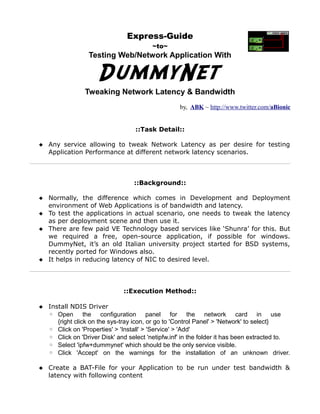
An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth
•
1 like•1,725 views
It's an Express Guide to "dummynet" for testing Web/Network Applications in real-use-case scenario ~~~~~ it can allow you to tweak Network Latencies and bandwidth to any value and test the application in those circumstances
Report
Share
Report
Share
Download to read offline
Recommended
VerneMQ - Distributed MQTT Broker

A presentation I made for the "Pervasive Systems" course of the "Master of Science in Engineering in Computer Science" at Sapienza Università di Roma (Sapienza University of Rome) A.Y. 2017/2018
Securing & Enforcing Network Policy and Encryption with Weave Net

This talk starts with a primer on container networking, then goes on to cover two distinct areas of container network security: encryption, enabled by IPsec in Weave Net and container firewalls, enabled by Kubernetes Network Policy and enforced by the Weave Net Network Policy Controller. A discussion of thread models is included.
Reaching 5 Million Messaging Connections: Our Journey with Kubernetes

Learn how we built a high-scale messaging service and state store on Kubernetes. The solution supports millions of persistent, concurrent connections; enables tens of thousands of messages per second; is globally addressable; stores millions of states; and responds with minimal latency (<250ms).
To evaluate build approaches, the team split into Makers & Breakers. Makers developed the solution stack while Breakers focused on repurposing Locust, a high-scale load testing framework, to simulate behavior. Leveraging the flexibility of Kubernetes, we were able to scale the stack and solve blockers on the path to a viable solution. Blockers included ingress, file descriptors, service discovery and resource limits. The experience was deeply educational, generating key learnings for developers tasked with building a scaled solution on top of Kubernetes.
Dos attack

This document discusses denial of service (DoS) attacks. It defines DoS as an attack meant to make a machine or network unavailable to its intended users. Several common DoS attack methods are described, including ICMP floods, teardrop attacks, and reflected/spoofed attacks. The document also provides information on tools used for DoS attacks and discusses how to identify an attack, what to do in response, and how to avoid being part of the problem.
Jacopo Nardiello - Monitoring Cloud-Native applications with Prometheus - Cod...

We are going to talk about Prometheus and how to use to monitor micro-services "Cloud-Native" application s. We are going to dive deep into the Prometheus monitoring model, we will see what are the components be hind this system and how they integrate with each others to provide an efficient and modern monitoring sy stem. We will also have a glance on Prometheus native integrations for cloud-native environments such as Kubernetes.
Baking even more Clam(AV)s for Fun & Profit.

This document discusses security issues with the open source antivirus software ClamAV when configured in a networked manner. Specifically, it notes that ClamAV's default configuration allows remote access without authentication, exposes administrative commands that could be abused, and has bugs that could allow denial of service attacks or information disclosure. It provides recommendations for secure configuration, access controls, and monitoring to help defend against risks.
OpenVPN

OpenVPN provides an easy to deploy and configure VPN server with centralized web-based management. The administrator installs OpenVPN Access Server, registers for a free account, and uses a configuration wizard to set up the server. Users authenticate using PAM, Radius, or Active Directory and download the OpenVPN client to connect. The Access Server provides GUI administration of both the server and client authentication.
Big Data, Better Networks

Cumulus Networks aims to bring the benefits of open source networking to big data environments through its Cumulus Linux operating system. By using a layer 3 fabric design with ECMP routing and open protocols, Cumulus Linux allows for unlimited east-west bandwidth between servers and improved failure handling. It also enables location independence, faster recovery from failures, and unified management of both servers and networking through automation tools. Cumulus Linux provides innovations like ONIE, ZTP, and network virtualization to simplify deployment and management of big data networks running workloads like Hadoop.
Recommended
VerneMQ - Distributed MQTT Broker

A presentation I made for the "Pervasive Systems" course of the "Master of Science in Engineering in Computer Science" at Sapienza Università di Roma (Sapienza University of Rome) A.Y. 2017/2018
Securing & Enforcing Network Policy and Encryption with Weave Net

This talk starts with a primer on container networking, then goes on to cover two distinct areas of container network security: encryption, enabled by IPsec in Weave Net and container firewalls, enabled by Kubernetes Network Policy and enforced by the Weave Net Network Policy Controller. A discussion of thread models is included.
Reaching 5 Million Messaging Connections: Our Journey with Kubernetes

Learn how we built a high-scale messaging service and state store on Kubernetes. The solution supports millions of persistent, concurrent connections; enables tens of thousands of messages per second; is globally addressable; stores millions of states; and responds with minimal latency (<250ms).
To evaluate build approaches, the team split into Makers & Breakers. Makers developed the solution stack while Breakers focused on repurposing Locust, a high-scale load testing framework, to simulate behavior. Leveraging the flexibility of Kubernetes, we were able to scale the stack and solve blockers on the path to a viable solution. Blockers included ingress, file descriptors, service discovery and resource limits. The experience was deeply educational, generating key learnings for developers tasked with building a scaled solution on top of Kubernetes.
Dos attack

This document discusses denial of service (DoS) attacks. It defines DoS as an attack meant to make a machine or network unavailable to its intended users. Several common DoS attack methods are described, including ICMP floods, teardrop attacks, and reflected/spoofed attacks. The document also provides information on tools used for DoS attacks and discusses how to identify an attack, what to do in response, and how to avoid being part of the problem.
Jacopo Nardiello - Monitoring Cloud-Native applications with Prometheus - Cod...

We are going to talk about Prometheus and how to use to monitor micro-services "Cloud-Native" application s. We are going to dive deep into the Prometheus monitoring model, we will see what are the components be hind this system and how they integrate with each others to provide an efficient and modern monitoring sy stem. We will also have a glance on Prometheus native integrations for cloud-native environments such as Kubernetes.
Baking even more Clam(AV)s for Fun & Profit.

This document discusses security issues with the open source antivirus software ClamAV when configured in a networked manner. Specifically, it notes that ClamAV's default configuration allows remote access without authentication, exposes administrative commands that could be abused, and has bugs that could allow denial of service attacks or information disclosure. It provides recommendations for secure configuration, access controls, and monitoring to help defend against risks.
OpenVPN

OpenVPN provides an easy to deploy and configure VPN server with centralized web-based management. The administrator installs OpenVPN Access Server, registers for a free account, and uses a configuration wizard to set up the server. Users authenticate using PAM, Radius, or Active Directory and download the OpenVPN client to connect. The Access Server provides GUI administration of both the server and client authentication.
Big Data, Better Networks

Cumulus Networks aims to bring the benefits of open source networking to big data environments through its Cumulus Linux operating system. By using a layer 3 fabric design with ECMP routing and open protocols, Cumulus Linux allows for unlimited east-west bandwidth between servers and improved failure handling. It also enables location independence, faster recovery from failures, and unified management of both servers and networking through automation tools. Cumulus Linux provides innovations like ONIE, ZTP, and network virtualization to simplify deployment and management of big data networks running workloads like Hadoop.
AWS re:Invent 2016: Encryption: It Was the Best of Controls, It Was the Worst...

This document provides a summary of a presentation on encryption. It discusses why encryption is important for compliance with regulations like PCI DSS and HIPAA. It covers different encryption techniques like block ciphers and stream ciphers. It describes how protocols like TLS work and how certain ciphers like RC4 have been broken over time. It discusses attacks like BEAST and ways crypto failures can occur. It emphasizes that encryption is difficult and recommends following best practices around key management and the challenges of real-world implementation.
Capistrano 3 Deployment

Capistrano 3 has been rebuilt from the ground up. Learn how to transition from using Capistrano version 2 to Capistrano version 3.
Control your deployments with Capistrano

This document discusses Capistrano, a remote server automation and deployment tool. Some key points:
- Capistrano allows reliable deployment of web applications to multiple machines simultaneously, with features like rollback, adding tasks, and automating common tasks.
- It works by creating a new folder for each deployment on servers and symlinking the current version. Shared files are not overwritten on redeploys.
- Configuration involves setting stages, roles, branches, and other parameters in Capistrano files. Tasks can be added for custom actions.
- Deploying runs tasks sequentially like updating servers, publishing, finishing. Rollback has similar reversing tasks. Plugins add features like maintenance modes.
Pipe your script to slack

Presented at SF SlackDevs Meetup on April 11, 2016
[Record of presentation]
http://www.ustream.tv/recorded/85566064 (0:26:00~)
[GitHub page of slacktee]
https://github.com/course-hero/slacktee
Windows Package Manager Concept

Year 2007: An attempt to develop a package manager (equivalent to apt/brew) for Windows Operating system.
Managing ejabberd Platforms with Docker - ejabberd Workshop #1

Christophe Romain (ProcessOne) introduces Docker and ProcessOne work in progress to support Docker-based ejabberd deployments.
Setup Kubernetes with flannel on ubuntu platform

This document provides instructions for setting up Kubernetes with 2 nodes using kubeadm and flannel on Ubuntu. It describes installing Docker and Kubernetes, initializing the master node with kubeadm init, joining the worker node with the kubeadm join command, installing and configuring flannel as the pod network, and deploying and exposing the Kubernetes dashboard for management. Specific steps include installing Docker, initializing the master, saving the join command, installing flannel on all nodes, joining the worker, installing the dashboard and changing its service type to NodePort for external access.
Ejabberd with xmpp

Ejabberd is an open-source XMPP instant messaging server written in Erlang. It is cross-platform, distributed, fault-tolerant, and based on open XMPP standards. Ejabberd supports features like internal and external authentication, virtual hosting, IPv6, and extensions for messaging, presence, file transfers and more. It can be installed on Linux, Windows and other platforms. Basic configuration involves setting up an admin user, hosts, and adding/managing other users.
Positive Hack Days. Pavlov. Network Infrastructure Security Assessment

A participant will acquire basic skills of searching for vulnerabilities on switches and routers from various vendors. The masterclass will cover both common network vulnerabilities, and exceptive cases that can be detected in the process of security assessment of real networks.
Virtualization and SAN Basics for DBAs

This document discusses best practices for virtual machines (VMs), storage area networks (SANs), and SQL Server. It provides three "nevers" for VMs: never overallocate virtual CPUs, never use automatic settings, and never assume VMs are alone. It also gives three "always" for SANs: always know your neighbors on the SAN, always test storage performance first with SQLIO before SQL Server, and always be checking performance metrics. Key metrics discussed include processor queue length, SQL Server memory page life expectancy, and physical disk read/write average time. The document emphasizes testing storage, understanding competition from other workloads, and monitoring for subtle performance changes.
Nimbuzz march2012

This summary provides an overview of the Nimbuzz architecture and technologies:
Nimbuzz is a communication platform that allows calling, messaging, and file sharing across mobile devices and computers using popular IM networks. It uses a microservices architecture with small, stateless services and external components communicating over XMPP. The platform is built on Ejabberd, an XMPP server written in Erlang, which provides features like concurrency, distribution, and high availability. Caching, database, and data processing best practices are employed to optimize performance for millions of daily users.
Capistrano - Deployment Tool

Seminar presentation on Capistrano by Nagesh at Nyros Technologies on 16th June, 2009.
http://www.nyros.com
Testing MidoNet

Tomoe Sugihara from Midokura presented on testing efforts for MidoNet software components. Key points include:
1. MidoNet has various software components like the controller, agents, and APIs that require different types of testing like unit, integration, and end-to-end.
2. MDTS is a testing framework that allows emulating a multi-node deployment on a single host to run end-to-end connectivity tests between virtual machines.
3. The testing system uses Jenkins for CI to run unit/integration tests and MDTS end-to-end tests, and a CT pipeline to run Tempest integration tests on OpenStack with MidoNet. Future work aims to optimize
Parallel Running Automation Solution with Docker, Jenkins and Zalenium

Presentation on how to build an infrastructure for running automated test suites using Docker, Jenkins and Zalenium (Selenium Grid in a docker container)
Recommended For: Any test engineer who wants a parallelization for running the automated tests using free sources technologies.
Meetup 23 - 01 - The things I wish I would have known before doing OpenStack ...

Meetup 23 - 01 - The things I wish I would have known before doing OpenStack ...Vietnam Open Infrastructure User Group
The document provides tips for OpenStack cloud transformation. It discusses (1) unifying CPU models on compute nodes for live migration, (2) clustering compute nodes by host aggregate, and (3) configuring options to slow down CPU during live migration for stability. Other tips include increasing HAProxy connection limits, enabling multiple network queues, implementing port level security, and ensuring adequate entropy for scale-out systems. The overall document offers best practices and configurations for improving performance and stability during OpenStack cloud transformations.Upcoming Products, Services and Features - Workshop by Praveen Umanath

The document summarizes upcoming products, services, and features from two product managers. New shared hosting features include SSH key authentication and Ruby support. A new VPS offering uses high-end hardware and storage. Dedicated servers will offer blade servers, storage expansion, and Linux/Windows support. Additional data centers in Turkey and Hong Kong are planned along with an enterprise email product in beta testing.
Remote Console: Say goodbye to RDP

This document provides an overview of the components and architecture of Veeam's Remote Console software. It discusses key concepts like availability, security and stability. It describes the various services that make up the software such as the Remote Console, Remote PS, Explorers and Mount Server. It also outlines the network connections and ports used, diagnostic and logging functions, and how the software can improve restore performance and support remote mounting and explorers.
OpenStack & OVS: From Love-Hate Relationship to Match Made in Heaven - Erez C...

OpenStack & OVS: From Love-Hate Relationship to Match Made in Heaven - Erez C...Cloud Native Day Tel Aviv
"Many developers building OpenStack clouds have “love-hate” relationship with OVS. They love flexibility and elasticity offered by OVS, but hate the network performance and scalability. As emerging technologies such as NFV keep pushing for higher network performance, it becomes critical to improve OVS performance without compromising flexibility, network programmability, and cost.
In this session, we will present an approach that Mellanox has devised with input from key partners and customers to accelerate Virtual Switch dataplane, using the embedded switch implemented in the server Network Interface Card (NIC)’s hardware. This approach supports both ParaVirt vNIC interfaces and SRIOV based vNICs interfaces"Backtrack Manual Part4

Automated Image & Restore (AIR) is an open source forensic imaging tool with a graphical user interface. It provides an easy front-end for disk/partition imaging using dd and dcfldd commands. Key features include support for hashing algorithms, SCSI tape drives, network imaging, splitting images, and detailed session logging. The tutorial demonstrates installing and using AIR to create a forensic image of a file on a Linux system and copy it to a CD-ROM for evidence preservation.
26.1.7 lab snort and firewall rules

The document provides instructions for a lab on Snort and firewall rules. It describes:
1) Setting up the virtual environment and configuring networking on the CyberOps Workstation VM.
2) Explaining the differences between firewall and IDS rules while noting their similarities, such as both having matching and action components.
3) Having students run commands to start a malware server, use Snort to monitor traffic, and download a file from the server to trigger an alert, observing the alert in the Snort log.
An Express Guide ~ SNMP for Secure Rremote Resource Monitoring

It's an Express Guide to "Basic & Secure Setup of SNMP with purpose of Remote Resource Monitoring" ~~~~~ described here with a use-case of setting it up for monitoring availability of Network Connection on a remote machine and Trap notification in case the link goes down ~~~~~ for both Linux & Windows platforms
J365963

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
More Related Content
What's hot
AWS re:Invent 2016: Encryption: It Was the Best of Controls, It Was the Worst...

This document provides a summary of a presentation on encryption. It discusses why encryption is important for compliance with regulations like PCI DSS and HIPAA. It covers different encryption techniques like block ciphers and stream ciphers. It describes how protocols like TLS work and how certain ciphers like RC4 have been broken over time. It discusses attacks like BEAST and ways crypto failures can occur. It emphasizes that encryption is difficult and recommends following best practices around key management and the challenges of real-world implementation.
Capistrano 3 Deployment

Capistrano 3 has been rebuilt from the ground up. Learn how to transition from using Capistrano version 2 to Capistrano version 3.
Control your deployments with Capistrano

This document discusses Capistrano, a remote server automation and deployment tool. Some key points:
- Capistrano allows reliable deployment of web applications to multiple machines simultaneously, with features like rollback, adding tasks, and automating common tasks.
- It works by creating a new folder for each deployment on servers and symlinking the current version. Shared files are not overwritten on redeploys.
- Configuration involves setting stages, roles, branches, and other parameters in Capistrano files. Tasks can be added for custom actions.
- Deploying runs tasks sequentially like updating servers, publishing, finishing. Rollback has similar reversing tasks. Plugins add features like maintenance modes.
Pipe your script to slack

Presented at SF SlackDevs Meetup on April 11, 2016
[Record of presentation]
http://www.ustream.tv/recorded/85566064 (0:26:00~)
[GitHub page of slacktee]
https://github.com/course-hero/slacktee
Windows Package Manager Concept

Year 2007: An attempt to develop a package manager (equivalent to apt/brew) for Windows Operating system.
Managing ejabberd Platforms with Docker - ejabberd Workshop #1

Christophe Romain (ProcessOne) introduces Docker and ProcessOne work in progress to support Docker-based ejabberd deployments.
Setup Kubernetes with flannel on ubuntu platform

This document provides instructions for setting up Kubernetes with 2 nodes using kubeadm and flannel on Ubuntu. It describes installing Docker and Kubernetes, initializing the master node with kubeadm init, joining the worker node with the kubeadm join command, installing and configuring flannel as the pod network, and deploying and exposing the Kubernetes dashboard for management. Specific steps include installing Docker, initializing the master, saving the join command, installing flannel on all nodes, joining the worker, installing the dashboard and changing its service type to NodePort for external access.
Ejabberd with xmpp

Ejabberd is an open-source XMPP instant messaging server written in Erlang. It is cross-platform, distributed, fault-tolerant, and based on open XMPP standards. Ejabberd supports features like internal and external authentication, virtual hosting, IPv6, and extensions for messaging, presence, file transfers and more. It can be installed on Linux, Windows and other platforms. Basic configuration involves setting up an admin user, hosts, and adding/managing other users.
Positive Hack Days. Pavlov. Network Infrastructure Security Assessment

A participant will acquire basic skills of searching for vulnerabilities on switches and routers from various vendors. The masterclass will cover both common network vulnerabilities, and exceptive cases that can be detected in the process of security assessment of real networks.
Virtualization and SAN Basics for DBAs

This document discusses best practices for virtual machines (VMs), storage area networks (SANs), and SQL Server. It provides three "nevers" for VMs: never overallocate virtual CPUs, never use automatic settings, and never assume VMs are alone. It also gives three "always" for SANs: always know your neighbors on the SAN, always test storage performance first with SQLIO before SQL Server, and always be checking performance metrics. Key metrics discussed include processor queue length, SQL Server memory page life expectancy, and physical disk read/write average time. The document emphasizes testing storage, understanding competition from other workloads, and monitoring for subtle performance changes.
Nimbuzz march2012

This summary provides an overview of the Nimbuzz architecture and technologies:
Nimbuzz is a communication platform that allows calling, messaging, and file sharing across mobile devices and computers using popular IM networks. It uses a microservices architecture with small, stateless services and external components communicating over XMPP. The platform is built on Ejabberd, an XMPP server written in Erlang, which provides features like concurrency, distribution, and high availability. Caching, database, and data processing best practices are employed to optimize performance for millions of daily users.
Capistrano - Deployment Tool

Seminar presentation on Capistrano by Nagesh at Nyros Technologies on 16th June, 2009.
http://www.nyros.com
Testing MidoNet

Tomoe Sugihara from Midokura presented on testing efforts for MidoNet software components. Key points include:
1. MidoNet has various software components like the controller, agents, and APIs that require different types of testing like unit, integration, and end-to-end.
2. MDTS is a testing framework that allows emulating a multi-node deployment on a single host to run end-to-end connectivity tests between virtual machines.
3. The testing system uses Jenkins for CI to run unit/integration tests and MDTS end-to-end tests, and a CT pipeline to run Tempest integration tests on OpenStack with MidoNet. Future work aims to optimize
Parallel Running Automation Solution with Docker, Jenkins and Zalenium

Presentation on how to build an infrastructure for running automated test suites using Docker, Jenkins and Zalenium (Selenium Grid in a docker container)
Recommended For: Any test engineer who wants a parallelization for running the automated tests using free sources technologies.
Meetup 23 - 01 - The things I wish I would have known before doing OpenStack ...

Meetup 23 - 01 - The things I wish I would have known before doing OpenStack ...Vietnam Open Infrastructure User Group
The document provides tips for OpenStack cloud transformation. It discusses (1) unifying CPU models on compute nodes for live migration, (2) clustering compute nodes by host aggregate, and (3) configuring options to slow down CPU during live migration for stability. Other tips include increasing HAProxy connection limits, enabling multiple network queues, implementing port level security, and ensuring adequate entropy for scale-out systems. The overall document offers best practices and configurations for improving performance and stability during OpenStack cloud transformations.Upcoming Products, Services and Features - Workshop by Praveen Umanath

The document summarizes upcoming products, services, and features from two product managers. New shared hosting features include SSH key authentication and Ruby support. A new VPS offering uses high-end hardware and storage. Dedicated servers will offer blade servers, storage expansion, and Linux/Windows support. Additional data centers in Turkey and Hong Kong are planned along with an enterprise email product in beta testing.
Remote Console: Say goodbye to RDP

This document provides an overview of the components and architecture of Veeam's Remote Console software. It discusses key concepts like availability, security and stability. It describes the various services that make up the software such as the Remote Console, Remote PS, Explorers and Mount Server. It also outlines the network connections and ports used, diagnostic and logging functions, and how the software can improve restore performance and support remote mounting and explorers.
OpenStack & OVS: From Love-Hate Relationship to Match Made in Heaven - Erez C...

OpenStack & OVS: From Love-Hate Relationship to Match Made in Heaven - Erez C...Cloud Native Day Tel Aviv
"Many developers building OpenStack clouds have “love-hate” relationship with OVS. They love flexibility and elasticity offered by OVS, but hate the network performance and scalability. As emerging technologies such as NFV keep pushing for higher network performance, it becomes critical to improve OVS performance without compromising flexibility, network programmability, and cost.
In this session, we will present an approach that Mellanox has devised with input from key partners and customers to accelerate Virtual Switch dataplane, using the embedded switch implemented in the server Network Interface Card (NIC)’s hardware. This approach supports both ParaVirt vNIC interfaces and SRIOV based vNICs interfaces"What's hot (18)
AWS re:Invent 2016: Encryption: It Was the Best of Controls, It Was the Worst...

AWS re:Invent 2016: Encryption: It Was the Best of Controls, It Was the Worst...
Managing ejabberd Platforms with Docker - ejabberd Workshop #1

Managing ejabberd Platforms with Docker - ejabberd Workshop #1
Positive Hack Days. Pavlov. Network Infrastructure Security Assessment

Positive Hack Days. Pavlov. Network Infrastructure Security Assessment
Parallel Running Automation Solution with Docker, Jenkins and Zalenium

Parallel Running Automation Solution with Docker, Jenkins and Zalenium
Meetup 23 - 01 - The things I wish I would have known before doing OpenStack ...

Meetup 23 - 01 - The things I wish I would have known before doing OpenStack ...
Upcoming Products, Services and Features - Workshop by Praveen Umanath

Upcoming Products, Services and Features - Workshop by Praveen Umanath
OpenStack & OVS: From Love-Hate Relationship to Match Made in Heaven - Erez C...

OpenStack & OVS: From Love-Hate Relationship to Match Made in Heaven - Erez C...
Similar to An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth
Backtrack Manual Part4

Automated Image & Restore (AIR) is an open source forensic imaging tool with a graphical user interface. It provides an easy front-end for disk/partition imaging using dd and dcfldd commands. Key features include support for hashing algorithms, SCSI tape drives, network imaging, splitting images, and detailed session logging. The tutorial demonstrates installing and using AIR to create a forensic image of a file on a Linux system and copy it to a CD-ROM for evidence preservation.
26.1.7 lab snort and firewall rules

The document provides instructions for a lab on Snort and firewall rules. It describes:
1) Setting up the virtual environment and configuring networking on the CyberOps Workstation VM.
2) Explaining the differences between firewall and IDS rules while noting their similarities, such as both having matching and action components.
3) Having students run commands to start a malware server, use Snort to monitor traffic, and download a file from the server to trigger an alert, observing the alert in the Snort log.
An Express Guide ~ SNMP for Secure Rremote Resource Monitoring

It's an Express Guide to "Basic & Secure Setup of SNMP with purpose of Remote Resource Monitoring" ~~~~~ described here with a use-case of setting it up for monitoring availability of Network Connection on a remote machine and Trap notification in case the link goes down ~~~~~ for both Linux & Windows platforms
J365963

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
NCS: NEtwork Control System Hands-on Labs 

Jason Yen, Solution Architect and Ashok Sadasivan, Solution Architect, discusses NCS: Network control systems at Cisco Connect Toronto 2015.
Howto Pxeboot

This document describes how to set up a thin client deployment using PXE boot in a Microsoft-dominated network environment. Key steps include:
1. Configuring the DHCP server to provide PXE boot options and boot file information.
2. Preparing the RIS server by creating a PXE directory structure and boot images using the PXES tool.
3. Addressing bugs in PXES related to USB support, Samba password changes, and keyboard mappings to allow booting into a Linux environment and connecting to Windows terminal servers.
Fault tolerance performance and scalability comparison: NEC hardware-based FT...

Fault tolerance performance and scalability comparison: NEC hardware-based FT...Principled Technologies
The document compares the performance and scalability of hardware-based fault tolerance provided by NEC Express5800/R320d-M4 servers versus software-based fault tolerance using VMware vSphere on NEC Express5800/R120d-M1 servers. It finds that when each solution ran eight simultaneous VMs, the hardware-based solution achieved more than twice the performance of the software-based solution, processing 2.4 times as many database orders per minute, and was able to recover from a service interruption with zero downtime.9 creating cent_os 7_mages_for_dpdk_training

This document provides instructions for setting up a CentOS 7 VM using VirtualBox for DPDK training. It describes installing CentOS 7 Minimal, configuring the VM with 4 network interfaces, installing DPDK and related tools, compiling sample applications like l3fwd and pktgen, and manually starting the applications on the VM to test basic packet forwarding functionality.
Ccnav5.org ccna 4-v50_practice_final_exam

A network administrator is troubleshooting connectivity issues between a router and a non-Cisco device running Frame Relay. The exhibit shows the router configuration. The likely cause of the Layer 2 connectivity problem is that the ietf keyword is missing when enabling Frame Relay on the serial interface. Adding this keyword should repair the connectivity issue.
PPPoE With Mikrotik and Radius

How to manage internet clients of an ISP with PPPoE and MikroTik. For
centralized AAA (Authentication, Authorization and Accounting), freeRadius is used.
NodeJS guide for beginners

Node.js is an open-source JavaScript runtime environment that allows building scalable server-side and networking applications. It uses asynchronous, event-driven, non-blocking I/O which makes it lightweight and efficient for data-intensive real-time applications that run across distributed devices. Some key features of Node.js include excellent support for building RESTful web services, real-time web applications, IoT applications and scaling to many users. It uses Google's V8 JavaScript engine to execute code outside of a browser.
7 hands on

The document provides instructions for running an Intel DPDK hands-on session to demonstrate packet forwarding using the l3fwd example. It describes downloading and compiling DPDK, getting and applying patches to l3fwd, configuring three VMs with pktgen to generate and receive packets and l3fwd to forward between them, and running l3fwd and pktgen manually or automatically on system startup.
Module1 print

This document provides instructions for isolating and troubleshooting printer problems on a network. It discusses using the configuration report to check the printer's IP address, subnet mask, and gateway. It also covers verifying the network adapter and IP address on the PWS, using ping and ipconfig commands to test network connectivity, and different network printing protocols like LPR, port 9100, and printing via the printer's web interface. The document also provides information on PCL and PostScript print drivers as well as instructions for downloading, installing, and configuring print drivers on the PWS.
Osol Netadmin Solaris Administrator

The document discusses four OpenSolaris projects - Network Auto-Magic, Clearview, Brussels, and Crossbow - that aim to simplify and enhance network administration on the Solaris platform. Network Auto-Magic seeks to automate basic network configuration. Clearview aims to unify and enhance features across different network interfaces. Brussels looks to simplify network interface configuration and tuning. Crossbow integrates network interface virtualization and resource management.
Novarum wlan

This document summarizes a test of three high-density wireless LAN infrastructures (Aruba, Cisco, Juniper) with over 300 Wi-Fi clients. Key findings include: Juniper maintained the best performance as load increased, delivering the highest throughput with the fewest retries and stream failures. Aruba performed lower than Juniper. Cisco struggled significantly, with over 62% of streams failing under one maximum load test. Juniper demonstrated the most robust performance for high client densities.
TechWiseTV Workshop: OpenDNS and AnyConnect

Join this in-depth look and detailed demonstration of the OpenDNS Umbrella integration with AnyConnect and how it really can stop most threats before they become serious problems, protecting users anywhere they go, even when the VPN is off.
Watch the workshop replay: http://bit.ly/2bPT1ax
Watch the Video: http://bit.ly/2c60obv
Network Design patters with Docker

Talk from DockerCon, looking at the various Docker network technologies and how to implement them to migration applications.
Transparent proxy - SIP - 2014 - NCC LAB

This document summarizes a summer internship project to implement a proxyless internet access system for a university campus network. The interns configured PfSense open source firewall/router software with Squid and Captive Portal to provide transparent proxy access along with user authentication. They implemented load balancing, high availability, and deep packet inspection for security and performance. The system allows all applications like Windows, Android, and iOS to access the internet without proxy settings while still providing logging and content filtering.
Open Programmable Architecture for Java-enabled Network Devices

Current network devices enable connectivity between end systems given a set of protocol software bundled with vendor hardware. It is impossible for customers to add software functionality running locally on top of network devices to augment vendor software. Our vision is to open network devices so that customized software can be downloaded, allowing for more flexibility and with a focus on industry and customer specific solutions. This brings considerable value to the customer. We have chosen to use Java because we can reuse its security mechanism and
dynamically download software. We can isolate the Java VM and downloaded Java programs from the core router functionality. We implemented Java Virtual Machines (JVMs) on a family of network devices,
implemented an Open Services framework, and developed an SNMP MIB API and a Network API upon which we can demonstate the value of openness and programmability of network devices.
Whatsup

This document provides an addendum to the user's guide for WhatsUp software version 2.5. It describes new features such as IPX monitoring and enhanced auto scan options. It also lists changes to system requirements for IPX support and notes documentation updates and corrections to the original user's guide.
Similar to An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth (20)
An Express Guide ~ SNMP for Secure Rremote Resource Monitoring

An Express Guide ~ SNMP for Secure Rremote Resource Monitoring
Fault tolerance performance and scalability comparison: NEC hardware-based FT...

Fault tolerance performance and scalability comparison: NEC hardware-based FT...
Open Programmable Architecture for Java-enabled Network Devices

Open Programmable Architecture for Java-enabled Network Devices
More from Abhishek Kumar
Insecurity-In-Security version.2 (2011)

Presentation (version.2) from 2011 describing how Security mechanisms placed to secure us are insecure themselves.
Insecurity-In-Security version.1 (2010)

Presentation (version.1) from 2010 describing how Security mechanisms placed to secure us are insecure themselves.
DevOps?!@

DevOps session#1 on what it is, which responsibilities it carries, what tools are already out there to help
xml-motor ~ What,Why,How

xml-motor
what, why & how about the new technique xml-parser rubygem
http://justfewtuts.blogspot.com/2012/03/xml-motor-what-it-is-how-why-should-you.html
XML-Motor

A new compact XML algorithm without any dependencies. Its implemented as a rubygem to provide Non-native XML parser for particular usages. RubyGem at http://rubygems.org/gems/xml-motor and https://github.com/abhishekkr/rubygem_xml_motor
DevOps with Sec-ops

it's presentation from a short 5-min talk at 1st DevOpsDays India about security implications and threats in DevOps related tasks
Syslog Centralization Logging with Windows ~ A techXpress Guide

Syslog Centralization Logging with Windows ~ A techXpress Guide ~ Setting up a centralized Syslog Server to get EventLogs from all Windows Hosts for analysis
Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide

Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide ~ Setting up a secured Chained-Proxy between different offices using Squid for a specific URL set.
Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide

Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide ~ for Load Balancing the Network Traffic on Multiple Etheret Cards attached on a Linux Box
Solaris Zones (native & lxbranded) ~ A techXpress Guide

Solaris Zones (native & lxbranded) ~ A techXpress Guide ~ Creating & Managing Solaris Zones; Mirroring an existing Linux Setup to a Zone; Setting up SVN, CIFS over a Zone
An Express Guide ~ Zabbix for IT Monitoring 

Zabbix is an open source infrastructure monitoring solution. It has two main parts - the Zabbix server and client.
The document provides step-by-step instructions to install and configure Zabbix on a Linux server. This includes installing prerequisites like NTP, PHP, MySQL, compiling and installing the Zabbix server and client, configuring the database, web interface, and more. Finally, it discusses initial configuration steps after installation like securing login credentials.
An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing

It's an Express Guide to "Setup of Cacti Server with purpose of IT Infrastructure Monitoring & Service Graphs" ~~~~~ its aimed at monitoring of various IT services and brilliant graphing of statistics
Presentation on "XSS Defeating Concept in (secure)SiteHoster" : 'nullcon-2011'

Nullcon is an annual hacker conference held in India. The document discusses defeating web application attacks through offensive security techniques like bug hunting and disarming malicious script tags. It also covers techniques for preventing cross-site scripting attacks, such as parsing user input and only allowing safe HTML tags.
XSS Defeating Concept - Part 2

An Approach Eradicating Effect of JavaScript Events in
User Input Being A Part of Web2.0 Facilities... in short the final nail to coffin of XSS Attacks
XSS Defeating Trick ~=ABK=~ WhitePaper

This document proposes a technique to prevent XSS attacks by modifying how browsers render <script> tags inserted into the <body> of an HTML document. The technique involves the web server transforming the page generated by the application server by wrapping the <body> contents in a <script> tag. This causes any <script> tags in the original <body> to not execute while preserving those in the <head>. The goal is to enable security without requiring input validation by web developers. A proof-of-concept implementation demonstrates how this modification disables injected malicious scripts.
FreeSWITCH on RedHat, Fedora, CentOS

This document provides instructions to install FreeSWITCH on CentOS/RedHat/Fedora in 13 steps: 1) Install dependencies with YUM; 2) Download and extract FreeSWITCH source; 3) Add OpenZAP support to configuration; 4) Compile and install FreeSWITCH; 5) Create symlinks for main binaries; 6) Launch FreeSWITCH as a service or from the command line; 7) Use fs_cli to access the command line.
More from Abhishek Kumar (16)
Syslog Centralization Logging with Windows ~ A techXpress Guide

Syslog Centralization Logging with Windows ~ A techXpress Guide
Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide

Squid for Load-Balancing & Cache-Proxy ~ A techXpress Guide
Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide

Ethernet Bonding for Multiple NICs on Linux ~ A techXpress Guide
Solaris Zones (native & lxbranded) ~ A techXpress Guide

Solaris Zones (native & lxbranded) ~ A techXpress Guide
An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing

An Express Guide ~ Cacti for IT Infrastructure Monitoring & Graphing
Presentation on "XSS Defeating Concept in (secure)SiteHoster" : 'nullcon-2011'

Presentation on "XSS Defeating Concept in (secure)SiteHoster" : 'nullcon-2011'
Recently uploaded
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
System Design Case Study: Building a Scalable E-Commerce Platform - Hiike

This case study explores designing a scalable e-commerce platform, covering key requirements, system components, and best practices.
AWS Cloud Cost Optimization Presentation.pptx

This presentation provides valuable insights into effective cost-saving techniques on AWS. Learn how to optimize your AWS resources by rightsizing, increasing elasticity, picking the right storage class, and choosing the best pricing model. Additionally, discover essential governance mechanisms to ensure continuous cost efficiency. Whether you are new to AWS or an experienced user, this presentation provides clear and practical tips to help you reduce your cloud costs and get the most out of your budget.
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on automated letter generation for Bonterra Impact Management using Google Workspace or Microsoft 365.
Interested in deploying letter generation automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI, built on the robust SAP Business Technology Platform (SAP BTP), is the latest and most advanced version of our AI development, reaffirming our commitment to delivering top-tier AI solutions. Skybuffer AI harnesses all the innovative capabilities of the SAP BTP in the AI domain, from Conversational AI to cutting-edge Generative AI and Retrieval-Augmented Generation (RAG). It also helps SAP customers safeguard their investments into SAP Conversational AI and ensure a seamless, one-click transition to SAP Business AI.
With Skybuffer AI, various AI models can be integrated into a single communication channel such as Microsoft Teams. This integration empowers business users with insights drawn from SAP backend systems, enterprise documents, and the expansive knowledge of Generative AI. And the best part of it is that it is all managed through our intuitive no-code Action Server interface, requiring no extensive coding knowledge and making the advanced AI accessible to more users.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
A Comprehensive Guide to DeFi Development Services in 2024

DeFi represents a paradigm shift in the financial industry. Instead of relying on traditional, centralized institutions like banks, DeFi leverages blockchain technology to create a decentralized network of financial services. This means that financial transactions can occur directly between parties, without intermediaries, using smart contracts on platforms like Ethereum.
In 2024, we are witnessing an explosion of new DeFi projects and protocols, each pushing the boundaries of what’s possible in finance.
In summary, DeFi in 2024 is not just a trend; it’s a revolution that democratizes finance, enhances security and transparency, and fosters continuous innovation. As we proceed through this presentation, we'll explore the various components and services of DeFi in detail, shedding light on how they are transforming the financial landscape.
At Intelisync, we specialize in providing comprehensive DeFi development services tailored to meet the unique needs of our clients. From smart contract development to dApp creation and security audits, we ensure that your DeFi project is built with innovation, security, and scalability in mind. Trust Intelisync to guide you through the intricate landscape of decentralized finance and unlock the full potential of blockchain technology.
Ready to take your DeFi project to the next level? Partner with Intelisync for expert DeFi development services today!
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf

When it comes to unit testing in the .NET ecosystem, developers have a wide range of options available. Among the most popular choices are NUnit, XUnit, and MSTest. These unit testing frameworks provide essential tools and features to help ensure the quality and reliability of code. However, understanding the differences between these frameworks is crucial for selecting the most suitable one for your projects.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Recently uploaded (20)
System Design Case Study: Building a Scalable E-Commerce Platform - Hiike

System Design Case Study: Building a Scalable E-Commerce Platform - Hiike
Letter and Document Automation for Bonterra Impact Management (fka Social Sol...

Letter and Document Automation for Bonterra Impact Management (fka Social Sol...
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...

Skybuffer AI: Advanced Conversational and Generative AI Solution on SAP Busin...
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
A Comprehensive Guide to DeFi Development Services in 2024

A Comprehensive Guide to DeFi Development Services in 2024
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf

Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
An Express Guide ~ "dummynet" for tweaking network latencies & bandwidth
- 1. Express-Guide ~to~ Testing Web/Network Application With DummyNet Tweaking Network Latency & Bandwidth by, ABK ~ http://www.twitter.com/aBionic ::Task Detail:: Any service allowing to tweak Network Latency as per desire for testing Application Performance at different network latency scenarios. ::Background:: Normally, the difference which comes in Development and Deployment environment of Web Applications is of bandwidth and latency. To test the applications in actual scenario, one needs to tweak the latency as per deployment scene and then use it. There are few paid VE Technology based services like ‘Shunra’ for this. But we required a free, open-source application, if possible for windows. DummyNet, it’s an old Italian university project started for BSD systems, recently ported for Windows also. It helps in reducing latency of NIC to desired level. ::Execution Method:: Install NDIS Driver ◦ Open the configuration panel for the network card in use {right click on the sys-tray icon, or go to 'Control Panel' > 'Network' to select} ◦ Click on 'Properties' > 'Install' > 'Service' > 'Add' ◦ Click on 'Driver Disk' and select 'netipfw.inf' in the folder it has been extracted to. ◦ Select 'ipfw+dummynet' which should be the only service visible. ◦ Click 'Accept' on the warnings for the installation of an unknown driver. Create a BAT-File for your Application to be run under test bandwidth & latency with following content
- 2. ◦ -------------------------------------- @echo on @set CYGWIN=nodosfilewarning @ipfw -q flush @ipfw -q pipe flush @echo ################# @echo ## Setting up ## @echo ################# ipfw pipe 3 config delay 1000ms bw 500Kbit/s mask all ipfw add pipe 3 ip from any to any ipfw pipe show your_command_running_your_app pause @echo ################# @echo ## Cleaning up ## @echo ################# ipfw -q flush ipfw -q pipe flush pause -------------------------------------- ◦ Here, 1000ms is latency set and can be changed to desired value 500 Kbps is bandwidth set and can be changed to desired value 'delay x' and 'bw x'; both can be used separately also as per need either place a command running your application to be tested in place of 'your_command_running_your_app'; or simple remove that line and when the command gets paused at the first pause, run your application manually. ::Tools/Technology Used:: DummyNet: http://info.iet.unipi.it/~luigi/dummynet/ ::Inference:: Different latency settings disturbs only certain network applications, not all of them. If a Web Application is supposed to run on variable latency system, say for now on cloud. Then it needs to be rigorously tested at different latency settings.
- 3. ::Troubleshooting/Updates:: Requirement: to test if it gets installed properly as a network services Solution: it has a testme.bat file showing different tests, just run it and check stats
