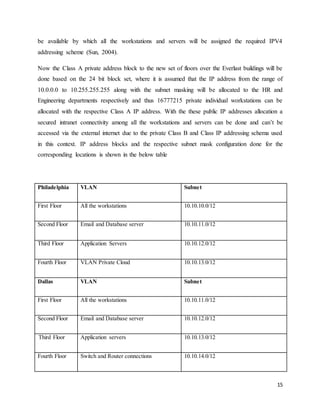
The document outlines a proposed network design for integrating the networks of Everlast and Riddell Sports, addressing existing issues and future enhancements required for their infrastructure. It covers key aspects such as network architecture, server virtualization, storage utilization, IP addressing, and security requirements. The design intends to support both companies' operations while facilitating their business needs through a comprehensive cloud-based solution.