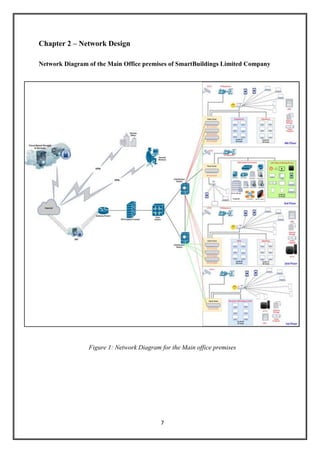
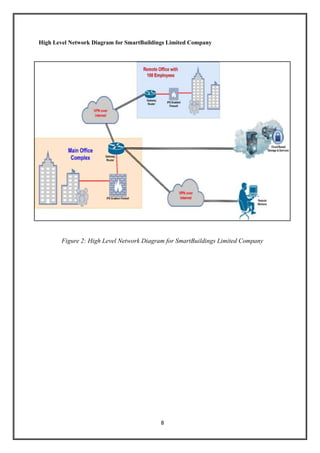
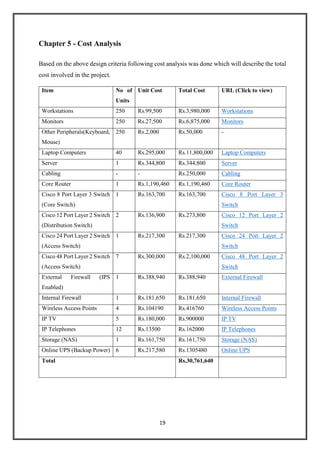
The document outlines a network design proposal for Smartbuildings Limited, focusing on upgrading their existing computer network systems to enhance efficiency and security in response to competition. It details the project goals, network architecture, device requirements, VLAN configurations, and cost considerations for a high-availability, robust network that will support future expansions. Key components include various protocols, a structured IP addressing scheme, and provisions for disaster recovery and remote access.