Embed presentation
Download as PDF, PPTX
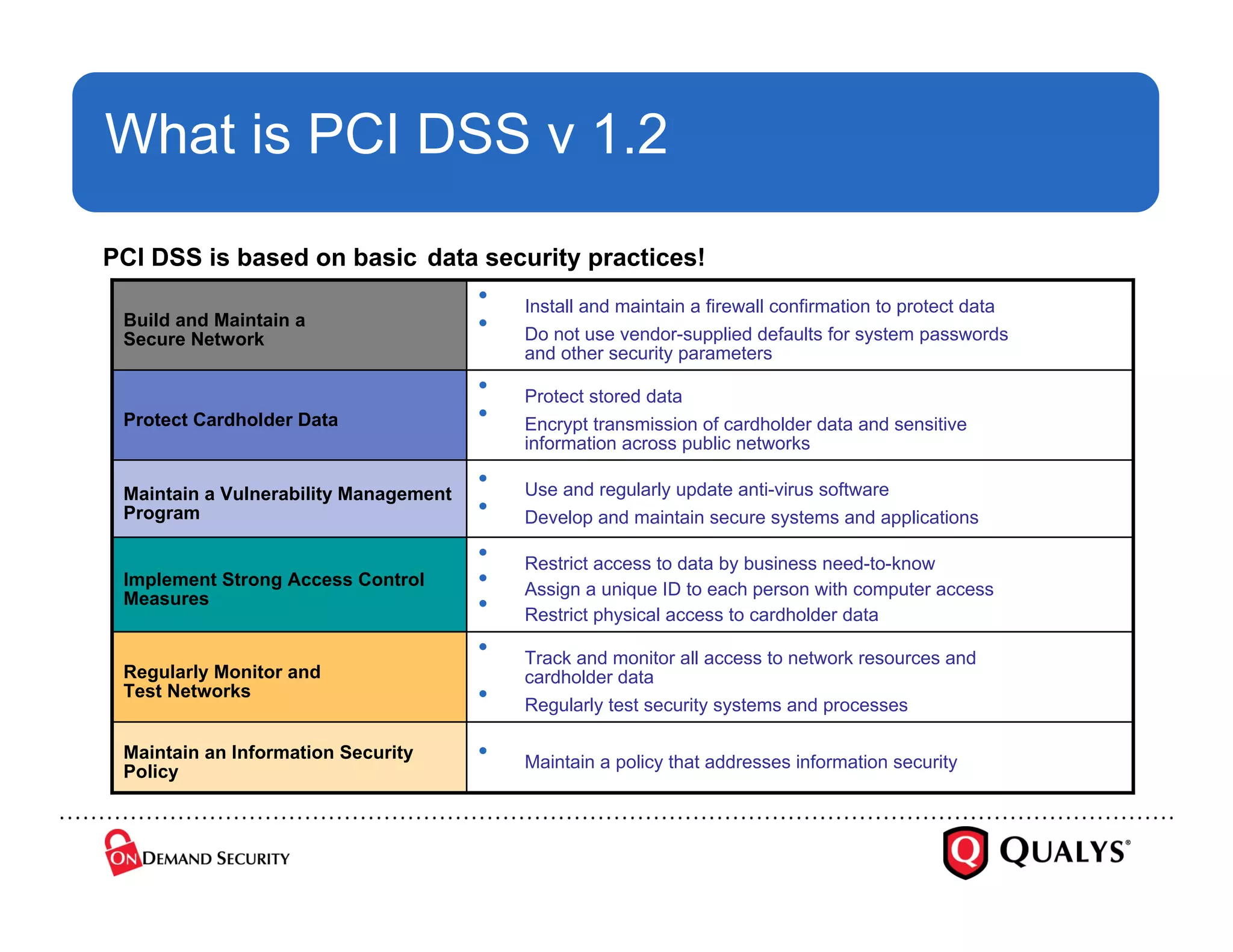

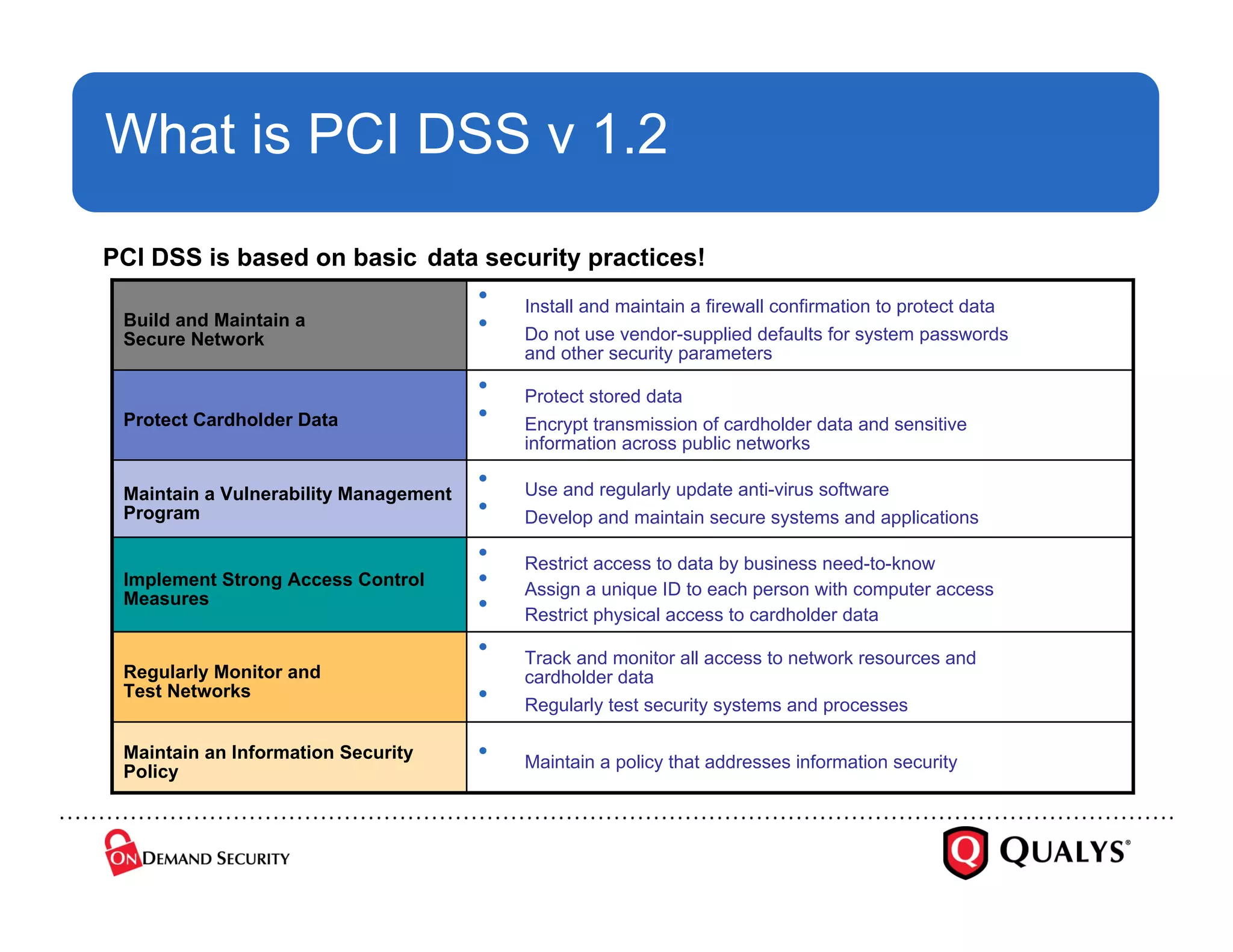
The document addresses common myths and misconceptions about PCI DSS, emphasizing that compliance applies to all entities handling credit card data, regardless of size or complexity. It outlines essential PCI requirements and warns against complacency, stressing that compliance is not just a one-time effort but requires ongoing commitment to security practices. Key implementation mistakes are highlighted, with a call for a shift from a compliance mindset to a risk management approach.