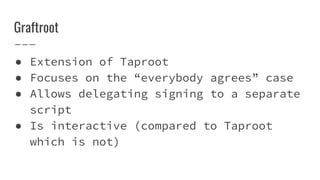
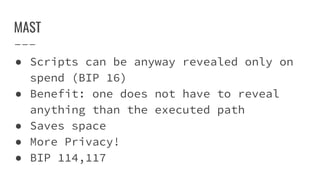
The document discusses future advancements in Bitcoin technology, focusing on concepts such as Schnorr signatures, MAST (Merkelized Abstract Syntax Tree), and Taproot. These innovations aim to improve transaction efficiency, enhance privacy, and reduce transaction sizes by allowing for aggregation and batch verification of signatures. Additionally, the introduction of new opcodes and interactive scripts is explored, highlighting their potential impact on Bitcoin's scripting capabilities.

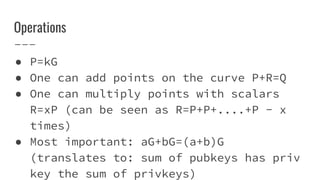


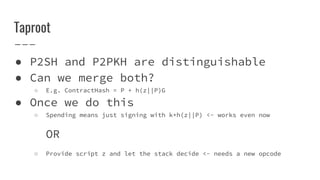
![Putting it together
● New opcode (OP_NEW)
● In output OP_NEW <pubkey>
● In input (to spend)
○ Provide <signature> in P2PKH mode
○ OR
○ <P> <script>[]<arguments> (taproot)
○ <scriptsig> <script> []<arguments> (graftroot)
● BIP-TAPROOT (no official # yet)](https://image.slidesharecdn.com/bitcoinnext-190801185746/85/Bitcoin-Next-19-320.jpg)