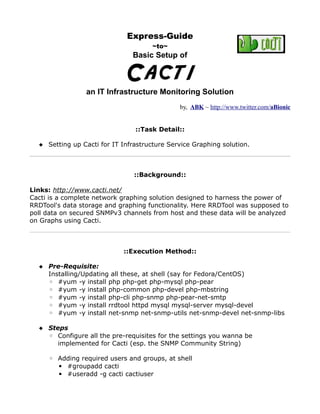
An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing
•
0 likes•1,195 views
It's an Express Guide to "Setup of Cacti Server with purpose of IT Infrastructure Monitoring & Service Graphs" ~~~~~ its aimed at monitoring of various IT services and brilliant graphing of statistics
Report
Share
Report
Share
Download to read offline
Recommended
Mikrotik Network Simulator (MUM Presentation Material 2013)

Rofiq Fauzi presented on creating a MikroTik network simulator using GNS3. He discussed how to install MikroTik RouterOS as a virtual machine using Qemu, add it to GNS3, and connect it to the host computer via a loopback interface to allow remote management. This allows testing of MikroTik features and network topologies without requiring physical hardware. Each additional MikroTik router added to GNS3 increases memory usage by approximately 80MB, allowing planning of resource requirements. Fauzi demonstrated the process and configuration steps to set up the simulator.
MTCNA - MikroTik Certified Network Associate - v2

MTCNA Outline
Module 1 : introduction
Module 2 : DHCP
Module 3 : Bridging
Module 4 : Routing
Module 5 : Wireless
Module 7 : QoS
Module 8 : Tunnels
Module 9 : Misc
Find me in :
https://www.instagram.com/yaser.rahmati
Running BGP with Mikrotik

Webinar topic: Running BGP with Mikrotik
Presenter: Achmad Mardiansyah
In this webinar series, We are discussing Running BGP with Mikrotik
Please share your feedback or webinar ideas here: http://bit.ly/glcfeedback
Check our schedule for future events: https://www.glcnetworks.com/schedule/
Follow our social media for updates: Facebook, Instagram, YouTube Channel, and telegram
The recording is available on Youtube
https://youtu.be/jqlz7C_Otv8
Mikro tik advanced training

Here are the steps to disable MAC-WinBox and MAC-Telnet on all interfaces except the local interface:
/ip service disable mac-telnet
/ip service disable mac-winbox interface=all
/ip service enable mac-winbox interface=local
This will disable MAC-Telnet on all interfaces and disable MAC-WinBox on all interfaces except the local interface, improving security as recommended.
VXLAN and FRRouting

Diskusi Networking V1 about Datacenter Networking, Open Hardware Trend, VXLAN and how to do it using open source software routing platform FRRouting
PPPoE With Mikrotik and Radius

How to manage internet clients of an ISP with PPPoE and MikroTik. For
centralized AAA (Authentication, Authorization and Accounting), freeRadius is used.
MikroTik & RouterOS

Marek Isalski, Faelix.net Ltd, describes the MikroTik range of routers and their applications, gives a pros and cons summary, and recommendations for budget provider edge deployment.
Ukk tkj p1 proxy mikrotik2014 2015

This document provides instructions for configuring a MikroTik router for a local area network (LAN) topology. It describes setting up the router interfaces, IP addresses, gateway, DNS, NAT firewall rules to allow clients to access the internet, and a proxy to block specific websites. The configuration is tested by checking if blocked sites like Facebook and YouTube result in an error page.
Recommended
Mikrotik Network Simulator (MUM Presentation Material 2013)

Rofiq Fauzi presented on creating a MikroTik network simulator using GNS3. He discussed how to install MikroTik RouterOS as a virtual machine using Qemu, add it to GNS3, and connect it to the host computer via a loopback interface to allow remote management. This allows testing of MikroTik features and network topologies without requiring physical hardware. Each additional MikroTik router added to GNS3 increases memory usage by approximately 80MB, allowing planning of resource requirements. Fauzi demonstrated the process and configuration steps to set up the simulator.
MTCNA - MikroTik Certified Network Associate - v2

MTCNA Outline
Module 1 : introduction
Module 2 : DHCP
Module 3 : Bridging
Module 4 : Routing
Module 5 : Wireless
Module 7 : QoS
Module 8 : Tunnels
Module 9 : Misc
Find me in :
https://www.instagram.com/yaser.rahmati
Running BGP with Mikrotik

Webinar topic: Running BGP with Mikrotik
Presenter: Achmad Mardiansyah
In this webinar series, We are discussing Running BGP with Mikrotik
Please share your feedback or webinar ideas here: http://bit.ly/glcfeedback
Check our schedule for future events: https://www.glcnetworks.com/schedule/
Follow our social media for updates: Facebook, Instagram, YouTube Channel, and telegram
The recording is available on Youtube
https://youtu.be/jqlz7C_Otv8
Mikro tik advanced training

Here are the steps to disable MAC-WinBox and MAC-Telnet on all interfaces except the local interface:
/ip service disable mac-telnet
/ip service disable mac-winbox interface=all
/ip service enable mac-winbox interface=local
This will disable MAC-Telnet on all interfaces and disable MAC-WinBox on all interfaces except the local interface, improving security as recommended.
VXLAN and FRRouting

Diskusi Networking V1 about Datacenter Networking, Open Hardware Trend, VXLAN and how to do it using open source software routing platform FRRouting
PPPoE With Mikrotik and Radius

How to manage internet clients of an ISP with PPPoE and MikroTik. For
centralized AAA (Authentication, Authorization and Accounting), freeRadius is used.
MikroTik & RouterOS

Marek Isalski, Faelix.net Ltd, describes the MikroTik range of routers and their applications, gives a pros and cons summary, and recommendations for budget provider edge deployment.
Ukk tkj p1 proxy mikrotik2014 2015

This document provides instructions for configuring a MikroTik router for a local area network (LAN) topology. It describes setting up the router interfaces, IP addresses, gateway, DNS, NAT firewall rules to allow clients to access the internet, and a proxy to block specific websites. The configuration is tested by checking if blocked sites like Facebook and YouTube result in an error page.
Mikrotik Hotspot With Queue Tree BW Management

The document discusses how to configure bandwidth management using queue trees on a Mikrotik router for a hotspot network. It provides steps to set up interfaces and IP addresses, enable masquerading and DNS, create hotspot user profiles with packet markings, configure firewall mangle rules for packet marking, and build a queue tree with bandwidth limits for different user groups and traffic directions. Screenshots are included to illustrate the hotspot user profile, mangle rules, and queue tree configurations.
PPPoE With Mikrotik and Radius

How to manage internet clients of an ISP with PPPoE and MikroTik. For
centralized AAA (Authentication, Authorization and Accounting), freeRadius is used.
Mikrotik Hotspot User Manager

This document provides instructions for setting up a Mikrotik hotspot with user management. It discusses configuring bridge and wireless interfaces, setting up a hotspot server and profile, installing the User Manager package to connect to RouterOS for user authentication, and creating bandwidth profiles, user profiles, and individual users. The network topology bridges the Ethernet and wireless interfaces for hotspot access. User Manager acts as a RADIUS server to limit bandwidth, time usage, and log users accessing the hotspot network.
Mikrotik Tutorial

A computer network connects computers together to share resources like internet access. A router receives and directs packets between networks and may convert between network types. The document then discusses configuring a MikroTik 951g-2hnd router by connecting it to a laptop, using Winbox software to add a WAN IP and default route, enable wireless and add a password, create a DHCP server, and configure NAT, NTP, and ports. Finally, the computer's IP is changed to automatic and ping tests are done to the Google DNS to confirm the basic router configuration.
Mikrotik

This document provides frequently asked questions about MikroTik RouterOS. It addresses questions about what RouterOS is, how to install and license it, how to configure features like networking, bandwidth management, wireless connectivity, and BGP routing. The document provides concise answers and instructions for tasks like upgrading RouterOS, recovering lost passwords, and troubleshooting common issues.
IPsec on Mikrotik

This document outlines an agenda for a webinar on IPsec on Mikrotik presented by GLC Networks. The agenda includes an introduction, reviewing basic networking and security concepts, discussing IPsec standards and how IPsec works on Mikrotik routers. It provides background on the presenter and invites attendees to introduce themselves. The document guides attendees on prerequisites and prepares them for a live demonstration and question/answer portion.
Mikrotik load balansing

This document provides information about load balancing techniques in networking. It discusses several types of load balancing including sub-packet load balancing using MLPPP, per-packet load balancing using bonding, per-connection load balancing using nth, per-address-pair load balancing using ECMP and PCC, custom load balancing using policy routing, and bandwidth-based load balancing using MPLS traffic engineering tunnels. It also provides examples and instructions for configuring various load balancing options in MikroTik RouterOS.
MikroTik BGP Security - MUM 2014 (rofiq fauzi)

The document discusses BGP security and routing protocols. It provides background on the presenter, Rofiq Fauzi, and his experience as a MikroTik consultant and certified trainer. The presentation covers BGP attacks like prefix hijacking and denial of service attacks. It also discusses interior gateway protocols (IGPs), autonomous systems (AS), and how to configure routing filters and detect false routing announcements to improve BGP security. Screenshots and a demo topology are provided to illustrate BGP concepts and potential attacks.
Open stack advanced_part

Openstack Networking Internals - Advanced Part
The pictures of the VNI were taken with the "Show my network state" tool
https://sites.google.com/site/showmynetworkstate/
MikroTik Basic Training Class - Online Moduls - English

This document provides an overview of an introductory training class on MikroTik router configuration. It discusses MikroTik's history as a router software and hardware manufacturer, the capabilities of their RouterOS software and RouterBoard hardware, and how to connect to and configure a MikroTik router using Winbox. The training covers topics like the MikroTik interface, network addressing, static and dynamic routing, and basic router management tools.
MikroTik Firewall : Securing your Router with Port Knocking

MikroTik Firewall : Securing your Router with Port KnockingAkbar Azwir, MM, PMP, PMI-SP, PSM I, CISSP
This presentation was presented at MUM Indonesia at Bali in 2008. Discussed about how to put extra layer of security into your MikroTik Router using Port Knocking mechanism.Openstack Networking Internals - first part

Openstack Networking Internals - first part
Description of the Virtual Network Infrastructure inside an OpenStack cluster
The pictures of the VNI were taken with the "Show my network state" tool
https://sites.google.com/site/showmynetworkstate/
OpenStack networking

This document provides an overview of OpenStack Networking (Neutron) and the different networking plugins and configurations available in Neutron. It discusses the Nova network manager, the Neutron OpenvSwitch plugin configured for VLAN and GRE tunneling modes, Neutron security groups, and Neutron's software defined networking capabilities. Diagrams and examples of packet flows are provided to illustrate how networks are logically and physically implemented using the different Neutron plugins.
NAT with ASA & ASA Security Context

The document discusses NAT and security contexts on an ASA firewall. It describes configuring NAT to translate internal networks to external IP addresses using a pool. It also describes configuring static NAT and port redirection. The document then discusses security contexts, which allow a single ASA to act as multiple virtual firewalls, with each context having its own interfaces, routing tables, and policies. It describes the system, admin, and logical contexts and differences between single and multiple mode.
Neutron: br-ex is now deprecated! what is modern way?

Usage of Neutron br-ex has been changed. Recommended is now to use br-int to connect to an external network.
Fools your enemy with MikroTik

With the emerging security threat nowadays, we should know how to detect and analyze every possible threat to your network.
Just with simple solution we could make our MikroTik to became a powerful tool to fool the hacker.
MikroTik as Low Interaction HoneyPot.
CCNA : Intro to Cisco IOS - Part 2

Webinar topic: CCNA : Intro to Cisco IOS
Presenter: Achmad Mardiansyah, M. Taufik Nurhuda
In this webinar series, CCNA : Intro to Cisco IOS
Please share your feedback or webinar ideas here: http://bit.ly/glcfeedback
Check our schedule for future events: https://www.glcnetworks.com/en/schedule/
Follow our social media for updates: Facebook, Instagram, YouTube Channel, and telegram also discord
Recording available on Youtube
https://youtu.be/uRDTRlslZtc
Workshop IPv6 APJII Jawa Barat 

Materi Workshop IPv6 yang di sampaikan pada event Asosiasi Penyelenggara Jasa Internet Indonesia Pengurus Wilayah Jawa Barat
http://jagonetwork.id
Multivendor MPLS L3VPN

- The document describes a small MPLS VPN network with multiple vendor PE routers (Mikrotik, Cisco, Juniper).
- There is a minor bug in Mikrotik's BGP-VPNv4 implementation where the Route Distinguisher is propagated in reverse order, but this does not cause issues.
- The network uses OSPF or BGP between the PE and CE routers to distribute routes for different VPNs with unique Route Distinguishers and Route Targets.
Wireless Developing Wireless Monitoring and Control devices

- Aidan Venn developed a system using Zabbix, Raspberry Pis, sensors, and actuators to remotely monitor and control 7 research and development sites to save energy, time, and money.
- Key objectives were to make the system scalable, have central control, be plug-and-play, have minimal overhead, be cost-effective, resilient, and prove the concept.
- Initial results showed 99% time savings from remote rebooting of frozen devices and energy savings from adjusting boiler temperatures based on sensor data.
- Challenges included passing macros to scripts for reusable commands and using macros in item keys for sensors.
Cacti desde-paquetes

Este documento proporciona una introducción a Cacti, una herramienta para monitorear el rendimiento y uso de recursos de redes y servidores. Cacti usa RRDtool para crear gráficos de datos históricos almacenados en archivos RRD. El documento explica cómo instalar y configurar Cacti, incluida la adición de dispositivos, la creación de plantillas de gráficos y la organización de nodos en un árbol jerárquico. También cubre conceptos clave como fuentes de datos, recop
Cacti

O documento descreve a ferramenta Cacti, que é um software livre para monitoramento de rede que coleta e armazena dados usando o RRDTool e gera gráficos. Ele explica como o Cacti funciona, os conceitos do RRDTool, fontes de dados, gráficos, gerenciamento de usuários e requisitos para instalação.
More Related Content
What's hot
Mikrotik Hotspot With Queue Tree BW Management

The document discusses how to configure bandwidth management using queue trees on a Mikrotik router for a hotspot network. It provides steps to set up interfaces and IP addresses, enable masquerading and DNS, create hotspot user profiles with packet markings, configure firewall mangle rules for packet marking, and build a queue tree with bandwidth limits for different user groups and traffic directions. Screenshots are included to illustrate the hotspot user profile, mangle rules, and queue tree configurations.
PPPoE With Mikrotik and Radius

How to manage internet clients of an ISP with PPPoE and MikroTik. For
centralized AAA (Authentication, Authorization and Accounting), freeRadius is used.
Mikrotik Hotspot User Manager

This document provides instructions for setting up a Mikrotik hotspot with user management. It discusses configuring bridge and wireless interfaces, setting up a hotspot server and profile, installing the User Manager package to connect to RouterOS for user authentication, and creating bandwidth profiles, user profiles, and individual users. The network topology bridges the Ethernet and wireless interfaces for hotspot access. User Manager acts as a RADIUS server to limit bandwidth, time usage, and log users accessing the hotspot network.
Mikrotik Tutorial

A computer network connects computers together to share resources like internet access. A router receives and directs packets between networks and may convert between network types. The document then discusses configuring a MikroTik 951g-2hnd router by connecting it to a laptop, using Winbox software to add a WAN IP and default route, enable wireless and add a password, create a DHCP server, and configure NAT, NTP, and ports. Finally, the computer's IP is changed to automatic and ping tests are done to the Google DNS to confirm the basic router configuration.
Mikrotik

This document provides frequently asked questions about MikroTik RouterOS. It addresses questions about what RouterOS is, how to install and license it, how to configure features like networking, bandwidth management, wireless connectivity, and BGP routing. The document provides concise answers and instructions for tasks like upgrading RouterOS, recovering lost passwords, and troubleshooting common issues.
IPsec on Mikrotik

This document outlines an agenda for a webinar on IPsec on Mikrotik presented by GLC Networks. The agenda includes an introduction, reviewing basic networking and security concepts, discussing IPsec standards and how IPsec works on Mikrotik routers. It provides background on the presenter and invites attendees to introduce themselves. The document guides attendees on prerequisites and prepares them for a live demonstration and question/answer portion.
Mikrotik load balansing

This document provides information about load balancing techniques in networking. It discusses several types of load balancing including sub-packet load balancing using MLPPP, per-packet load balancing using bonding, per-connection load balancing using nth, per-address-pair load balancing using ECMP and PCC, custom load balancing using policy routing, and bandwidth-based load balancing using MPLS traffic engineering tunnels. It also provides examples and instructions for configuring various load balancing options in MikroTik RouterOS.
MikroTik BGP Security - MUM 2014 (rofiq fauzi)

The document discusses BGP security and routing protocols. It provides background on the presenter, Rofiq Fauzi, and his experience as a MikroTik consultant and certified trainer. The presentation covers BGP attacks like prefix hijacking and denial of service attacks. It also discusses interior gateway protocols (IGPs), autonomous systems (AS), and how to configure routing filters and detect false routing announcements to improve BGP security. Screenshots and a demo topology are provided to illustrate BGP concepts and potential attacks.
Open stack advanced_part

Openstack Networking Internals - Advanced Part
The pictures of the VNI were taken with the "Show my network state" tool
https://sites.google.com/site/showmynetworkstate/
MikroTik Basic Training Class - Online Moduls - English

This document provides an overview of an introductory training class on MikroTik router configuration. It discusses MikroTik's history as a router software and hardware manufacturer, the capabilities of their RouterOS software and RouterBoard hardware, and how to connect to and configure a MikroTik router using Winbox. The training covers topics like the MikroTik interface, network addressing, static and dynamic routing, and basic router management tools.
MikroTik Firewall : Securing your Router with Port Knocking

MikroTik Firewall : Securing your Router with Port KnockingAkbar Azwir, MM, PMP, PMI-SP, PSM I, CISSP
This presentation was presented at MUM Indonesia at Bali in 2008. Discussed about how to put extra layer of security into your MikroTik Router using Port Knocking mechanism.Openstack Networking Internals - first part

Openstack Networking Internals - first part
Description of the Virtual Network Infrastructure inside an OpenStack cluster
The pictures of the VNI were taken with the "Show my network state" tool
https://sites.google.com/site/showmynetworkstate/
OpenStack networking

This document provides an overview of OpenStack Networking (Neutron) and the different networking plugins and configurations available in Neutron. It discusses the Nova network manager, the Neutron OpenvSwitch plugin configured for VLAN and GRE tunneling modes, Neutron security groups, and Neutron's software defined networking capabilities. Diagrams and examples of packet flows are provided to illustrate how networks are logically and physically implemented using the different Neutron plugins.
NAT with ASA & ASA Security Context

The document discusses NAT and security contexts on an ASA firewall. It describes configuring NAT to translate internal networks to external IP addresses using a pool. It also describes configuring static NAT and port redirection. The document then discusses security contexts, which allow a single ASA to act as multiple virtual firewalls, with each context having its own interfaces, routing tables, and policies. It describes the system, admin, and logical contexts and differences between single and multiple mode.
Neutron: br-ex is now deprecated! what is modern way?

Usage of Neutron br-ex has been changed. Recommended is now to use br-int to connect to an external network.
Fools your enemy with MikroTik

With the emerging security threat nowadays, we should know how to detect and analyze every possible threat to your network.
Just with simple solution we could make our MikroTik to became a powerful tool to fool the hacker.
MikroTik as Low Interaction HoneyPot.
CCNA : Intro to Cisco IOS - Part 2

Webinar topic: CCNA : Intro to Cisco IOS
Presenter: Achmad Mardiansyah, M. Taufik Nurhuda
In this webinar series, CCNA : Intro to Cisco IOS
Please share your feedback or webinar ideas here: http://bit.ly/glcfeedback
Check our schedule for future events: https://www.glcnetworks.com/en/schedule/
Follow our social media for updates: Facebook, Instagram, YouTube Channel, and telegram also discord
Recording available on Youtube
https://youtu.be/uRDTRlslZtc
Workshop IPv6 APJII Jawa Barat 

Materi Workshop IPv6 yang di sampaikan pada event Asosiasi Penyelenggara Jasa Internet Indonesia Pengurus Wilayah Jawa Barat
http://jagonetwork.id
Multivendor MPLS L3VPN

- The document describes a small MPLS VPN network with multiple vendor PE routers (Mikrotik, Cisco, Juniper).
- There is a minor bug in Mikrotik's BGP-VPNv4 implementation where the Route Distinguisher is propagated in reverse order, but this does not cause issues.
- The network uses OSPF or BGP between the PE and CE routers to distribute routes for different VPNs with unique Route Distinguishers and Route Targets.
Wireless Developing Wireless Monitoring and Control devices

- Aidan Venn developed a system using Zabbix, Raspberry Pis, sensors, and actuators to remotely monitor and control 7 research and development sites to save energy, time, and money.
- Key objectives were to make the system scalable, have central control, be plug-and-play, have minimal overhead, be cost-effective, resilient, and prove the concept.
- Initial results showed 99% time savings from remote rebooting of frozen devices and energy savings from adjusting boiler temperatures based on sensor data.
- Challenges included passing macros to scripts for reusable commands and using macros in item keys for sensors.
What's hot (20)
MikroTik Basic Training Class - Online Moduls - English

MikroTik Basic Training Class - Online Moduls - English
MikroTik Firewall : Securing your Router with Port Knocking

MikroTik Firewall : Securing your Router with Port Knocking
Neutron: br-ex is now deprecated! what is modern way?

Neutron: br-ex is now deprecated! what is modern way?
Wireless Developing Wireless Monitoring and Control devices

Wireless Developing Wireless Monitoring and Control devices
Viewers also liked
Cacti desde-paquetes

Este documento proporciona una introducción a Cacti, una herramienta para monitorear el rendimiento y uso de recursos de redes y servidores. Cacti usa RRDtool para crear gráficos de datos históricos almacenados en archivos RRD. El documento explica cómo instalar y configurar Cacti, incluida la adición de dispositivos, la creación de plantillas de gráficos y la organización de nodos en un árbol jerárquico. También cubre conceptos clave como fuentes de datos, recop
Cacti

O documento descreve a ferramenta Cacti, que é um software livre para monitoramento de rede que coleta e armazena dados usando o RRDTool e gera gráficos. Ele explica como o Cacti funciona, os conceitos do RRDTool, fontes de dados, gráficos, gerenciamento de usuários e requisitos para instalação.
CACTI herramienta de monitoreo

La instalación de CACTI en OpenSuse requiere 15 pasos que incluyen instalar paquetes requeridos, crear una base de datos MySQL para CACTI, importar datos de ejemplo, configurar el archivo config.php, agregar permisos a directorios, agregar una tarea cron, permitir acceso remoto a través de Apache, y configurar servicios y firewall para el acceso a la interfaz web de CACTI.
Nagios Conference 2011 - Tony Roman - Cacti Workshop

Tony Roman's workshop on Cacti. The workshop was given during the Nagios World Conference North America held Sept 27-29th, 2011 in Saint Paul, MN. For more information on the conference (including photos and videos), visit: http://go.nagios.com/nwcna
Cacti

Cacti es una herramienta que permite monitorizar y visualizar gráficas y estadísticas de dispositivos de red a través del protocolo SNMP. Recupera información de los dispositivos, almacena los datos usando RRDtool y los representa gráficamente, mostrando métricas como el mínimo, máximo y promedio. Requiere la instalación de Apache, PHP, MySQL, entre otros, y permite agregar dispositivos de forma manual para su supervisión.
Conference on Nagios: Reinhard Scheck on Cacti

Cacti is an open source, agentless monitoring and graphing tool based on RRDtool. It allows users to centrally monitor network devices, servers, applications and services through a web-based interface. Cacti uses templates to easily configure the monitoring of multiple devices of the same type. It also has a plugin architecture that extends its functionality. Some key features include fault, service level and performance monitoring, fast and scalable data collection, and support for hundreds of templates and plugins contributed by an active user community.
Cacti

Cacti is an open source software that uses RRDTool to graph and store time-series data from data sources like SNMP. It stores data in a MySQL database and uses PHP to provide a frontend interface for creating graphs, templates, and managing users. Cacti supports unlimited graph items, auto-padding, custom data gathering scripts, and SNMP to monitor network traffic and system metrics over time through graphs. It also provides features like data source templates, host templates, and user management to scale monitoring of large networks.
Cacti overview

Cacti is a front-end GUI for RRDtool that provides graphing and monitoring of data gathered by various plugins. It stores configuration and user data in MySQL and stores monitored device data in RRD files. Cacti includes polling capabilities via PHP or C-based plugins, and allows additional applications and data sources to be monitored through an extensible framework. It also has alerting functionality via the thold plugin. The MySQL plugin provides predefined monitoring templates for databases, servers, and applications.
Cacti presentation

Cacti is a front end for RRDtool that provides a web GUI for configuring RRDtool and organizing graphs. It stores administrative configuration data in MySQL and monitors device data in RRDs, providing a historical view. Cacti handles data gathering through polling and SNMP and allows creation of graphs and data sources. It also includes user management, alerting capabilities, and templating to scale to large numbers of data sources and graphs.
Viewers also liked (10)
Nagios Conference 2011 - Tony Roman - Cacti Workshop

Nagios Conference 2011 - Tony Roman - Cacti Workshop
Similar to An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing
Installing Cacti openSUSE Leap 42.1

This document provides instructions for installing and configuring Cacti on openSUSE Leap 42.1. It describes getting root access, adding repositories, installing required packages like MySQL and Cacti, configuring services, securing MySQL, configuring Apache and file permissions, creating the Cacti database, configuring Cacti, and completing the installation process in a web browser.
Install cacti on open suse 13

This document provides instructions for installing and configuring Cacti on openSUSE 13.2. It involves installing required packages, creating a MySQL database for Cacti, importing the Cacti database, configuring Cacti settings, changing file permissions, adding a cron job, enabling and restarting services, and completing the Cacti installation wizard. Finally, the Cacti dashboard is shown and additional documentation is provided.
AtlasCamp 2015 Docker continuous integration training

A 2-hour training session delivered at AtlasCamp in Prague, June 9th 2015.
* Docker vs virtual machines
* Docker concepts
* Docker for testing
* Automation with Docker Compose
* Continuous integration with Bamboo Docker support
* Extracting test results from Docker containers
* Continuous deployment with deployment environments
DeveloperWeek 2015: A Practical Introduction to Docker

Steve Smith gave a presentation on Docker and how it can be used for development and testing. He demonstrated how to build Docker images for Elasticsearch and Postgresql databases. Fig was shown to automate and simplify running linked Docker containers. Continuous integration and deployment with Docker was briefly discussed. While Docker provides benefits, it is still changing rapidly and there is no single solution.
Caching and tuning fun for high scalability

Caching has been a 'hot' topic for a few years. But caching takes more than merely taking data and putting it in a cache : the right caching techniques can improve performance and reduce load significantly. But we'll also look at some major pitfalls, showing that caching the wrong way can bring down your site. If you're looking for a clear explanation about various caching techniques and tools like Memcached, Nginx and Varnish, as well as ways to deploy them in an efficient way, this talk is for you.
kubernetes practice

The document provides instructions for setting up a Kubernetes cluster with one master node and one worker node on VirtualBox. It outlines the system requirements for the nodes, describes how to configure the networking and hostnames, install Docker and Kubernetes, initialize the master node with kubeadm init, join the worker node with kubeadm join, and deploy a test pod. It also includes commands to check the cluster status and remove existing Docker installations.
Basic Linux kernel

This document provides an overview of the Linux kernel, including its history, structure, build process, installation, updating, and customization. It discusses getting the kernel source code, configuring and building the kernel, installing modules and the kernel, applying updates via patches, and determining the correct driver for PCI devices by matching the vendor and device IDs. The key steps are to find the PCI IDs, search for the IDs in kernel headers to identify the driver, search the kernel makefiles and configuration to enable that driver for compilation.
Howto Pxeboot

This document describes how to set up a thin client deployment using PXE boot in a Microsoft-dominated network environment. Key steps include:
1. Configuring the DHCP server to provide PXE boot options and boot file information.
2. Preparing the RIS server by creating a PXE directory structure and boot images using the PXES tool.
3. Addressing bugs in PXES related to USB support, Samba password changes, and keyboard mappings to allow booting into a Linux environment and connecting to Windows terminal servers.
OFY-2015-Cloud-In-A-Day

This document outlines steps to build a cloud in 4 hours using Apache CloudStack and Citrix XenServer. It discusses installing Oracle VirtualBox, Citrix XenServer, CentOS, CloudStack, and configuring MySQL, NFS, firewall rules. Key steps include downloading templates, seeding the SystemVM template, configuring zones/pods/clusters/hosts, and creating VMs to test the cloud infrastructure. Resources for further exploration are provided.
MySQL Spider Architecture

This document discusses the setup and architecture of a MySQL Spider configuration. It describes installing multiple MySQL instances on a single server, including 4 MariaDB 10.1 nodes and 6 MySQL 5.7 nodes. It then configures the Spider storage engine to partition tables across these nodes for both data sharding and high availability. Key steps include defining servers, creating federated tables, and testing data is replicated correctly across nodes. The architecture provides both data sharding and high availability through table partitioning and failure recovery mechanisms.
Spider Setup with AWS/sandbox

This document discusses the setup and architecture of a MySQL Spider configuration. It describes installing multiple MySQL instances on a single server, including 4 MariaDB 10.1 nodes and 6 MySQL 5.7 nodes. It then configures the Spider storage engine to partition tables across these nodes for both data sharding and high availability. Examples are provided of creating servers, tables, and inserting/selecting data to demonstrate the federated and sharded architecture.
Linux hpc-cluster-setup-guide

This document provides instructions for setting up a Linux high-performance computing cluster. It details how to configure the master node to function as a DHCP and TFTP server to provide network installation files to client nodes. The document is divided into sections covering master node configuration such as network setup, DHCP, NFS, and key configuration; software installation including compilers, job schedulers, and scientific packages; and client node installation using PXE network boot.
9 creating cent_os 7_mages_for_dpdk_training

This document provides instructions for setting up a CentOS 7 VM using VirtualBox for DPDK training. It describes installing CentOS 7 Minimal, configuring the VM with 4 network interfaces, installing DPDK and related tools, compiling sample applications like l3fwd and pktgen, and manually starting the applications on the VM to test basic packet forwarding functionality.
Integrating Apache Web Server with Tomcat Application Server

This document provides instructions for integrating the Apache web server with the Tomcat application server on a Solaris 9 system. Key steps include compiling Apache from source, installing Java and Tomcat, and building the JK connector module to enable Apache to forward requests to Tomcat running on port 8009. Configuration changes to the Apache and Tomcat configuration files complete the integration.
Integrating Apache Web Server with Tomcat Application Server

This document provides instructions for integrating the Apache web server with the Tomcat application server on a Solaris 9 system. Key steps include:
1) Installing prerequisite software packages for Solaris 9 including GNU compiler tools;
2) Building Apache and the JK connector module from source;
3) Installing Java SDK and the Tomcat application server;
4) Configuring Apache and Tomcat to communicate via the JK connector module so that Apache can forward requests to servlets running on Tomcat.
Nginx 0.8.x 安装手册

This document provides instructions to install Nginx 0.8.x and PHP 5.2.10 using the FastCGI mode on a Linux system. It involves installing prerequisite packages and libraries, compiling and configuring MySQL, PHP, and additional PHP modules like memcache and imagick. The PHP installation is configured to use FastCGI mode and optimized using eAccelerator. Configuration files are modified and shell scripts are created to manage the MySQL service.
k8s practice 2023.pptx

The document provides instructions for setting up Kubernetes on two VMs (master and worker nodes) using VirtualBox. It describes the minimum requirements for the VMs and outlines the steps to configure networking and install Kubernetes, container runtime (containerd), and CNI (Flannel). The steps covered include setting up NAT and host-only networking in VirtualBox, configuring the hosts file, installing Kubernetes packages (kubeadm, kubelet, kubectl), initializing the master node with kubeadm, joining the worker node to the cluster, and deploying a sample pod.
Drupaljam 2017 - Deploying Drupal 8 onto Hosted Kubernetes in Google Cloud

In this presentation I explain using video examples how kubernetes works and how this can be used to host your Drupal 7 or 8 site. There are obviously also gotcha's and I'd like to warn you to not use this in production until you've verified it
Hdf installing-hdf

This document provides instructions for installing and configuring an HDF cluster using Ambari. It describes installing Ambari, required databases, and the HDF management pack. It then covers installing an HDF cluster using Ambari, and configuring various HDF components like Schema Registry, SAM, NiFi, Kafka, Storm and Log Search. It also provides instructions for configuring high availability for Schema Registry and SAM.
Openstack installation using rdo multi node

Openstack 3 node setup using RDO on top of RHEL 7.
Complete steps which will give you more convenience to work on top of Openstack without any installation issues.
Similar to An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing (20)
AtlasCamp 2015 Docker continuous integration training

AtlasCamp 2015 Docker continuous integration training
DeveloperWeek 2015: A Practical Introduction to Docker

DeveloperWeek 2015: A Practical Introduction to Docker
Integrating Apache Web Server with Tomcat Application Server

Integrating Apache Web Server with Tomcat Application Server
Integrating Apache Web Server with Tomcat Application Server

Integrating Apache Web Server with Tomcat Application Server
Drupaljam 2017 - Deploying Drupal 8 onto Hosted Kubernetes in Google Cloud

Drupaljam 2017 - Deploying Drupal 8 onto Hosted Kubernetes in Google Cloud
More from Abhishek Kumar
Insecurity-In-Security version.2 (2011)

Presentation (version.2) from 2011 describing how Security mechanisms placed to secure us are insecure themselves.
Insecurity-In-Security version.1 (2010)

Presentation (version.1) from 2010 describing how Security mechanisms placed to secure us are insecure themselves.
DevOps?!@

DevOps session#1 on what it is, which responsibilities it carries, what tools are already out there to help
xml-motor ~ What,Why,How

xml-motor
what, why & how about the new technique xml-parser rubygem
http://justfewtuts.blogspot.com/2012/03/xml-motor-what-it-is-how-why-should-you.html
XML-Motor

A new compact XML algorithm without any dependencies. Its implemented as a rubygem to provide Non-native XML parser for particular usages. RubyGem at http://rubygems.org/gems/xml-motor and https://github.com/abhishekkr/rubygem_xml_motor
DevOps with Sec-ops

it's presentation from a short 5-min talk at 1st DevOpsDays India about security implications and threats in DevOps related tasks
Syslog Centralization Logging with Windows ~ A techXpress Guide

Syslog Centralization Logging with Windows ~ A techXpress Guide ~ Setting up a centralized Syslog Server to get EventLogs from all Windows Hosts for analysis
Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide

Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide ~ Setting up a secured Chained-Proxy between different offices using Squid for a specific URL set.
Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide

Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide ~ for Load Balancing the Network Traffic on Multiple Etheret Cards attached on a Linux Box
Solaris Zones (native & lxbranded) ~ A techXpress Guide

Solaris Zones (native & lxbranded) ~ A techXpress Guide ~ Creating & Managing Solaris Zones; Mirroring an existing Linux Setup to a Zone; Setting up SVN, CIFS over a Zone
An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth

It's an Express Guide to "dummynet" for testing Web/Network Applications in real-use-case scenario ~~~~~ it can allow you to tweak Network Latencies and bandwidth to any value and test the application in those circumstances
An Express Guide ~ Zabbix for IT Monitoring 

Zabbix is an open source infrastructure monitoring solution. It has two main parts - the Zabbix server and client.
The document provides step-by-step instructions to install and configure Zabbix on a Linux server. This includes installing prerequisites like NTP, PHP, MySQL, compiling and installing the Zabbix server and client, configuring the database, web interface, and more. Finally, it discusses initial configuration steps after installation like securing login credentials.
An Express Guide ~ SNMP for Secure Rremote Resource Monitoring

It's an Express Guide to "Basic & Secure Setup of SNMP with purpose of Remote Resource Monitoring" ~~~~~ described here with a use-case of setting it up for monitoring availability of Network Connection on a remote machine and Trap notification in case the link goes down ~~~~~ for both Linux & Windows platforms
Presentation on "XSS Defeating Concept in (secure)SiteHoster" : 'nullcon-2011'

Nullcon is an annual hacker conference held in India. The document discusses defeating web application attacks through offensive security techniques like bug hunting and disarming malicious script tags. It also covers techniques for preventing cross-site scripting attacks, such as parsing user input and only allowing safe HTML tags.
XSS Defeating Concept - Part 2

An Approach Eradicating Effect of JavaScript Events in
User Input Being A Part of Web2.0 Facilities... in short the final nail to coffin of XSS Attacks
XSS Defeating Trick ~=ABK=~ WhitePaper

This document proposes a technique to prevent XSS attacks by modifying how browsers render <script> tags inserted into the <body> of an HTML document. The technique involves the web server transforming the page generated by the application server by wrapping the <body> contents in a <script> tag. This causes any <script> tags in the original <body> to not execute while preserving those in the <head>. The goal is to enable security without requiring input validation by web developers. A proof-of-concept implementation demonstrates how this modification disables injected malicious scripts.
FreeSWITCH on RedHat, Fedora, CentOS

This document provides instructions to install FreeSWITCH on CentOS/RedHat/Fedora in 13 steps: 1) Install dependencies with YUM; 2) Download and extract FreeSWITCH source; 3) Add OpenZAP support to configuration; 4) Compile and install FreeSWITCH; 5) Create symlinks for main binaries; 6) Launch FreeSWITCH as a service or from the command line; 7) Use fs_cli to access the command line.
More from Abhishek Kumar (17)
Syslog Centralization Logging with Windows ~ A techXpress Guide

Syslog Centralization Logging with Windows ~ A techXpress Guide
Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide

Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide
Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide

Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide
Solaris Zones (native & lxbranded) ~ A techXpress Guide

Solaris Zones (native & lxbranded) ~ A techXpress Guide
An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth

An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth
An Express Guide ~ SNMP for Secure Rremote Resource Monitoring

An Express Guide ~ SNMP for Secure Rremote Resource Monitoring
Presentation on "XSS Defeating Concept in (secure)SiteHoster" : 'nullcon-2011'

Presentation on "XSS Defeating Concept in (secure)SiteHoster" : 'nullcon-2011'
Recently uploaded
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on automated letter generation for Bonterra Impact Management using Google Workspace or Microsoft 365.
Interested in deploying letter generation automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Azure API Management to expose backend services securely

How to use Azure API Management to expose backend service securely
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on integration of Salesforce with Bonterra Impact Management.
Interested in deploying an integration with Salesforce for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Digital Marketing Trends in 2024 | Guide for Staying Ahead

https://www.wask.co/ebooks/digital-marketing-trends-in-2024
Feeling lost in the digital marketing whirlwind of 2024? Technology is changing, consumer habits are evolving, and staying ahead of the curve feels like a never-ending pursuit. This e-book is your compass. Dive into actionable insights to handle the complexities of modern marketing. From hyper-personalization to the power of user-generated content, learn how to build long-term relationships with your audience and unlock the secrets to success in the ever-shifting digital landscape.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
dbms calicut university B. sc Cs 4th sem.pdf

Its a seminar ppt on database management system using sql
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Recently uploaded (20)
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Letter and Document Automation for Bonterra Impact Management (fka Social Sol...
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...

Overcoming the PLG Trap: Lessons from Canva's Head of Sales & Head of EMEA Da...
Azure API Management to expose backend services securely

Azure API Management to expose backend services securely
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Digital Marketing Trends in 2024 | Guide for Staying Ahead

Digital Marketing Trends in 2024 | Guide for Staying Ahead
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
WeTestAthens: Postman's AI & Automation Techniques

WeTestAthens: Postman's AI & Automation Techniques
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing
- 1. Express-Guide ~to~ Basic Setup of Cacti an IT Infrastructure Monitoring Solution by, ABK ~ http://www.twitter.com/aBionic ::Task Detail:: Setting up Cacti for IT Infrastructure Service Graphing solution. ::Background:: Links: http://www.cacti.net/ Cacti is a complete network graphing solution designed to harness the power of RRDTool's data storage and graphing functionality. Here RRDTool was supposed to poll data on secured SNMPv3 channels from host and these data will be analyzed on Graphs using Cacti. ::Execution Method:: Pre-Requisite: Installing/Updating all these, at shell (say for Fedora/CentOS) ◦ #yum -y install php php-get php-mysql php-pear ◦ #yum -y install php-common php-devel php-mbstring ◦ #yum -y install php-cli php-snmp php-pear-net-smtp ◦ #yum -y install rrdtool httpd mysql mysql-server mysql-devel ◦ #yum -y install net-snmp net-snmp-utils net-snmp-devel net-snmp-libs Steps ◦ Configure all the pre-requisites for the settings you wanna be implemented for Cacti (esp. the SNMP Community String) ◦ Adding required users and groups, at shell ▪ #groupadd cacti ▪ #useradd -g cacti cactiuser
- 2. ◦ Configuring MySQL server ▪ #mysqladmin -u root password newPassword ▪ #mysql -u root -p$Whatever_Password_You_Want ▪ mysql>CREATE DATABASE cactidb; ▪ mysql>GRANT ALL ON cactidb.* TO root; ▪ mysql>GRANT ALL ON cactidb.* TO root@localhost; ▪ mysql>GRANT ALL ON cactidb.* TO cacti; ▪ mysql>GRANT ALL ON cactidb.* TO cacti@localhost; ▪ mysql>SET PASSWORD FOR cactiuser@localhost=PASSWORD('cactiUserPassword'); ▪ mysql>exit ◦ Install Cacti ▪ #yum -y install cacti ◦ Prepare database find path for cacti.sql from following command ▪ #rpm -ql cacti | grep -i cacti.sql Note: suppose it gives "/usr/share/.../cacti.sql" path, then #mysql -u cactiuser -p cactidb< /usr/share/.../cacti.sql ◦ Configure Cacti ▪ Open '/etc/cacti/db-php' in any editor, and set values as given $database_type="mysql" $database_default="cactidb" $database_hostname="localhost" $database_username="cactiuser" $database_password="cactiUserPassword" $database_port=3300 ◦ Configure httpd for Cacti ▪ Open '/etc/httpd/conf.d/cacti.conf' in any editor, add lines ##########start of text to add####### Alias /cacti /usr/share/cacti <Directory /usr/share/cacti> Order,Deny,Allow Deny from all Allow from 192.168.0.0/16 </Directory> ###########end of text to add####### ◦ Setup Cacti cronjob Open '/etc/cron.d/cacti' in any editor, and un-comment the line '*/5 * * * * cacti /usr/bin/php /user/share/cacti/poller.php > /dev/null 2 > &1'
- 3. ◦ Restart the 'httpd' service, then open 'http://CactiServerIP/cacti' in any browser and follow easy installation method, rectifying any error found. ◦ Default username and password to login is admin:admin ::Tools/Technology Used:: Cacti : http://www.cacti.net/ Net-SNMP : http://www.net-snmp.org MySQL : http://dev.mysql.com/downloads/ ::Inference:: Cacti is a brilliant network graphing system, but certain of its dependencies only supported their old version. They also have a Cacti ready linux-distro CactiEZ which is loaded with many useful plug-ins but when installed, ask nothing for Partition and use the entire HDD with best way easy installation. ::Troubleshooting/Updates:: Problem: if during Web Installation part any error comes regarding RRDTool or PHP Solution: In that portal itself mention the checked paths for them, which should be RRDTool=/usr/local/rrdtool/bin/rrdtool PHP=/www/php/bin/php
