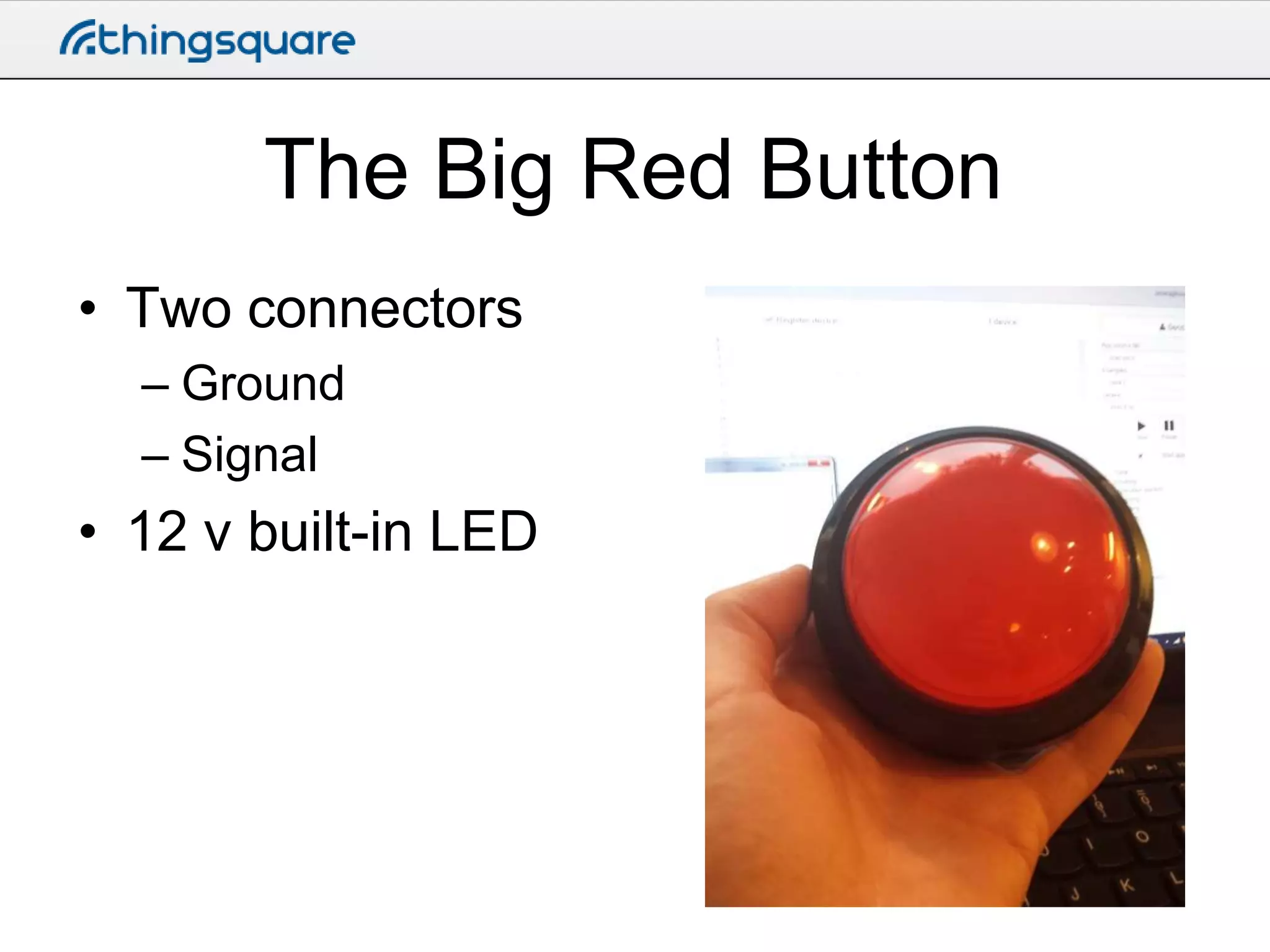
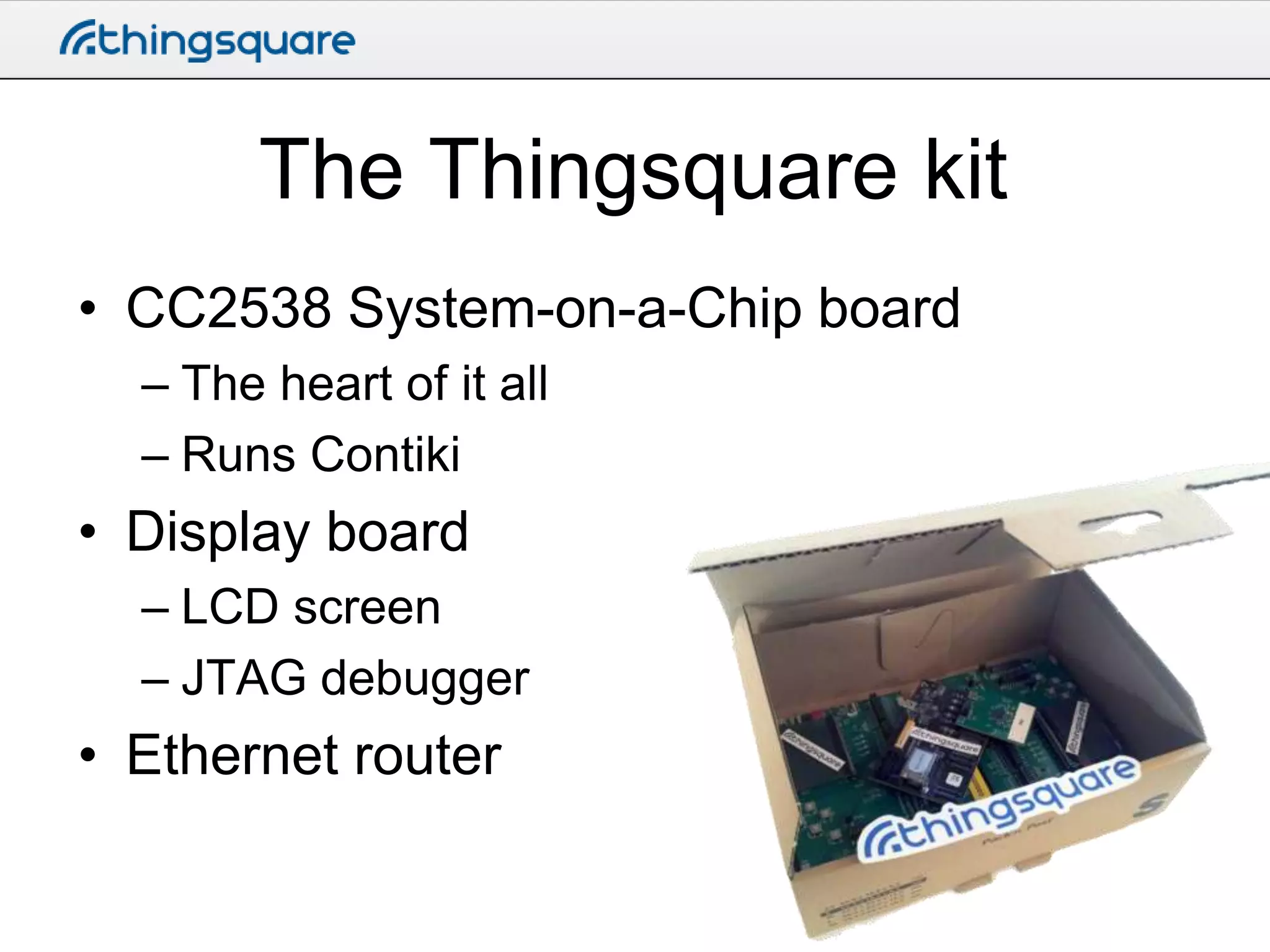
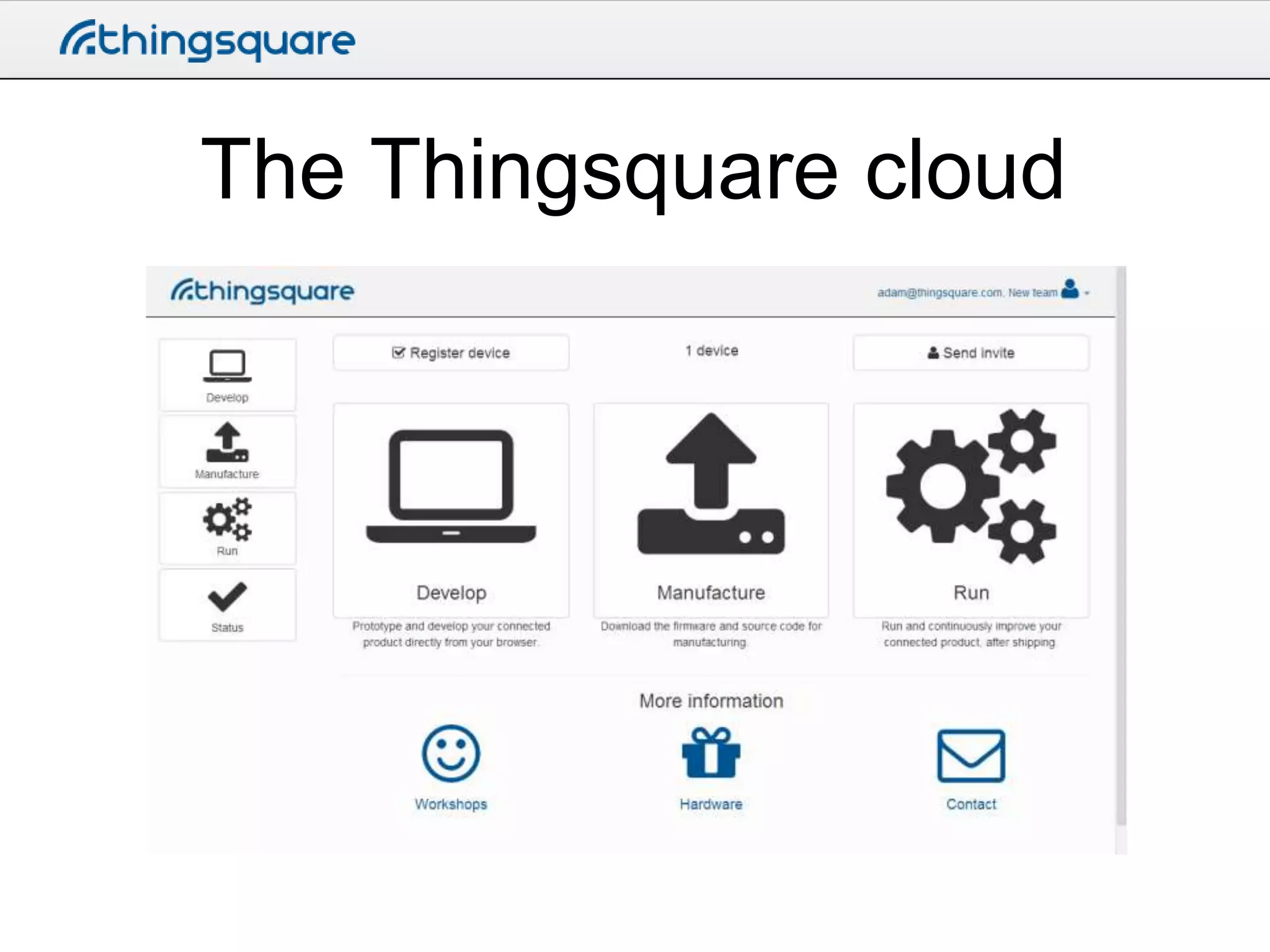
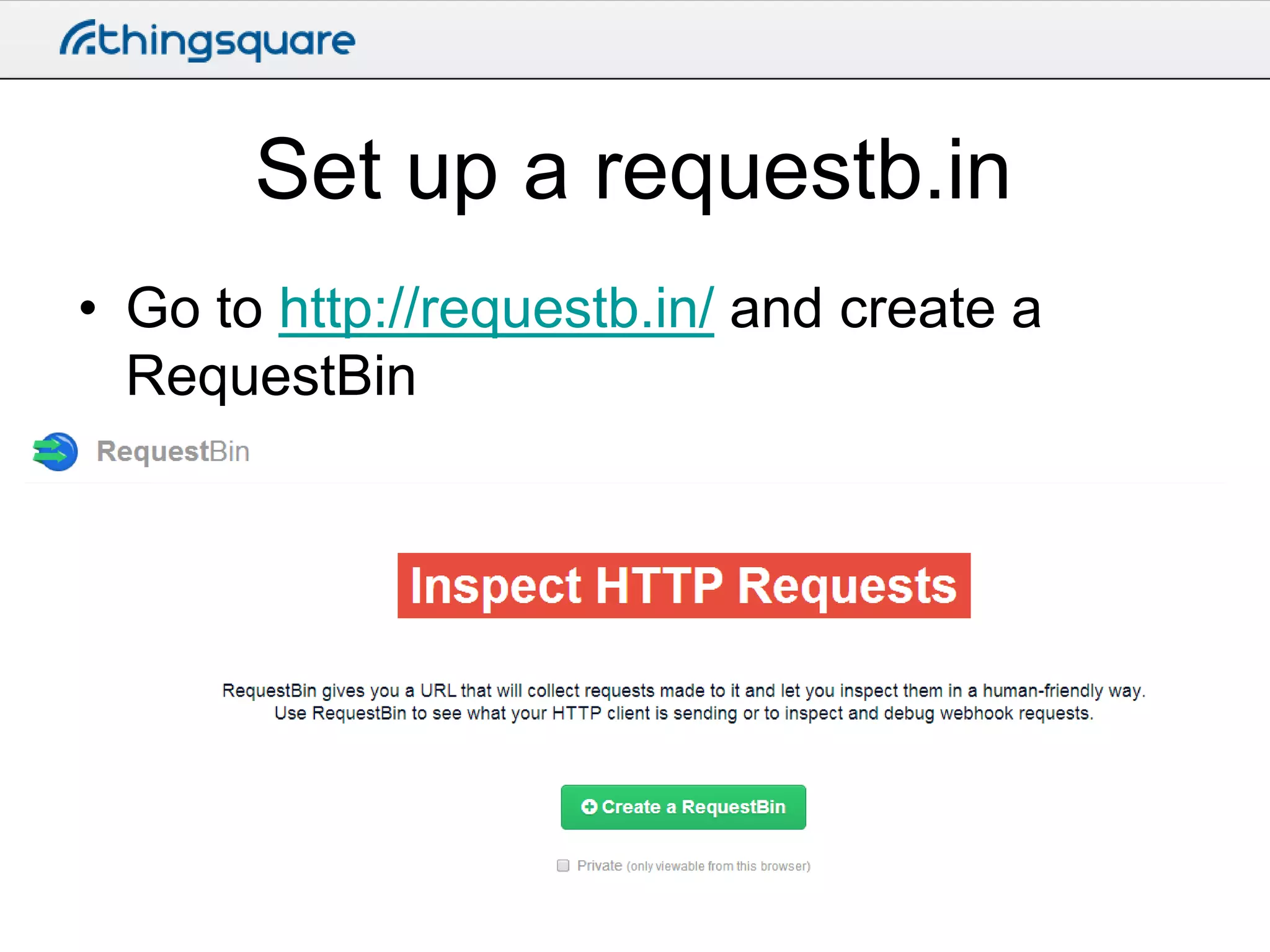
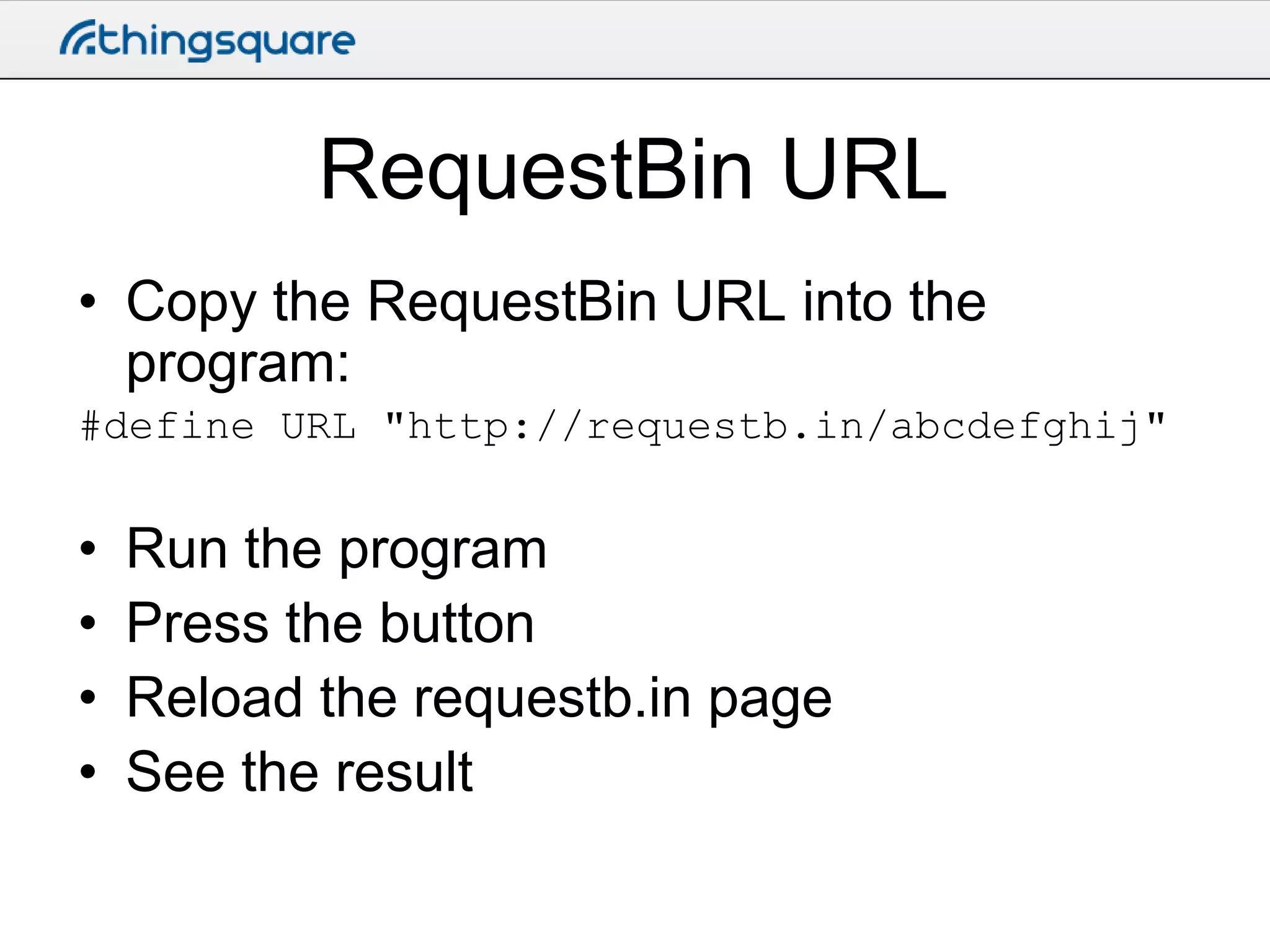
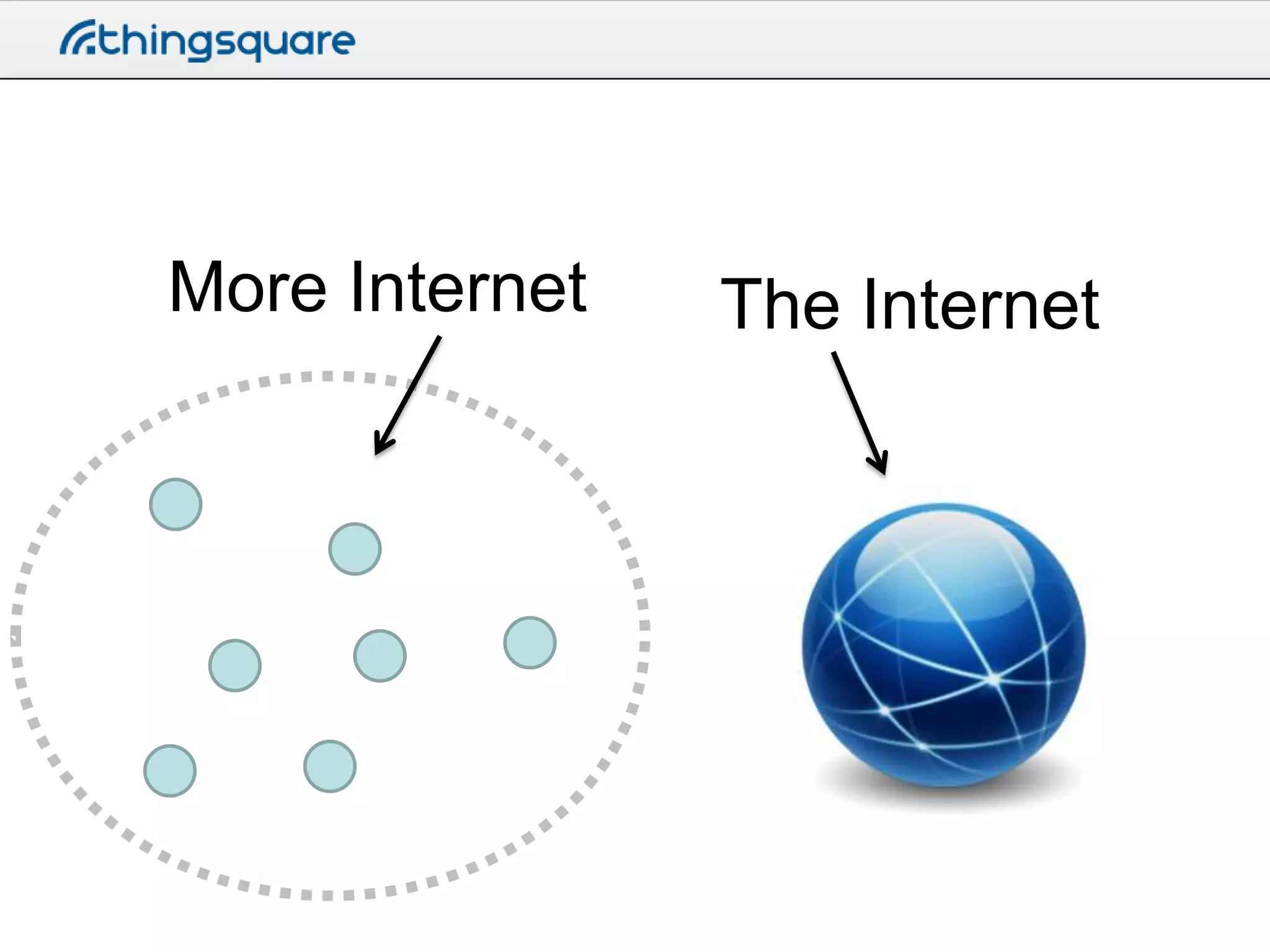
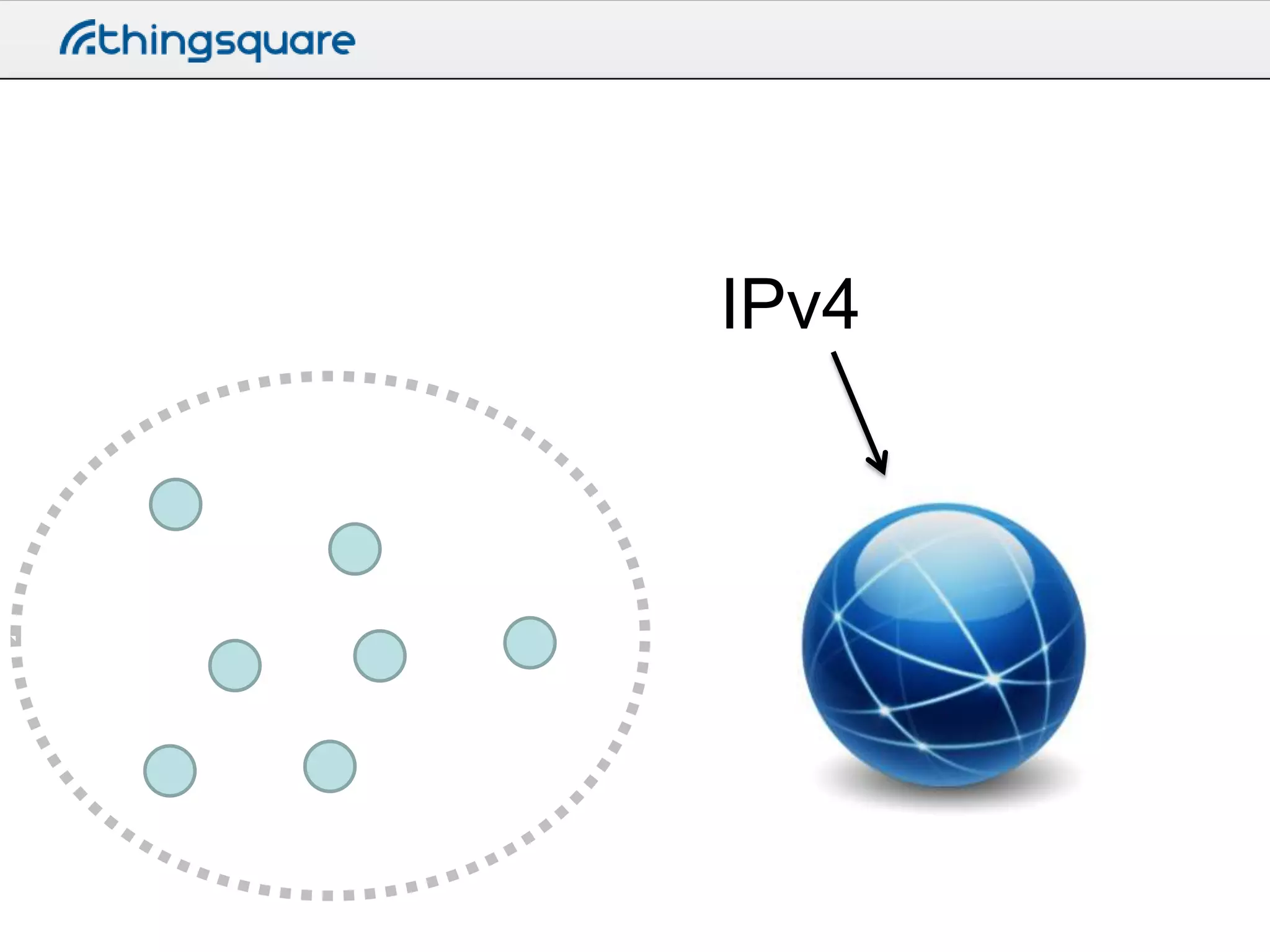
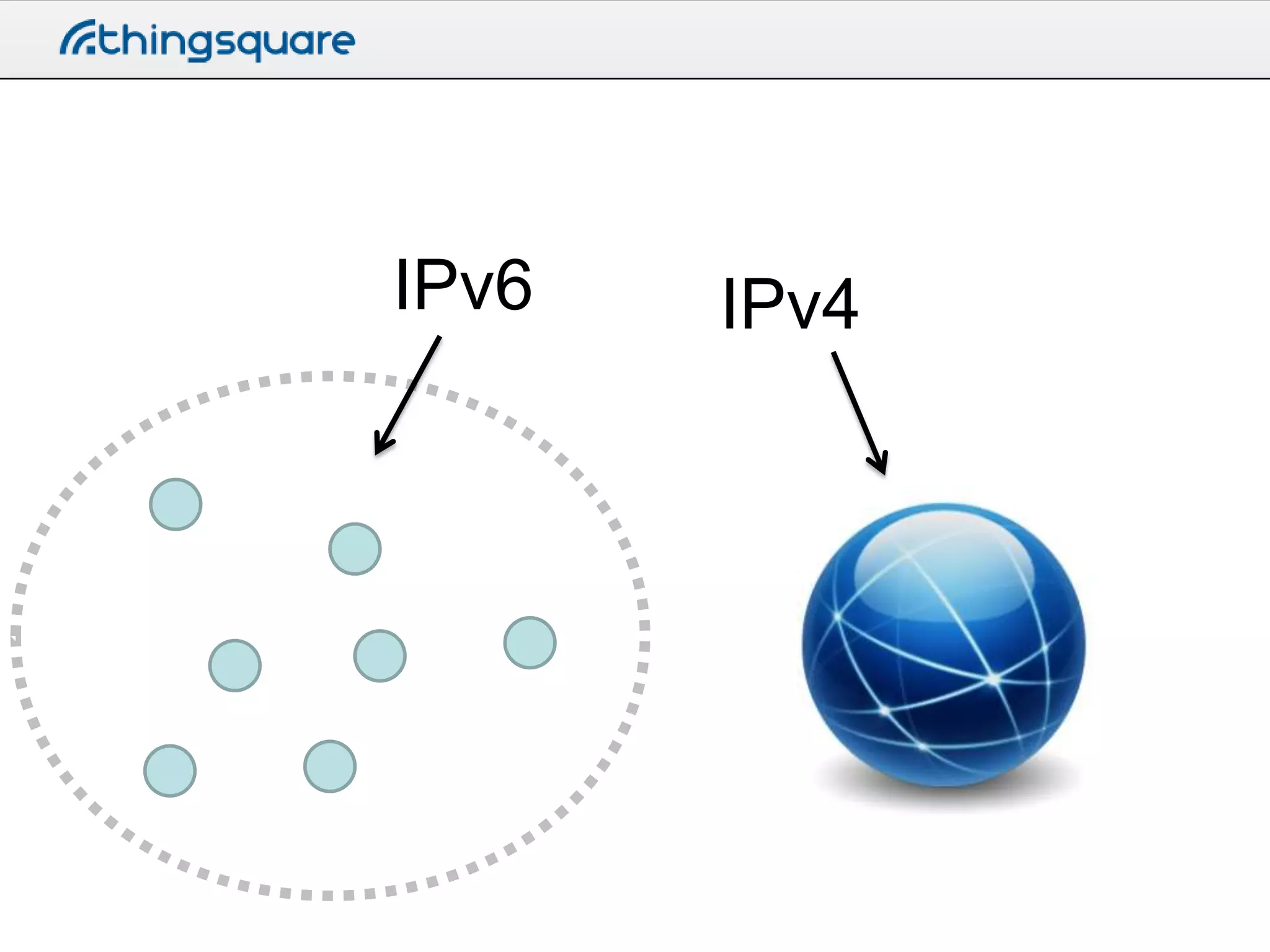
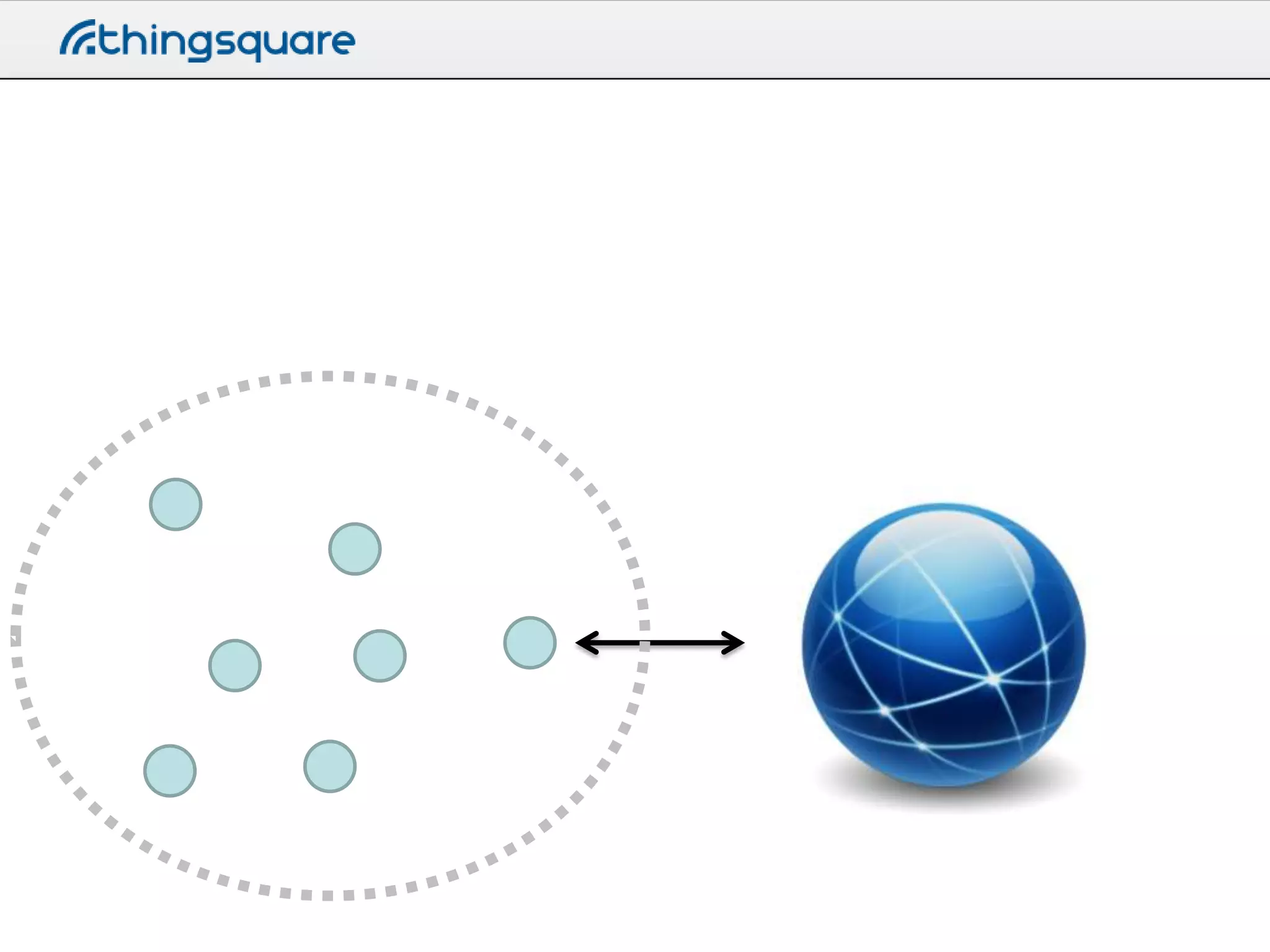
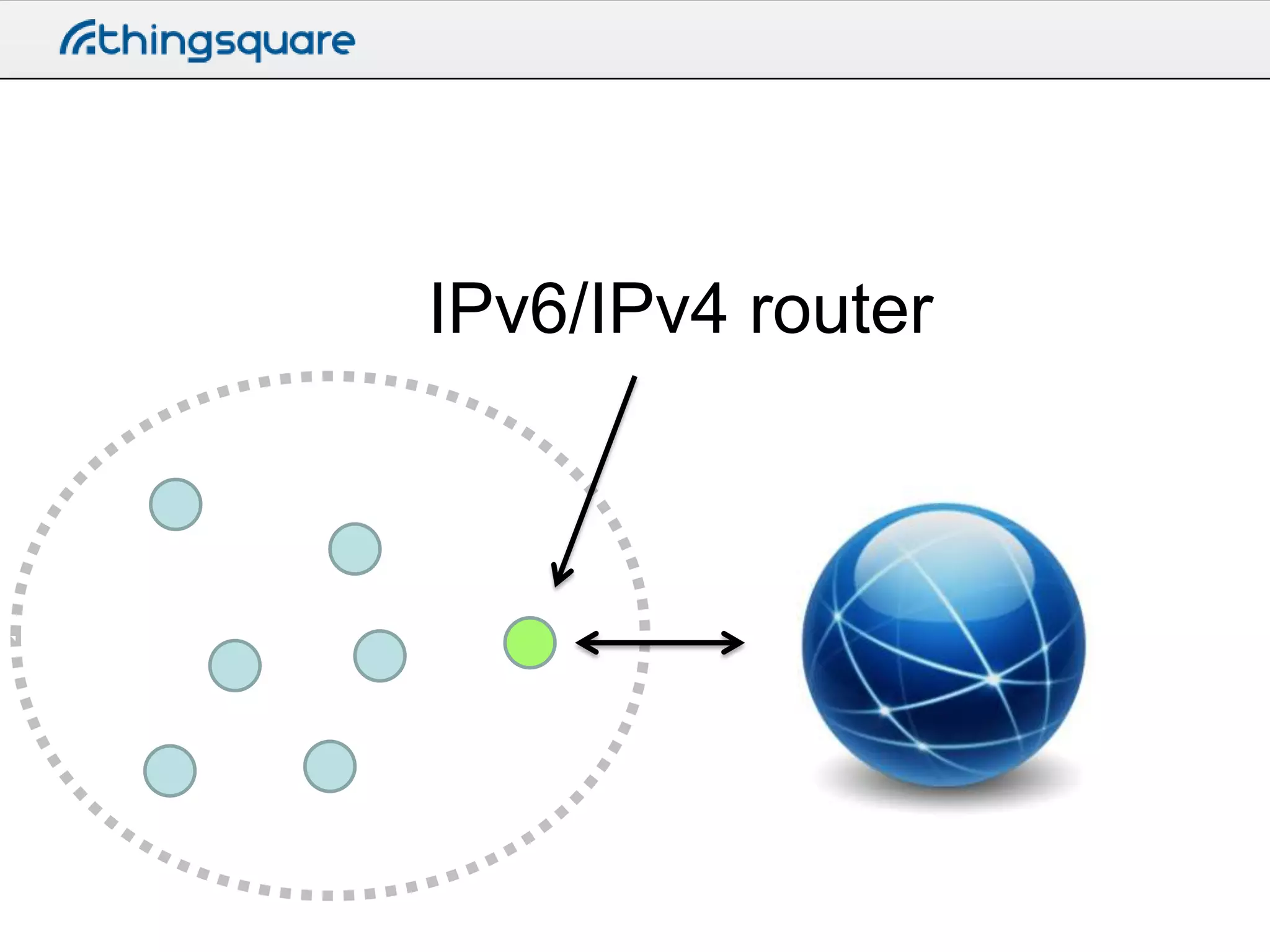
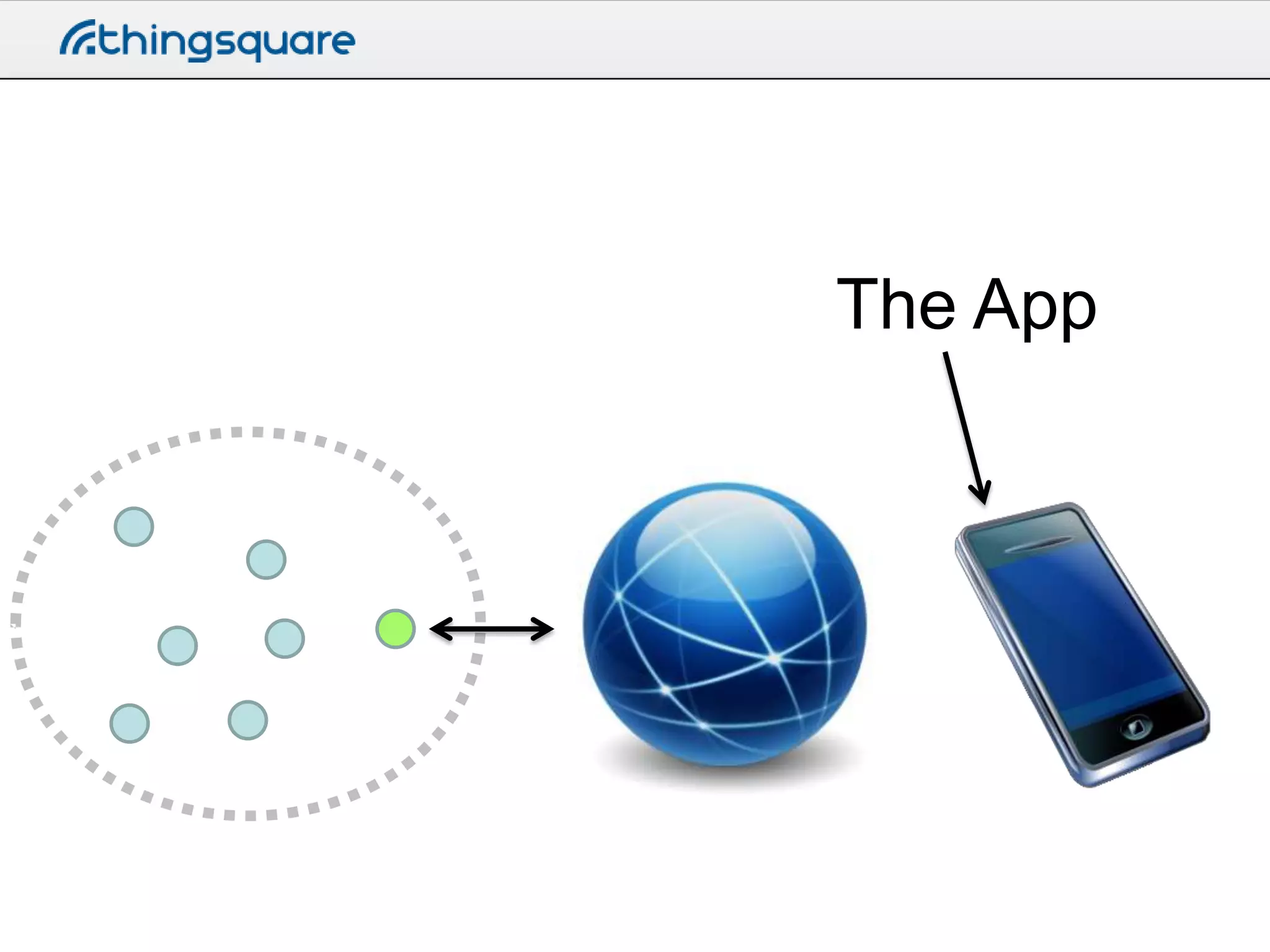
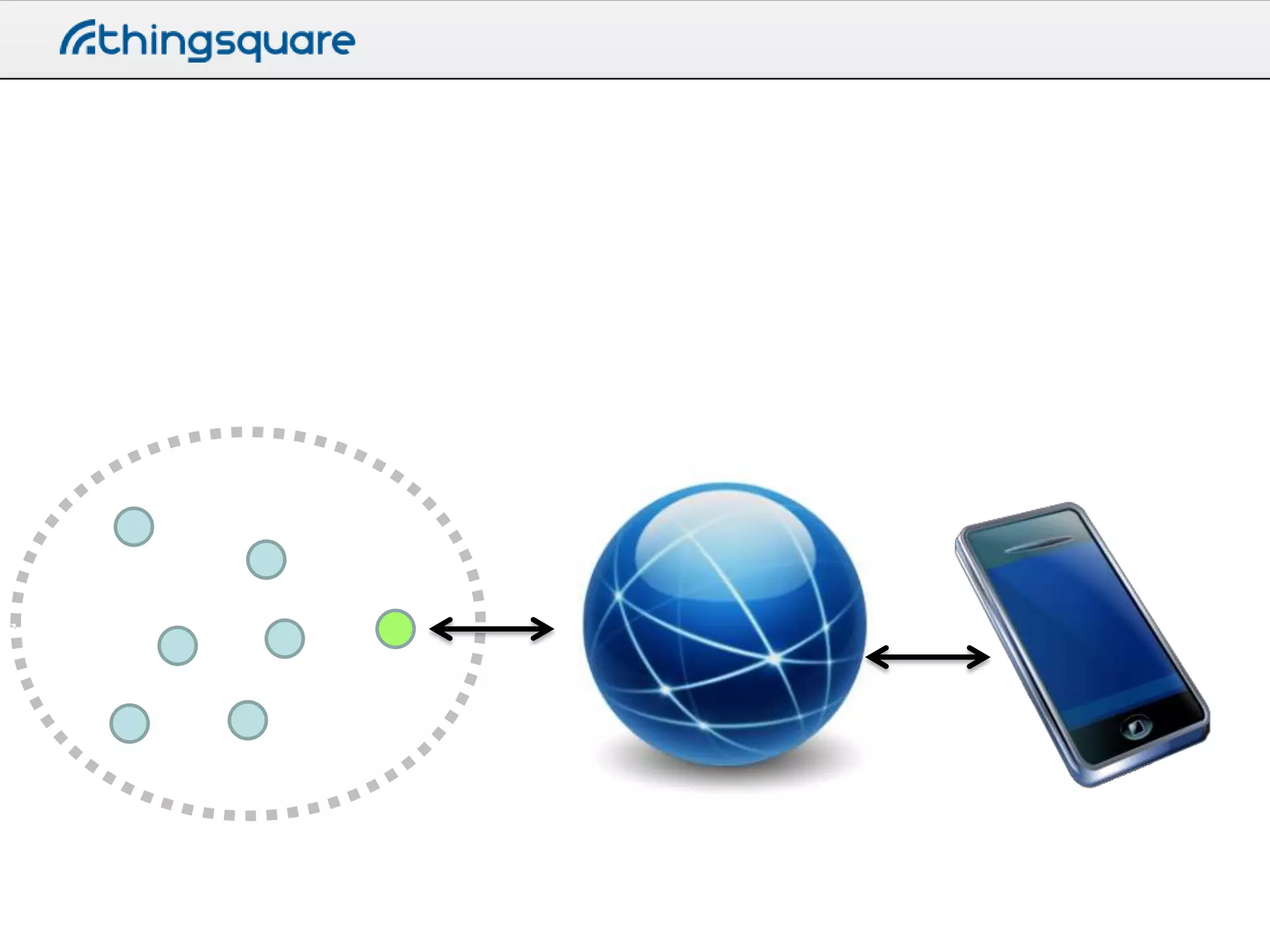
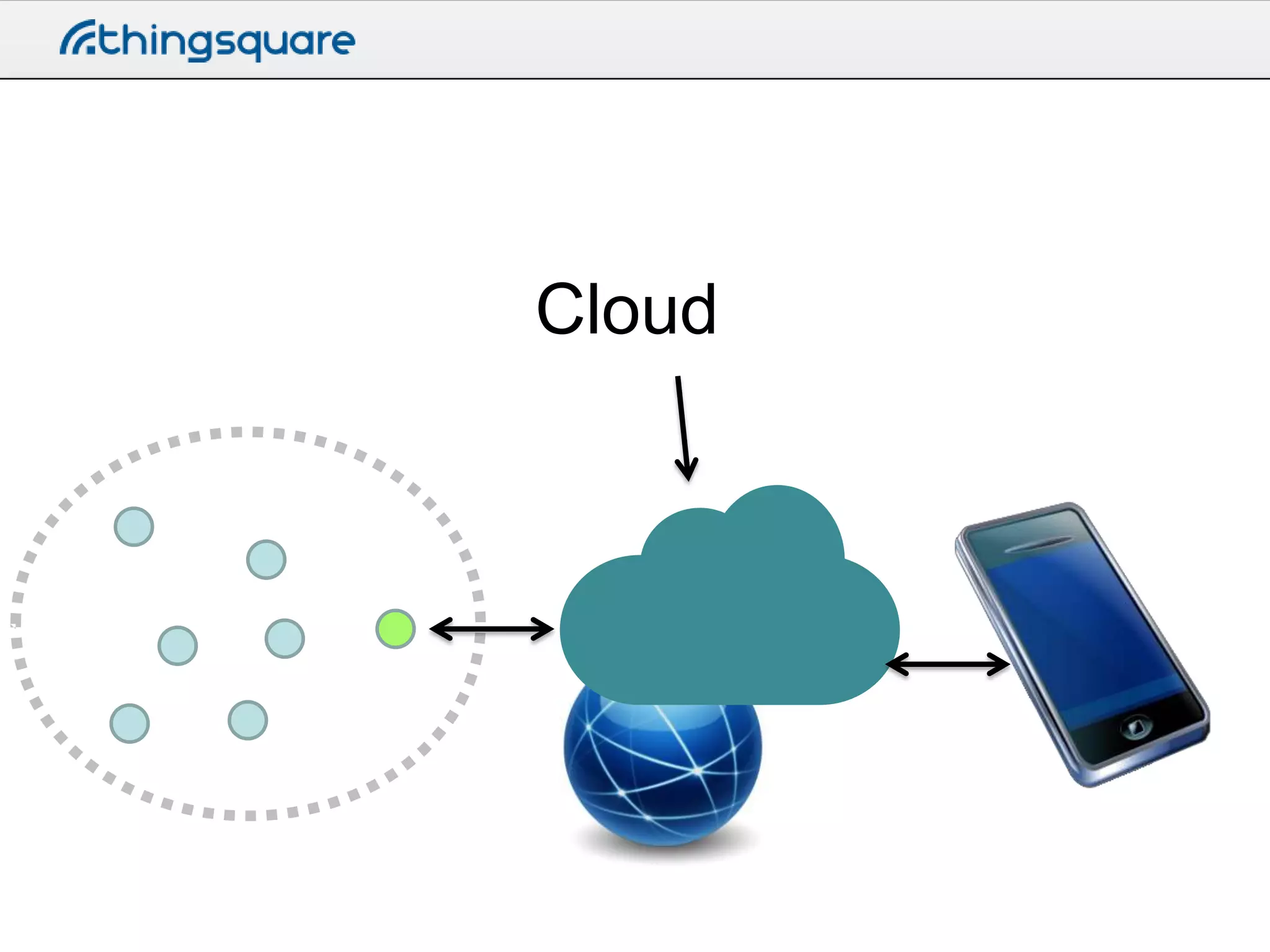
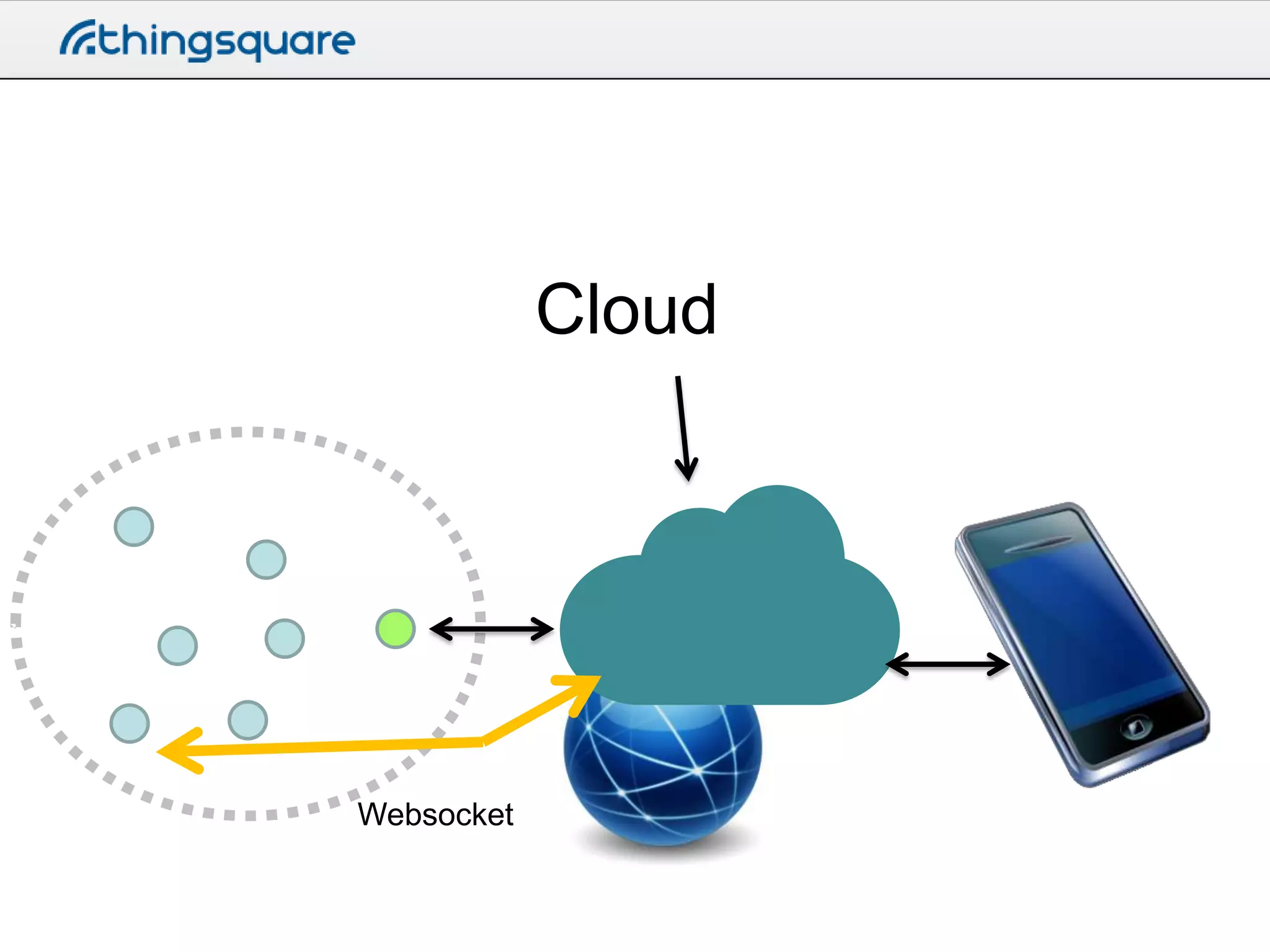
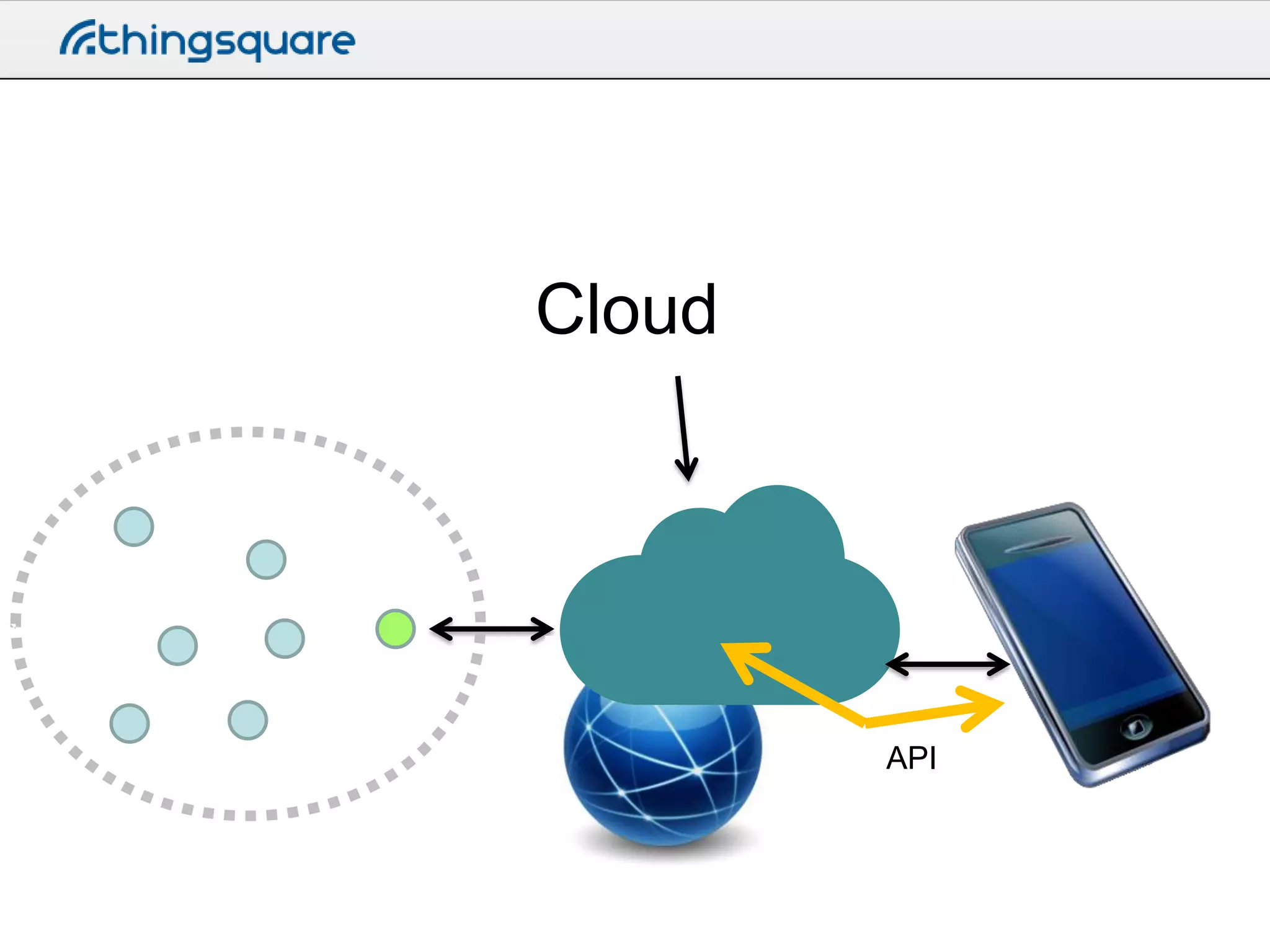
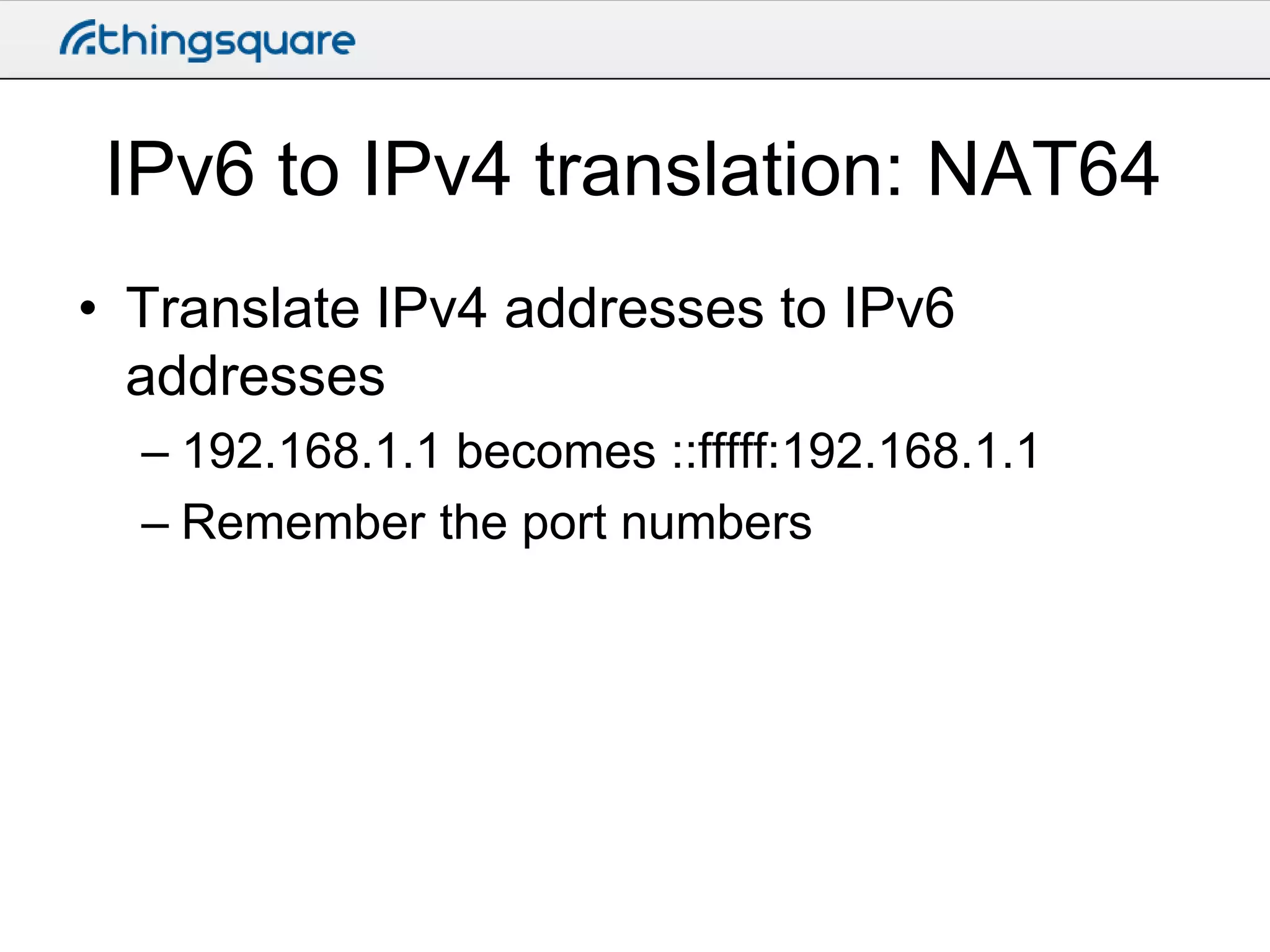
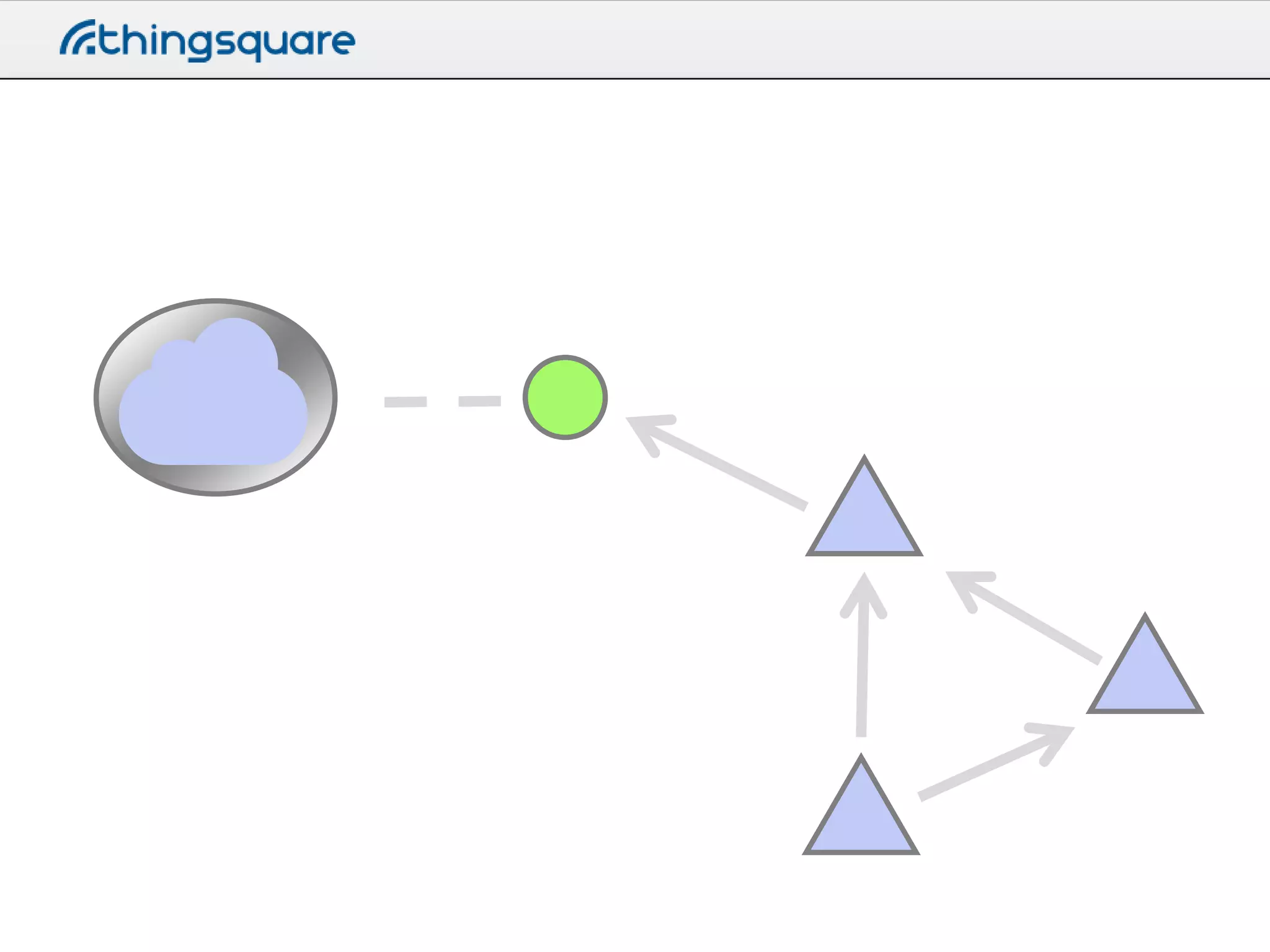
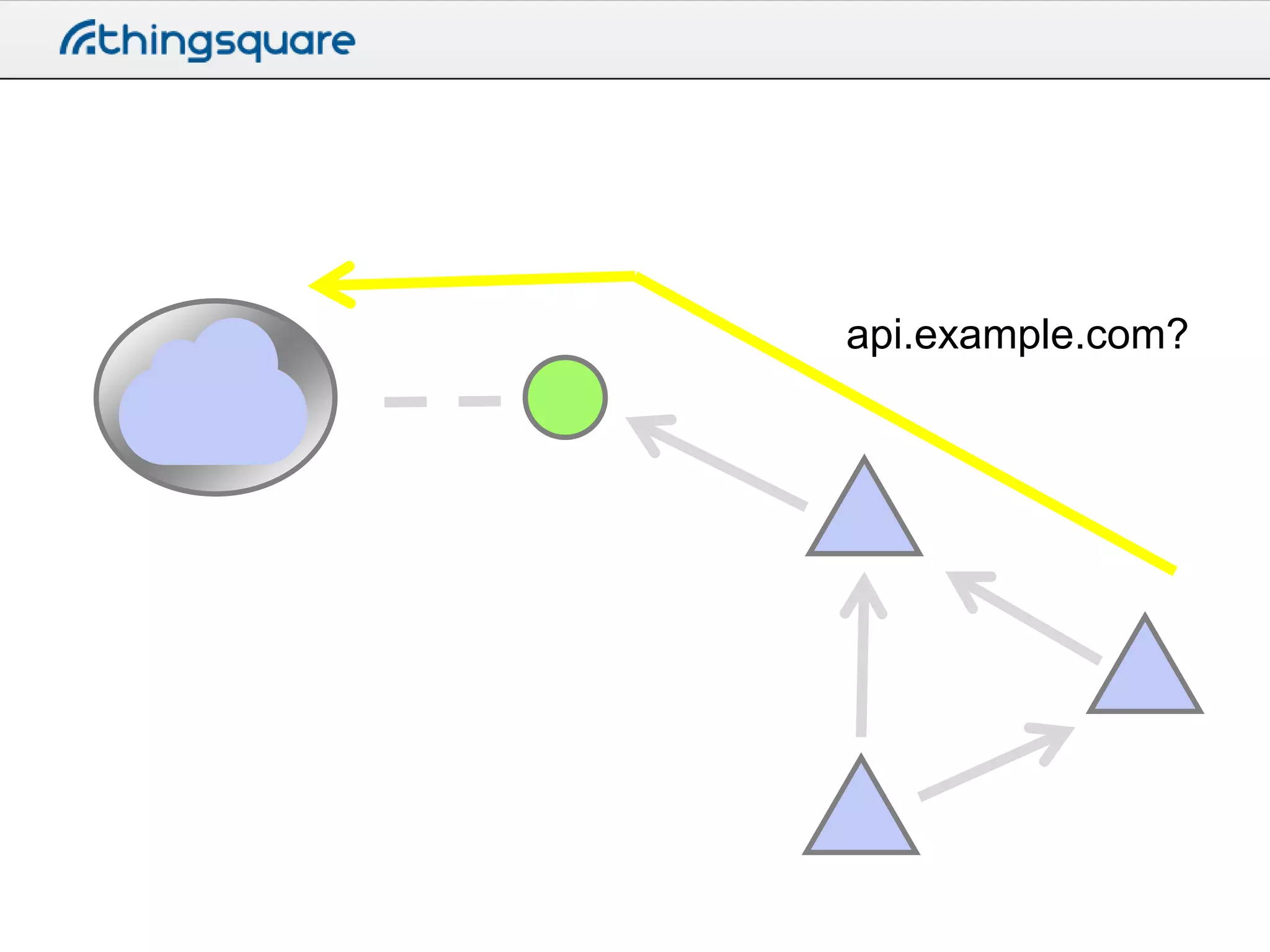
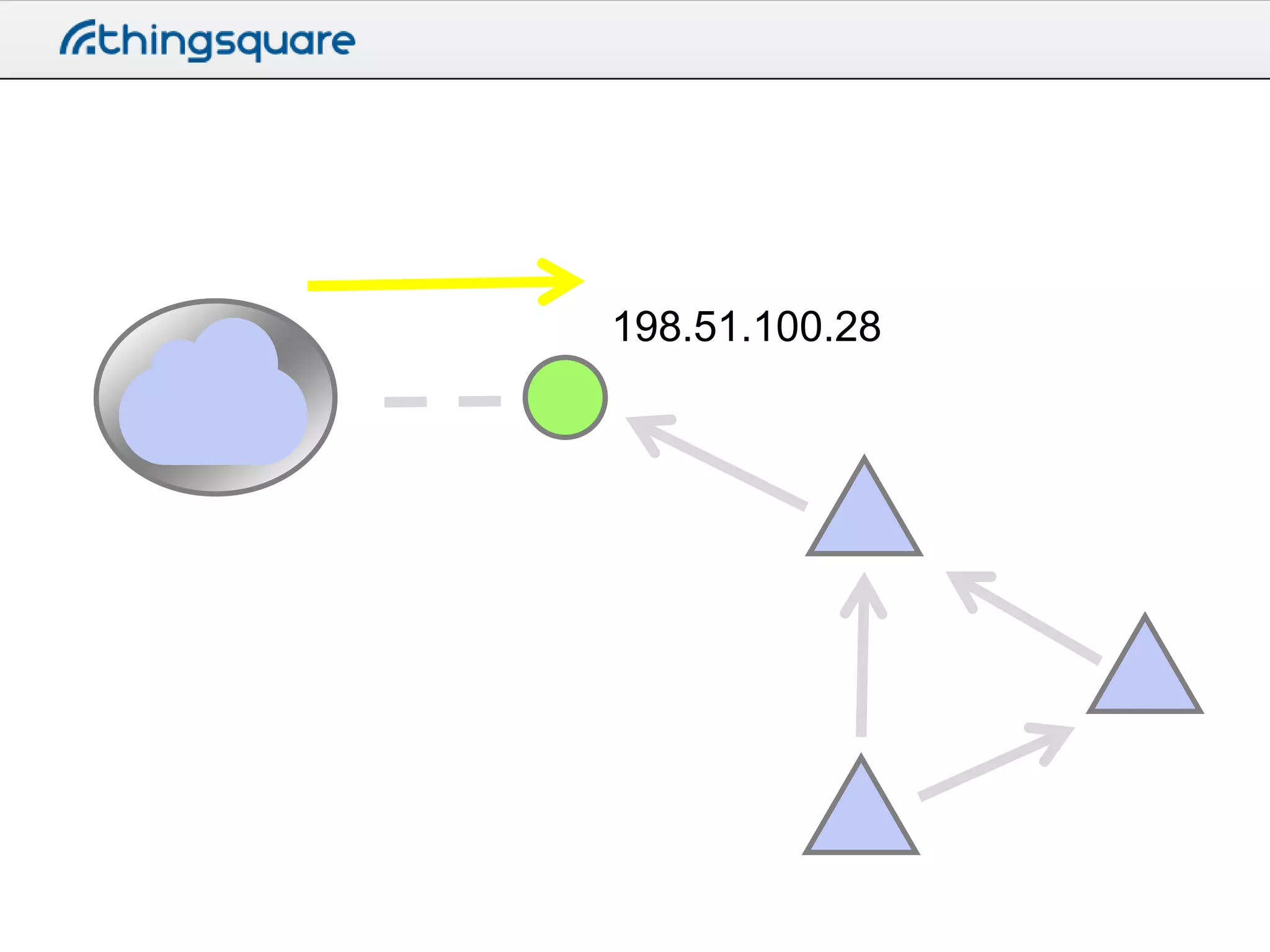
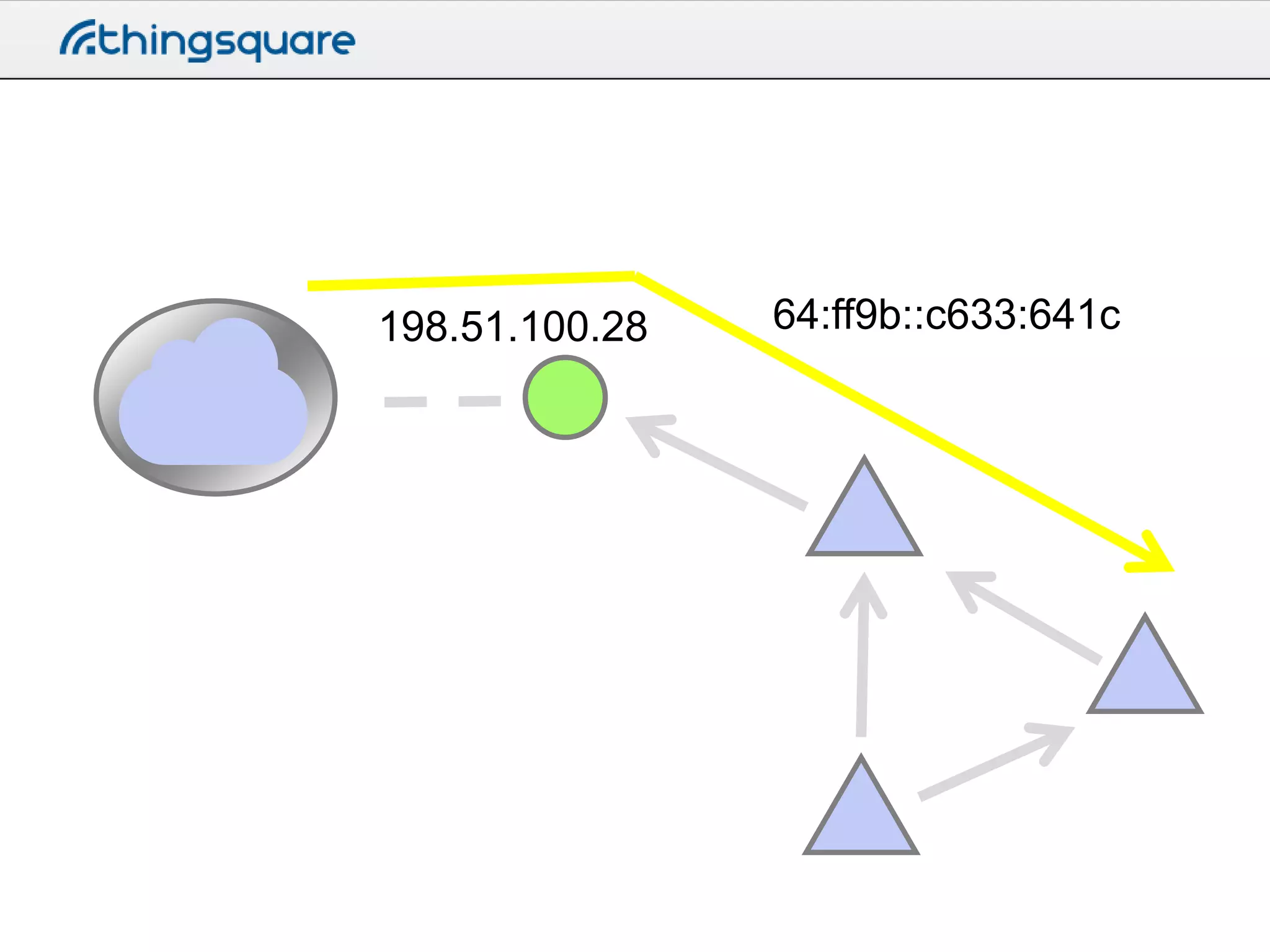
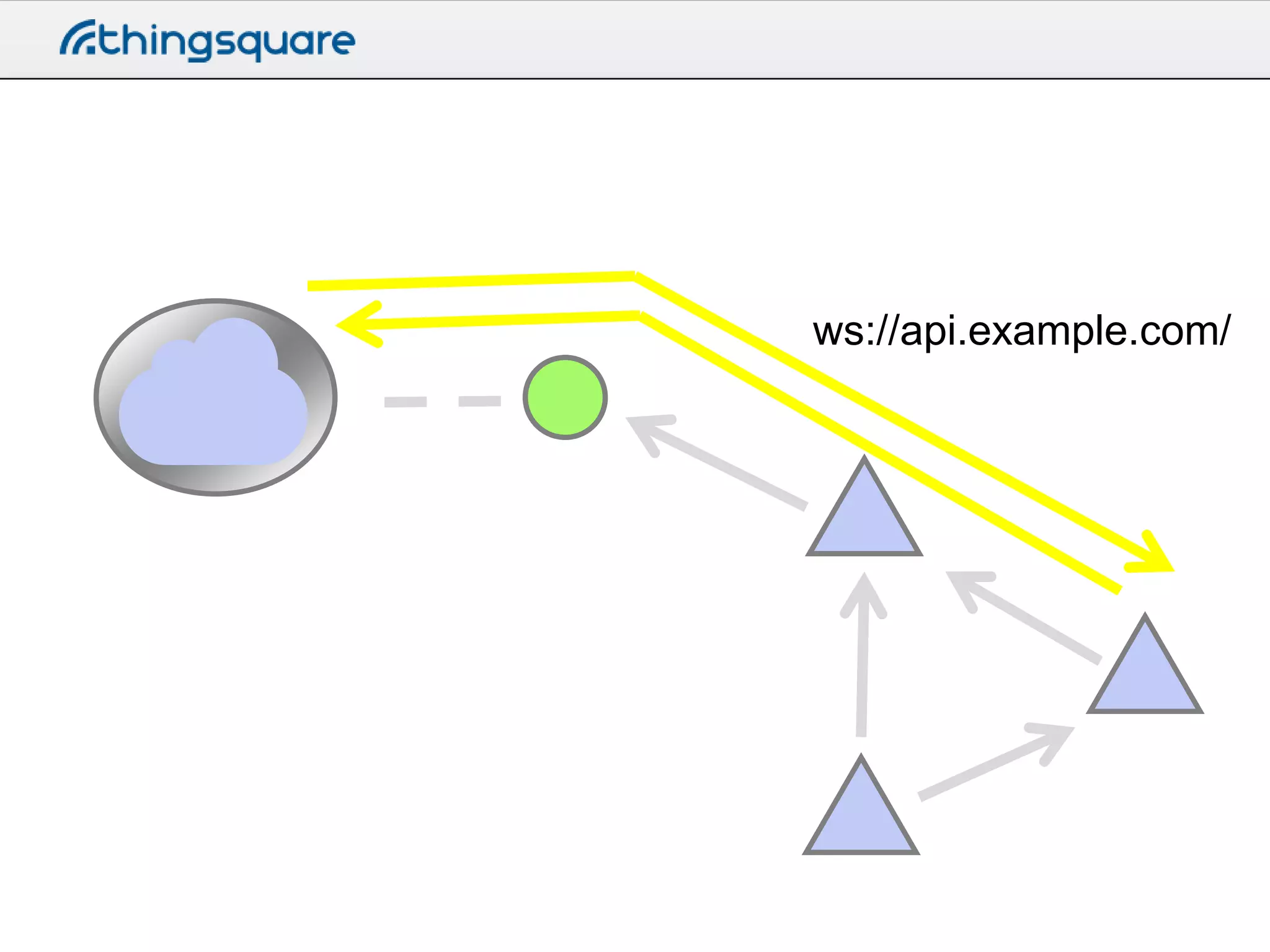
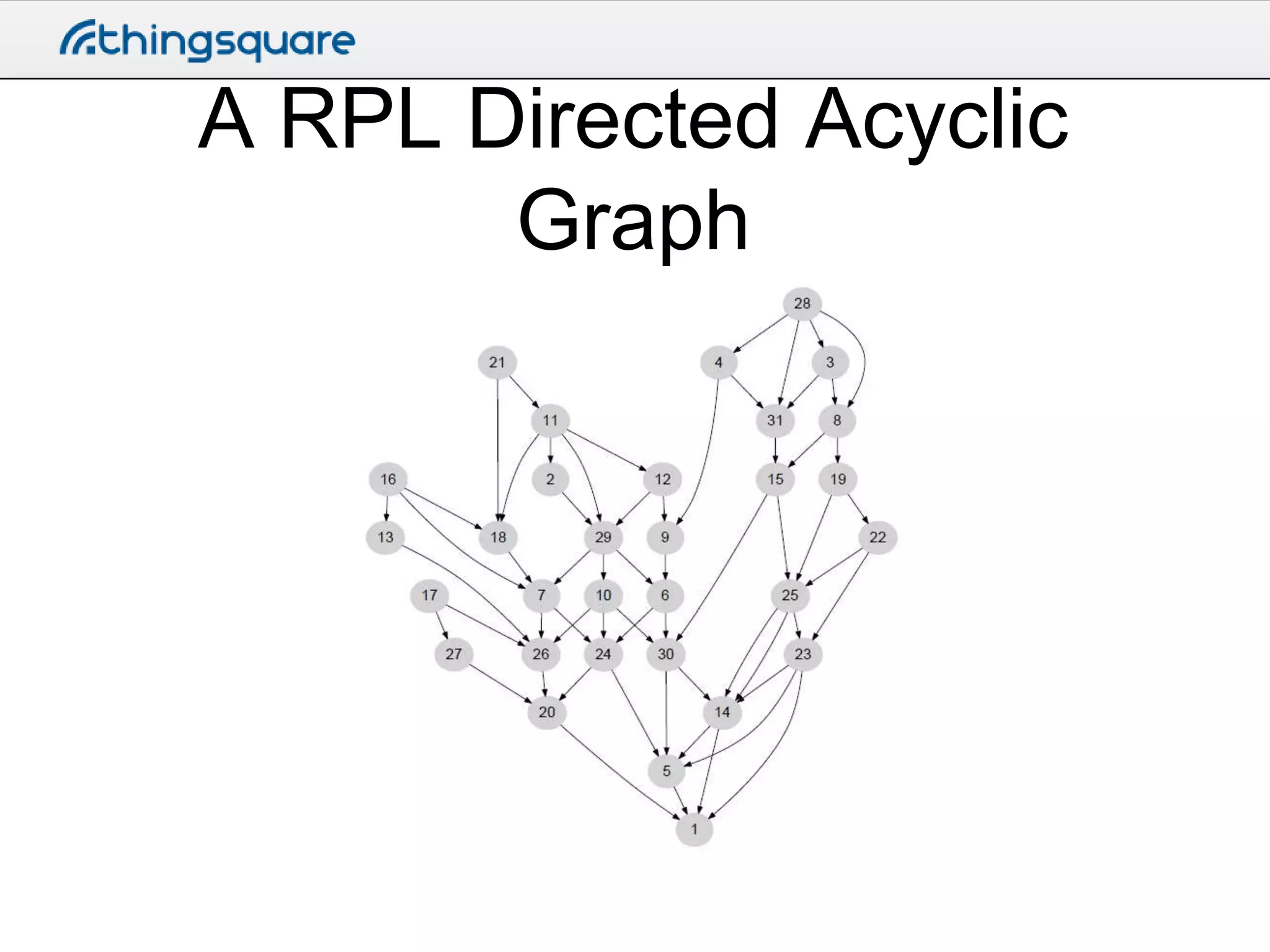
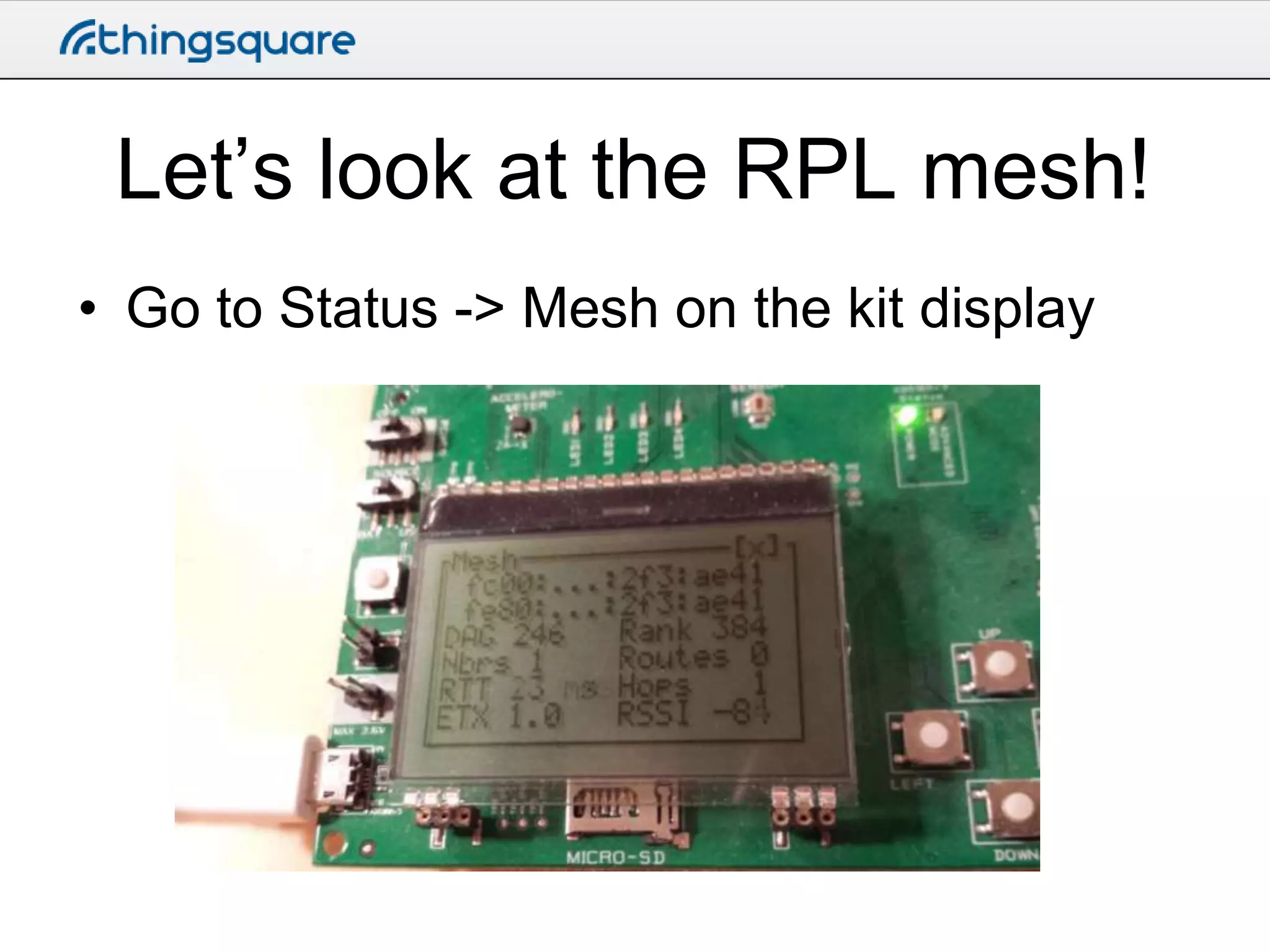
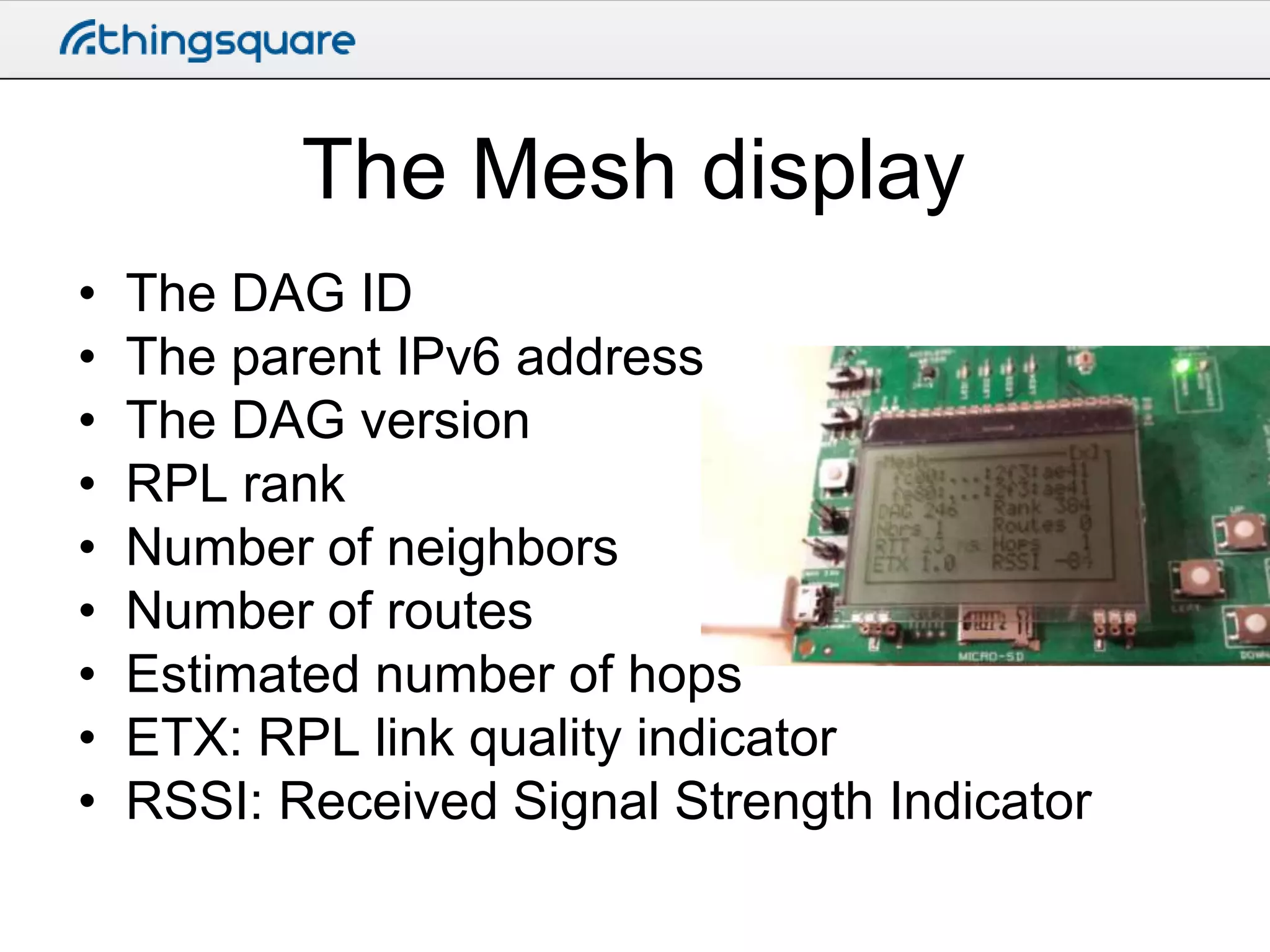
The document outlines a lab exercise involving a big red internet button connected to the Thingsquare IoT cloud. It details the setup process, including connecting the button, uploading a program that sends HTTP posts, and setting up a requestbin for data inspection. Additionally, it briefly explains the use of IPv6 in the context of the IoT, along with the RPL routing protocol for forming wireless networks.