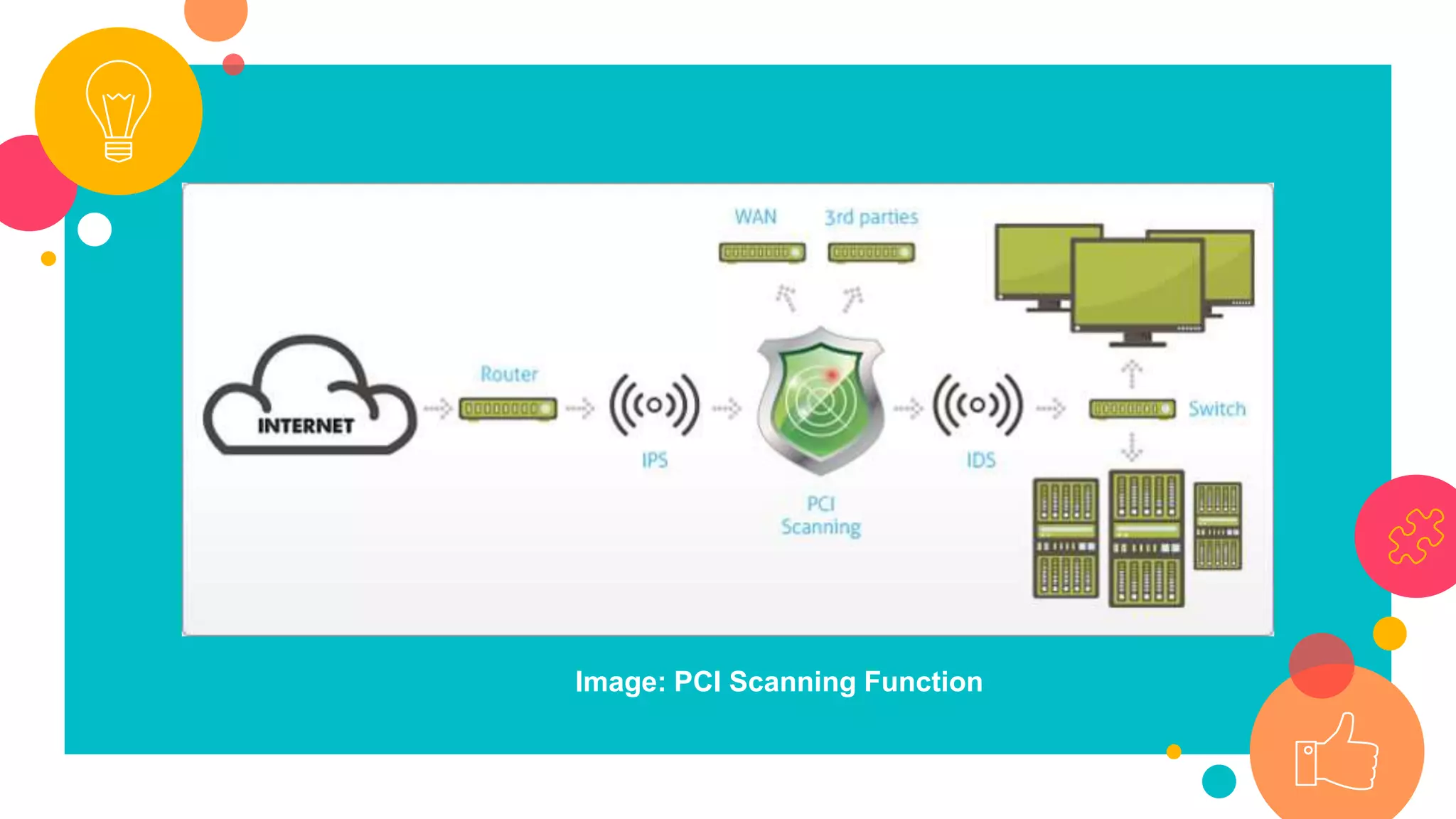
The document discusses the importance of PCI DSS compliance for online businesses, highlighting that compliant organizations are significantly less likely to experience data breaches. The 2017 Verizon Payment Security Report reveals that while compliance rates have improved, over 40% of organizations still fail to meet PCI DSS standards and many lose compliance shortly after assessment. Key requirements include maintaining firewalls, avoiding default credentials, and conducting regular security testing, with significant non-compliance observed in areas like tracking and monitoring access.



![• Speaking of which Rodolphe Simonetti, Verizon’s global managing
director for security consulting said
“There is a clear link between PCI DSS compliance and an
organization’s ability to defend itself against cyberattacks, [While] it is
good to see PCI compliance increasing, the fact remains that over 40
percent of the global organizations we assessed – large and small –
are still not meeting PCI DSS compliance standards. Of those that pass
validation, nearly half fall out of compliance within a year — and many
much sooner.”](https://image.slidesharecdn.com/isyourbusinesspcidsscompliantyourediggingyourowngraveifnot-171013120652/75/Is-your-business-PCI-DSS-compliant-You-re-digging-your-own-grave-if-not-16-2048.jpg)