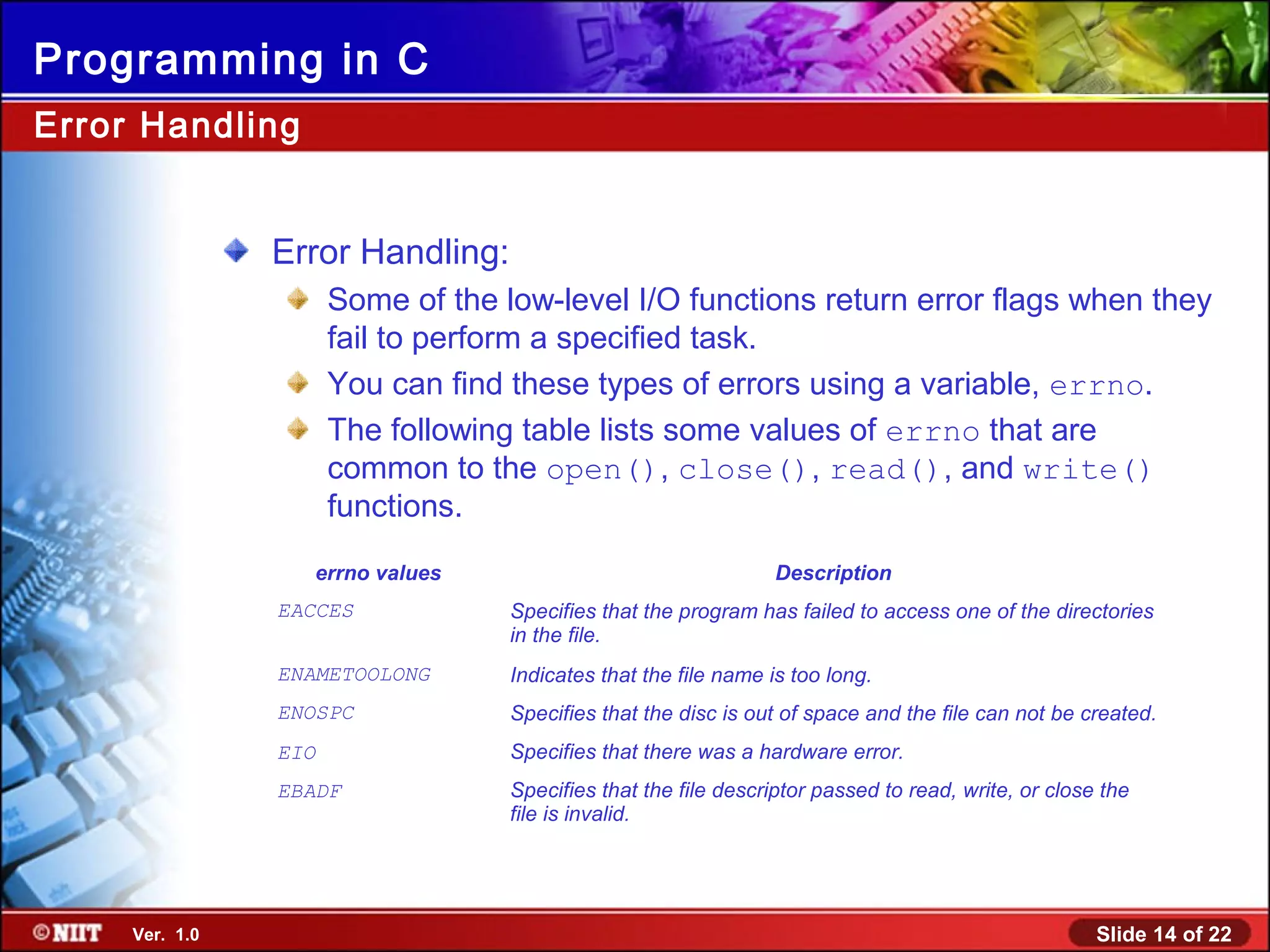
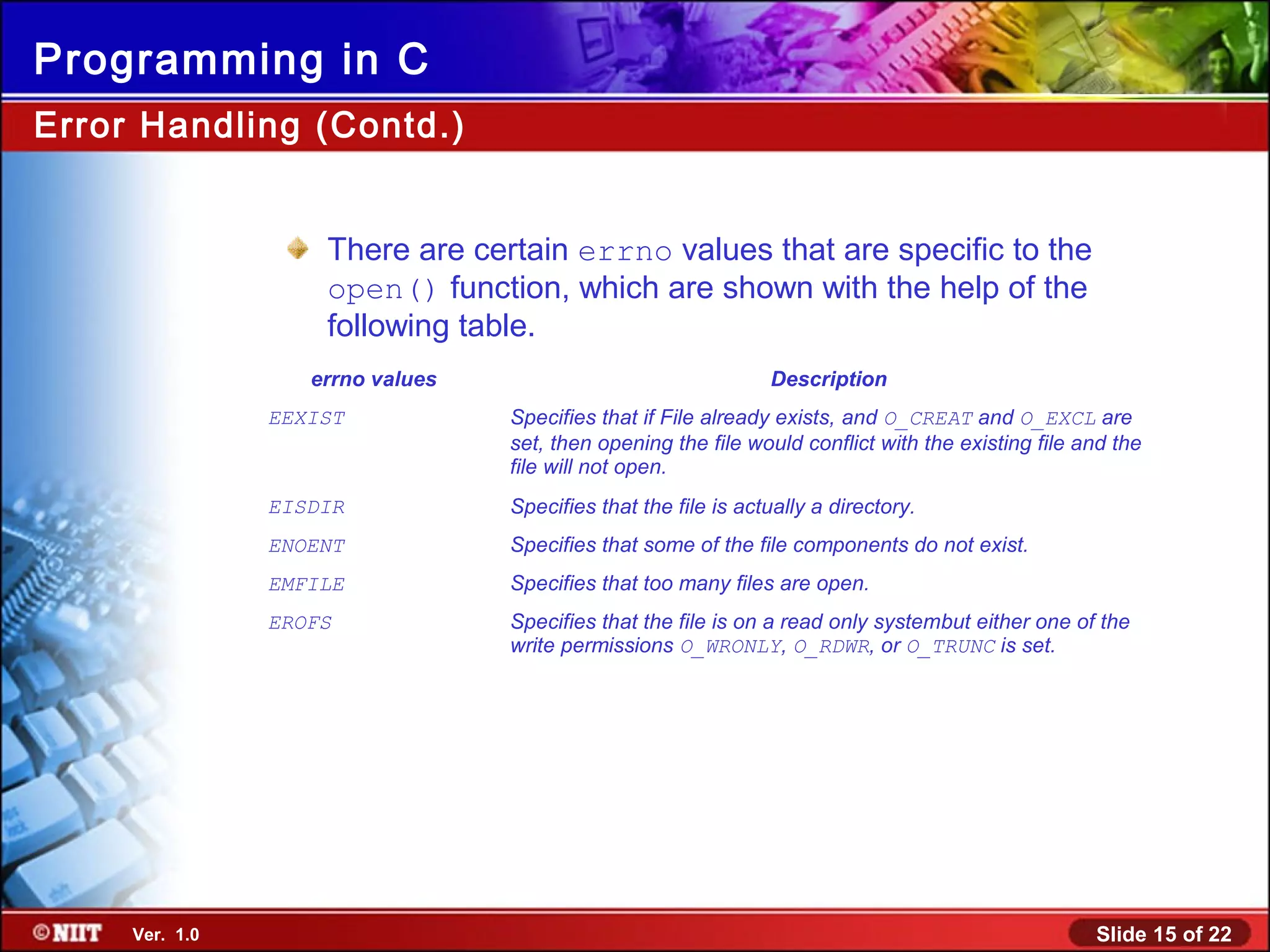
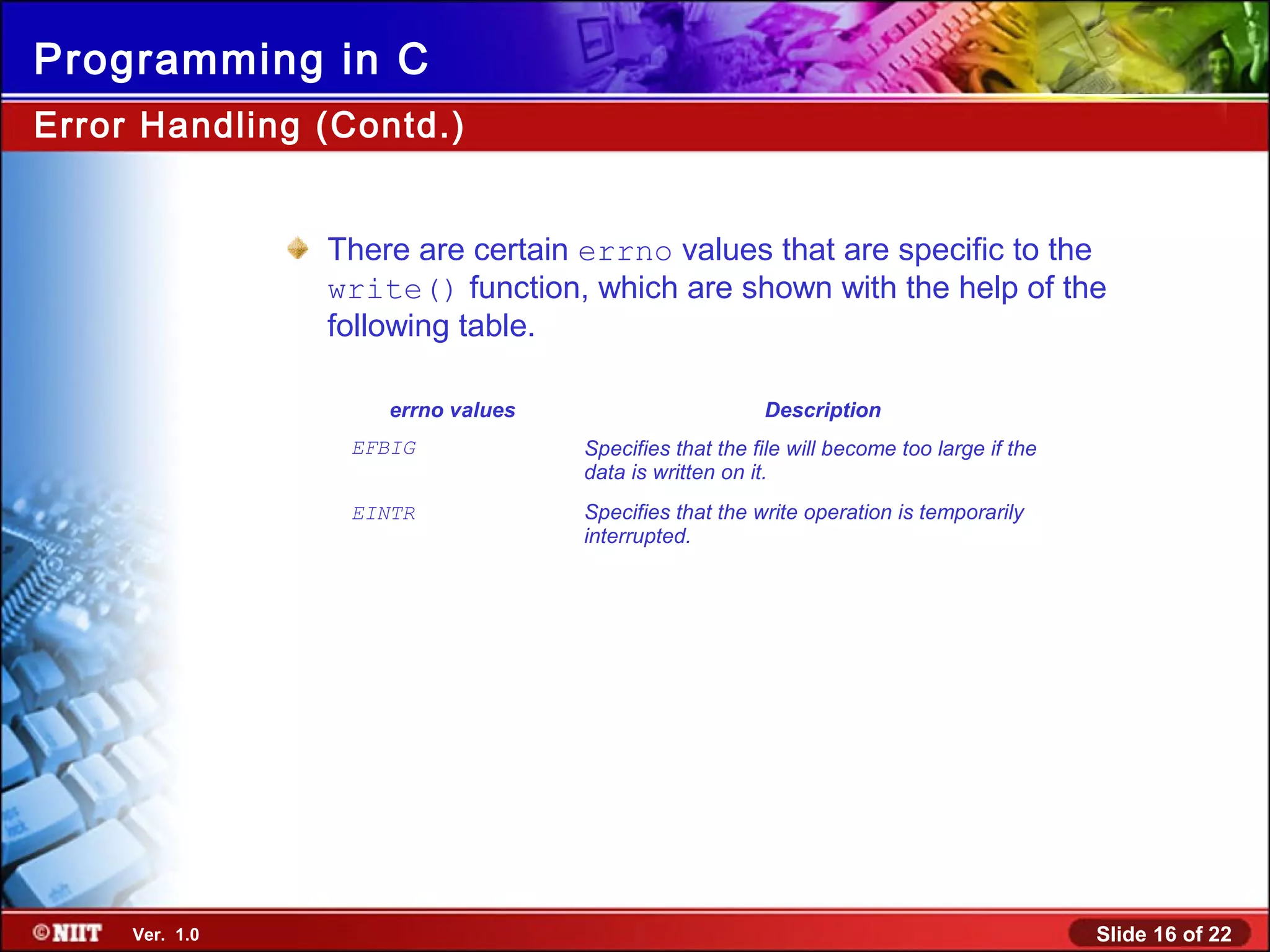
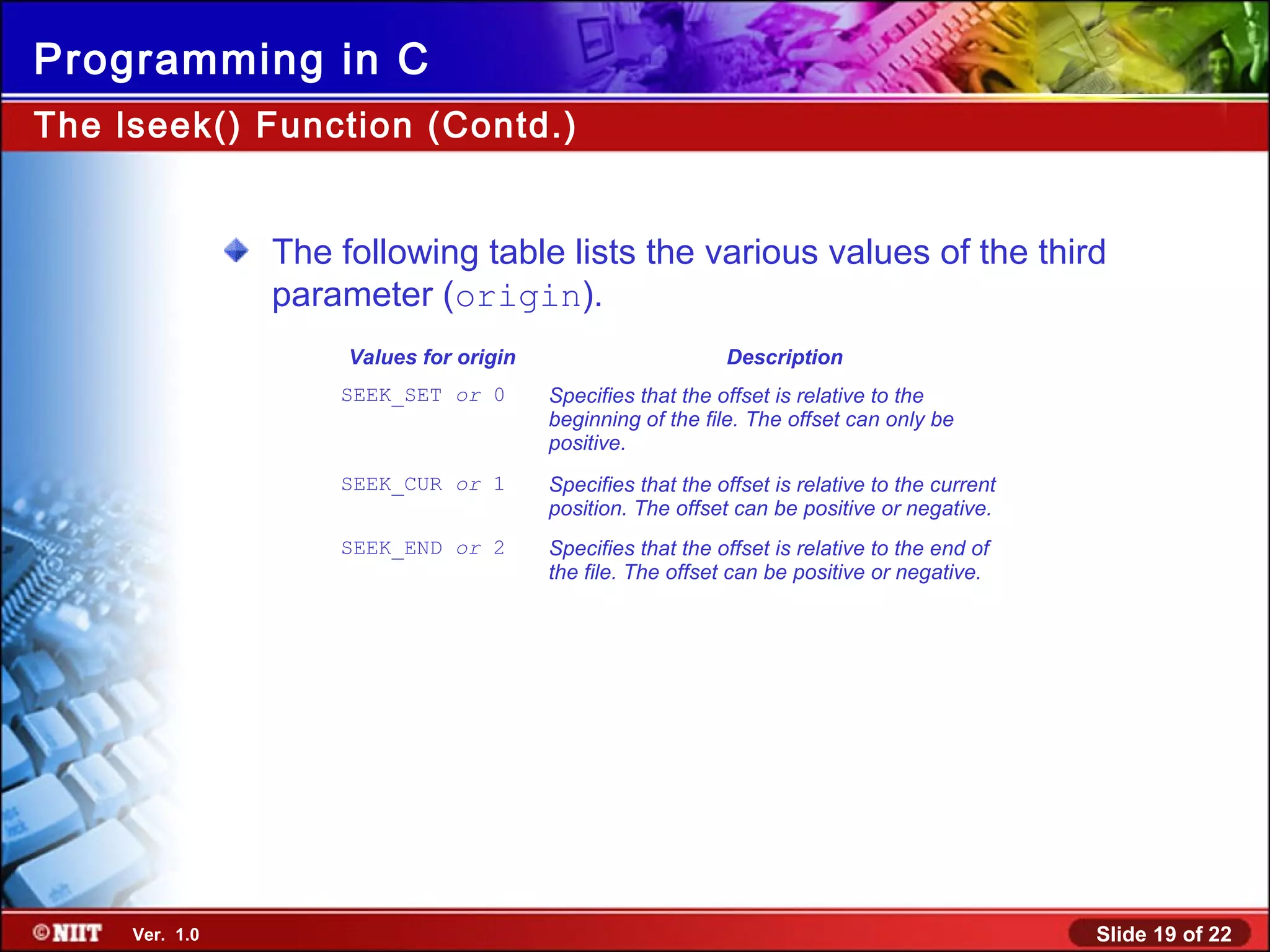
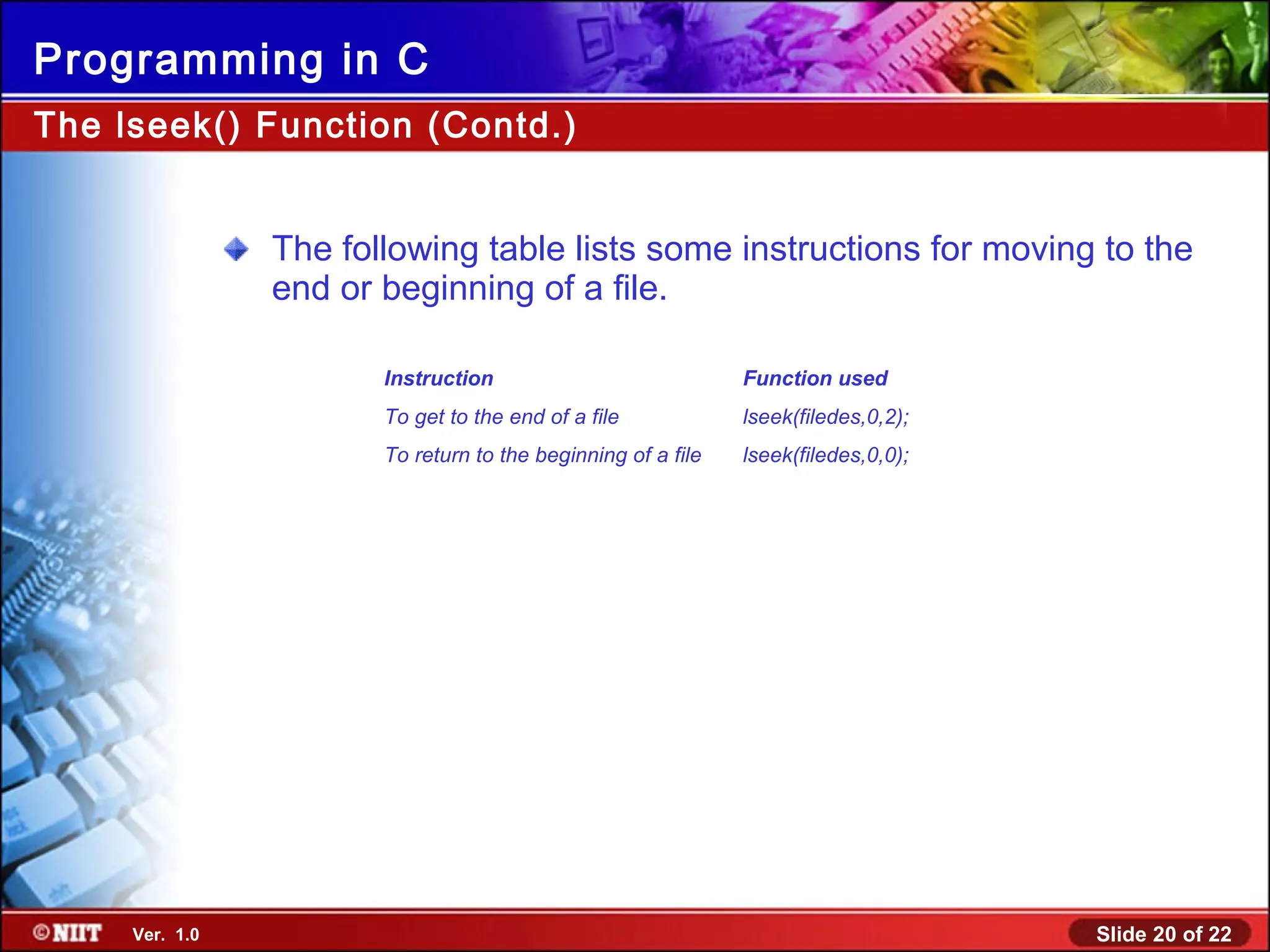
This document discusses low-level input/output in C programming. It explains that low-level I/O provides direct access to files and devices using functions like open(), close(), read(), write(), and lseek(). These functions take a file descriptor as a parameter and allow accessing files sequentially or randomly. The document also covers error handling using errno values and differentiates between high-level and low-level I/O.