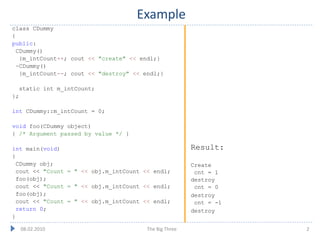
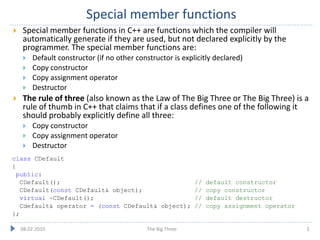
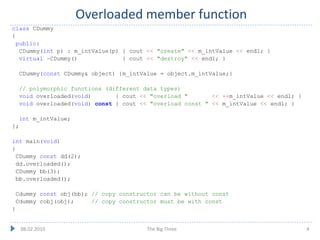
The document explains the concept of special member functions in C++, including the default constructor, copy constructor, copy assignment operator, and destructor. It emphasizes the 'Rule of Three,' stating that if a class defines any of these functions, it should likely define all three. Additionally, it provides examples of function overloads and class declarations related to these concepts.