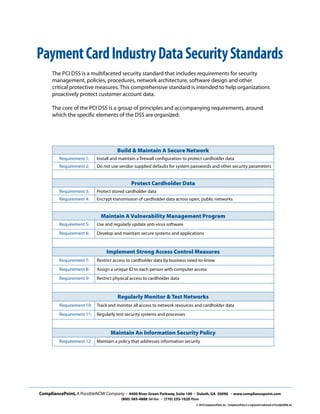
The document discusses the Payment Card Industry Data Security Standard (PCI DSS), which establishes security standards for businesses that accept payment cards. It aims to protect cardholder data and ensure privacy. The PCI DSS includes 12 requirements around data security best practices that cover managing, monitoring and securing cardholder information. It also introduces CompliancePoint, a company that assists other businesses in achieving and maintaining PCI compliance through services like security assessments, policy development and IT consulting.