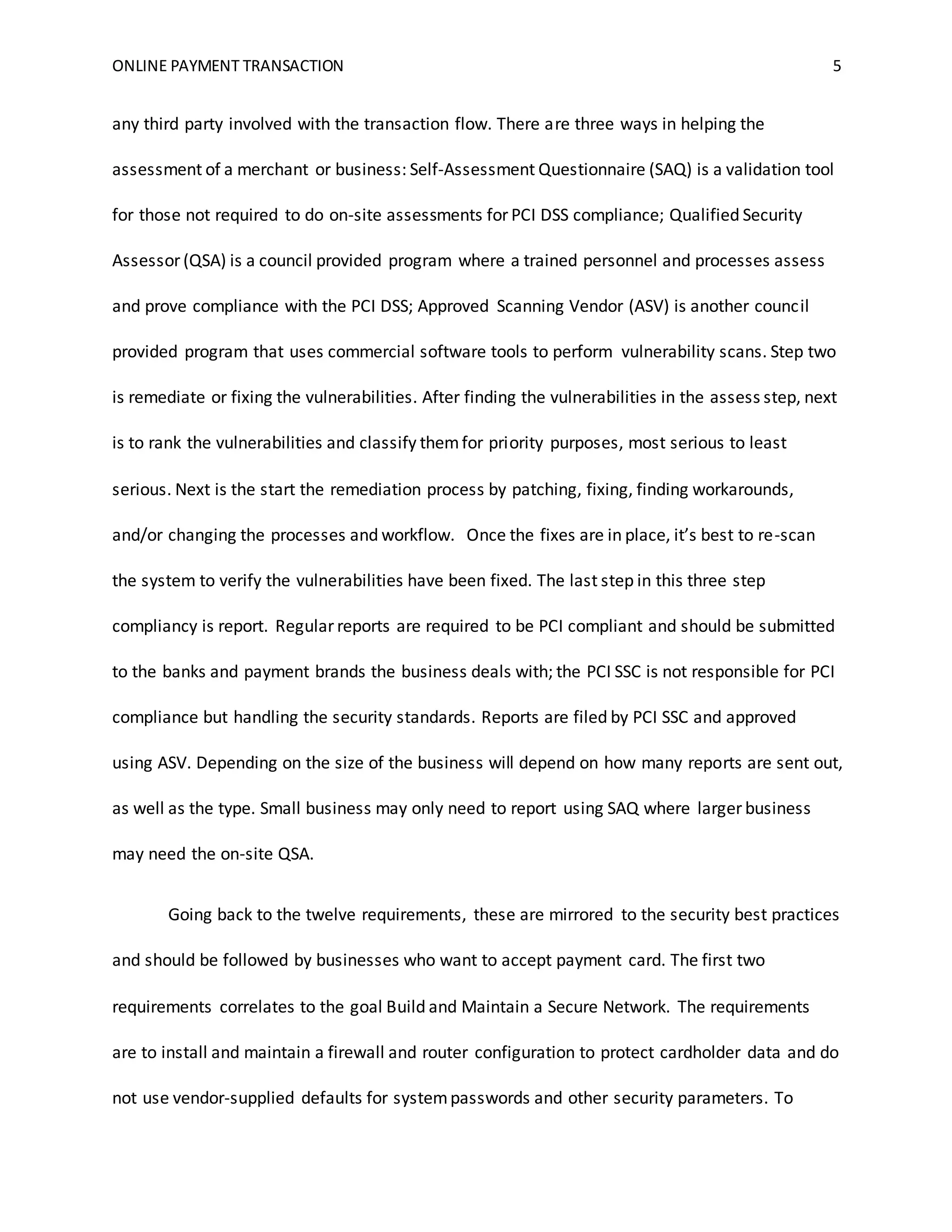
This document discusses online payment transactions and the PCI DSS security standards. It explains that the PCI DSS was established by the major credit card companies to protect customer payment information. The PCI DSS has 12 requirements across 3 key goals - building a secure network, protecting stored data, and maintaining security. Merchants must be compliant with PCI DSS to accept credit cards. Compliance involves regularly assessing systems for vulnerabilities, remediating any issues found, and reporting on compliance efforts.