Anonymous Security Scanning and Browsing
•Download as PPTX, PDF•
1 like•930 views
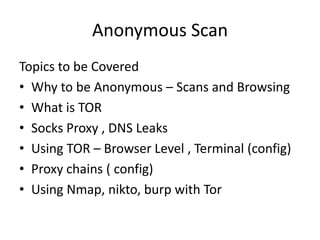
It is for Information Security professionals, to perform anonymous scans and browsing. This presentation will guide to perform nmap and burp scans using TOR network.
Report
Share
Report
Share
Recommended
Netcat

Netcat is a versatile networking tool that can be used for port scanning, port redirection, listening for incoming connections, and creating remote connections. It allows creating a simple command line chat server by running nc in listen mode on one system and connecting to it from another. Netcat can also identify services running on specific ports by obtaining port banners, and has been used by hackers to create backdoors by launching a shell on a listened port.
Network scanning

The document provides an overview of different network scanning techniques that can be performed using tools like Nmap, Wireshark, and Hping3 on Kali Linux. It discusses passive scanning techniques like sniffing network traffic with Wireshark and viewing ARP tables. It also covers various active scanning techniques using tools like Nmap for port scanning, service/OS detection and using scripts. Tips are provided for bypassing IPS/IDS devices and optimizing scans for stealth.
Nmap

This document introduces Nmap, an open source network scanning tool. It describes Nmap's basic syntax and how it works, outlines different types of scans like TCP, UDP, and SYN scans, discusses timing options, and provides references and links to tutorials on hackingarticles.in about using Nmap for tasks like port scanning, vulnerability detection, and password cracking.
Nmap(network mapping)

This document discusses various port scanning techniques used by hackers to discover services, operating systems, and open ports on target hosts. It explains common TCP scans like SYN scans which identify open and closed ports, and UDP scans. Timing options and techniques for hiding scans are also covered. The document provides examples of using the Nmap tool to perform scans and identify operating systems.
Dynamic Port Scanning

The document discusses dynamic port scanning (DPS), which integrates ARP poisoning into port scanning to dynamically spoof the source IP address of scan packets. DPS works by poisoning the ARP cache of the target host or gateway so that scan replies are delivered to the scanning machine regardless of the spoofed source IP. This allows the scan to appear as if it is coming from many machines, improving stealth, while still obtaining results unlike traditional IP spoofing techniques. The document outlines how DPS works, current spoofing methods, advantages over other techniques, and limitations.
Nmap

Nmap is a network scanning tool that can discover hosts and services on a network. It can scan TCP and UDP ports, perform OS and version detection, and has both command line and GUI interfaces. Nmap allows specification of target hosts by IP address, CIDR notation for subnets, or hostname. It provides information about open ports and common services, and can detect vulnerabilities.
Irc how to sept 2012

This document provides an overview of Internet Relay Chat (IRC) including a brief history, technical details, terminology, instructions for connecting to networks, basic commands, and how to register with NickServ and ChanServ. It outlines what IRC is, how it works, examples of raw IRC messages, explanations of networks, clients, channels, operators, and commands. It also gives guidance on joining channels, sending private messages, setting status, and more.
Internet and world wide web protocol (draft 2)

This document discusses internet protocols and network analysis tools. It covers how web pages are served from servers to clients using HTTP and IP addresses. It then explains common network protocols like TCP, IP, HTTP, and routing protocols. The document proceeds to describe the secure shell client Putty, differences between Telnet and SSH, and finally the network packet analyzer Wireshark including its uses and functionality.
Recommended
Netcat

Netcat is a versatile networking tool that can be used for port scanning, port redirection, listening for incoming connections, and creating remote connections. It allows creating a simple command line chat server by running nc in listen mode on one system and connecting to it from another. Netcat can also identify services running on specific ports by obtaining port banners, and has been used by hackers to create backdoors by launching a shell on a listened port.
Network scanning

The document provides an overview of different network scanning techniques that can be performed using tools like Nmap, Wireshark, and Hping3 on Kali Linux. It discusses passive scanning techniques like sniffing network traffic with Wireshark and viewing ARP tables. It also covers various active scanning techniques using tools like Nmap for port scanning, service/OS detection and using scripts. Tips are provided for bypassing IPS/IDS devices and optimizing scans for stealth.
Nmap

This document introduces Nmap, an open source network scanning tool. It describes Nmap's basic syntax and how it works, outlines different types of scans like TCP, UDP, and SYN scans, discusses timing options, and provides references and links to tutorials on hackingarticles.in about using Nmap for tasks like port scanning, vulnerability detection, and password cracking.
Nmap(network mapping)

This document discusses various port scanning techniques used by hackers to discover services, operating systems, and open ports on target hosts. It explains common TCP scans like SYN scans which identify open and closed ports, and UDP scans. Timing options and techniques for hiding scans are also covered. The document provides examples of using the Nmap tool to perform scans and identify operating systems.
Dynamic Port Scanning

The document discusses dynamic port scanning (DPS), which integrates ARP poisoning into port scanning to dynamically spoof the source IP address of scan packets. DPS works by poisoning the ARP cache of the target host or gateway so that scan replies are delivered to the scanning machine regardless of the spoofed source IP. This allows the scan to appear as if it is coming from many machines, improving stealth, while still obtaining results unlike traditional IP spoofing techniques. The document outlines how DPS works, current spoofing methods, advantages over other techniques, and limitations.
Nmap

Nmap is a network scanning tool that can discover hosts and services on a network. It can scan TCP and UDP ports, perform OS and version detection, and has both command line and GUI interfaces. Nmap allows specification of target hosts by IP address, CIDR notation for subnets, or hostname. It provides information about open ports and common services, and can detect vulnerabilities.
Irc how to sept 2012

This document provides an overview of Internet Relay Chat (IRC) including a brief history, technical details, terminology, instructions for connecting to networks, basic commands, and how to register with NickServ and ChanServ. It outlines what IRC is, how it works, examples of raw IRC messages, explanations of networks, clients, channels, operators, and commands. It also gives guidance on joining channels, sending private messages, setting status, and more.
Internet and world wide web protocol (draft 2)

This document discusses internet protocols and network analysis tools. It covers how web pages are served from servers to clients using HTTP and IP addresses. It then explains common network protocols like TCP, IP, HTTP, and routing protocols. The document proceeds to describe the secure shell client Putty, differences between Telnet and SSH, and finally the network packet analyzer Wireshark including its uses and functionality.
Nmap and metasploitable

This was presented in Null Open Security community july meetup, Session was on Nmap and metasploitable
Security Onion Advance

This document provides an overview and comparison of Suricata and Snort intrusion detection systems. It discusses features like performance, rule writing, and capabilities. PF_ring and netsniff-ng are introduced as tools for improving packet capture speed. The document also demonstrates how to write Snort rules specifying actions, protocols, IP addresses, ports, directions and other options.
Recon with Nmap 

The document discusses using Nmap to perform network scanning and reconnaissance. It provides an overview of Nmap, describing common scan types like TCP and UDP scans. It also covers useful Nmap options for tasks like service and operating system detection. The document demonstrates the Nmap Scripting Engine for tasks like vulnerability scanning and brute force attacks. It provides examples of commands for different scan types and scripts.
BlueHat v17 || TLS 1.3 - Full speed ahead... mind the warnings - the great, t...

BlueHat v17 || TLS 1.3 - Full speed ahead... mind the warnings - the great, t...BlueHat Security Conference
Joseph Salowey, Tableau Software
Transport Layer Security (TLS) 1.3 is almost here. The protocol that protects most of the Internet secure connections is getting the biggest ever revamp, and is losing a round-trip. We will explore differences between TLS 1.3 and previous versions in detail, focusing on the performance and security improvements of the new protocol as well as some of the challenges we face around securely implementing new features such as 0-RTT resumption.
N map presentation

Nmap is a security scanning tool that can discover open ports, scan for services, and determine operating systems on a network. It works by sending packets to IP addresses and analyzing the responses to infer information about the target system, such as which ports are open or closed and what services are running. Nmap displays this information to the user and can be run from both graphical and command line interfaces on many operating systems. While useful for security auditing, Nmap could also enable hacking if used without permission on a network.
SSH Tunneling Recipes

This document provides recipes and explanations for using SSH tunneling techniques. SSH tunneling allows creating encrypted tunnels through an SSH connection to securely access services, bypass firewalls and censorship, and forward X11 applications. It discusses local and remote port forwarding, dynamic SOCKS proxying, and tools like autossh and sslh. Common uses of SSH tunneling include securely accessing services on insecure networks, circumventing censorship, opening firewall ports dynamically through port knocking, and forwarding graphical X11 applications remotely.
NMap

Nmap (Network Mapper} is and an Open Source utility which can quickly scan broad ranges of devices and provide valuable information about the devices on your network.It can be used for IT auditing and asset discovery as well as security profiling of the network.
CNIT 50: 6. Command Line Packet Analysis Tools

This document provides an overview of 6 command line packet analysis tools used for network security monitoring: Tcpdump, Dumpcap, Tshark, Argus, the Argus Ra client, and Argus Racluster. It describes what each tool is used for, basic syntax and examples of using filters to view specific traffic like ICMP, DNS, TCP handshakes. It also covers running these tools from the command line, reading captured packet files, and examining Argus session data files.
Penetration Testing Boot CAMP

The document provides instructions on how to configure an SSH server on Linux, perform footprinting and reconnaissance, scanning tools and techniques, enumeration tools and techniques, password cracking techniques and tools, privilege escalation methods, and keylogging and hidden file techniques. It discusses active and passive footprinting, Nmap port scanning, NetBIOS and SNMP enumeration, Windows password hashes, the sticky keys method for privilege escalation, ActualSpy keylogging software, and hiding files using NTFS alternate data streams. Countermeasures for many of these techniques are also outlined.
NMAP

Nmap is a network exploration tool that collects information about target hosts including open ports, services, OS detection, and running scripts. It offers various host discovery techniques like ICMP ping, TCP and UDP ping to find active systems on the network. Once hosts are identified, nmap performs port scanning using TCP SYN, ACK, and UDP scans to determine open and closed ports. It can also detect services, versions, and OS on each host. Nmap scripts provide additional information gathering capabilities for vulnerabilities and exploits.
Wireless security beyond password cracking by Mohit Ranjan

Network attacks in wired Lan environments
Protection in wired Lan
Layout of modern networks ( wired + wireless )
Difference between wired and wireless security
Most powerful situation to acquire in any network
Wireless attacks
Why NTP ?
Captive portal attacks
Conclusion and some wild thoughts
For complete data to perform this attack please go to the Github link below:
https://github.com/mohitrajain/Wireless_security_beyond_password_cracking
Netcat - A Swiss Army Tool

Netcat, also known as the Swiss Army knife of networking tools, can be used for various purposes including creating chat servers, serving web pages, port scanning, file transfers, and obtaining remote shells. The document discusses different versions of Netcat, provides examples of using Netcat for these tasks, and notes some security disadvantages when using it without encryption. Key topics covered include creating a basic chat server and web server, using Netcat for port scanning and file transfers, and obtaining a remote Windows command shell, although this last use raises security concerns.
Snort by SecArmour

This document discusses different types of intrusion detection systems including network intrusion detection systems like Snort, host intrusion detection systems like OSSEC, and distributed intrusion detection systems. It provides an introduction to Snort, describing what it is, where it came from, and its architecture. It also covers Snort addons, deployment options, rule categories and options, and concludes with a brief overview of the open source host-based intrusion detection system OSSEC.
Introduction to SSH

The document provides an overview of SSH (Secure Shell), including what it is, its history and architecture, how to install and configure it, use public-key authentication and agent forwarding, and set up port forwarding tunnels. SSH allows securely executing commands, transferring files, and accessing systems behind firewalls.
Sniffing in a Switched Network

The document provides instructions for using ARP spoofing to intercept network traffic between a switch and remote network administrators. It describes using Ettercap to spoof the ARP tables of the switch and routers, and Ethereal to sniff the traffic, in order to capture the telnet credentials used to access the switch. The goal is to gain unauthorized access to the main company switch by sniffing the network traffic and obtaining the admin password.
Netscreen Policy Based Routing

Policy-based routing (PBR) on Juniper NetScreen firewalls allows routing decisions to be based on various packet attributes like source/destination addresses, ports, and protocols. This provides flexibility to redirect traffic in different ways, such as sending all HTTP traffic through a transparent proxy server or distributing traffic across multiple internet connections. The configuration involves creating extended ACLs to match traffic, match groups to group ACLs, action groups to define routing actions, policies to combine matches and actions, and binding policies to interfaces or virtual routers. Keeping PBR configurations simple and leaving room for future policies is recommended.
DRAFT Internet and world wide web protocol ; pu t ty ; telnet ; wireshark

This document discusses internet protocols including web browsers, web servers, IP addresses, DNS, HTTP, TCP, UDP, TCP/IP, RIP, OSPF, and ICMP. It compares Telnet and SSH protocols, noting that SSH is more secure since it runs on port 22, uses encryption, and is difficult to decrypt, while Telnet is not secure. The document also mentions network analysis tools PuTTy, Telnet, and Wireshark but does not provide details about them.
Team 5 presentation

Rlogin, Telnet, and SSH are remote access protocols. Rlogin and Telnet transmit information in plaintext, posing security risks, while SSH uses cryptography to secure connections. SSH was developed in 1995 as a more secure replacement for insecure remote shells like Rlogin and Telnet. SSH provides secure login, file transfer, and process execution between computers using encryption techniques like public-key authentication and symmetric encryption.
Network Penetration Testing Toolkit - Nmap, Netcat, and Metasploit Basics

Learn the basics of network penetration testing success - an introduction to the top three tools that will help you on your security journey: Nmap, Netcat, and Metasploit. See how to use Nmap both for port scanning and vulnerability discovery. You'll also learn how to use Netcat to grab banners, make HTTP requests, and create both reverse and bind shells. Finally, we’ll learn the ins and outs of Metasploit, including how to integrate our Nmap scan results for even more ownage and using the built-in exploits to get shells.
At the end of this, you will be port scanning, creating payloads, and popping shells. This technical workshop is designed to familiarize you with the necessary tools to continue your ethical hacking journey. From here, take your l33t new skillz and apply them to Capture The Flag (CTF) competitions or scanning your home network for vulnerabilities.
(This was originally presented on February 22, 2010 at Day of Shecurity Boston 2019).
Nmap commands

Nmap is a security scanning tool used to discover hosts and services on a computer network. It sends specially crafted packets to target hosts and analyzes the responses to perform functions like host discovery, port scanning, version detection, and operating system detection. The document provides 20 examples of Nmap commands, such as commands to scan a single host or IP address, scan multiple addresses or ranges, perform specific scans like OS detection or version detection, and save scan output to files.
Mobile Application Security Testing (Static Code Analysis) of Android App

This document discusses three angles for performing mobile application security testing: client side checks, dynamic/runtime checks of local storage, databases and more, and static code analysis. It focuses on static code analysis, explaining that it covers over 50% of the OWASP Mobile Top 10 risks. It provides details on fetching APKs, converting them to source code, manual and automated static code analysis tools like MobSF and QARK, and common issues like improper use of Android intents that can be discovered through static analysis.
The End of Anonymity on Anonymous Networks

The problem of user de-anonymization on the Darknet becomes more and more popular. The report will cover a variety of exploits for vulnerabilities in .onion resources and configuration flaws that can be utilized to obtain information on Tor users.
More Related Content
What's hot
Nmap and metasploitable

This was presented in Null Open Security community july meetup, Session was on Nmap and metasploitable
Security Onion Advance

This document provides an overview and comparison of Suricata and Snort intrusion detection systems. It discusses features like performance, rule writing, and capabilities. PF_ring and netsniff-ng are introduced as tools for improving packet capture speed. The document also demonstrates how to write Snort rules specifying actions, protocols, IP addresses, ports, directions and other options.
Recon with Nmap 

The document discusses using Nmap to perform network scanning and reconnaissance. It provides an overview of Nmap, describing common scan types like TCP and UDP scans. It also covers useful Nmap options for tasks like service and operating system detection. The document demonstrates the Nmap Scripting Engine for tasks like vulnerability scanning and brute force attacks. It provides examples of commands for different scan types and scripts.
BlueHat v17 || TLS 1.3 - Full speed ahead... mind the warnings - the great, t...

BlueHat v17 || TLS 1.3 - Full speed ahead... mind the warnings - the great, t...BlueHat Security Conference
Joseph Salowey, Tableau Software
Transport Layer Security (TLS) 1.3 is almost here. The protocol that protects most of the Internet secure connections is getting the biggest ever revamp, and is losing a round-trip. We will explore differences between TLS 1.3 and previous versions in detail, focusing on the performance and security improvements of the new protocol as well as some of the challenges we face around securely implementing new features such as 0-RTT resumption.
N map presentation

Nmap is a security scanning tool that can discover open ports, scan for services, and determine operating systems on a network. It works by sending packets to IP addresses and analyzing the responses to infer information about the target system, such as which ports are open or closed and what services are running. Nmap displays this information to the user and can be run from both graphical and command line interfaces on many operating systems. While useful for security auditing, Nmap could also enable hacking if used without permission on a network.
SSH Tunneling Recipes

This document provides recipes and explanations for using SSH tunneling techniques. SSH tunneling allows creating encrypted tunnels through an SSH connection to securely access services, bypass firewalls and censorship, and forward X11 applications. It discusses local and remote port forwarding, dynamic SOCKS proxying, and tools like autossh and sslh. Common uses of SSH tunneling include securely accessing services on insecure networks, circumventing censorship, opening firewall ports dynamically through port knocking, and forwarding graphical X11 applications remotely.
NMap

Nmap (Network Mapper} is and an Open Source utility which can quickly scan broad ranges of devices and provide valuable information about the devices on your network.It can be used for IT auditing and asset discovery as well as security profiling of the network.
CNIT 50: 6. Command Line Packet Analysis Tools

This document provides an overview of 6 command line packet analysis tools used for network security monitoring: Tcpdump, Dumpcap, Tshark, Argus, the Argus Ra client, and Argus Racluster. It describes what each tool is used for, basic syntax and examples of using filters to view specific traffic like ICMP, DNS, TCP handshakes. It also covers running these tools from the command line, reading captured packet files, and examining Argus session data files.
Penetration Testing Boot CAMP

The document provides instructions on how to configure an SSH server on Linux, perform footprinting and reconnaissance, scanning tools and techniques, enumeration tools and techniques, password cracking techniques and tools, privilege escalation methods, and keylogging and hidden file techniques. It discusses active and passive footprinting, Nmap port scanning, NetBIOS and SNMP enumeration, Windows password hashes, the sticky keys method for privilege escalation, ActualSpy keylogging software, and hiding files using NTFS alternate data streams. Countermeasures for many of these techniques are also outlined.
NMAP

Nmap is a network exploration tool that collects information about target hosts including open ports, services, OS detection, and running scripts. It offers various host discovery techniques like ICMP ping, TCP and UDP ping to find active systems on the network. Once hosts are identified, nmap performs port scanning using TCP SYN, ACK, and UDP scans to determine open and closed ports. It can also detect services, versions, and OS on each host. Nmap scripts provide additional information gathering capabilities for vulnerabilities and exploits.
Wireless security beyond password cracking by Mohit Ranjan

Network attacks in wired Lan environments
Protection in wired Lan
Layout of modern networks ( wired + wireless )
Difference between wired and wireless security
Most powerful situation to acquire in any network
Wireless attacks
Why NTP ?
Captive portal attacks
Conclusion and some wild thoughts
For complete data to perform this attack please go to the Github link below:
https://github.com/mohitrajain/Wireless_security_beyond_password_cracking
Netcat - A Swiss Army Tool

Netcat, also known as the Swiss Army knife of networking tools, can be used for various purposes including creating chat servers, serving web pages, port scanning, file transfers, and obtaining remote shells. The document discusses different versions of Netcat, provides examples of using Netcat for these tasks, and notes some security disadvantages when using it without encryption. Key topics covered include creating a basic chat server and web server, using Netcat for port scanning and file transfers, and obtaining a remote Windows command shell, although this last use raises security concerns.
Snort by SecArmour

This document discusses different types of intrusion detection systems including network intrusion detection systems like Snort, host intrusion detection systems like OSSEC, and distributed intrusion detection systems. It provides an introduction to Snort, describing what it is, where it came from, and its architecture. It also covers Snort addons, deployment options, rule categories and options, and concludes with a brief overview of the open source host-based intrusion detection system OSSEC.
Introduction to SSH

The document provides an overview of SSH (Secure Shell), including what it is, its history and architecture, how to install and configure it, use public-key authentication and agent forwarding, and set up port forwarding tunnels. SSH allows securely executing commands, transferring files, and accessing systems behind firewalls.
Sniffing in a Switched Network

The document provides instructions for using ARP spoofing to intercept network traffic between a switch and remote network administrators. It describes using Ettercap to spoof the ARP tables of the switch and routers, and Ethereal to sniff the traffic, in order to capture the telnet credentials used to access the switch. The goal is to gain unauthorized access to the main company switch by sniffing the network traffic and obtaining the admin password.
Netscreen Policy Based Routing

Policy-based routing (PBR) on Juniper NetScreen firewalls allows routing decisions to be based on various packet attributes like source/destination addresses, ports, and protocols. This provides flexibility to redirect traffic in different ways, such as sending all HTTP traffic through a transparent proxy server or distributing traffic across multiple internet connections. The configuration involves creating extended ACLs to match traffic, match groups to group ACLs, action groups to define routing actions, policies to combine matches and actions, and binding policies to interfaces or virtual routers. Keeping PBR configurations simple and leaving room for future policies is recommended.
DRAFT Internet and world wide web protocol ; pu t ty ; telnet ; wireshark

This document discusses internet protocols including web browsers, web servers, IP addresses, DNS, HTTP, TCP, UDP, TCP/IP, RIP, OSPF, and ICMP. It compares Telnet and SSH protocols, noting that SSH is more secure since it runs on port 22, uses encryption, and is difficult to decrypt, while Telnet is not secure. The document also mentions network analysis tools PuTTy, Telnet, and Wireshark but does not provide details about them.
Team 5 presentation

Rlogin, Telnet, and SSH are remote access protocols. Rlogin and Telnet transmit information in plaintext, posing security risks, while SSH uses cryptography to secure connections. SSH was developed in 1995 as a more secure replacement for insecure remote shells like Rlogin and Telnet. SSH provides secure login, file transfer, and process execution between computers using encryption techniques like public-key authentication and symmetric encryption.
Network Penetration Testing Toolkit - Nmap, Netcat, and Metasploit Basics

Learn the basics of network penetration testing success - an introduction to the top three tools that will help you on your security journey: Nmap, Netcat, and Metasploit. See how to use Nmap both for port scanning and vulnerability discovery. You'll also learn how to use Netcat to grab banners, make HTTP requests, and create both reverse and bind shells. Finally, we’ll learn the ins and outs of Metasploit, including how to integrate our Nmap scan results for even more ownage and using the built-in exploits to get shells.
At the end of this, you will be port scanning, creating payloads, and popping shells. This technical workshop is designed to familiarize you with the necessary tools to continue your ethical hacking journey. From here, take your l33t new skillz and apply them to Capture The Flag (CTF) competitions or scanning your home network for vulnerabilities.
(This was originally presented on February 22, 2010 at Day of Shecurity Boston 2019).
Nmap commands

Nmap is a security scanning tool used to discover hosts and services on a computer network. It sends specially crafted packets to target hosts and analyzes the responses to perform functions like host discovery, port scanning, version detection, and operating system detection. The document provides 20 examples of Nmap commands, such as commands to scan a single host or IP address, scan multiple addresses or ranges, perform specific scans like OS detection or version detection, and save scan output to files.
What's hot (20)
BlueHat v17 || TLS 1.3 - Full speed ahead... mind the warnings - the great, t...

BlueHat v17 || TLS 1.3 - Full speed ahead... mind the warnings - the great, t...
Wireless security beyond password cracking by Mohit Ranjan

Wireless security beyond password cracking by Mohit Ranjan
DRAFT Internet and world wide web protocol ; pu t ty ; telnet ; wireshark

DRAFT Internet and world wide web protocol ; pu t ty ; telnet ; wireshark
Network Penetration Testing Toolkit - Nmap, Netcat, and Metasploit Basics

Network Penetration Testing Toolkit - Nmap, Netcat, and Metasploit Basics
Viewers also liked
Mobile Application Security Testing (Static Code Analysis) of Android App

This document discusses three angles for performing mobile application security testing: client side checks, dynamic/runtime checks of local storage, databases and more, and static code analysis. It focuses on static code analysis, explaining that it covers over 50% of the OWASP Mobile Top 10 risks. It provides details on fetching APKs, converting them to source code, manual and automated static code analysis tools like MobSF and QARK, and common issues like improper use of Android intents that can be discovered through static analysis.
The End of Anonymity on Anonymous Networks

The problem of user de-anonymization on the Darknet becomes more and more popular. The report will cover a variety of exploits for vulnerabilities in .onion resources and configuration flaws that can be utilized to obtain information on Tor users.
Touring the Dark Side of Internet: A Journey through IOT, TOR & Docker

With the advent of IOT, Every 'Thing' is getting Smart, starting from the range of smartwatches, smart refrigerators, smart bulbs to smart car, smart healthcare, smart agriculture, smart retail, smart city and what not, even smart planet. But why is every thing getting smart? People are trying to bridge the gap between Digital World & Physical World by means of ubiquitous connectivity to Internet, and when digital things become physical, digital threats also become physical threats. Security & Privacy issues are rising as never before. What if the microphone in your smart TV can be used to eavesdrop the private communications in your bed room? What if a smart driverless car deliberately crashes itself into an accident? What if you want to be Anonymous over Internet and don't want anybody to track you?
This talk will focus on answering the above questions with a view on 'What are we currently doing to protect ourselves' and 'What we need to do'. What are the new security challenges that are coming up and how privacy & anonymity is taking the lead over security. The talk will also sensitive the audience about the paradigm shift that is happening in IOT DevOps, with help of Docker Containers and how they can be anonymised using TOR.
Tor network seminar by 13504 

The document provides an overview of the Tor network, which aims to enable anonymous communication on the internet. It discusses why anonymity is needed, how the Tor network works using onion routing and circuits of routers to hide a user's location and identity, limitations of Tor including slow speeds and vulnerability of exit nodes, licit and illicit uses of Tor for privacy and censorship circumvention as well as illegal activities, and dangers of using Tor including surveillance risks. It concludes that research has made progress on anonymous communication and public interest in privacy tools like Tor is likely to increase.
Anonymizing Networks

This document discusses different types of anonymous networks and how they provide anonymity for internet users. It introduces mix networks, peer-to-peer networks and other approaches that aim to hide a user's identity and communications. The document outlines various anonymous network architectures including centralized high-latency systems, centralized low-latency systems, and distributed/pseudo-distributed networks. It also discusses some of the challenges of providing anonymity including various attack approaches adversaries may use to try and de-anonymize networks.
Onion protocol

Onion routing is a technique for anonymous communication over a computer network. In an onion network, messages are encapsulated in layers of encryption, analogous to layers of an onion. The encrypted data is transmitted through a series of network nodes called onion routers, each of which "peels" away a single layer, uncovering the data's next destination. When the final layer is decrypted, the message arrives at its destination. The sender remains anonymous because each intermediary knows only the location of the immediately preceding and following nodes.
Onion routing was developed in the mid-1990s at the U.S. Naval Research to protect U.S. intelligence communications online. It was further developed by the Defence Advanced Research Projects Agency (DARPA) and patented by the Navy in 1998. Onion Routing is implemented The Onion Routing project or TOR project.
Tor Pivoting Networks Share 

The document summarizes Tor (The Onion Routing), an anonymizing network that allows users to improve their privacy and security on the Internet. Tor works by routing traffic through several volunteer servers run by others around the world, hiding a user's location and usage from anyone conducting network surveillance or traffic analysis. It enables a wide range of uses including circumventing censorship, protecting government communications, and allowing dissidents and journalists to communicate more safely.
Onion routing and tor: Fundamentals and Anonymity

Onion Routing and Tor: Fundamentals and anonymity discusses anonymity on the internet and how Tor works to provide anonymity. It explains that traditional IP addresses and browser tracking can be linked to a user's identity. Tor creates circuits through multiple relay nodes to hide a user's location and communications. Key features of Tor include using volunteer-run relay nodes, protecting against traffic analysis, and enabling hidden services to host anonymous websites. While Tor enhances anonymity, it cannot prevent all timing attacks if the start and end of a user's traffic can be observed.
I2P and the Dark Web

I2P is an anonymous network layer that provides stronger privacy protections than Tor. It uses garlic routing, message bundling and end-to-end encryption over short-lived tunnels to obscure a user's location and activities. Sites hosted on I2P, called eepsites, can only be accessed by other users on the network. While smaller than Tor currently, I2P offers increased security through its fully distributed architecture with no centralized points of control or surveillance.
Introduction to anonymity network tor

This second-generation Onion Routing system addresses limitations in the original design by adding perfect forward secrecy, congestion control, directory servers, integrity checking, configurable exit policies, and a practical design for location-hidden services via rendezvous points. Tor works on the real-world Internet, requires no special privileges or kernel modifications, requires little synchronization or coordination between nodes, and provides a reasonable tradeoff between anonymity, usability, and efficiency.
Tor the onion router

Tor is an anonymous communication network that allows users to securely communicate on the internet without revealing their location or identity. It works by routing a user's communications through a series of relay servers run by volunteers all around the world, making it difficult to trace the origin or destination of the communications. Tor protects users' privacy and anonymity through its onion routing technique which encrypts and then randomly bounces communications through multiple nodes. While Tor provides anonymity, it can also be used for illegal activities which presents challenges for its widespread adoption and use.
Tor Presentation

Onion Routing (Tor) is an anonymity network that allows users to securely communicate on the internet without compromising their privacy. It works by routing traffic through several servers, making it impossible for observers to trace the connection back to the user. Tor is the most widely used implementation of the Onion Routing design and improves upon the original design by allowing any server along the circuit to act as an exit point, making it harder to determine where traffic originated. Individuals, organizations, and governments all use Tor to keep communications private.
TOR NETWORK

This seminar discuss about the TOR BROWSER NETWORK TECHNOLOGY. The discussion includes, How it works, its weakness, its advantage, hidden services, about anonymity etc.
Data collection methods

Secondary data refers to data that has already been collected by someone else, while primary data is data that is collected by the researcher themselves. Some advantages of using secondary data include not having to reinvent the wheel, saving time and money, and the data may be very accurate if collected by a government agency. However, secondary data can be limited by being outdated, incomplete, or inconsistent over time. Primary data collection allows customizing data to specific research questions but is more time consuming and expensive. Researchers must determine if their question can be answered by existing secondary data or requires new primary data collection.
Research tools & data collection method_vipin

data collection method-
it include following sub points-
1) definition of research tool
2) data
3) primary and secondary data
4) observation method
5) interview
6) questionnaire
7) physiological measure
Big Data - 25 Amazing Facts Everyone Should Know

Here are 25 eye-opening facts about the phenomenon we call Big Data. Together they illustrate how much of a game-changer Big Data is.
Viewers also liked (16)
Mobile Application Security Testing (Static Code Analysis) of Android App

Mobile Application Security Testing (Static Code Analysis) of Android App
Touring the Dark Side of Internet: A Journey through IOT, TOR & Docker

Touring the Dark Side of Internet: A Journey through IOT, TOR & Docker
Similar to Anonymous Security Scanning and Browsing
Meek and domain fronting public

This document discusses Meek and domain fronting as techniques for circumventing internet censorship. It provides an overview of censorship tools and the arms race between censors and circumvention methods. Meek uses domain fronting to hide proxy traffic by making encrypted requests to CDNs like Google and Cloudflare that appear as normal traffic, making the connections difficult for censors to block without blocking major sites. Meek has been implemented in tools like Psiphon and Tor to provide uncensorable access by tunneling their protocols over domain-fronted connections. While attacks from deep packet inspection are possible, Meek has so far proven very effective at evading censorship.
Penetration Testing Services Technical Description Cyber51

This document describes the methodology for conducting network penetration tests and web application penetration tests. For network penetration tests, it involves footprinting, scanning and enumeration, vulnerability analysis, exploitation, and reporting. The goal is to identify security vulnerabilities in the network that could be exploited by hackers. For web application tests, it analyzes the application's configuration, authentication, session management, authorization, data validation, web services, and produces a report of findings and recommendations. The overall goal is to evaluate the security of networks and web applications and provide remedies to identified vulnerabilities.
osint + python: extracting information from tor network and darkweb 

The talk will start explaining how Tor project can help us to the research and development of tools for online anonymity and privacy of its users while surfing the Internet, by establishing virtual circuits between the different nodes that make up the Tor network. Later, we will review main tools for discover hidden services in tor network with osint tools. Finally we will use python for extracting information from tor network with specific modules like stem https://stem.torproject.org/
These could be the main points of the talk:
- Introduction to Tor project and hidden services
- Discovering hidden services with osint tools
- Extracting information from tor network with python
TOR... ALL THE THINGS

The global Tor network and its routing protocols provide an excellent framework for online anonymity. However, the selection of Tor-friendly software for Windows is sub-par at best.
Want to anonymously browse the web? You’re stuck with Firefox, and don’t even think about trying to anonymously use Flash. Want to dynamically analyze malware without letting the C2 server know your home IP address? You’re outta luck. Want to anonymously use any program that doesn’t natively support SOCKS or HTTP proxying? Not gonna happen.
While some solutions currently exist for generically rerouting traffic through Tor, these solutions either don’t support Windows, or can be circumvented by malware, or require an additional network gateway device.
Missed the live session at Black Hat USA 2013? Check out the slides from Jason Geffner's standing room only presentation! Jason released a free new CrowdStrike community tool to securely, anonymously, and transparently route all TCP/IP and DNS traffic through Tor, regardless of the client software, and without relying on VPNs or additional hardware or virtual machines.
Darknet

This document discusses various topics related to anonymity on darknets including:
- Ways enterprises bypass data leakage prevention including encryption and VPNs
- Differences between proxies, Tor, and VPNs and why Tor provides more anonymity
- Options for maximum anonymity hosting and WikiLeaks platforms on darknets
- Using open Wi-Fis or custom configurations as darknet exit nodes
- Digital currencies and tools like OpenTransactions that allow untraceable transactions
- Decentralized portal systems like Osiris and peer-to-peer networks for private file sharing and chat
- The relationship between encryption, anonymity, and enabling free speech
Network security basics

This document provides an overview of basic network security concepts. It discusses what security is, why we need it, who is vulnerable, and common security attacks like denial of service attacks, TCP attacks, packet sniffing, and their countermeasures. It also covers firewalls and intrusion detection systems, explaining what they are used for and how they help address security issues. The document uses examples to illustrate concepts like how firewall rules work and how packet sniffing, man-in-the-middle attacks, and dictionary attacks exploit vulnerabilities.
501 ch 3 network technologies tools

This chapter reviews basic networking concepts like protocols, ports, and network devices. It discusses how switches prevent flooding attacks and use protocols like STP. Routers are covered, including how they route traffic and use ACLs to filter traffic. Firewalls are also summarized, including the differences between stateful and stateless configurations and how firewall rules work. Network segmentation methods like DMZs, proxies, and VLANs are also introduced.
Nmap project presentation : Unlocking Network Secrets: Mastering Port Scannin...

Nmap project presentation : Unlocking Network Secrets: Mastering Port Scannin...Boston Institute of Analytics
Empower yourself to see what's lurking on your network with our Nmap project presentation! This presentation delves into the world of port scanning with Nmap, the industry-standard tool. Explore how Nmap works, uncover different scanning techniques (SYN scan, UDP scan, etc.), and learn to identify open ports, potential vulnerabilities, and running services. Whether you're a network administrator, security professional, or simply curious about your network traffic, this presentation equips you with the skills to gain valuable insights into your network health. Visit us for more nmap project presentations, https://bostoninstituteofanalytics.org/cyber-security-and-ethical-hacking/ Setting Up .Onion Addresses for your Enterprise, v3.5

Onion networking provides an alternative to traditional IP networking by using self-authenticating onion addresses and circuits through the Tor network. Some key aspects of onion networking include:
1) It establishes circuits between clients and servers to transport TCP connections, similar to how IP uses frames and MAC addresses.
2) Onion addresses resolve to introduction points that introduce circuits to rendezvous points for communication, providing redundancy and avoiding single points of failure.
3) While slower than traditional networking due to additional hops, onion networking provides benefits like built-in anonymity, censorship resistance, and lack of single points of control due to its distributed nature.
wireshark

What is Wireshark?
Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communication protocol development, and education.
Wireshark perhaps one of the best open source packet analyzer available for Windows and LINX
Some Important Purpose
Network Administrator used for troubleshoot network problem.
Network security engineer used for examine security problem.
Developer used for debug protocol implementation.
People used for learn protocol protocol internals.
Proxy servers

Proxy servers sit between an internal network and an external network. They act as an intermediary for requests from the internal users to hide their IP addresses and improve security. Proxy servers terminate TCP connections, caching frequently requested files to improve performance, and can filter content to enforce security policies. They provide anonymity and security for internal users while allowing access to external networks and resources.
Chap 1 Network Theory & Java Overview

This document provides an overview and introduction to network theory and Java programming. It discusses key topics like network communication models (OSI and TCP/IP), protocols, ports, sockets, firewalls, proxies, and an overview of Java. The document also provides code samples for basic Java socket programming including using ServerSocket for servers and Socket for clients. It explains concepts like connection-oriented and connectionless sockets in UDP and TCP. The objective is to help readers understand network environments and be able to develop basic networking applications in Java.
Security attacks

The document discusses network security vulnerabilities like spoofing and flooding attacks. It covers denial of service (DoS) and distributed denial of service (DDoS) attacks. Firewalls like packet filters and proxies are introduced as a way to limit network access and inspect traffic according to security policies. Intrusion detection systems (IDS) are also mentioned for detecting intrusions through signatures or anomalies.
Network Penetration Testing

The Slides deck contains Network penetration testing requirements & Tools used in real world pentesting. For Demo purposes, I had used a vulnhub machine called Metasploitable 2 for testing purposes. Looking into various Ports and Services Vulnerabilities using Kali open source tools.
CNIT 121: 9 Network Evidence

Slides for a college course based on "Incident Response & Computer Forensics, Third Edition" by by Jason Luttgens, Matthew Pepe, and Kevin Mandia.
Teacher: Sam Bowne
Twitter: @sambowne
Website: https://samsclass.info/121/121_F16.shtml
Shmoocon Epilogue 2013 - Ruining security models with SSH

This document summarizes how SSH can be used to compromise security in several ways:
1. Authentication can be bypassed by generating a public key on an attacker's machine and transferring it to a victim's machine to allow code execution without a password.
2. SSH allows file transfer and traffic tunneling which can be used to transfer tools, exfiltrate data, and bypass firewalls by tunneling any protocol over an SSH connection.
3. Dynamic tunneling with tools like SOCKS and Proxychains allows running scans, exploits, and other tools through an SSH connection without needing privileged access on the target.
CNIT 152: 9 Network Evidence 

Slides for a college course based on "Incident Response & Computer Forensics, Third Edition" by by Jason Luttgens, Matthew Pepe, and Kevin Mandia, at City College San Francisco.
Website: https://samsclass.info/152/152_F18.shtml
CNIT 152: 9 Network Evidence 

Slides for a college course based on "Incident Response & Computer Forensics, Third Edition" by by Jason Luttgens, Matthew Pepe, and Kevin Mandia, at City College San Francisco.
Website: https://samsclass.info/152/152_F18.shtml
Introduction to Tor

Tor is an anonymity network that allows users to browse the web anonymously. It works by routing traffic through a series of volunteer servers, or relays, that encrypt and then randomly route data in an attempt to make it untraceable. The Tor browser bundles this routing technology to allow users to access the open web as well as "hidden services" anonymously. While Tor provides anonymity, it has some weaknesses including potential traffic analysis of autonomous systems and exit node eavesdropping. The presentation provides an overview of how Tor works and relays, how to use Tor safely, and some common services found on Tor.
port forwarding.pptx

What is port forwarding used for?
Port forwarding, also known as port management, allows remote servers and devices on the internet to be able to access devices that are on a private network. If you are not using port forwarding, only devices on that private internal network can have access to each other or your network.
Similar to Anonymous Security Scanning and Browsing (20)
Penetration Testing Services Technical Description Cyber51

Penetration Testing Services Technical Description Cyber51
osint + python: extracting information from tor network and darkweb 

osint + python: extracting information from tor network and darkweb
Nmap project presentation : Unlocking Network Secrets: Mastering Port Scannin...

Nmap project presentation : Unlocking Network Secrets: Mastering Port Scannin...
Setting Up .Onion Addresses for your Enterprise, v3.5

Setting Up .Onion Addresses for your Enterprise, v3.5
Shmoocon Epilogue 2013 - Ruining security models with SSH

Shmoocon Epilogue 2013 - Ruining security models with SSH
Recently uploaded
一比一原版新西兰林肯大学毕业证(Lincoln毕业证书)学历如何办理

原版办【微信号:95270640】【新西兰林肯大学毕业证(Lincoln毕业证书)】【微信号:95270640】《成绩单、外壳、雅思、offer、真实留信官方学历认证(永久存档/真实可查)》采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【我们承诺采用的是学校原版纸张(纸质、底色、纹路)我们拥有全套进口原装设备,特殊工艺都是采用不同机器制作,仿真度基本可以达到100%,所有工艺效果都可提前给客户展示,不满意可以根据客户要求进行调整,直到满意为止!】
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信号95270640】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信号95270640】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
留信网服务项目:
1、留学生专业人才库服务(留信分析)
2、国(境)学习人员提供就业推荐信服务
3、留学人员区块链存储服务
【关于价格问题(保证一手价格)】
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:客户在留信官方认证查询网站查询到认证通过结果后付款,不成功不收费!
Securing BGP: Operational Strategies and Best Practices for Network Defenders...

Md. Zobair Khan,
Network Analyst and Technical Trainer at APNIC, presented 'Securing BGP: Operational Strategies and Best Practices for Network Defenders' at the Phoenix Summit held in Dhaka, Bangladesh from 23 to 24 May 2024.
How to make a complaint to the police for Social Media Fraud.pdf

How to make a complaint to the police for Social Media Fraud.pdf
一比一原版(uc毕业证书)加拿大卡尔加里大学毕业证如何办理

原版一模一样【微信:741003700 】【(uc毕业证书)加拿大卡尔加里大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
办理(uc毕业证书)加拿大卡尔加里大学毕业证【微信:741003700 】外观非常简单,由纸质材料制成,上面印有校徽、校名、毕业生姓名、专业等信息。
办理(uc毕业证书)加拿大卡尔加里大学毕业证【微信:741003700 】格式相对统一,各专业都有相应的模板。通常包括以下部分:
校徽:象征着学校的荣誉和传承。
校名:学校英文全称
授予学位:本部分将注明获得的具体学位名称。
毕业生姓名:这是最重要的信息之一,标志着该证书是由特定人员获得的。
颁发日期:这是毕业正式生效的时间,也代表着毕业生学业的结束。
其他信息:根据不同的专业和学位,可能会有一些特定的信息或章节。
办理(uc毕业证书)加拿大卡尔加里大学毕业证【微信:741003700 】价值很高,需要妥善保管。一般来说,应放置在安全、干燥、防潮的地方,避免长时间暴露在阳光下。如需使用,最好使用复印件而不是原件,以免丢失。
综上所述,办理(uc毕业证书)加拿大卡尔加里大学毕业证【微信:741003700 】是证明身份和学历的高价值文件。外观简单庄重,格式统一,包括重要的个人信息和发布日期。对持有人来说,妥善保管是非常重要的。
怎么办理(umiami毕业证书)美国迈阿密大学毕业证文凭证书实拍图原版一模一样

原版定制【微信:bwp0011】《(umiami毕业证书)美国迈阿密大学毕业证文凭证书》【微信:bwp0011】成绩单 、雅思、外壳、留信学历认证永久存档查询,采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【微信bwp0011】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【微信bwp0011】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
【关于价格问题(保证一手价格)】
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
HijackLoader Evolution: Interactive Process Hollowing

CrowdStrike researchers have identified a HijackLoader (aka IDAT Loader) sample that employs sophisticated evasion techniques to enhance the complexity of the threat. HijackLoader, an increasingly popular tool among adversaries for deploying additional payloads and tooling, continues to evolve as its developers experiment and enhance its capabilities.
In their analysis of a recent HijackLoader sample, CrowdStrike researchers discovered new techniques designed to increase the defense evasion capabilities of the loader. The malware developer used a standard process hollowing technique coupled with an additional trigger that was activated by the parent process writing to a pipe. This new approach, called "Interactive Process Hollowing", has the potential to make defense evasion stealthier.
快速办理(新加坡SMU毕业证书)新加坡管理大学毕业证文凭证书一模一样

学校原件一模一样【微信:741003700 】《(新加坡SMU毕业证书)新加坡管理大学毕业证文凭证书》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Bengaluru Dreamin' 24 - Personal Branding

Session on Personal Branding presented at Bengaluru Dreamin
快速办理(Vic毕业证书)惠灵顿维多利亚大学毕业证完成信一模一样

学校原件一模一样【微信:741003700 】《(Vic毕业证书)惠灵顿维多利亚大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Honeypots Unveiled: Proactive Defense Tactics for Cyber Security, Phoenix Sum...

Adli Wahid, Senior Internet Security Specialist at APNIC, delivered a presentation titled 'Honeypots Unveiled: Proactive Defense Tactics for Cyber Security' at the Phoenix Summit held in Dhaka, Bangladesh from 23 to 24 May 2024.
Recently uploaded (11)
Securing BGP: Operational Strategies and Best Practices for Network Defenders...

Securing BGP: Operational Strategies and Best Practices for Network Defenders...
How to make a complaint to the police for Social Media Fraud.pdf

How to make a complaint to the police for Social Media Fraud.pdf
HijackLoader Evolution: Interactive Process Hollowing

HijackLoader Evolution: Interactive Process Hollowing
Honeypots Unveiled: Proactive Defense Tactics for Cyber Security, Phoenix Sum...

Honeypots Unveiled: Proactive Defense Tactics for Cyber Security, Phoenix Sum...
Anonymous Security Scanning and Browsing
- 1. Anonymous Scan Topics to be Covered • Why to be Anonymous – Scans and Browsing • What is TOR • Socks Proxy , DNS Leaks • Using TOR – Browser Level , Terminal (config) • Proxy chains ( config) • Using Nmap, nikto, burp with Tor
- 2. Why to be Anonymous • Privacy reasons – Citizens • Business need to keep Trade Secrets, Network security • Govt – for its security • Military, Law enforcement orgs needs anonymity to get their job done • Anonymity isn't cryptography, steganography Operating Systems and Applications leak your info
- 3. Info. Getting leaked via • Browser Plug-in, Cookies, Extensions, • Shockwave/Flash, Java, QuickTime and even PDF
- 4. TOR “The onion router” • online anonymity software and network • open source, freely available • active research environment Estimated 3,00,000 daily Tor users
- 5. Works on Relay Principle Each node knows only the previous hop and the next hop. No node in the path can discover the full path
- 6. • TOR uses Onion Routing • Onion Routing technique for anonymous communication over a network. • Messages are encapsulated in layers of encryption.
- 7. Socks Proxy • It’s a Protocol / Socks – Socket Secure • A SOCKS server is a general purpose proxy server that establishes a TCP connection to another server on behalf of a client
- 8. TOR Browser Level • Download TOR • Run
- 9. Steps to Install 1. Install TOR sudo apt-get install tor 2. Install proxychains sudo apt-get install proxychains 3. Open /etc/proxychains.conf & add [ProxyList] # add proxy here ... # meanwile # defaults set to "tor" socks4 127.0.0.1 9050
- 10. Start and Test TOR 1. sudo service tor start (llly, stop and restart) 2. sudo tor status (to check the status) 3. sudo proxychains firefox www.ipchicken.com
- 14. DNS Leaks • traffic leaks outside of the secure connection to the network • Under certain conditions, • OS will continue to use its default DNS servers instead of the anonymous DNS servers • Results in DNS Leaks
- 15. Nmap, nikto • sudo proxychains nmap -sT –PN < IP address> • sudo nikto proxychains <host> • For all command line scans…..
- 16. Scan on abc.com
- 17. IP belongs china’s ISP
- 18. Burp suite • Install TOR • Go to <OPTIONS> • Set SOCKS as 127.0.0.1 9050 • NOTE : – Proxy settings in foxy proxy and burp suite will same as 127.0.0.1 8080
