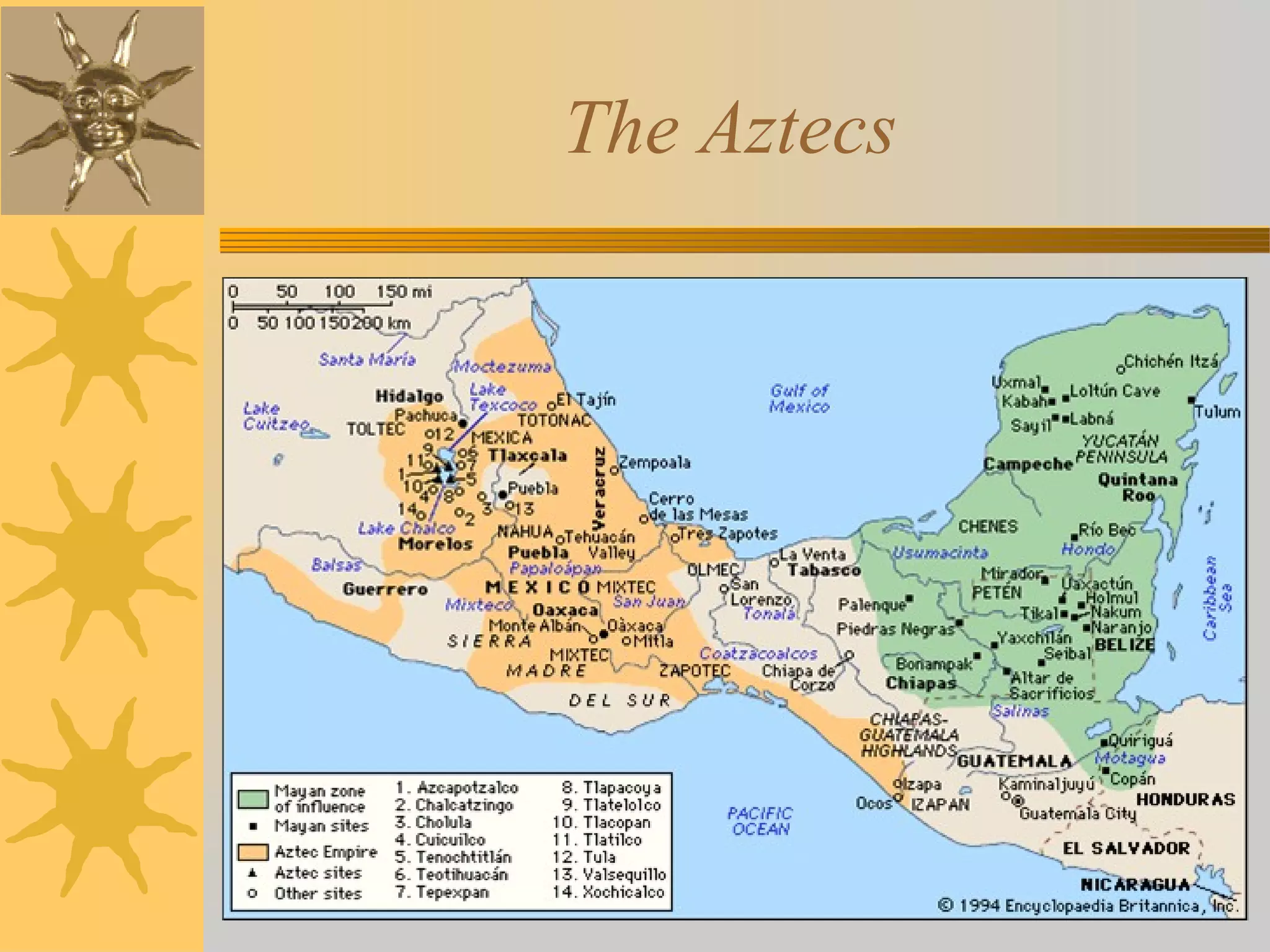
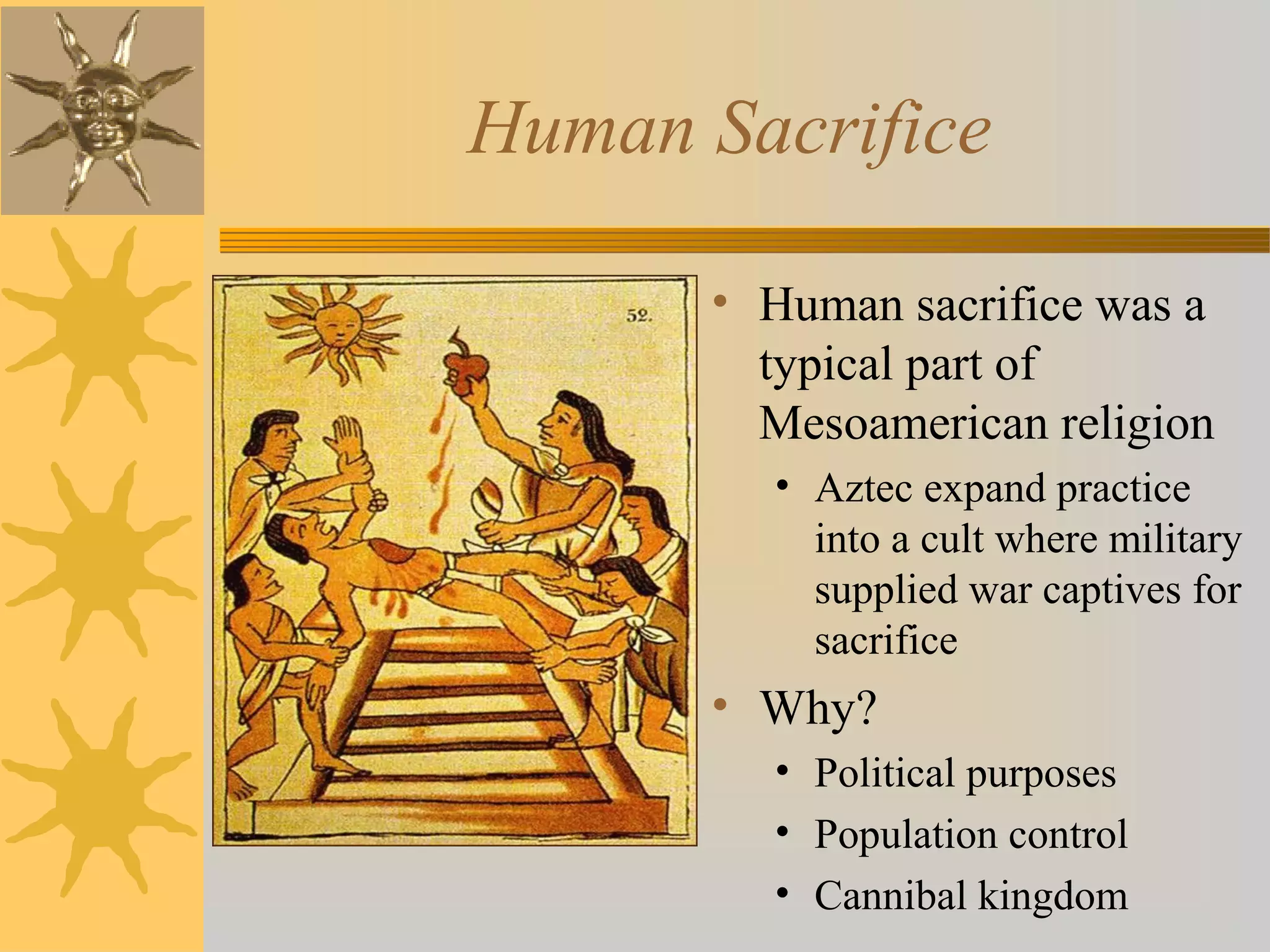
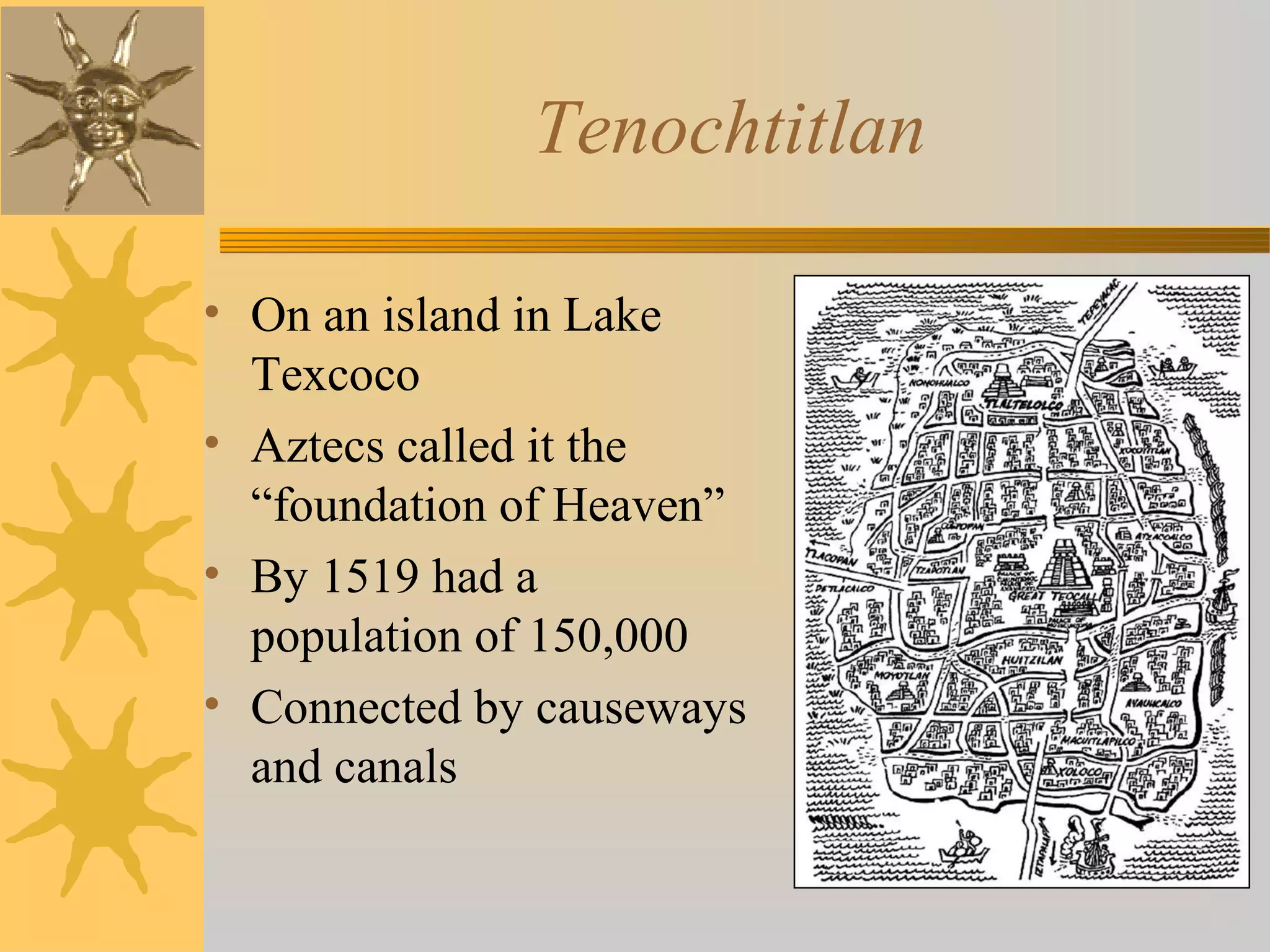
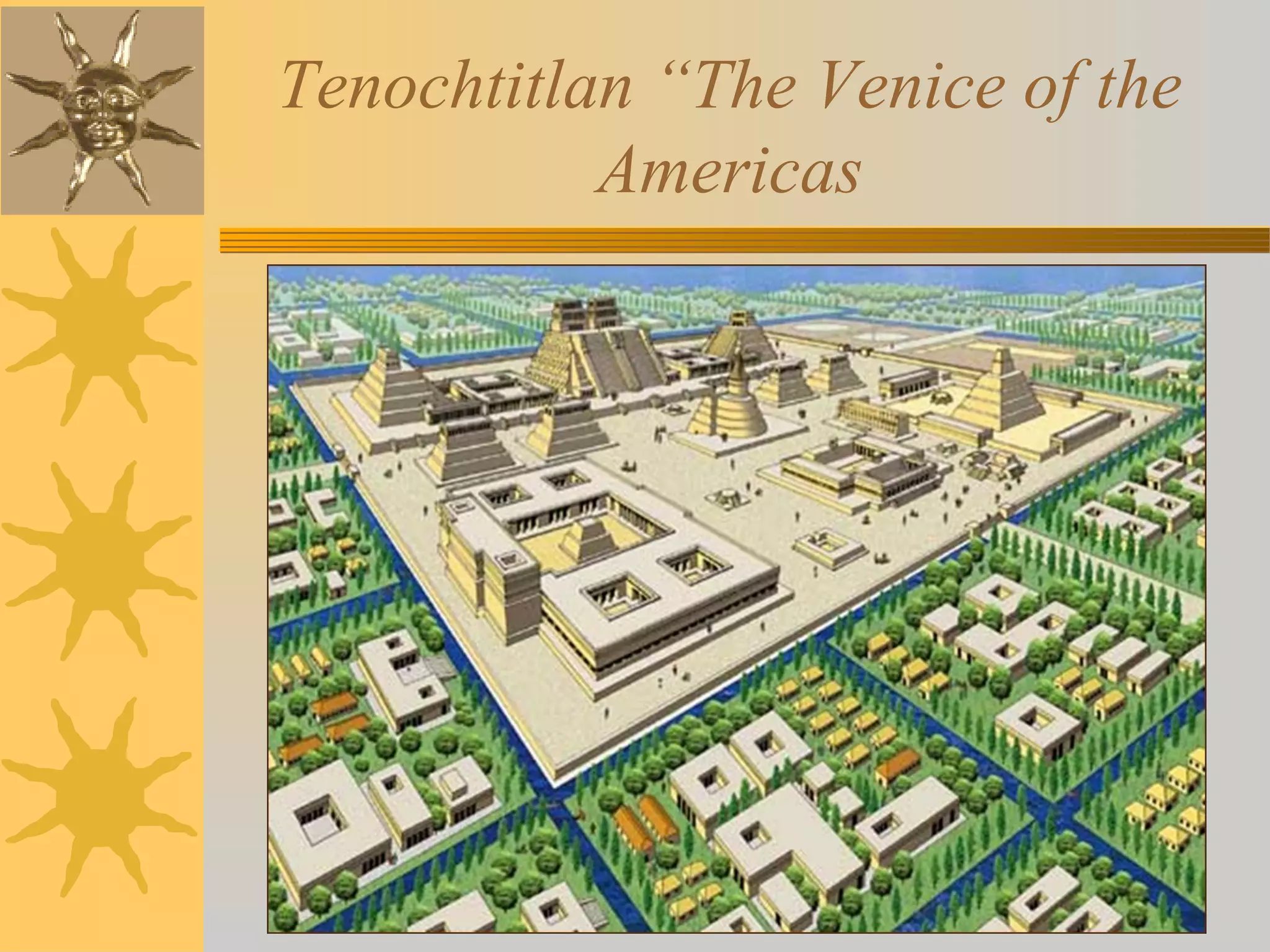
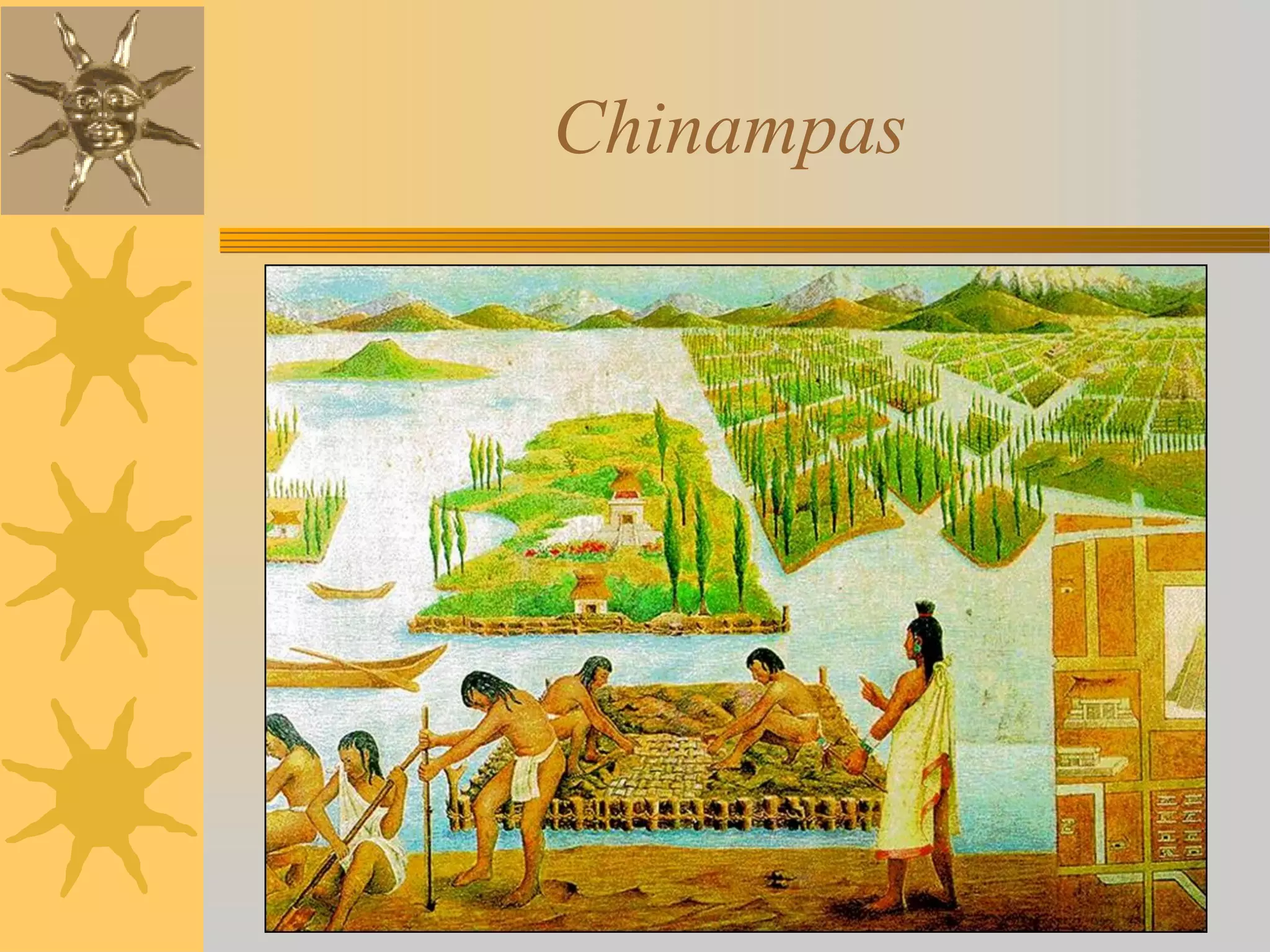
The Aztecs rose to power in central Mexico in the 14th century, founding the city of Tenochtitlan in 1325 and establishing an empire in 1434 ruled by an emperor. They developed a complex religion centered around over 100 deities including Huitzilopochtli and practiced widespread human sacrifice of war captives for political and religious purposes. By 1519, Tenochtitlan had grown to a population of 150,000 and was connected by causeways, canals, and featured floating agricultural islands called chinampas. The Aztec economy was based on agriculture and long distance trade while their society was divided into noble and common classes.